For Manufacturing, Cyberattacks Can
Be Devastating.
Are You Ready?
14%
Manufacturing accounted for 14% of all ransomware attacks in 2025
+30%
Cyberattacks on manufacturing increased 30% year‑over‑year
27%
Manufacturing accounted for 27.7% of all cyberattacks in 2025
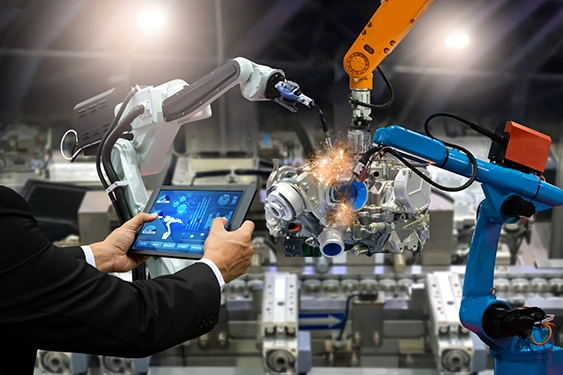
The Remote Work Challenge in Construction and Manufacturing
VPN Access
Traditional VPNs expose networks to threats by granting users full network access.
Complex Management
Security teams face immense management and operational overhead trying to enforce least-privilege access.
Compliance Issues
Meeting regulatory frameworks and cyber insurance policies is difficult without centralized visibility.
Protecting Remote Workers in Construction and Manufacturing
These core protections form the foundation of WatchGuard FireCloud, providing seamless access to SaaS and private applications from anywhere.
Zero Trust Network Access (ZTNA)
ZTNA provides identity-based access to an organization's private applications and resources.
Firewall as a Service (FWaaS)
FWaaS extends enterprise-grade network security directly to every remote and hybrid user through a lightweight agent installed on their device.
Secure Web Gateway (SWG)
SWG protects users from web-based threats, enforces acceptable use policies, and secures access to the Internet and Software as a Service (SaaS) applications.
Secure VPN Alternative
FireCloud replaces legacy VPNs with identity-based, per-app access that limits exposure and improves performance.
Secure Your Company Today
Contact us to discover how WatchGuard can help manufacturing stay secure.
Key Cybersecurity Challenges Facing Manufacturers
Manufacturers face unique cybersecurity risks, from ransomware and legacy systems to remote access vulnerabilities. Explore the critical challenges impacting operations and what organizations must address to stay secure.

Start Protecting Yourself Today
Discover how simple it is to keep manufacturing facilities secure with WatchGuard.