Modern SOC and MDR Services Series: What They Are, Why They Matter
Inadequate cybersecurity is a severe issue that challenges SMBs and enterprises indiscriminately, putting them at risk. Reasons for the business impact include:
- No business is immune to breaches in security. No matter their size or industry.
- Organizations can’t keep up with the increasing number and sophistication of threats. The threat landscape has evolved dramatically in the number and sophistication of attacks.
- A successful data breach costs time, resources, reputation, and cash. In addition to the expense of detecting, mitigating, and cleaning up after a breach, there are long-term costs.
- Expansion of the attack surface due to the number of employees working from home and the growing use of the Cloud.
- Insufficient detection and response time. Hackers have enough time to move laterally in systems and achieve their objectives without being detected by standard security solutions.
- Organizations struggle with compliance obligations that require organizations to meet specific cybersecurity requirements.
To help businesses navigate cybersecurity risks, many delegate to internal or external security operation centers (SOC).
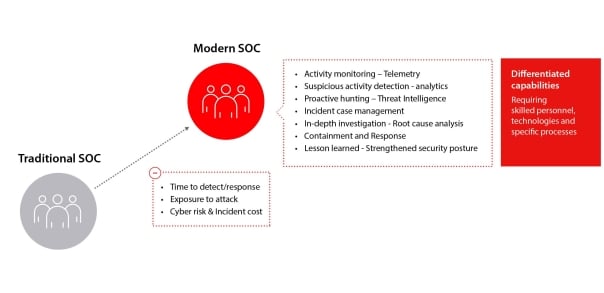
In general, while every SOC team implements the organization’s overall cybersecurity strategy and coordinates efforts to monitor, assess, and defend against cyberattacks, modern SOCs also focus on reducing the time attackers have access to resources by detecting, responding to, and helping recover from incidents.
Let’s better understand the difference between a SOC and a modern SOC:
A security operations center (SOC) is a facility where the information security team constantly monitors and analyzes the security of an organization through logs and alerts. The primary purpose of the SOC team is to detect, analyze and respond to cybersecurity incidents using technology, people, and processes.
However, the requirements for SOCs have evolved in recent years as the volume and sophistication of threats grow, the damage to businesses’ economics and reputations increases, the attack surface expands, and the volume of cybersecurity data and alerts to handle grows exponentially.
In addition to the functions of a SOC, the modern SOC monitors the network, endpoints, applications, and user activity to proactively detect abnormal behaviors, investigate those indicators of a security incident or attack, and immediately respond to the threats.
Those threats can bypass the existing security controls and lurk in the organizational environment looking for an opportunity to gain access and breach company assets. By being ahead of the adversary, the modern SOC can anticipate its detection and response, stopping it before the damage is done, avoiding the compromise, mitigating the impact, and reducing the incident costs.
Modern SOC components
Modern SOCs operate 24/7, with employees working shifts to monitor activity, detect abnormal behavior and mitigate threats that otherwise can pass under the radar.
The modern SOC staff may work closely with other teams or departments but are typically self-contained with security analysts and engineers with distinguished cybersecurity skills to ensure security issues are addressed quickly upon discovery.
While SOCs tend to react to a security incident by rapidly searching for a fix without digging too deep, modern SOCs act proactively to uncover and hunt for threats in their very first steps in the network and deeply investigate the course of action, the threat group, and the reasons behind the incident. As a consequence of this proactivity, analysts can identify the weaknesses of the organization’s security program and establish a robust plan to improve its security posture to avoid future incidents and reduce the time of exposure to threats and their repercussions.
Reactive, proactive, and threat hunting methods bring value at different levels.
What are managed detection and response (MDR) service providers?
MDR service providers deliver remote threat hunting, proactive detection, investigation, and response functions from a modern SOC to customers through a Cloud-based infrastructure.
MDR service providers offer a turnkey experience, using a predefined technology stack to collect relevant logs, system activity, data, and contextual information. This telemetry is analyzed within the provider’s platform using various technologies, including artificial intelligence and machine learning (AI/ML) and up-to-the-minute threat intelligence. This process allows for investigation by expert skilled analysts, who deliver actionable outcomes or actively respond through threat mitigation and containment.
When a threat is detected, they will verify the criticality and investigate the incident to find the root cause and course of action, while actively responding or recommending the response to the partner and customer.
WatchGuard for SOCs
WatchGuard for SOC brings a series of leading-edge solutions specialized in addressing and solving the security problems of organizations with higher levels of maturity in cybersecurity managed by security service providers, modern SOCs, and MDR service providers. WatchGuard for SOCs provides products and services that automate their advanced security programs and augment their security teams with expertise, technologies, and processes that enable them to uncover, detect, contain, and respond rapidly to threats that have successfully evaded other protections.
Learn more about Modern SOCs and MDR Services by reading our latest eBook, Modern SOC and MDR: What they are, why they matter and visiting WatchGuard for SOC.
