Applies To: Locally-managed Fireboxes
This topic explains how to edit an existing Mobile VPN with IKEv2 configuration. You can configure:
- Address and certificate settings
- Networking settings — Full or split tunnel
- Virtual IP address pool
- Authentication servers
- Users, groups, and enforcement
- Certificates
- Phase 1 and 2 settings
- DNS and WINS
- Timeout setting for user authentication
- DF bit options
- Disable Mobile VPN with IKEv2
If you have not already configured Mobile VPN with IKEv2, we recommend that you use the Setup Wizard. The Setup Wizard helps you to set up a basic Mobile VPN with IKEv2 configuration. For more information, go to Use the WatchGuard IKEv2 Setup Wizard.
- (Fireware v12.3 or higher) Select VPN > Mobile VPN.
- In the IKEv2 section, select Configure.
The Mobile VPN with IKEv2 page opens. - (Fireware v12.2.1 or lower) Select VPN > Mobile VPN with IKEv2.
The Mobile VPN with IKEv2 page opens. - Click Configure.
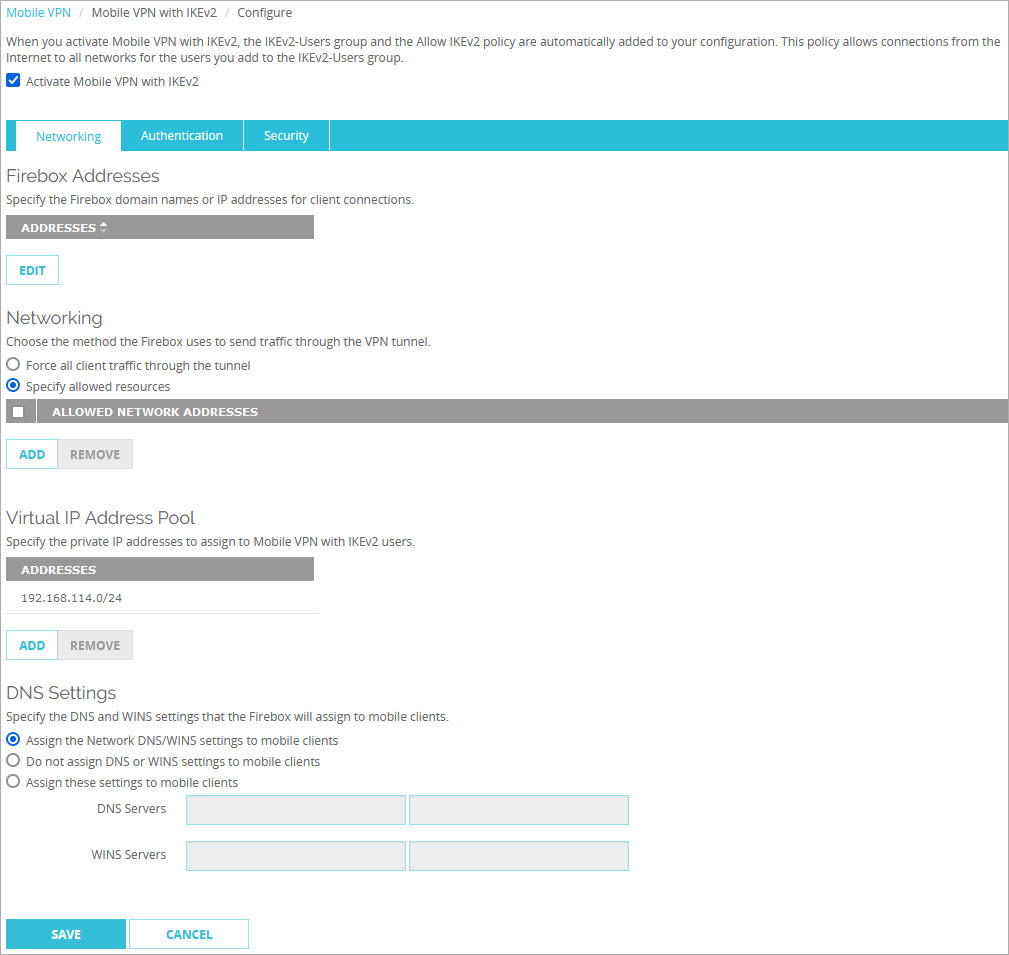
- Select the Activate Mobile VPN with IKEv2 check box if Mobile VPN with IKEv2 is not already activated.
- Use the information in the next sections to configure the Mobile VPN with IKEv2 settings.
- (Fireware v12.3 or higher) Select VPN > Mobile VPN > IKEv2.
The Mobile VPN with IKEv2 Configuration dialog box opens. - (Fireware v12.2.1 or lower) Select VPN > Mobile VPN > IKEv2 > Configure.
The Mobile VPN with IKEv2 Configuration dialog box opens.
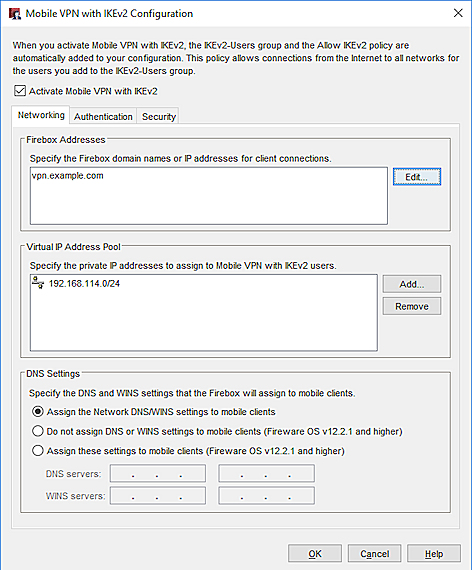
- Select the Activate Mobile VPN with IKEv2 check box if Mobile VPN with IKEv2 is not already activated.
- Use the information in the next sections to configure the Mobile VPN with IKEv2 settings.
Edit Address and Certificate Settings
On the Networking tab, in the Firebox Addresses section, specify an IP address or domain name for connections from Mobile VPN with IKEv2 users. If your Firebox is behind a NAT device, you must specify the public IP address or domain name of the NAT device.
Edit the Networking Settings
On the Networking tab, in the Networking section, you can select how the Firebox sends traffic through the VPN tunnel. Select one of these options:
Force all client traffic through the tunnel
This option sends all traffic from VPN clients through the VPN tunnel.
Traffic destined for the Internet and your local network goes through your Firebox policies, which provide consistent security but reduced performance. This option is also known as full tunneling or default route. This is the default setting.
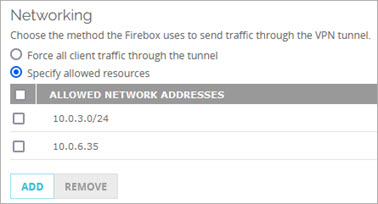
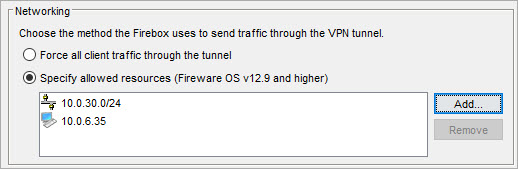
Specify allowed resources (Fireware v12.9 or higher)
This option allows Mobile VPN with IKEv2 users to connect to only specified resources on your internal networks. This option is also known as split tunneling.
A split tunnel offers better performance than a full tunnel because the Firebox processes less traffic. However, a split tunnel can affect security because the Firebox does not inspect traffic sent to the Internet from VPN clients or traffic sent to the remote VPN client network.
After you specify allowed resources in the Mobile VPN with IKEv2 configuration:
- The allowed resources are added to new Firebox security policies.
- The IPSec SA still shows the 0.0.0.0/0 traffic selector, but traffic is controlled by the security policy.
- The Firebox drops traffic that does not match the policies.
- Select VPN > Mobile VPN > IKEv2.
- In the IKEv2 section, select Configure
- Select Force all client traffic through the tunnel.
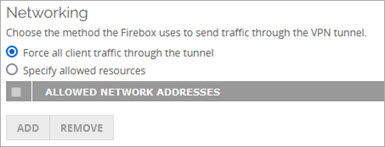
- Select VPN > Mobile VPN > IKEv2.
- In the Networking section, select Force all client traffic through the tunnel.

- Select VPN > Mobile VPN > IKEv2.
- In the IKEv2 section, select Configure
- Select Specify allowed resources.
- Click Add.
The Add Allowed Resources dialog box opens. - From the Choose Type drop-down list, select Host IPv4 or Network IPv6.
- If you selected Host IPv4, in the Host IP text box, enter the IP address of the host.
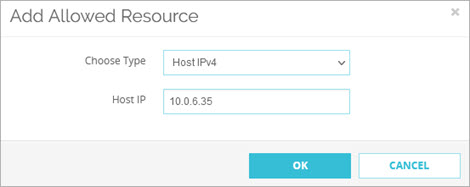
- If you selected Network IPv4, in the Network IP text box, enter the network IP address.
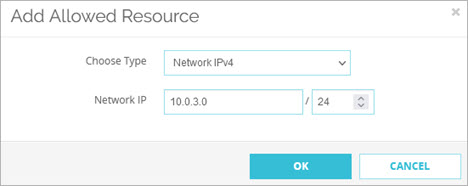
-
Click OK.
The IP addresses that you entered appear in the Allowed Network Addresses list.
- To add another allowed resource, click Add.
- To remove one or more resources, select the check box adjacent to each resource and click Remove.
If you edit the list of allowed resources after you download and install the client configuration files on user devices, download updated client configuration files from the Firebox and reinstall those on user devices. If you remove an allowed host or network from the list, but you do not install updated client configuration files on user computers, VPN clients can initiate traffic to that host or network, but the Firebox denies the traffic.
- Select VPN > Mobile VPN > IKEv2.
- In the Networking section, select Specify allowed resources.
- Click Add.
The Add Address dialog box opens. - From the Choose Type drop-down list, select Host IPv4 or Network IPv6.
- If you selected Host IPv4, in the Host IP text box, enter the IP address of the host.
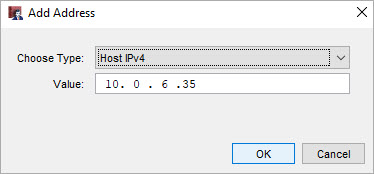
- If you selected Network IPv4, in the Network IP text box, enter the network IP address.
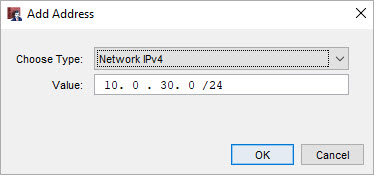
-
Click OK.
The IP addresses that you entered appear in the Allowed Network Addresses list.
If you edit the list of allowed resources after you download and install the client configuration files on user devices, download updated client configuration files from the Firebox and reinstall those on user devices. If you remove an allowed host or network from the list, but you do not install updated client configuration files on user computers, VPN clients can initiate traffic to that host or network, but the Firebox denies the traffic.
Edit the Virtual IP Address Pool
On the Networking tab, the Virtual IP Address Pool shows the internal IP addresses that are used by Mobile VPN with IKEv2 users over the tunnel. The virtual IP address pool must contain at least two IP addresses. By default, the Firebox assigns addresses in the 192.168.114.0/24 range to Mobile VPN with IKEv2 clients.
We recommend that you do not use the private network ranges 192.168.0.0/24 or 192.168.1.0/24 on your corporate or guest networks. These ranges are commonly used on home networks. If a mobile VPN user has a home network range that overlaps with your corporate network range, traffic from the user does not go through the VPN tunnel. To resolve this issue, we recommend that you Migrate to a New Local Network Range.
For more information about virtual IP addresses, go to Virtual IP Addresses and Mobile VPNs.
To add to the virtual IP address pool:
- Click Add.
The Add Address Pool dialog box opens. - From the Choose Type drop-down list, select Network IPv4 or Host IPv4.
- In the adjacent text box, type an IP address or network IP address.
Edit Authentication Settings
On the Authentication tab, you can configure authentication servers and the authorized users and groups.
If your users authenticate to network resources with Active Directory, we recommend that you configure RADIUS authentication so the IKEv2 VPN can pass through Active Directory credentials.
In Fireware v12.7 or higher, you can configure the Firebox to forward authentication requests for IKEv2 VPN users directly to AuthPoint, the cloud-based multi-factor authentication (MFA) solution from WatchGuard. After you configure the required settings in AuthPoint, AuthPoint appears in the authentication server list on the Firebox. In the Mobile VPN with IKEv2 configuration, you must select AuthPoint as an authentication server. For more information about multi-factor authentication for Mobile VPN with IKEv2, go to About Mobile VPN with IKEv2 User Authentication.
Configure Authentication Servers (Fireware v12.5 or Higher)
- Select the Authentication tab.
- From the Authentication Servers drop-down list, select a server.
- Click Add.
- Repeat Steps 2–3 to add more servers.
- To make a server the primary server, select it and click Move Up until it appears first in the list.
- Select the Authentication tab.
- From Authentication Servers list, select one or more servers.
- To make a server the primary server, select it and click Make Default.
Configure Authentication Servers (Fireware v12.4.1 or Lower)
- Select the Authentication tab.
- From Authentication Servers list, select one or more servers.
- If you select both Firebox-DB and RADIUS, you can select Set as default server to make RADIUS the default authentication server.
- Select the Authentication tab.
- From Authentication Servers list, select one or more servers.
- If you select both Firebox-DB and RADIUS, you can select Set as default server to make RADIUS the default authentication server.
Configure Users, Groups, and Network Access Enforcement
If you use Firebox-DB for authentication, you must use the IKEv2-Users group that is created by default. You can add the names of other groups and users that use Mobile VPN with IKEv2. For each group or user you add, you can select the authentication server where the group exists or select Any if that group exists on more than one authentication server. The group or user name you add must exist on the authentication server. The group and user names are case sensitive and must be the same as the name on your authentication server. For more information about user authentication, go to About Mobile VPN with IKEv2 User Authentication.
To limit mobile VPN connections to devices that follow corporate policy, you can use network access enforcement. Before you enable network access enforcement for groups specified in the Mobile VPN with IKEv2 configuration, enable and configure network access enforcement for your locally-managed Firebox at Subscription Services > Network Access Enforcement (Fireware v12.9 or higher). For more information, go to Network Access Enforcement Overview.
In Fireware v12.5.4 to v12.8.x, this feature was called TDR Host Sensor Enforcement. TDR is now end of life and cannot be used for network access enforcement. In the user interface, this feature is no longer functional but is required by the configuration schema. To enable network access enforcement, we recommend that you upgrade to EDR Core. For more information, go to this Knowledge Base article: Host Sensor Upgrade to Endpoint Security.
For information on how to configure network access enforcement for cloud-managed Fireboxes, go to Configure Network Access Enforcement for a Cloud-Managed Firebox.
- In the Users and Groups section, select users and groups for Mobile VPN with IKEv2.
- To add a new Firebox-DB user or group, select Firebox-DB from the first drop-down list.
- To add a new RADIUS user or group, select Any from the first drop-down list.
- From the second drop-down list, select User or Group.
- Click Add.
The Firebox User, Firebox Group, or Add User or Group dialog box opens. - To add a new Firebox-DB user, follow Steps 5–14 in the Define a New User for Firebox Authentication topic.
- To add a new Firebox-DB group, follow Steps 4–9 in the Define a New Group for Firebox Authentication topic.
- To add new users and groups for third-party authentication, follow Steps 4–11 in the Use Users and Groups in Policies topic.
- (Optional) To apply enforcement settings to Mobile VPN with IKEv2 groups:
- Select the check box for a group.
- In Fireware v12.9 or higher, in the Network Access Enforcement column, select Yes.
- To disable enforcement for a group, select the check box for that group and select No.
In the Users and Groups section, you can select users and groups for Mobile VPN with IKEv2.
To add a new Firebox-DB user:
- Click New.
- Select Firebox-DB User/Group.
The Authentication Servers dialog box opens. - To add a user, in the Users section, click Add.
The Setup Firebox User dialog box opens. - Specify the user name, password, and timeout settings.
- (Optional) Specify login limit settings for the user.
- To add a new Firebox-DB group, in the User Groups section, click Add.
The Setup Firebox Group dialog box opens. - Specify the name and login limit settings for the group.
- (Optional) To apply enforcement settings to Mobile VPN with IKEv2 groups:
- Select the check box for a group.
- In Fireware v12.9 or higher, in the Network Access Enforcement column, select Yes. .
- To disable enforcement for a group, select the check box for that group and select No.
To add a new RADIUS user or group:
- Click New.
- The Add User or Group dialog box opens.
- Specify the group name.
- (Optional) Specify login limit settings for the group.
- (Optional) In Fireware v12.5.4, you can
- (Optional) To apply enforcement settings to Mobile VPN with IKEv2 groups:
- Select the check box for a group.
- In Fireware v12.9 or higher, select the Network Access Enforcement check box. In
- To disable enforcement for a group, select the check box for that group and select No.
For more information about how to add Firebox-DB users, go to Define a New User for Firebox Authentication.
For more information about how to add Firebox-DB groups, go to Define a New Group for Firebox Authentication.
For more information about how to add RADIUS users and groups, go to Use Users and Groups in Policies.
For more information about network access enforcement, go to Network Access Enforcement Overview.
Configure a Certificate for Authentication
You can select a Firebox certificate or a third-party certificate for Mobile VPN with IKEv2 authentication. Firebox and third-party certificates have these requirements:
- Extended Key Usage (EKU) flags "serverAuth"
- IP address or DNS name as a Subject Alternative Name value
In Fireware v12.5 or higher, the Firebox supports ECDSA (EC) certificates for Mobile VPN with IKEv2. Your IKEv2 client must also support EC certificates. Support varies by operating system. For more information, go to About Elliptic Curve Digital Signature Algorithm (ECDSA) certificates.
To select a certificate for authentication:
- Click the Security tab.
- To specify a certificate for authentication, click Edit.
The Firebox Address and Certificate Settings dialog box opens. - In the Type drop-down list, select Firebox-Generated Certificate or Third-Party Certificate.
Configure the Phase 1 and 2 Settings
To configure the Phase 1 settings, select VPN > IKEv2 Shared Settings. For more information about IKEv2 Shared Settings, go to Configure IKEv2 Shared Settings.
The IPSec Phase 2 proposals used for Mobile VPN with IKEv2 are the same proposals you configure to use with an IPSec branch office VPN. If you want to configure a new Phase 2 proposal to use with Mobile VPN with IKEv2, you must add it in the Phase 2 Proposals page. Then you can add it to the Mobile VPN with IKEv2 configuration.
- (Fireware v12.3 or higher) Select VPN > Mobile VPN > Configure.
- (Fireware v12.2.1 or lower) Select VPN > Mobile VPN with IKEv2 > Configure.
- Select Security > Phase 2.
- Select the Phase 2 Settings tab.
- Select Enabled Perfect Forward Secrecy to enable Perfect Forward Secrecy (PFS).
- From the adjacent drop-down list, select a Diffie-Hellman Group.
- In the IPSec Proposals section, select an existing proposal from the drop-down list.
- Click Add.
- To add a new proposal, select VPN > Phase 2 Proposals. For more information about Phase 2 Proposals, go to Add a Phase 2 Proposal.
- Click Save.
- (Fireware v12.3 or higher) Select VPN > Mobile VPN > IKEv2.
- (Fireware v12.2.1 or lower) Select VPN > Mobile VPN > IKEv2 > Configure.
- Select Security > Phase 2.
- Select the Phase 2 Settings tab.
- Select the PFS check box to enable Perfect Forward Secrecy (PFS).
- From the adjacent drop-down list, select a Diffie-Hellman Group.
- In the IPSec Proposals section, select an existing proposal from the drop-down list.
- Click Add.
- To add a new proposal, select VPN > Phase 2 Proposals. For more information about Phase 2 Proposals, go to Add a Phase 2 Proposal.
- Click OK.
Configure the DNS and WINS Settings
In Fireware v12.2.1 or higher, you can specify DNS and WINS servers in the Mobile VPN with IKEv2 configuration.
In Fireware v12.9 or higher, the WatchGuard automatic configuration script includes a domain name suffix if you specify one in the network (global) DNS settings on the Firebox. In the Mobile VPN with IKEv2 configuration on the Firebox, you must select Assign the Network DNS/WINS settings to mobile clients. Mobile VPN clients inherit the domain name suffix.
For information about how to configure the network (global) DNS settings on the Firebox, go to Configure Network DNS and WINS Servers.
For detailed information about DNS settings for Mobile VPN with IKEv2, go to Configure DNS and WINS Servers for Mobile VPN with IKEv2.
In Fireware v12.8.2 or earlier, Mobile IKEv2 clients do not inherit a domain name suffix from the Firebox. To manually configure a domain name suffix in Windows, go to Configure DNS server and suffix settings in IKEv2 and L2TP VPN clients in the WatchGuard Knowledge Base.
- Select VPN > Mobile VPN with IKEv2.
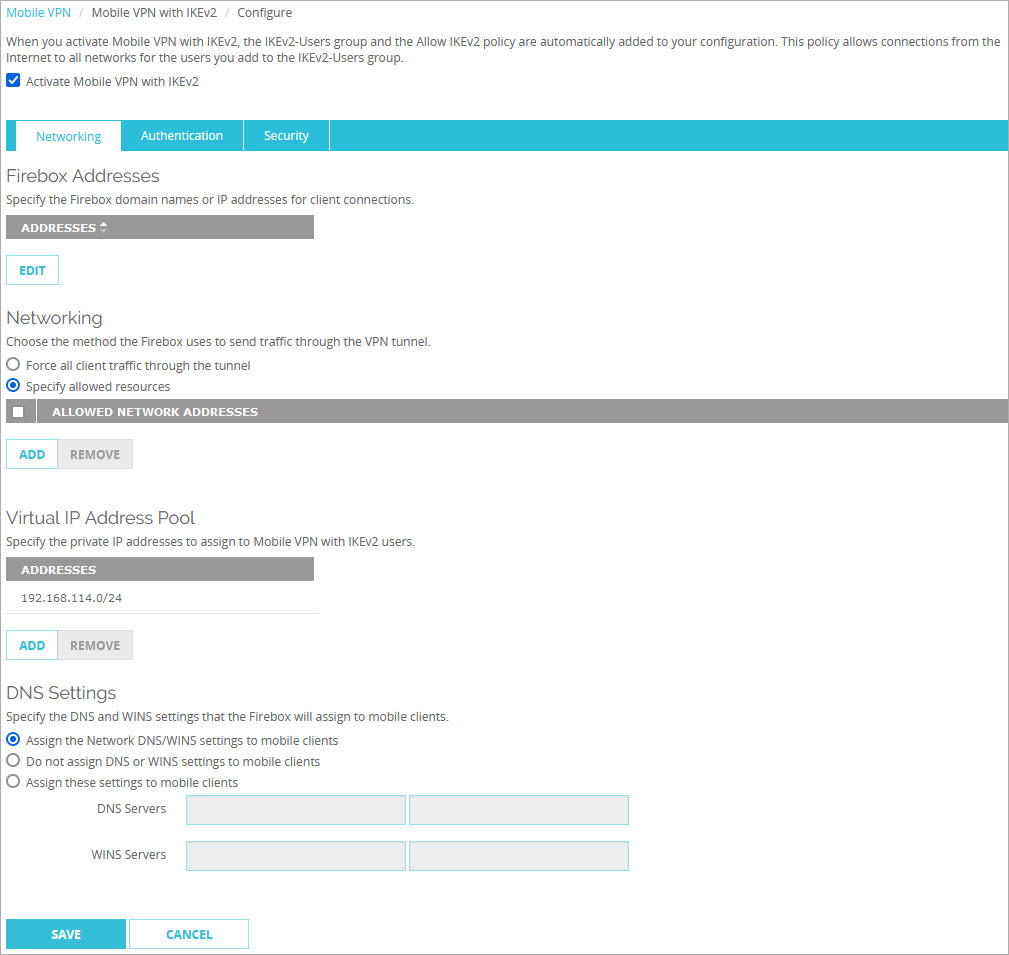
- In the DNS Settings section, select one of these options:
Assign the network DNS/WINS settings to mobile clients
If you select this option, mobile clients receive the first two DNS servers and the first two WINS servers you specify at Network > Interfaces > DNS/WINS. For example, if you specify the DNS server 10.0.2.53in the Network DNS/WINS settings, mobile VPN clients use 10.0.2.53as a DNS server. Although you can specify up to three Network DNS servers, mobile VPN clients use only the first two in the list.
By default, the Assign the Network DNS/WINS Server settings to mobile clients setting is selected for new mobile VPN configurations.
In Fireware v12.9 or higher, if you select Specify allowed resources, Mobile IKEv2 clients inherit the domain name suffix specified in the Network DNS server settings.
Do not assign DNS or WINS settings to mobile clients
If you select this option, clients do not receive DNS or WINS settings from the Firebox.
Assign these settings to mobile clients
If you select this option, mobile clients receive the DNS server and WINS servers you specify in this section. For example, if you specify 10.0.2.53 as the DNS server, mobile clients use 10.0.2.53 as the DNS server.
You can specify up to two DNS server IP addresses and up to two WINS server IP addresses. You cannot specify a domain name suffix.
- Click Save.
- Select VPN > Mobile VPN > IKEv2 > Configure.
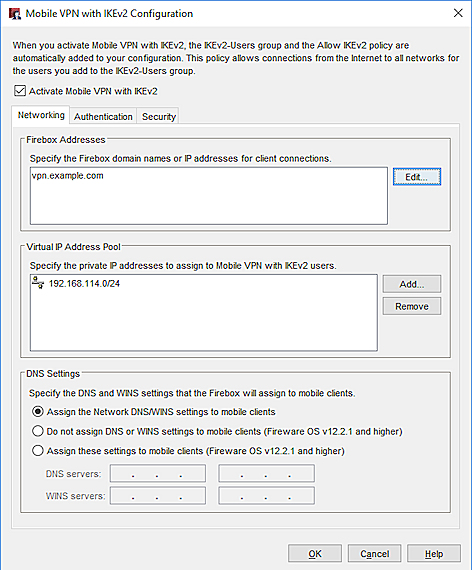
- In the DNS Settings section, select one of these options:
Assign the network DNS/WINS settings to mobile clients
If you select this option, mobile clients receive the first two DNS servers and the first two WINS servers you specify at Network > Interfaces > DNS/WINS. For example, if you specify the DNS server 10.0.2.53in the Network DNS/WINS settings, mobile VPN clients use 10.0.2.53as a DNS server. Although you can specify up to three Network DNS servers, mobile VPN clients use only the first two in the list.
By default, the Assign the Network DNS/WINS Server settings to mobile clients setting is selected for new mobile VPN configurations.
In Fireware v12.9 or higher, if you select Specify allowed resources, Mobile IKEv2 clients inherit the domain name suffix specified in the Network DNS server settings.
Do not assign DNS or WINS settings to mobile clients
If you select this option, clients do not receive DNS or WINS settings from the Firebox.
Assign these settings to mobile clients
If you select this option, mobile clients receive the DNS server and WINS servers you specify in this section. For example, if you specify 10.0.2.53 as the DNS server, mobile clients use 10.0.2.53 as the DNS server.
You can specify up to two DNS server IP addresses and up to two WINS server IP addresses. You cannot specify a domain name suffix.
- Click OK.
In Fireware v12.2 or lower, you cannot configure DNS and WINS settings in the Mobile VPN with IKEv2 configuration. Clients automatically receive the DNS and WINS servers specified in the Network (global) DNS/WINS settings on the Firebox. The domain name suffix is not inherited. Although you can specify up to three Network DNS servers, mobile VPN clients use only the first two in the list. For information about the Network DNS/WINS settings, go to Configure Network DNS and WINS Servers.
Timeout Setting for User Authentication
In Fireware v12.5.4 or higher, you can specify a custom timeout value for Mobile VPN with IKEv2 EAP user authentication. You might specify a custom timeout value if your mobile IKEv2 users authenticate with multi-factor authentication (MFA) and require more time to respond to MFA prompts. The default timeout value is 20 seconds.
Before you change the user authentication timeout setting, consider other timeout settings that might affect Mobile VPN with IKEv2:
- Firebox RADIUS settings—The default timeout setting is 30 seconds (10 seconds and 3 retries). If you specify a Mobile VPN with IKEv2 user authentication timeout greater than 30 seconds, and your mobile IKEv2 users authenticate through RADIUS, you must also increase the default RADIUS timeout setting so that it is greater than 30 seconds.
- AuthPoint—The default timeout setting is 60 seconds and cannot be changed. If your mobile IKEv2 users authenticate through AuthPoint, the user authentication timeout for Mobile VPN with IKEv2 must not exceed 60 seconds.
- Microsoft NPS (RADIUS server)—The default timeout is 30 seconds.
For more information about timeout settings for mobile IKEv2 users who authenticate through AuthPoint and RADIUS, go to Firebox Mobile VPN with IKEv2 Integration with AuthPoint.
Configure the timeout setting
You must use Fireware CLI to configure this setting. Use this command:
WG#diagnose vpn "/ike/param/set ikev2_eap_timeout=[xxx] action=now"
For example, to configure a custom timeout value of 40 seconds, specify the following:
WG#diagnose vpn "/ike/param/set ikev2_eap_timeout=40 action=now"
You can specify a timeout value between 20 and 300 seconds. If you specify action=now, you do not have to restart the Firebox for this setting to take effect and the tunnel will not be rekeyed. The new timeout value that you specify will apply to new IKEv2 connections.
Configure DF Bit Options
The Don't Fragment (DF) bit is a flag in the header of a packet. In Fireware v12.8 or higher, you can use the CLI to specify a custom DF bit option for Mobile VPN with IKEv2 client connections.
The DF bit can be a value between 0 and 2, which corresponds to these options:
- 0 — Copy (default). This option applies the DF bit setting of the original frame to the IPSec encrypted packet.
- 1 — Set. This option instructs the Firebox to not fragment the frame regardless of the original bit setting.
- 2 — Clear. This option breaks the frame into pieces that can fit in an IPSec packet with the ESP or AH header, regardless of the original bit setting.
For example, to clear the DF bit, specify the following:
WG#diagnose vpn "/ike/param/set mobile_ikev2_dfbit=2 action=now"
If you specify action=now, you do not have to restart the Firebox for this setting to take effect, and the tunnel will not be rekeyed. The new timeout value that you specify will apply to new IKEv2 connections.
You cannot configure the DF bit setting in Fireware Web UI or Policy Manager.
Disable Mobile VPN with IKEv2
You can disable a Mobile VPN with IKEv2 configuration from Fireware Web UI or Policy Manager.
- Select VPN > Mobile VPN.
- In the IKEv2 section, click Configure.
The Mobile VPN with IKEv2 Configuration page opens. - Clear the Activate Mobile VPN with IKEv2 check box.
- Click Save.
- Select VPN > Mobile VPN > IKEv2.
The Mobile VPN with IKEv2 Configuration dialog box opens. - Clear the Activate Mobile VPN with IKEv2 check box.
- Click OK.
Use the WatchGuard IKEv2 Setup Wizard
Configure iOS and macOS Devices for Mobile VPN with IKEv2
Configure Windows Devices for Mobile VPN with IKEv2
Configure Android Devices for Mobile VPN with IKEv2
Configure Client Devices for Mobile VPN with IKEv2
Internet Access Through a Mobile VPN with IKEv2 Tunnel
Certificates for Mobile VPN with IKEv2 Tunnel Authentication