Applies To: Locally-managed Fireboxes
Firebox Authentication, also known as Firebox-DB authentication, enables you to store on your Firebox the user accounts that you create to give your users access to your network. To make sure that the credentials for each user account stored on your Firebox are secure, the passphrase that you specify for each user account is encrypted with an NT hash in the device configuration file. When the configuration file is exported to a clear text file (such as for communication between the Firebox and a Fireware device configuration management tool), the passphrase is further encrypted with an AES key wrap.
Create User Accounts
You can create the user accounts for Firebox Authentication and specify which users can authenticate to your Firebox. You can also specify whether the user names that you define in the Firebox internal database are case sensitive. When case-sensitivity is enabled, users must type their user names with the same capitalization you used when you defined the user accounts.
Minimum Passphrase Length
In Fireware v12.2.1 or higher, you must specify the minimum number of characters for a passphrase. You can specify a value between 8 and 32 characters. Longer passphrases are more secure.
The minimum passphrase length setting applies to:
- New Firebox-DB accounts added in the Firebox-DB server, Access Portal, and Mobile VPN with IKEv2 configurations
- New Firebox management accounts (admin and status accounts)
- New Support Access accounts
This setting controls only the minimum passphrase length. The maximum passphrase length is 32 characters and cannot be changed.
Passphrases for current Firebox-DB users are not changed when you upgrade to Fireware v12.2.1 or higher, but any new passphrases selected for current accounts must meet the minimum passphrase requirement. For example, if you unlock a user account and select the option to reset the passphrase, the new passphrase must meet the minimum length requirement.
Allow Unlimited Concurrent Login Sessions
By default, the Allow unlimited concurrent firewall authentication logins from the same account option is selected. This option allows users to authenticate to the authentication server more than once at the same time. This is useful for guest accounts or in laboratory environments.
Global authentication settings for concurrent user sessions do not apply to mobile VPN sessions.
Limit Login Sessions
To restrict your users to a specific number of authenticated sessions, select Limit concurrent user sessions to. If you select this option, you can specify the number of times your users can use the same credentials to log in to one authentication server from different IP addresses. When a user is authenticated and tries to authenticate again, you can select whether the first user session is terminated when an additional session is authenticated, or if the additional sessions are rejected.
You can configure login session limits at the global, group, and user level.
- User settings take precedence over the group and global settings.
- If user's login session limits are not configured, group settings take precedence, if configured.
- If a user belongs to more than one group, the settings for the first group in the user's group list takes precedence.
- If user or group login session limits are not configured, the global settings are used.
- Select Authentication > Servers.
The Authentication Servers page opens. - From the Authentication Servers list, select Firebox-DB.
The Firebox page opens with the Users and Groups tab selected by default.
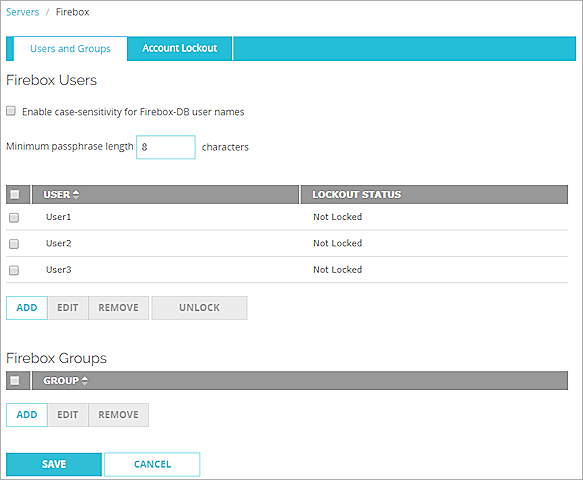
- To enable case-sensitivity and require your users to type their user names with specific capitalization, select the Enable case-sensitivity for Firebox-DB user names check box.
- (Fireware v12.2.1 or higher) In the Minimum passphrase length text box, type a number between 8 and 32.
- In the Firebox Users section, click Add.
The Firebox User dialog box opens.
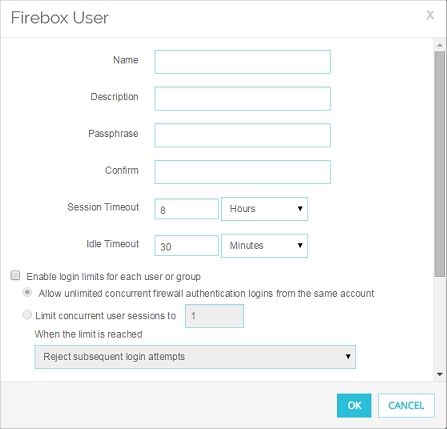
- In the Name text box, type the user name for this user.
The user name must not include special characters or spaces. - (Optional) In the Description text box, type a description of the new user.
- Type and confirm the Passphrase for the user.
Tip!
The passphrase can include letters, number, special characters, and spaces, but cannot include only space characters. - In the Session Timeout text box, type or select the maximum length of time the user can send traffic to the external network. Tip!
- In the Idle Timeout text box, type or select the length of time the user can stay authenticated when idle (not passing any traffic to the external network). Tip!
- Select the Enable login limits for each user or group check box.
- Select an option:
- Allow unlimited concurrent firewall authentication logins from the same account
- Limit concurrent user sessions to
- In the text box, type or select the number of allowed concurrent user sessions.
- From the drop-down list, select an option:
- Reject subsequent login attempts
- Allow subsequent login attempts and logoff the first session.
To limit concurrent user sessions for mobile VPN users, you must use Mobile VPN with IKEv2 and Firebox-DB or AuthPoint user accounts. You cannot limit concurrent user sessions for Mobile VPN with IKEv2 users with accounts on third-party authentication servers. You cannot limit concurrent user sessions for Mobile VPN with L2TP, Mobile VPN with SSL, or Mobile VPN with IPSec users with Firebox-DB accounts or accounts on third-party authentication servers.
- To add this user to an authentication group, in the Firebox Authentication Group list, select the check box for each group to add this user to.
If necessary, scroll down to view this list. - Click OK.
The new user shows in the Firebox Users list.
- Select Setup > Authentication > Authentication Servers.
The Authentication Servers dialog box opens.
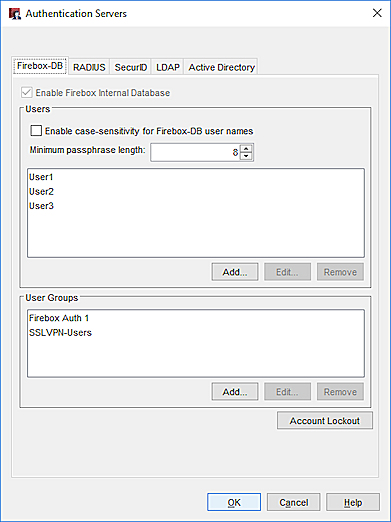
- To enable case-sensitivity and require your users to type their user names with specific capitalization, select the Enable case-sensitivity for Firebox-DB user names check box.
- (Fireware v12.2.1 or higher) In the Minimum passphrase length text box, type a number between 8 and 32.
- On the Firebox tab, in the Users section, click Add.
The Setup Firebox User dialog box opens.
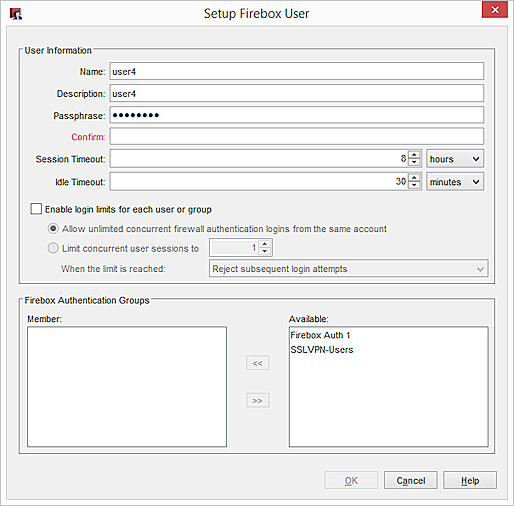
- In the Name text box, type the user name for this user account.
The user name must not include special characters or spaces. - (Optional) In the Description text box, type a description of the new user.
- Type and confirm the Passphrase for the user.
Tip!
The passphrase can include letters, number, special characters, and spaces, but cannot include only space characters. - In the Session Timeout text box, type or select the maximum length of time the user can send traffic to the external network. Tip!
- In the Idle Timeout text box, type or select the length of time the user can stay authenticated when idle (when the user does not pass any traffic to the external network). Tip!
- Select the Enable login limits for each user or group check box.
- Select an option:
- Allow unlimited concurrent firewall authentication logins from the same account
- Limit concurrent user sessions to
- In the text box, type or select the number of allowed concurrent user sessions.
- From the drop-down list, select an option:
- Reject subsequent login attempts
- Allow subsequent login attempts and logoff the first session.
To limit concurrent user sessions for mobile VPN users, you must use Mobile VPN with IKEv2 and Firebox-DB or AuthPoint user accounts. You cannot limit concurrent user sessions for Mobile VPN with IKEv2 users with accounts on third-party authentication servers. You cannot limit concurrent user sessions for Mobile VPN with L2TP, Mobile VPN with SSL, or Mobile VPN with IPSec users with Firebox-DB accounts or accounts on third-party authentication servers.
- To add this user to a Firebox Authentication Group, select the group name in the Available list.
- Click
 to move the name to the Member list.
to move the name to the Member list.
Or, you can double-click the group name in the Available list.
The group is added to the Member list. You can then add more groups for this user. - Click OK.
The new user shows in the Firebox Users list.
Configure Account Lockout Settings
You can enable Account Lockout to prevent brute force attempts to guess user account passwords. When Account Lockout is enabled, the Firebox temporarily locks a user account after a specified number of consecutive, unsuccessful login attempts, and permanently locks a user account after a specified number of temporary account lockouts.
For detailed steps to configure Account Lockout settings, go to Configure Firebox Account Lockout Settings.
Configure Your Firebox as an Authentication Server