Configure SSID Settings
Applies To: Wi-Fi Cloud-managed Access Points (AP125, AP225W, AP325, AP327X, AP420)
SSID settings are also inherited by subfolder locations, and you can customize the settings for a specific subfolder.
To add a new SSID in Discover:
- Open Discover.
- Open the Navigator, and select a location where to apply the SSID settings.
- Select Configure > WiFi.
- Select the SSID tab.
- Click Add SSID.
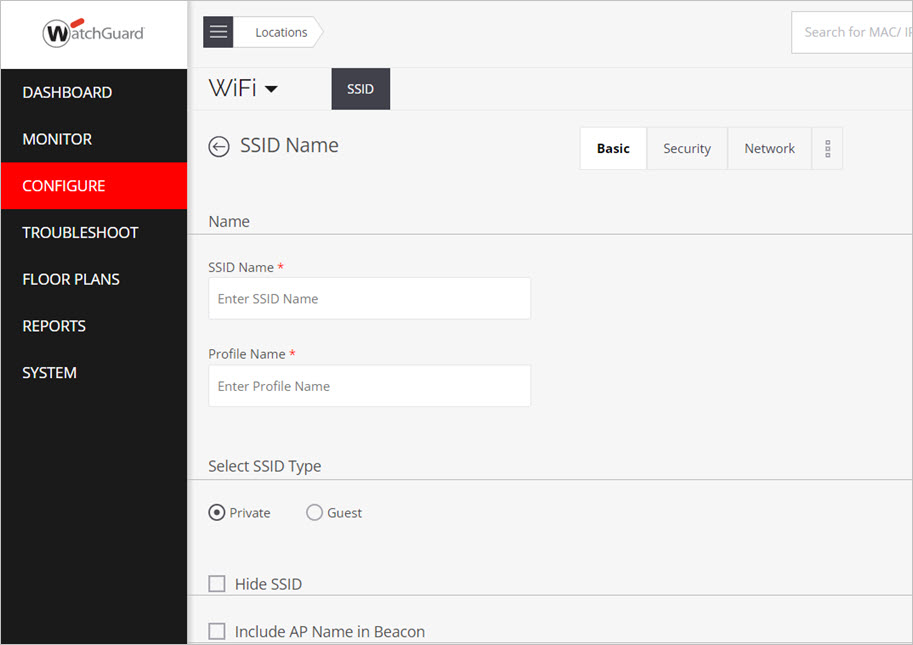
- Complete each section of the SSID settings for your specific deployment. Click Save or Save & Turn SSID On when you finish.
- SSID Name — Type a name for the SSID that your APs will broadcast.
- Profile Name — Type a descriptive profile name for the SSID settings.
- Select SSID Type — Select Private for a private Wi-Fi network SSID, or select Guest for a guest Wi-Fi network SSID.
- Hide SSID (Optional) — Select this option if you do not want the SSID name broadcast on your Wi-Fi network.
- Include AP Name in Beacon (Optional) — Select this option to include the name of the AP in the beacon.
- Select Security Level for Associations— Select the security protocols used for associations to your SSID. We recommend at minimum you select WPA2 with PSK security.
- Open — Open means no security settings are applied. This is the default security setting, and is typically used for guest networks.
- WPA2 — WPA2 is the latest and most secure protocol. It fully implements the IEEE 802.11i standard.
- WPA and WPA2 mixed mode — A mix of WPA and WPA2 protocols to support legacy clients that use WPA (TKIP).
- WPA3 — (WPA3 is not supported by WatchGuard APs in Wi-Fi Cloud) WPA3 is the latest and most secure protocol for Wi-Fi 6 (802.11ax) APs.
- WPA2 and WPA3 mixed mode — A mix of WPA2 and WPA3 protocols.
WPA3, OWE, and UPSK only work with Wi-Fi 6 802.11ax access points, and are not supported by WatchGuard APs in Wi-Fi Cloud.
- OWE (Enhanced Open) — (OWE not supported by WatchGuard APs in Wi-Fi Cloud) Opportunistic Wireless Encryption (OWE) is the latest and most secure open protocol for Wi-Fi 6 (802.11ax) APs that provides each user with encryption that protects data exchange between the client and the wireless network. This enables you to create an open network that can provide data privacy without authentication. Clients that do not support OWE cannot connect with an OWE SSID. Both AP and clients must support OWE. Select the Transition Mode check box to enable clients that do not support OWE to be able to connect to the OWE SSID with the Open protocol. Two SSIDs are created when you enable transition mode. The first SSID is the OWE SSID. The second SSID is a copy of the first SSID with Open security only.
- 802.1x — If you select 802.1x, you must configure the RADIUS servers. For more information, see Configure RADIUS Servers in Discover. You can add one primary RADIUS server, and up to 3 additional RADIUS servers for backup.
- Caller Station ID — A free form text parameter that the AP passes to the RADIUS server in the standard RADIUS parameter, Called-Station-Id, during the authentication or accounting process. You can use one or more of the special format specifiers such as '%m, %n, %l and/or %s to represent the called station ID. The AP replaces %m with the Ethernet MAC address of the AP. The AP replaces %s with the SSID. The AP replaces %l with the location tag. The AP replaces %n with the device name. You can repeat the format specifiers. You can enter text instead of using the format specifiers.
- NAS ID — This field is used when a network access server (NAS) serves as a single point to access network resources. A NAS supports hundreds of simultaneous users. When a RADIUS client connects to a NAS, the NAS sends access request packets to the RADIUS server. These packets must contain either the NAS IP address or the NAS identifier. The NAS ID or the NAS-Identifier is used to authenticate RADIUS clients with the RADIUS server. You can specify a string for the NAS ID. You can use one or more of the special format specifiers, %m, %n, %l and/or %s to represent the NAS ID. The AP replaces %m with the Ethernet MAC address of the AP. The AP replaces %s with the SSID. The AP replaces %l with the location tag.The AP replaces %n with the device name. You can repeat the format specifiers. The default value of NAS ID is %m-%s. The NAS ID corresponds to the NAS-Identifier attribute on the RADIUS server. The attribute ID for the NAS-Identifier RADIUS attribute is 32. Ensure that the NAS ID is not the same as the shared secret configured for the RADIUS server in the RADIUS Authentication section. APs also support the NAS-IP-Address and NAS-IPv6-Address attributes. The AP uses these attributes along with the existing NAS-ID attribute to uniquely identify the NAS in Disconnect-Request and CoA-Request packets. These attributes simplify integrations with servers such as Cisco ISE, Forescout, and Aruba ClearPass because the NAS ID is not required. The AP will give preference to a NAS ID, if specified, then the NAS-IP-Address and NAS-IPv6-Address attributes.
- Opportunistic Key Caching — Enable client fast handoffs with the opportunistic key caching method. Key caching only works within the same subnet and not across subnets.
- Pre-authentication — Enable client fast handoffs with the pre-authentication method.
- Dynamic VLANs — Based on the VLAN returned by the RADIUS server, the AP dynamically redirects the network traffic of a RADIUS-authenticated user to the VLAN that is associated with the group to which the user belongs. Until the RADIUS server authenticates the user, the EAP packets will pass through the default VLAN. Note that the VLAN ID that is set in the Wi-Fi profile network settings is used as the default VLAN. To enable RADIUS-based assignment of VLANs, you must enable Dynamic VLANs and type a comma-separated list of dynamic VLANs (up to a maximum of 32) to which RADIUS users can be redirected. If the VLAN specific to the user group is not present, the default VLAN is used.
- Change of Authorization (CoA) — Enables a change of authorization (CoA) for a user session after the session has been authenticated. When you enable CoA, you can change the per user VLAN settings and per user bandwidth settings for an authenticated user session. Make sure that port 3799 is open on your firewall for CoA packets to the AP from the RADIUS server. Organizations with load balancer deployments can add additional CoA server IP addresses to directly send CoA requests from RADIUS servers to APs. APs accept the authentication and authorization messages coming from a load-balancer server and CoA requests coming from RADIUS servers.
- Prefer Primary RADIUS Server — Enables authentication to fall back to the primary RADIUS server when the server comes back online after a failover. When an AP detects a failover to the secondary RADIUS server, it waits for the Dead Time interval before switching back to the primary. This allows time for the primary server to stabilize.
- Open — Open means no security settings are applied. This is the default security setting, and is typically used for guest networks.
- Type a Passphrase for the security mode you selected.
- Mitigate WPA/WPA2 Key Reinstallation Vulnerabilities —This option mitigates recently discovered WPA/WPA2 vulnerabilities that affect APs and clients. To mitigate these client vulnerabilities, APs can block handshake messages that can potentially exploit clients, and force clients to reauthenticate. This option is disabled by default. This mitigation logic can trigger for other similar dropped packet symptoms, for example, natural frame errors during a handshake, or dropped packets when a client roams from one AP to another or roams beyond the range of the current AP connection. This can cause some legitimate client authentication connections to fail and be reestablished. WatchGuard recommends that you enable this mitigation feature until you have updated all your client software to address the client vulnerabilities.
- 802.11w — If you select WPA2 as the security protocol, an additional security mechanism of 802.11w management frame protection (MFP) can be enabled to protect a certain class of management frames and prevent spoofing attacks. 802.11w MFP protects the deauthentication, disassociation, and robust action management frames. Integrity Group Temporal Key (IGTK) is used to provide an integrity check for multicast management action frames. Pairwise Transient Key (PTK) is used to encrypt and protect unicast management action frames. 802.11w MFP can be enabled on an optional or mandatory basis. When it is enabled on an optional basis, both 802.11w and non-802.11w clients can connect to the AP. When 802.11w is enabled on a required basis, only 802.11w clients are allowed to connect to the AP. 802.11w management frame protection is disabled by default.
- VLAN ID — You can map your wireless network SSID to a VLAN mapping on your network. A Virtual Local Area Network (VLAN) enables you to logically organize separate virtual networks within your physical network regardless of the location of your clients. Clients on a VLAN communicate as if they are on the same physical network. VLANs use an ID to identify the VLAN on the network. VLANs can be tagged (VLAN information is tagged within the Ethernet frame for communication with a VLAN-enabled switch), or untagged (no VLAN information sent). You can assign a VLAN ID from 0 to 4094 for each SSID. There is no theoretical limit to the number of SSIDs you can create, however, you can only assign a maximum of 8 SSIDs per radio on an AP.
The default VLAN ID is 0. To map to an untagged VLAN on your switch port, use the default value of 0 for the VLAN ID, regardless of the VLAN ID assigned to the untagged VLAN on the switch. Otherwise, you can type a VLAN ID from 1-4094.
You can also use Dynamic VLANs with Wi-Fi Cloud. A Dynamic VLAN automatically manages VLAN port configuration based on the client's MAC address and authentication to the network, and enables you to use multiple VLANs with a single SSID. Wi-Fi Cloud supports 32 Dynamic VLANs per SSID and up to 4 SSIDs with Dynamic VLANs per AP. This provides a total of up to 128 Dynamic VLANs per device template configuration for an AP. There is no theoretical limit to the number of device templates you can create. For more information on how to configure Dynamic VLANs in a device template, see Dynamic VLAN Assignment in Wi-Fi Cloud.
You can use a VLAN Name to specify an SSID VLAN mapping. This enables dynamic resolution of VLAN Names to one or more VLAN IDs so you can map different VLAN IDs at different locations to the same SSID. This type of mapping is called SSID VLAN mapping. Specify a Fallback VPN ID to use if the mapped ID / VLAN Name is not available.
You can also configure a location-based VLAN mapping that maps the VLAN ID to a VLAN Name at a specific location. Location-based VLAN mapping takes precedence over the SSID VLAN Mapping. For more information, see Location-based VLAN Mapping. - Bridged — Use a bridged network when the AP and the clients associating with the AP are in the same subnet, and you expect the clients to receive IP addresses from a DHCP server on the network.
- NAT — Use Network Address Translation ( NAT) when you want to have the clients in a separate subnet and the AP in another separate subnet. With NAT, the clients can have a private IP address pool.
- Start IP address — The starting IP address of the DHCP address pool in the selected network ID.
- End IP address — The end IP address of the DHCP address pool in the selected network ID.
- Local IP address — An IP address in the selected network ID outside of the DHCP address pool. This address is used as the gateway address for the guest wireless network.
- Subnet Mask — The net mask for the selected network ID.
- Lease Time — The DHCP lease time in minutes. Minimum value is 30 minutes. Maximum value is 1440 minutes.
- DNS Servers — The DNS servers that the wireless clients can make DNS queries to. You can specify up to three DNS servers.
- Enable Wired Extension — Extends the NAT-enabled wireless LAN to the wired network using an additional LAN port on the AP. All network settings configured on this SSID will apply to the wired devices connected to the AP LAN port.
- L2 Tunnel — Select the L2 Tunnel check box if you want to aggregate all Wi-Fi traffic from your access points to a single layer 2 remote endpoint or gateway that can then forward the traffic. Select a Tunnel Interface from the drop-down list. For more information, see Configure Tunnel Interfaces.
- VPN Tunnel — Select the VPN Tunnel check box if you want to use this SSID with an IPSec VPN tunnel. Select a Tunnel Interface from the drop-down list. For example, select this option to deploy an SSID with an IPSec tunnel configured for a remote AP connection. For more information, see Remote Access Point.
- Split Tunnel for Client Traffic — With IPSec VPN tunnels, you can split the traffic between the corporate network and the public Internet. Only corporate-bound traffic is sent through the tunnel, while Internet traffic bypasses the tunnel. You can specify the subnets that are accessible through the tunnel. For example: 192.168.1.0/24.
- Use Tunnel for RADIUS Message — When you select an L2 or VPN Tunnel, you can use the tunnel for RADIUS communications. This enables devices to send messages (such as 802.1X or RADIUS MAC authentication, accounting, and CoA messages) to a RADIUS server behind a remote tunnel endpoint. 802.1X or RADIUS MAC Authentication must be enabled for communications with a remote RADIUS server.
- Layer 2 Traffic Inspection and Filtering — Layer 2 inspection and filtering prevents frames exchanged between two mobile devices from being delivered by the Wi-Fi access network without first being inspected and filtered by either the hotspot operator network or the service provider core network. This processing provides some protection for mobile devices against attacks.
- Inter AP Coordination — APs periodically broadcast data to other APs through inter-AP coordination for fast handover and seamless roaming of clients across APs in the same subnet or APs at the same location.
Broadcasts can occur through:- Layer 2 Broadcast — APs broadcast their information over the wired network. L2 broadcast works on the SSID VLAN. When Layer 2 GRE is enabled, it also works on the communication VLAN. Select Use Tunneling for Inter AP Coordination so that information related to inter-AP coordination flows through the tunnel.
- RF Neighbors — APs exchange information only with their RF neighbors. Dual-radio APs use background scanning to find their RF neighbors, and tri-radio APs use their third WIPS radio. Select Use Tunneling for Inter AP Coordination so that information related to inter-AP coordination flows through the tunnel. The RF Neighbors option only works with 802.11ac devices.
- This Server (the Manage server) — APs exchange information through the Manage server. The information is shared from a location to its subfolder locations.
- Advertise Client Associations on SSID VLAN — If enabled, APs on this SSID broadcast their client associations to other APs on the same SSID VLAN. This helps clients with fast roaming.
- Enable/Disable DHCP Option 82 — DHCP Option 82 is used in distributed DHCP server environments where an AP inserts additional information to identify the client point of attachment. The circuit ID represents the client point of attachment. DHCP Option 82 is available for a bridged SSID only. When DHCP option 82 is enabled and the AP receives DHCP packets from the client, the AP appends a circuit ID to the DHCP packets from the client. It then forwards this DHCP request to the DHCP server. Based on the circuit ID in the DHCP request, the DHCP server makes a decision on the IP pool from which to assign an IP address to the client. When DHCP assigns the IP address and passes it to the AP, the AP passes it on to the client after it strips the circuit ID.
Type the Circuit ID. You can use one or more special format specifiers: %s, %m, %l, and %n.
The AP replaces %s with the SSID.
The AP replaces %m with the AP MAC address.
The AP replaces %l with the location tag configured for the location to which the AP is assigned.
The AP replaces %n with the device name. - Multicast DNS (mDNS) Packet Tagging — mDNS enables you to resolve hostnames to IP addresses in networks that do not have a local name server. mDNS gateways on supported aggregation switches extend the scope of mDNS messages to additional subnets that enables hosts to discover services and resolve domain names across the larger logical network. A Wi-Fi client sends an mDNS packet to query for services on the network, such as a printer. An AP can tag client mDNS query packets with a location name that you define as a location tag. The AP adds this tag to the mDNS query that is used by the mDNS gateway to filter the services returned in response to the mDNS query.
- mDNS tagging is not supported in NAT or VPN Tunnel modes.
- Make sure your aggregation switch supports mDNS gateways.
- Make sure you have assigned the correct location tag to each location. mDNS gateways return devices based on the location tag. For more information, see Configure Location Folders with the Navigator.
- Firewall — A firewall controls incoming (wired to wireless) and outgoing (wireless to wired) network traffic for wired-side hosts based on a set of defined rules. The firewall rules defined for the SSID are evaluated in order from top to bottom. The first rule is evaluated first, followed by the next rule until a match is found for the respective host name and direction. To reorder the rules, you can click a rule and move it to a different location. When you create an SSID, the default rule is set to block all incoming and outgoing requests from any host or domain. To define the default rule, select Allow or Block to allow or block any type of requests from IP addresses, host names, subdomain names, or domain names for which no specific firewall rules have been defined. For more information, see Firewall Settings.
- Application Firewall — You can enable an Application Firewall and create rules to control application use. You can enable the Application Firewall independently of the firewall rules and create rules to allow or block specific applications on the SSID. Rules are processed in the configured order. When a rule match occurs, the configured action is performed and all other rules are ignored. You can select and move entries to reorder the rules. You must enable Application Visibility on an SSID to be able to use the Application Firewall. Application Visibility and the Application Firewall are only supported on 802.11ac Wave 2 APs. For more information, see Application Firewall.
- Bonjour Gateway — Bonjour is the Apple implementation of zero-configuration networking. You can use Bonjour to discover devices and services advertised by Bonjour-capable devices on a local network using multicast Domain Name System (mDNS). Bonjour traffic runs on local networks and is restricted to the broadcast domain of a single VLAN subnet. Clients on a different VLAN cannot discover Bonjour services. You can use the Bonjour Gateway in Wi-Fi Cloud to route traffic from the SSID VLAN to multiple different VLANs. When a client connects to an SSID that has Bonjour Gateway enabled and a Service VLAN configured, the AP forwards the mDNS packets from the Service VLAN to the client VLAN (the VLAN ID configured in the SSID). The client can then see Bonjour service advertisement traffic and connect to Bonjour services on the wireless network. If the devices are deployed on different VLANs, enter a comma-separated list of VLAN IDs. You can enter a maximum of 12 VLAN IDs. If Dynamic VLAN is configured in the SSID, the mDNS packets from each Service VLAN are forwarded to all the client VLANs listed under the VLAN pool field for Dynamic VLANs. Dynamic VLAN is available only if the Security Mode in the Security tab is set to any mode other that Open and WEP. The AP forwards the mDNS packets only to the client VLAN on the WLAN (wireless side). If wired extension is configured, the mDNS packets do not reach the wired VLANs.
- DHCP Fingerprinting-based Access Contol — (AP420 only) You can use DHCP Fingerprinting-based access control to allow or deny client connections to an SSID. The AP identifies the operating system of the client based on the DHCP packets exchanged between the client and the DHCP server. DHCP uses Option 55 to identify the client operating system. Wi-Fi Cloud uses this information to restrict clients from connecting to the network based on your settings. You can create a default rule to Allow or Deny a client from connecting to an AP based on its identified operating system. You can also control the action performed on clients that are not identified, and create exceptions to the default rule.
- Redirection — Redirects clients to a Web portal and blocks their access to the network (except to the sites listed in the Websites That Can Be Accessed Before Authorization section). You can redirect either Smartphones and Tablets or All Clients of the SSID to the Redirect URL you specify. For example, in an enterprise network, you may want smartphones and tablets to be redirected when accessing the SSID, but allow laptops and desktops to directly start to use Wi-Fi.
- Role Based Control — Role Based Control enables you to restrict wireless network access to authorized users. Users are granted controlled access to wireless resources based on the roles assigned to them. For example, you can restrict users to specific VLANs, apply bandwidth controls, enforce network and application firewall rules, or redirect users to a portal based on their role profile. When a user connects to an SSID, the user is authenticated based on Google or RADIUS authentication, and then depending on the Role Based Control rule that matches the user role, the corresponding role profile is applied for the user session. For more information, see About Role Based Control.
- WiFi Clients in Allow List or Deny List — You can create a list of allowed or denied wireless clients for an SSID based on the MAC address. For each SSID, you can add a maximum of 1024 clients to the Allow List or the Deny List.
- MAC addresses listed in the Allow List are allowed access to the SSID, while all other clients are denied access.
- MAC addresses listed in the Deny List are denied access, while all other clients are allowed access to the SSID.
- Client Isolation — Client isolation is an SSID-specific option that prevents communication between wireless clients connected to the same network. This includes clients on the same radio, different radios of an AP, or on different APs. Wireless clients also cannot communicate with wired-side hosts on the same network. Client isolation is useful in guest Wi-Fi access deployments to prevent communications between guest clients. Wi-Fi clients cannot communicate with another wired or wireless host on the same network. This includes local printers, NAS drives, and any other local hosted service, such as local DNS servers. If the other wired or wireless host is on a different network that is routable through your default gateway, this traffic is not limited by client isolation.
- These features do not work when client isolation is enabled:
- External portal hosted on a local network
- L2TIF
- IPv6 is not supported by client isolation. Wireless clients can still communicate with each other over IPv6.
- Clients connected to the same SSID but mapped to different VLANs on different APs cannot be isolated. You can perform this isolation with your router configuration.
- A VLAN where all clients have static IP addresses cannot be isolated.
- These features do not work when client isolation is enabled:
- Client Authentication — When you enable secondary authorization on your network, a wireless user first authenticates on the wireless network, and then the device used to connect to the network is authenticated to determine whether it is an authorized device. You can enforce device authorization through Google Integration or RADIUS MAC Authorization.
- Google Integration — To use this option, you must configure Google Integration. For more information, see Google Integration in Discover and Google Device Authorization. In the If Client Authorization Fails section, select Disconnect to disconnect the client if authentication fails, or select Assign Role and select an existing Role Profile from the drop-down list. Click Add/Edit to manage Role Profiles. For more information on Role Profiles, see Configure Role Profiles in Discover.
- RADIUS MAC Authentication — After the user successfully authenticates to the SSID, the AP authenticates the MAC address of the connecting client with a RADIUS server. For more information on how to configure RADIUS servers, see Configure RADIUS Servers in Discover. In the If Client Authorization Fails section, select Disconnect to disconnect the client if authentication fails, or select Stay Connected to allow the client and optionally select an existing Role Profile from the drop-down list to assign to the client. Click Add/Edit to manage Role Profiles. For more information on Role Profiles, see Configure Role Profiles in Discover. For more information on RADIUS MAC Authentication and additional parameters, see Configure RADIUS MAC Authentication.
- Association — Enable this option to store information about the clients that connect to or associate to your APs. You can view a report of this information in the Reports page in Discover. Association analytics include:
- Client MAC address
- Protocol
- SSID of the network to which the client connects
- Location of the client
- Start time of client association with the AP (GMT)
- End time of client association with the AP (GMT)
- Start time of client association with the AP according to local time of the user
- End time of client association with the AP according to local time at the user
- Session duration
- Data transfer from client device in bytes
- Data transfer to client device in bytes
- Data rate in Kbps
- Smart device type
- Local time zone
- Website URLs accessed by WiFi users — This option appears if you enable the Association analytics option. You can download a list, in CSV format, of the HTTP content analytics that include the website URLs accessed by wireless clients on your network. This report is available in the Reports page in Discover.
- Application Visibility — You can enable monitoring of applications on your Wi-Fi network. You can view the list of applications for a specific SSID in Monitior > WiFi > Application Visibility in Discover. For more information, see Monitor Application Visibility. You can also use the Application Firewall to manage access for detected applications. For more information. see Application Firewall. Application Visibility and the Application Firewall are only supported on 802.11ac Wave 2 APs.
- Push Analytics to Third-Party Server — You can transfer client HTTP content analytics or browsing data from clients over HTTP or HTTPS to an external server for storage and analysis. The analytics data is sent in a JSON file format, and you can use any analytics server that supports JSON file format. For more information, see About HTTP Content Analytics.
- Captive Portal — Select the type of portal to use:
- AP Hosted — The portal page is hosted by the AP. The portal is a customizable click-through page that you can use to display the terms and conditions for guest network usage and any other information required. For more information, see AP Hosted Splash Page with Click-through.
- Cloud Hosted — The portal page is hosted by Wi-Fi Cloud (requires a Total Wi-Fi AP subscription). You can configure a basic portal page with a customized background image, logo, text, privacy policy, terms of use, and these login methods:
- Clickthrough — Enables a guest to get access to the Internet without authentication. You can configure your portal page to force guest users to accept terms and conditions before they can get access to the Internet. For more information, see Configure the Clickthrough Plug-in.
- Social — Allows guests to authenticate with their social media account credentials. For more information, see Configure Portal Social Media Plug-Ins and Create Social Media Plug-In Apps.
- Username/Password — Helps you maintain a private list of guest users who can access to your Wi-Fi network. Guests can also self-register for access. For more information, see Configure the Username/Password Plug-in.
- Passcode through SMS — Enables a guest user to receive an Internet access code in an SMS text message. The guest user must provide a mobile phone number on the portal page. For more information, see Configure the Passcode Through SMS Plug-in.
- Web Form — An enhanced type of clickthrough. Guest users must complete a form on the portal page before Internet access is allowed. For more information. see Configure the Webform Plug-in.
- External RADIUS — Guests users are authenticated through an external RADIUS server. The RADIUS plug-in cannot be used with any other plug-in. If the RADIUS plug-in is selected, other plug-ins will be disabled. For more information on how to add RADIUS servers, see Configure RADIUS Servers in Discover.
- Custom (SAML) — Guests users are authenticated with an SAML-based authentication server by an identity provider (IdP). For more information, go to Configure the SAML Plug-in.
- Third-Party Hosted — Use a third-party hosted captive portal page or Wi-Fi Cloud portal campaign that you have created with Engage and Analyze.
- You must specify the Splash Page URL and Shared Secret for the portal page. You can find this information in the portal configuration in Analyze or on your third-party server. For more information, see Third-Party Hosted AP Captive Portal.
- When you use a third-party hosted server with RADIUS authentication, the guest user is authenticated by a RADIUS server when they log in to the portal. For more information, see Third-Party Hosted AP Captive Portal with RADIUS Authentication.
- Skip Splash Page — If you select this option, guest Wi-Fi users only see the Splash Page the first time they get access to the Internet. On subsequent attempts to connect to the Internet in the specified Application Usage Time, the Splash Page does not appear and users are automatically connected to the Internet with the same authentication method specified for their previous connection.
- HTTPS Redirection — Securely redirect a user to the portal when the user tries to access an HTTPS site. If HTTPS Redirection is not enabled, the client is not redirected to the captive portal if they first browse to an HTTPS site. Type the organization details (Common Name, Organization, and Organization Unit) to use as the information for HTTPS redirection purposes.
- Websites that users can access before login — Specify a list of web sites (walled garden) that guest users can access before they authenticate to the captive portal. This list should include services that might be required by the client to login, such as authentication sites, social media logins, and content servers.
- Redirect URL — Specify the URL to redirect to after the user authenticates on the portal page. If you leave this option undefined, the browser is redirected to the original URL requested when the portal page was displayed.
- Login Timeout — Specify the time, in minutes, during which a wireless user can get access to the guest network after they submit the portal page. After the timeout, access to the guest network is blocked and the portal page is displayed again. The user must submit the portal page to regain access to the guest network. If the user disconnects and reconnects to the guest network before the session times out, the user does not have to enter their credentials on the splash page.
- Blackout Time — Specify the time, in minutes. for which a user is not allowed to log in after the previous successful session timed out. For example, if the session timeout is one hour and the blackout time is 30 minutes, a user will be timed out one hour after a successful login. After this point, the user cannot log in again for 30 minutes. After 30 minutes, the user can log in again.
- Detect when Internet connection is down and inform guest users — Notify guests when the Internet is temporarily unavailable on the guest SSID. When the AP detects that Internet connectivity is not available from the guest VLAN, it automatically redirects all HTTP requests from guest users to a splash page. A message is displayed that the Internet is temporarily unavailable.
- Smart Client Load Balancing — Smart Client Load Balancing efficiently manages and distributes the clients across APs within the same band. For example, in high-density environments, a client might find more than one AP in the vicinity with good signal strength. As a result, a number of clients could connect to an AP with the best signal strength and cause performance issues and degradation of the wireless network. Smart Client Load Balancing prevents this issue. For more information on load balancing parameters, see Configure Radio Settings.
- Smart Steering — Smart Steering addresses the problems that occur when a roaming client moves away from the AP that it is currently associated with and stays connected to the AP although there is a better AP in the vicinity. Smart Steering proactively steers the client to a better AP for a better connection. For more information on steering parameters, see Configure Radio Settings.
- Minimum RSSI Based Association — You can define the minimum RSSI required for a client to associate to an AP. This helps with roaming issues where a roaming client may try to connect to an AP several times because of the weak signal. If the client tries to connect too many times, the client may be classified as a desperate client and could be allowed to associate with the AP. You can configure minimum RSSI settings with the Steering RSSI Threshold device setting for an AP. For more information, see Configure Device Settings.
- Band Steering — When you configure an SSID in both the 2.4 GHz and 5 GHz bands, clients in one of these bands can be steered towards the other band to balance the load on the AP. Band Steering helps to evenly distribute the wireless clients between the two bands. When you select the Enforce Steering option, 802.11ac APs can process additional management packets to make sure a client is always disconnected from the 2.4 GHz radio and steered to the 5 GHz radio when the client reconnects to the AP. This option is ignored for APs that do not support 802.11ac. For more information on band steering settings, see Configure Radio Settings.
- 802.11k Neighbor List — Provides wireless clients with nearby AP information that helps clients make fast roaming decisions. Works with the 802.11w fast roaming protocol to help provide seamless roaming between access points to prevent interruptions to streaming applications. You can also optionally enable a search in both 2.4 and 5 GHz bands.
- 802.11v BSS Transition — Enables an AP to warn an associated client that the client will be disconnected from this AP because there are APs with a stronger signal to connect to. Works with the 802.11w fast roaming protocol to help provide seamless roaming between access points to prevent interruptions to streaming applications. You can enable the Disassociation Imminent option and configure the Disassociation Timer field. This is the time after which the client will be disconnected from the AP. The Disassociation Timer is expressed in number of beacon intervals. The range of the Disassociation Timer should be between 10 to 3000 TBTT (Target Beacon Transmission Time). When the Disassociation Timer reaches zero, then the client can be disassociated based on the Force Disconnection option.
- 802.11r — If WPA2 is selected, you can also enable 802.11r. 802.11r, or Fast Transition (FT), allows clients to reestablish security and QoS parameters before they associate with a new AP, significantly reducing the interruption that the client experiences during the transition. Select Over the DS if you want to set a preference for clients to roam by using the Over the Distribution System (DS) mode of roaming. Client devices govern the mode of roaming from one AP to another. When you do not select Over the DS, clients roam over the air. Note that this is only a preference. A client can roam over the air irrespective of the preference. Select Mixed Mode to allow both 802.11r compatible and 802.11r non-compatible clients to connect to the SSID.
- Proxy ARP and NDP — The AP filters downstream ARP (IPv4) and NDP (IPv6) packets and also responds as appropriate on behalf of wireless clients to conserve wireless bandwidth. The Disable DGAF option (Downstream Group-Addressed Forwarding) drops all multicast and broadcast packets from the wired to the wireless network. It is only used with Hotspot 2.0.
- Broadcast and Multicast Control — Many enterprise deployments prevent excessive and unnecessary broadcast and multicast traffic from being forwarded from the wired side to the wireless side of an access point. You can block broadcast and multicast packets on your wireless network and create exemptions for specific applications.
- Enable Block Wireless to Wired to block broadcast and multicast traffic from the wireless side to the wired side.
- Enable Allow Bonjour to allow the Apple Bonjour protocol for services such as Apple AirPlay and AirPrint.
- You can add the protocol details for applications that must be allowed to use broadcast/multicast packets to theExemption List.
- IGMP Snooping — IGMP Snooping listens to IGMP (Internet Group Management Protocol) network traffic to track connections that require IP multicast streams, such as video streaming traffic. Enable snooping for an SSID to block multicast packets if no client joins the multicast group to optimize streaming traffic. You can create exceptions for specific IP addresses. Packets with multicast IP addresses in the exception list are not dropped even if no client joins the multicast group.
- Limit maximum number of simultaneous associations to — Specify the maximum number of clients per radio that can associate with an SSID.
- Limit the maximum upload bandwidth on the SSID to — Type the data rate (0-1024 Kbps or Mbps) to restrict the upload bandwidth for the SSID.
- Limit the maximum download bandwidth on the SSID to — Type the data rate (0-1024 Kbps or Mbps) to restrict the download bandwidth for the SSID.
- Limit the maximum upload bandwidth per user to — Type the data rate (0-1024 Kbps or Mbps) to restrict the upload bandwidth for each user.
- Limit the maximum download bandwidth per user to — Type the data rate (0-1024 Kbps or Mbps) to restrict the download bandwidth for each user.
- QoS — Enable Quality of Service (QoS) controls. QoS ensures that applications or traffic that require higher priority get the required priority. The service guarantee is met by allocating adequate bandwidth based on the QoS priority. Maintaining a high QoS helps with streaming multimedia applications such as voice over IP, video, and online games. For more information, see Configure QoS Settings.
- Enforce WMM Admission Control — Enforce the admission control parameters configured in the advanced radio settings. For more information, see Configure Radio Settings. WMM Admission Control settings configured in the radio settings override any QoS settings configured in the SSID.
- Set the data rate for multicast, broadcast and management traffic to — Type the data rate (0-54 Mbps) for the AP. This option controls the data rate at which broadcast/multicast packets and beacons are sent. Increasing the basic rate of the AP does reduce transmission airtime, but it also reduces the effective coverage area. This could cause issues for a client if the AP coverage for the client cannot support that data rate. For example, real-time streaming of audio and video are applications that commonly use multicast packets for delivery. If clients have problems receiving multicast packets because the AP coverage is not strong enough to support higher data rates, they experience latency with audio and video streams.
- Limit the minimum unicast traffic data rate to — Specify the minimum unicast data rate for AP to client communication. Only adjust these values if legacy 802.11a/b/g clients cannot connect to Wi-Fi networks that offer higher data rates.
- Limit the maximum unicast traffic data rate to — Specify the maximum unicast data rate for AP to client communication. Only adjust these values if legacy 802.11a/b/g clients cannot connect to Wi-Fi networks offering higher data rates. Enable the Apply to all clients including 802.11n and 802.11ac option to apply the specified maximum data rate for unicast traffic to all 802.11n and 802.11ac clients.
When you enable a VLAN Extension on the AP225W, the VLAN Extension takes precedence over the Wired Extension configuration. For more information see Configure Device Settings.
A captive portal is a web page to which a client is redirected when they connect to a guest SSID. The client can gain access to the Internet after they successfully authenticate or accept the terms of use on the portal page. This enables you to restrict wireless connectivity (such as Internet-only connectivity) for guest wireless clients.
Cloud-hosted Analyze and Engage captive portal features require a Total Wi-Fi AP subscription.
You can configure several RF optimization features for your Wi-Fi network. For more information, see Configure RF Optimization Settings.
Use SSID scheduling to make an SSID available only for a limited time period, or only for a limited number of hours in the day. For example, you might want to keep an SSID available only during working hours. Define the duration for which you want to make the SSID available (Now to Forever or Custom), then define the schedule in the day and time grid.
SSID scheduling is performed based on the time zone of the location where the SSID configuration is applied.
To effectively utilize your network bandwidth, you can use traffic management and QoS (Quality of Service). For example, you can configure an upload and download limit for the network, restrict the number of client associations, and define QoS parameters. You can use one or more of these methods depending on the network traffic, the applications used on the SSID, and your AP model.
For example, You can restrict downloads for users connected to your Guest SSID so they do not slow down the rest of the network, or apply limits to all users across your entire wireless network. The values you define depend on the bandwidth available on your Internet connection, how many concurrent clients are connected and the type and size of traffic, and if your users require audio/video streaming or other high-bandwidth applications.
The value for minimum and maximum unicast data rates cannot be a combination of 6 and 9 Mbps (for example, 6 Mbps minimum, 9 Mbps maximum, or any combination of these values), or you will be unable to save the configuration and broadcast the SSID. For more information, go to Cannot save Wi-Fi configuration or broadcast SSID if the maximum and minimum unicast data rates are in combination of 6 and 9 Mbps in the WatchGuard Knowledge Base.