Applies To: Endpoint Security Elite, Endpoint Security 360, Endpoint Security Prime, WatchGuard EDR, Endpoint Security Basic
Each WatchGuard Endpoint Security product includes software installed on endpoints and the Endpoint Security management UI to manage security for the devices and your IT network. To get started with Endpoint Security, complete these high-level steps.
- Step 1: Activate an Endpoint Security License
- Step 2: Allocate Endpoints (Service Providers Only)
- Step 3: Configure Pre-Deployment Settings
- Step 4: Deploy the WatchGuard Agent
For information on how to get started with WatchGuard EDR Core (Total Security Suite), go to Quick Start — Set Up WatchGuard EDR Core.
Step 1: Activate an Endpoint Security License
- If you do not have a WatchGuard account, create one at https://accountmanager.cloud.watchguard.com/create-account.
-
Activate your WatchGuard Endpoint Security license in the WatchGuard website.
For more information, go to Activate an Endpoint Security License.
Trial licenses are also available in WatchGuard Cloud. On the Administration > Trials page, you can start a trial of an endpoint product or module. Trial product licenses include up to 250 endpoint licenses for WatchGuard EDR, Endpoint Security Basic, Endpoint Security Prime, Endpoint Security 360, or Endpoint Security Elite. For more information, go to Start a Trial – Service Providers.
Step 2: Allocate Endpoints (Service Providers Only)
- Log in to your WatchGuard Cloud account.
-
Allocate endpoint licenses to your managed accounts.
For more information, go to Allocate Endpoints.
Step 3: Configure Pre-Deployment Settings
The WatchGuard Endpoint Security installation process consists of a series of steps that depend on the status of the network at the time of deployment and the number of computers and devices you want to protect. Before you deploy the WatchGuard Agent, we recommend that you complete these steps to plan the installation of WatchGuard Endpoint Security:
- Identify Unprotected Devices
- Verify Minimum Requirements for Target Devices
- Determine Computer Default Settings
Identify Unprotected Devices
Identify the physical and virtual Mac, Android, iOS, Windows, or Linux computers and devices you want to protect with Endpoint Security.
Verify that you have purchased enough licenses for the unprotected devices. Endpoint Security allows you to install the WatchGuard Agent even when you do not have enough licenses for all the computers you want to protect. Computers without a license still show information such as installed software and hardware on the computer details page, but are not protected.
For more information, go to Unmanaged Computers Discovered List .
Verify Minimum Requirements for Target Devices
Make sure that the computers and devices you want to protect meet the minimum installation requirements. For information on requirements, go to Installation Requirements in the Release Notes.
For modules requirements, go to the appropriate topic:
- WatchGuard Full Encryption Requirements
- Patch Management Requirements
- Advanced Visualization Tool Requirements
- Data Control Requirements
- SIEMFeeder Requirements
WatchGuard endpoint security products require access to multiple Internet-hosted resources. Make sure these URLs and ports are open to allow communication with the WatchGuard servers.
For more information on URLs and port access, go to WatchGuard Cloud URLs and Network Access Requirements.
Determine Computer Default Settings
When the client software is installed on the computer or device, Endpoint Security applies the group security settings to the computer or device. During installation, you select a target group for the computer with the required network settings. If the network settings for the selected group differ from the settings specified during installation, the installation settings apply.
For more information, go to Best Practices — Installation Tips for Endpoint Groups and Settings.
Configure the group organization and define settings before you deploy the WatchGuard Agent.
For more information about the different types of groups, and specific instructions, go to Manage Computers and Devices in Groups in Endpoint Security.
Endpoint groups can be used to configure deployment behavior for products installed by the WatchGuard Agent in the WatchGuard Cloud user interface. For more information, go to Configure WatchGuard Agent Deployment in WatchGuard Cloud.
To add a group:
- In WatchGuard Cloud, select Configure > Endpoint Security.
- Select Computers.
- From the left pane, select
 My Organization.
My Organization. - Next to the group in which you want to add a group, click
 .
.
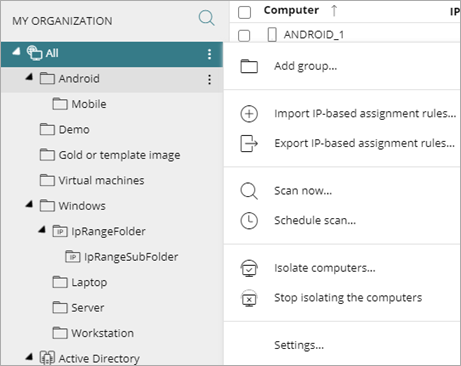
- Select Add Group.
The Add Group dialog box opens.
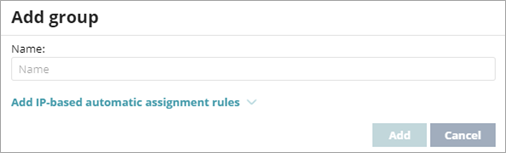
- Type a Name for the group.
- Click Add.
To configure settings from WatchGuard Cloud, you must first create a settings profile. For more information, go to Best Practices — Installation Tips for Endpoint Groups and Settings.
If you plan to use Endpoint Security with third-party antivirus software, you should add exclusions in both the third-party product and Endpoint Security to make sure that they do not overlap or create false detections. For information on how to create exclusions, go to Create Exclusions in WatchGuard Endpoint Security.
To create a settings profile:
- In WatchGuard Cloud, select Configure > Endpoint Security.
- Select Settings.
- From the left pane, select the type of security settings you want to create a profile for.
- In the upper-right corner, click Add.
The Add Settings page opens.
The Add Settings page shows different options for Endpoint Security Elite, 360, Prime, Basic, WatchGuard EDR and EDR Core.
- In the Name text box, type a new name for the settings profile.
- In the Description text box, type a description of the profile.
For example, you might describe the security needs addressed in the settings. - Expand each section and configure the settings.
- Configure Per-Computer Settings
- Configure Remote Control Settings (Endpoint Security Elite only)
- Configure Network Settings
- Configure Workstations and Servers Security Settings
- About the IOC Gallery (Endpoint Security Elite only)
- Configure Indicators of Attack Settings
- Configure Risks Settings
- Configure Script Blocking (Windows Computers)
- Configure Program Blocking Security Settings (Windows Computers)
- Configure Authorized Software Settings (Windows Computers)
- Configure Mobile Device Security Settings
- Configure Vulnerability Assessment Settings
- Configure Patch Management Settings
- Configure Endpoint Access Enforcement Settings (Windows Computers)
- Encryption Settings
Settings vary for Endpoint Security Elite, 360, Prime, Basic, WatchGuard EDR, and EDR Core. Throughout this documentation, Endpoint Security refers generally to all products. If a setting is not visible in the Endpoint Security management UI, it is not supported by your product.
For more information, go to:
- When you have configured all the settings, click Save.
Step 4: Deploy the WatchGuard Agent
For accounts with more than one WatchGuard product license (for example, an Endpoint Security product license and a FireCloud license), the Configure > Agent Deployment page in WatchGuard Cloud is useful to centrally configure product deployment behavior for endpoint groups and endpoints. For more information, go to Configure WatchGuard Agent Deployment in WatchGuard Cloud.
Deploy the WatchGuard Agent to computers and devices in your organization with the correct network settings. The deployment strategy depends on the number of devices to protect, the devices with an WatchGuard Agent already installed, and the company network architecture, including whether there is a mobile device management solution in use.
For more information, go to the appropriate installation procedure for your scenario and platform:
- Download the WatchGuard Agent Installer for Endpoint Security Products
- Install the Endpoint Software Locally
- Install the Endpoint Security Software on Windows Computers and Servers
- Install the Endpoint Security Software on Mac Computers
- Install the Endpoint Security Software on Linux Computers
- Install the WatchGuard Mobile Security App on Android Devices
- Install the WatchGuard Mobile Security App on iOS Devices
- Install the Endpoint Software Remotely (Windows Computers)
- Deploy the Endpoint Software with Centralized Tools (Windows Computers)
- Install the Endpoint Software on Virtual Environments with a Template or Gold Image (Windows Computers)
Endpoint Security Installation Requirements (external link)
Endpoint Security Installation Plan