Applies To: WatchGuard Advanced EPDR, WatchGuard EPDR, WatchGuard EDR
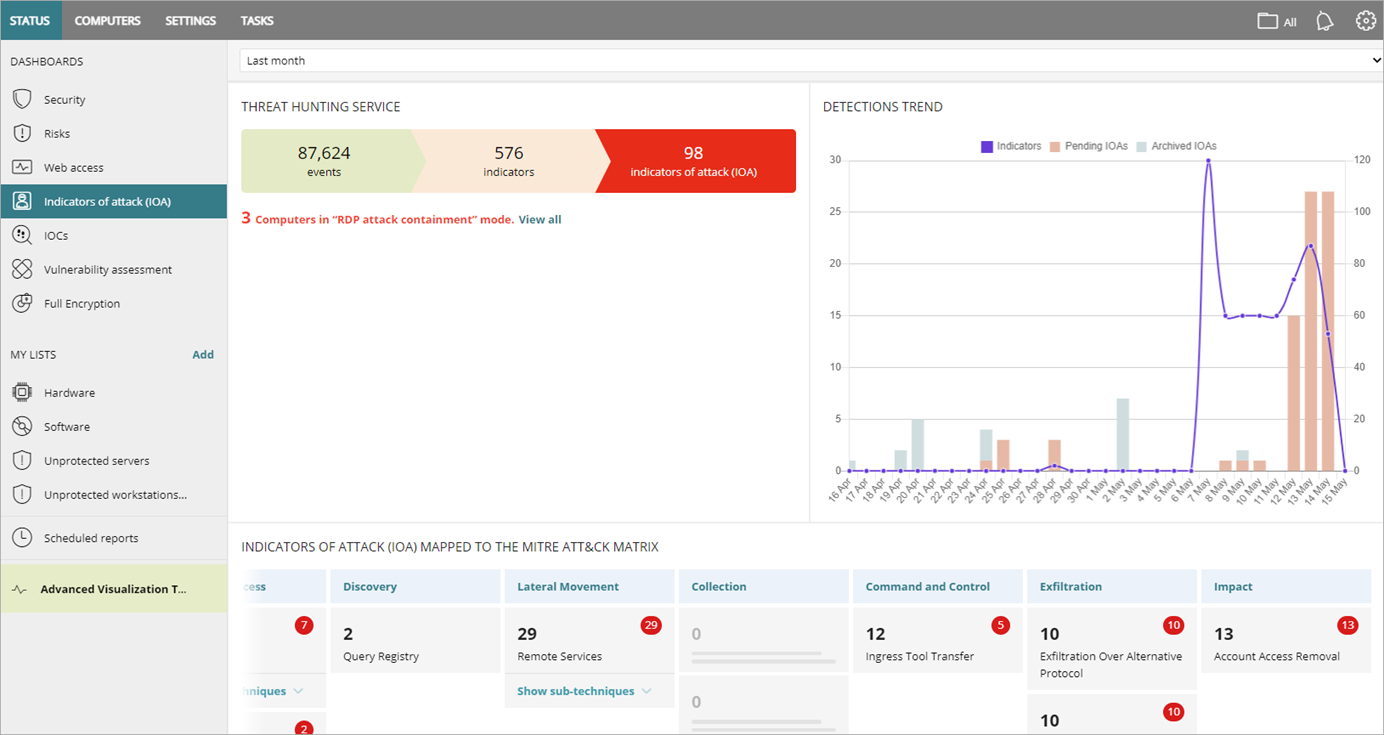
The Indicators of Attack (IOA) dashboard provides visibility into detections by the Threat Hunting Services. Several tiles show important information and provide links to more details.
Time Period Selector
The dashboard shows information for the time period selected by the administrator in the drop-down list at the top of the page.
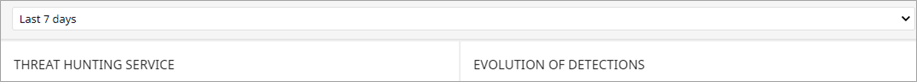
You can select from these time periods:
- Last 24 hours
- Last 7 days
- Last month
The Indicators of Attack dashboard includes these tiles:
- Threat Hunting Service
- Detections Trend
- Indicators of Attack Mapped to the MITRE Matrix
- Detected Indicators of Attack
- Indicators of Attack by Computer
Click a tile to view detailed information.
Threat Hunting Service
The Threat Hunting Service tile shows a summary of the Events, Indicators, and IOAs for all computers and devices on the network, for a selected time, to help you determine if there are intrusion attempts.
- Events — Number of actions carried out by programs installed on protected computers and monitored by WatchGuard Advanced EPDR, EPDR, or EDR.
- Indicators — Number of suspicious event patterns detected in the event data flow.
- Indicators of Attack — Number of indicators that are highly likely to be an attack.
To open the list, click the number of Indicators of Attack. For more information, go to Indicators of Attack List.
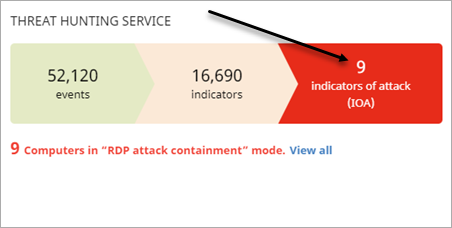
To view a list of the computers that experienced an attack through the RDP protocol, click View All.
The Computer Protection Status list opens. Each row displays the red RDP ![]() icon to indicate that the computer is in RDP Attack Containment mode. For more information, go to RDP Attack Containment Modes.
icon to indicate that the computer is in RDP Attack Containment mode. For more information, go to RDP Attack Containment Modes.
Detections Trend
The Detections Trend tile includes a line and bar graph that shows the number of Indicators, Pending IOAs, and Archived IOAs over time.
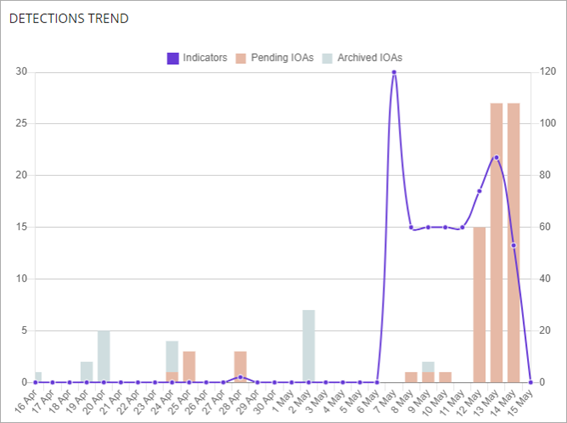
- Indicators — Number of suspicious patterns detected in the event flow received.
- Pending IOAs — Number of suspicious patterns that are highly likely to indicate an attack. An administrator has not analyzed or resolved the IOA.
- Archived IOAs — Number of IOAs that an administrator has analyzed or resolved and marked as Archived.
The Y-axis on the left measures detected pending and archived IOA. The Y-axis on the right measures indicators detected.
To open the Indicators of Attack list, click the tile. For more information, go to Indicators of Attack List.
Indicators of Attack Mapped to the MITRE Matrix
The MITRE ATT&CK™ framework is an industry standard to classify attack tactics and techniques. It is used by threat hunters to assess risk to an organization. On the IOA dashboard, this tile shows a table of the numbers of IOA detected during the selected time period, arranged by MITRE tactic and technique.
To view the name and code of the technique or the total number of detections, point to a column or box. Tactics are the columns headings. Techniques display below the tactic.
Point to the red circle to review the pending IOA. Click Show Sub-Techniques to expand a list of sub-techniques, when applicable. An IOA has at least one tactic and one technique associated with it. However, not all IOAs have sub-techniques associated with them.
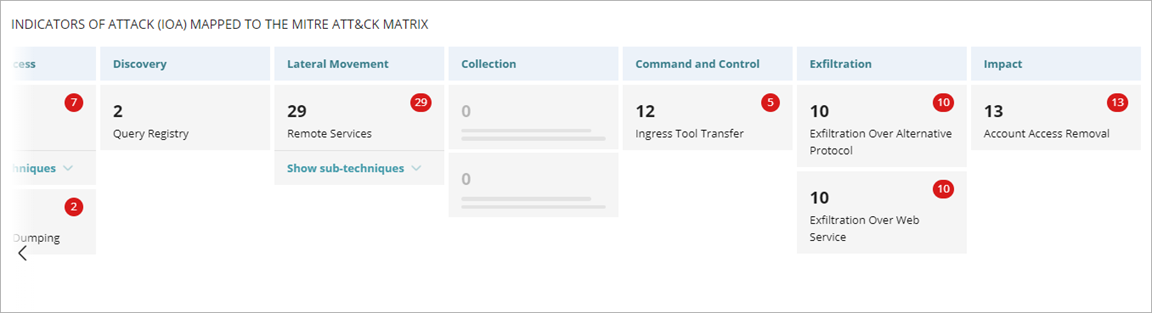
Click a tactic or technique to open the Indicators of Attack list filtered by the tactic, or tactic and technique. For more information, go to Indicators of Attack List.
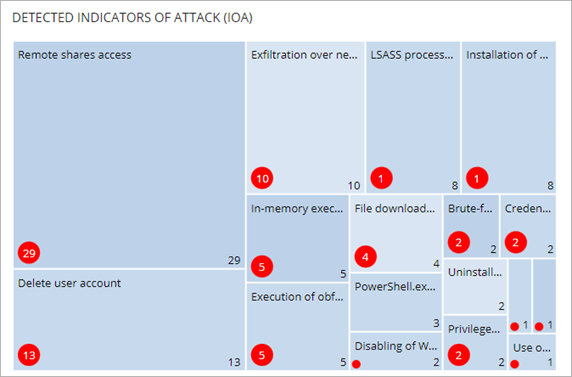
Detected Indicators of Attack
The Detected Indicators of Attack (IOA) tile shows the distribution of IOA by type detected during the selected time period. The greater the number of detected IOA of a particular type, the larger the box within the tile.
Indicators of Attack by Computer
The Indicators of Attack (IOA) by Computer tile shows the distribution of IOA for each computer on the network during the time period.
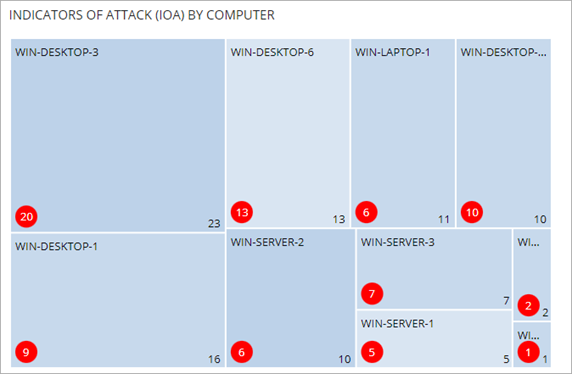
To open a filtered Indicators of Attack list, click the box for a computer. For more information, go to Indicators of Attack List.
About My Lists in Endpoint Security
Advanced EPDR Security Dashboard
WatchGuard EPDR Security Dashboard