VPN vulnerability exposes a nuclear institute in South Korea
The Korea Atomic Energy Research Institute (KAERI) is the South Korean government agency in charge of nuclear technology research. It is responsible for structures and elements such as power plants, reactors and nuclear safety at a national level. This clearly makes it a target for espionage and cyberattacks by Seoul's main adversary: North Korea.
A few weeks ago, KAERI revealed an incident had occurred that proves this: a group of cyberattackers had infiltrated its internal network. It seems that the entry vector was once again a vulnerability in the organization's VPN network. Due to the rise in working from home during the pandemic, this is an increasingly common route for hackers as demonstrated by the ransomware that affected CAPCOM, as we explained previously in our blog. The opposition to the South Korean government claims that North Korean cybercriminals managed to break in by getting hold of an email and the credentials of a former advisor to President Moon-Jae In.
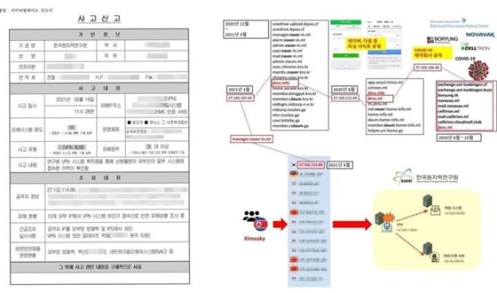
Diagrams of the incident at KAERI
Be that as it may, the South Korean agency maintains that hackers infiltrated the system from several locations, as the forensic analysis shows that 13 IP addresses gained access to the corporate network. But most significantly, one of these IP addresses was already known to have been used by the Kimsuky Group.
APT specialized in intelligence and critical infrastructure
Kimsuky is also known as Velvet Cholima and Black Banshee. It is an advanced persistent threat (APT) with clear links to the North Korean regime. Its targets are usually government organizations or think tanks, but also attacks critical infrastructures such as utilities and military units. However, it has also been known to hit other targets beyond South Korea, such as the International Atomic Energy Agency (IAEA) and ambassadors from other countries.
The US Cybersecurity and Infrastructure Security Agency (CISA) issued a report last year warning of its most common tactics. Spearphishing is cited among these strategies, but they include the use of malicious scripts with the ability to collect user credentials.
Updates and advanced firewall devices
The techniques we have described necessarily involve a high level of resources and sophistication on the part of Kimsuky. This indicates how dangerous these attacks are to organizations in charge of sensitive information or facilities that are of interest to the regime in Pyongyang. Notwithstanding, and beyond North Korea, Kimsuky highlights the risks posed by APTs to organizations, in particular through the KAERI incident, and the danger from VPNs used for remote working.
In this context, MSPs must first ensure that their VPN software contains the latest updates to minimize the risk of cyberattackers exploiting vulnerabilities. But in addition to this best practice, they must also have resources in place to ensure the cybersecurity of remote working in their organizations. In this regard, WatchGuard's Cloud-hosted firewalls provide top-notch network security that helps load balance VPN traffic.
WatchGuard FireboxV provides comprehensive protection and delivers the network and security services also found in WatchGuard physical firewalls, including HTTPS inspection and support for mobile devices. In addition, it works on most industry-standard servers and through WatchGuard System Manager's intuitive console, and can be easily managed from anywhere, providing full visibility into the network. As a result, the VPNs and corporate networks of organizations such as KAERI will have much more comprehensive cybersecurity capabilities available to combat cyber threats.
