PUTIN, or Putin Team, is an NB65 (Conti v2) derivative that one would believe would be of Russian origin and, thus, likely attack targets outside of Russia. However, the operators behind this ransomware perform the opposite action and are known to have attacked two organizations, both in Russia. One was a dentistry and the other was a distribution and logistics company. These were posted on their Telegram page, of which they had two - one to negotiate extortions and the other to publish double extortions. Interestingly, these two companies were directly named in ransom notes. However, the other four samples we located only state a unique victim ID. This appears to be a preference of the operators, as the payloads were similar aside from that.
This ransomware is practically the same as MEOW! (MeowCorp) and is only inserted as a separate entry because of the subtle differences in theme (Russia), ransom note, and extortion tactics. MEOW! had listed several emails and Telegram accounts. However, the group behind this ransomware is the same as MEOW! and calls themselves NB65 (Network Battalion 65), a cybergroup from Ukraine. NB65, and Anti-Russian Extortion Group, which could be the same operators, began attacking Russian companies in response to the war in Ukraine. Hence, the Russian theme. They aren't Russian; they exclusively attack Russia.
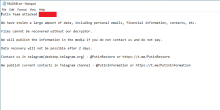
Like Conti v2 (NB65), the ransomware encrypts files using ChaCha20 and RSA-4096. However, the file extension used on encrypted files is <file name>.PUTIN. Hence the ransomware name - PUTIN. However, there were at least two other variations of the PUTIN naming convention as the '.KREMLIN' and '.RUSSIA' file extensions were also discussed on Kaspersky forums by victims of this ransomware. The last known discussion of the PUTIN ransomware was in February 2023, when the threat actors declared they were seizing operations and subsequently released decryption keys for victims. However, since the Conti v2 encryptor leaked, it's likely we will see other variants bearing different names but with similar payloads.
Samples (SHA-256)(6)
| Industry Sector | Country | Extortion Date | Amount (USD) |
|---|---|---|---|
| Healthcare & Medicine | Russia | ||
| Distribution & Logistics | Russia |