New BianLian Ransomware Activity Detected: SVG Phishing Campaign Targeting Venezuelan Companies
WatchGuard telemetry identified some malicious files being downloaded by victims, and almost all of them originated in Venezuela, indicating a possible malicious campaign targeting companies in this country.
The malicious files are distributed via phishing emails that have a SVG file with a filename in Spanish, generally indicating invoices, receipts, or budgets.
SVG stands for Scalable Vector Graphics, a file format for two-dimensional vector images. It allows images to be scaled without loss of quality, making it ideal for web graphics like logos and illustrations.
If an SVG file is opened in a text editor, it has XML code. It has already been observed that some phishing emails were distributed with SVG containing malicious code.
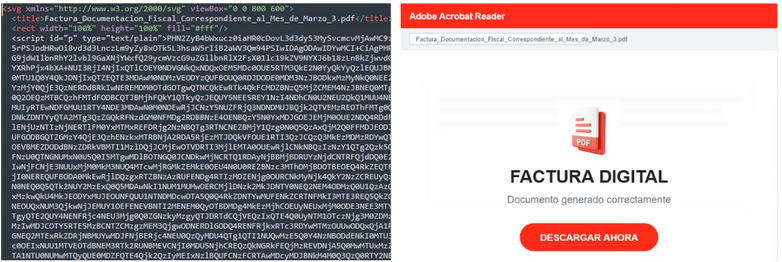
Figure 1. Example of a malicious SVG file
When these malicious SVGs are opened, they communicate with a URL that downloads the malicious artifact.
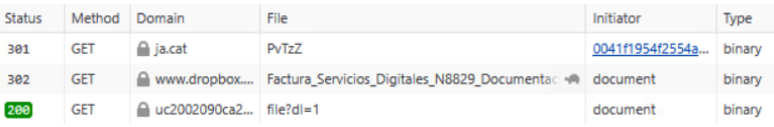
Figure 2. Network communication when a malicious SVG file is opened
A recent campaign distributing malicious SVG files in Spanish was observed last year; the target was victims in Colombia, and the files had fake portals impersonating Colombia's judicial system.
Initial Vector
As mentioned earlier, the campaign starts with phishing, delivering malicious SVG files that are used to download the malware.
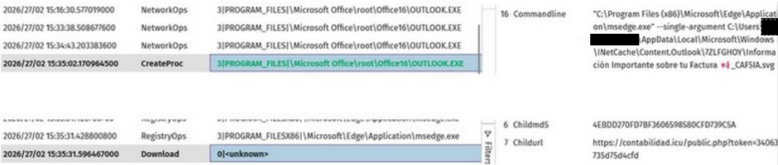
Figure 3. Events showing that the phishing email was opened by the victim
This campaign uses ja.cat to shorten URLs from legitimate domains that have a vulnerability that allows redirects to any URL, so they point to the original domain where the malware is downloaded. The domains affected by the URL redirection are from Brazil.
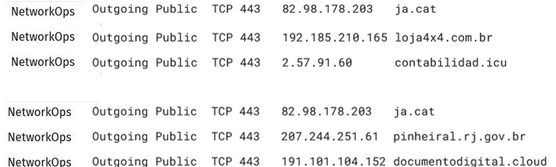
Figure 4. Network connections are established when the SVGs used in the campaign are opened
The URLs used in the malicious campaign are in the format https://<domain>/public.php?token=<16_digit_token>
Artifact Analysis
The artifact is a Windows Executable written in Go
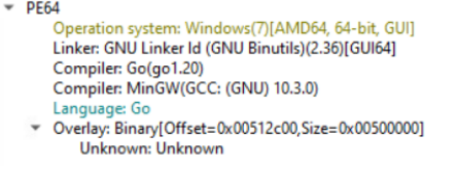
Figure 5. Information about the analyzed artifact
At the start of execution, the malware executes a routine that retrieves the address of various export functions. Among these functions are LoadLibraryExA and LoadLibraryExW, which are used to load some important DLLs. These DLLs are dynamically loaded to avoid detection.
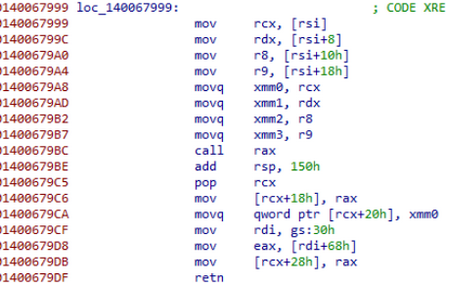
Figure 6. Routine of instruction made by malware at the start
Some of the export functions loaded by the malware are SetErrorMode, to prevent the display of the Windows Error Reporting dialog, and RtlAddVectoredExceptionHandler, to register a VEH, which can be used by malware to control how exceptions are handled and ensure that the payload remains active in case of errors.
It also loads functions associated with threads, such as CreateWaitableTimerExW, which creates a waitable timer object, allowing synchronization between processes that can be used by functions executed in parallel, like threads.
We can see timeBeginPeriod used to request a minimum timer resolution for periodic timers, allowing applications to achieve higher accuracy in timing operations. It’s used to restore the previous timer resolution and avoid potential negative impacts on system performance and power usage.
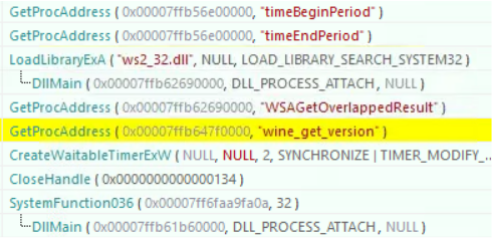
Figure 7. Windows APIs called during execution
One important DLL loaded during runtime is ws2_32.dll, which is responsible for network communication. It starts using WSAGetOverlappedResult to retrieve the results of an overlapped operation on the specified socket.
Another DLL is powrprof.dll, which uses the PowerREgisterSuspendResumeNotification function. It is used to register itself to receive notification when the system is suspended or resumed. This can be used by malware to monitor if the system is suspended and execute certain actions, because in this state, security solutions may be less active in monitoring.
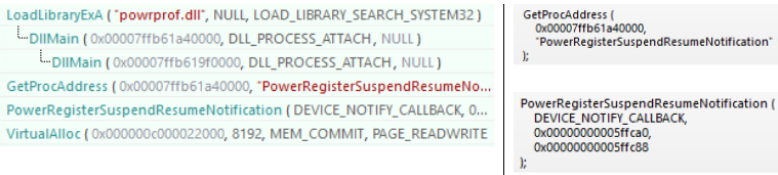
Figure 8. Call to PowerRegisterSuspendResumeNotification
The malware gets system environment variables, including GODEBUG and DEBUG_HTTP2_GOROUTINES, which are specific to the Go language.

Figure 9. Calls to get system environments
SystemFunction036, which is an alias for the RtlGenRandom function that generates pseudo-random numbers in Windows operating systems, is also used. It is accessed through the Advapi32.dll library and requires dynamic linking using LoadLibrary and GetProcAddress functions.
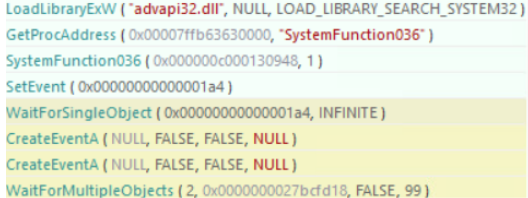
Figure 10. Call to SystemFunction036 and start of a thread
These actions are the same observed in a SecurityScorecard report, which links these actions to BianLian ransomware.
BianLian ransomware is a developer, deployer, and data extortion cybercriminal group that has been active since 2022. It was observed attacking critical structure in US and Australia, but the group targets multiple industries and has tactics and techniques that have been evolving.
One of the most interesting things that we saw in the analyzed artifacts is the utilization of the function wine_get_version, which is used to detect if the system is running in Wine.
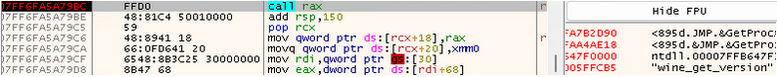
Figure 11. Call to wine_get_version
There is a routine that makes byte operations using a value loaded from a location in the Thread Local Storage (TLS) at the start of the execution, and the result is the address of the function that will be called in a thread.
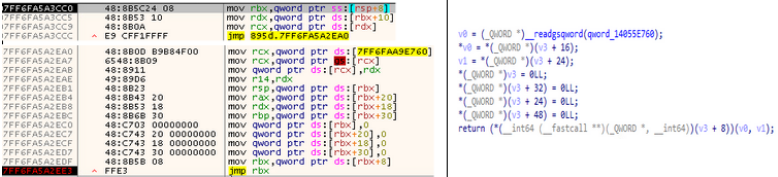
Figure 12. Routine instructions that call different functions in a thread
In the code, we can also observe anti-debugging techniques to make the analysis more difficult.
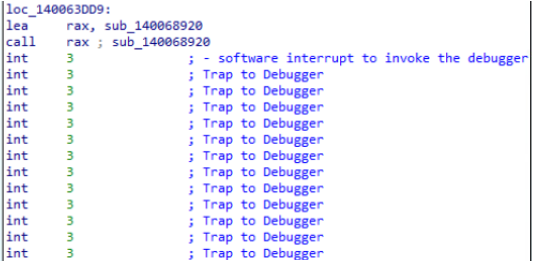
Figure 13. Anti-debugger technique in the malware code
Another BianLian characteristic observed in the analyzed artifacts is the use of AES functions implemented in Assembly to accelerate encryption.
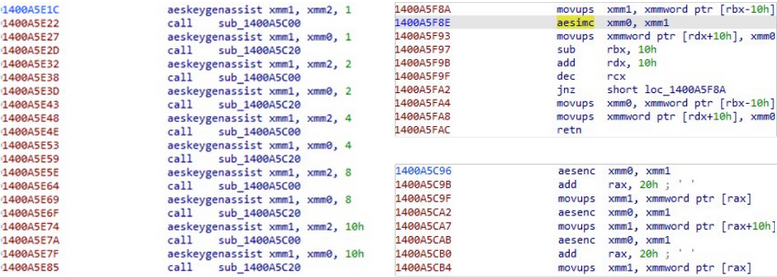
Figure 14. Use of AES functions in the malware code
Indicators of Compromise
Domains:
contabilidad[.]icu
documentodigital[.]cloud
getpdfdigital[.]cloud
soportedigital[.]cloud
What This Campaign Reveals About Evolving Ransomware Delivery
This campaign is a strong reminder that even seemingly harmless file types like SVGs can be used to deliver serious threats. In this case, malicious SVG attachments were used to initiate a phishing chain that led to malware delivery associated with BianLian activity.
Organizations should treat unexpected image attachments with caution, strengthen email and endpoint defenses, and monitor for suspicious outbound connections. As attackers continue to evolve their delivery methods, understanding how ransomware reaches victims is critical to stopping it earlier in the attack chain.
