Applies To: ThreatSync
ThreatSync automation policies define the actions that ThreatSync takes automatically when a threat is detected.
Automation policies enable Incident Responders to automatically respond to specific types of incidents so they can focus on the most important incidents that might require manual investigation and response. For example, default automation policies automatically close specific types of incidents that have a low-risk score, and perform automatic response actions on the most critical incidents.
Your operator role determines what you can see and do in WatchGuard Cloud. Your role must have the ThreatSync Core permission to view or configure this feature. For more information, go to Manage WatchGuard Cloud Operators and Roles.
You can manually respond to any incidents not covered by an automation policy. For more information, go to Perform Actions in ThreatSync.
To learn more about automation policies, go to these sections:
- ThreatSync Automation Policy Types
- Default ThreatSync Automation Policies
- ThreatSync Automation Policy Conditions and Actions
- ThreatSync Automation Policy Precedence
- ThreatSync Automation Policy Templates
We recommend that you do not add automation policies other than the default automation policies in ThreatSync Best Practices until you are familiar with the different types of incidents that can occur in your environment and the response actions you can perform.
ThreatSync Automation Policy Types
In ThreatSync, you can configure two types of automation policies:
Remediation Policy
A Remediation automation policy performs the specified response actions for incidents that meet the policy conditions.
Close Policy
A Close automation policy changes the status of incidents that meet the policy conditions to Closed.
Default ThreatSync Automation Policies
Each ThreatSync account has two default automation policies. These default automation policies enable ThreatSync to take automatic action on the highest and lowest risk incidents so you can focus on the most important incidents that might require manual investigation and response.
Default Remediation Automation Policy
To make sure that ThreatSync automatically protects you from high risk incidents, we recommend you enable the default remediation policy for incidents with a risk range of 7-10. For more information about how to enable or disable automation policies, go to Enable or Disable an Automation Policy.
Default Remediation Policy
- Rank — 1
- Policy Type — Remediation
- Risk Range — 7-10
- Device Type — Endpoint, Firebox, Access Point
- Actions — Perform > Isolate Device
This policy automatically isolates from the network any devices affected by incidents with a score of 7 or higher to prevent the spread of the threat. This enables you to analyze isolated devices and investigate incident details. For more information, go to Review Incident Details in ThreatSync.
Default Close Automation Policy
To reduce the number of low risk incidents in the incident list so you can focus on higher risk incidents, we recommend you enable the default Close automation policy that applies to incidents with a risk score of 1.
Default Close Policy
- Policy Type — Close
- Risk Range — 1
- Device Type — Endpoint, Firebox, Access Point
- Actions — Perform > Close
This policy automatically closes incidents with a risk score of 1. We recommend you review closed incidents and decide if any other actions are necessary. To review your closed incident list, filter your incidents by status on the Incidents page. For more information, go to Monitor Incidents in ThreatSync.
If you do not have time to investigate every low risk incident, consider a change to your close policy to increase the risk range to 1-3.
ThreatSync Automation Policy Conditions and Actions
For each ThreatSync automation policy, you configure conditions and actions.
Conditions
Conditions define when ThreatSync executes a policy. If an incident meets the conditions of a policy, ThreatSync performs the specified actions.
For each policy, you can specify these conditions.
- Risk Range — Specify a range of incident risk levels. For more information, go to ThreatSync Risk Levels and Scores.
- Incident Type — Select one or more incident types.
- Device Type — Select Firebox, Endpoint, or Access Point.
- Actions Performed — Select one or more of these actions performed on an incident (Close policy only).
The Actions Performed condition is only available for the Close policy type. Remediation policies have a separate section to select response actions.
Actions
Actions define what ThreatSync does when the policy executes.
For each policy, you must specify whether the policy performs or prevents actions.
- Perform — ThreatSync performs the specified actions for new incidents that meet the policy conditions.
- Prevent — ThreatSync prevents the specified actions. To create an exception to a broader Perform policy, you can add a policy with the Prevent action and rank it higher than the other policy in the policy list. A policy with the Prevent action does not prevent the manual execution of an action by an operator.
For a Remediation policy, select one or more of these actions to perform:
- Block Threat Origin IP (only external IPs) — Blocks the external IP address associated with the incident. When you select this action, all Fireboxes with ThreatSync enabled in the WatchGuard Cloud account block connections to and from the IP address.
- Delete File — Deletes the flagged file associated with the incident.
- Isolate Device — Isolates the computer from the network to prevent the spread of the threat, and to block the exfiltration of confidential data.
- Block Connections to Access Point — Blocks wireless client connections to malicious access points.
- Kill Malicious Process — Terminates a process that exhibited malicious behavior associated with the incident.
- Block Domain — Blocks the domain associated with the incident. When you select this action, all Fireboxes with ThreatSync enabled in the WatchGuard Cloud account block connections to and from the domain.
- Disable User in Microsoft 365 — Disables the Microsoft 365 user associated with the ThreatSync+ Advanced Security Policy incident.
- Block User in AuthPoint — Blocks the user associated with a Credential Access incident in AuthPoint. For more information on how to block users or activate blocked users in AuthPoint, go to Block a User or Token.
For a Close policy, there is only one action:
- Close the Incident — Changes the incident status to Closed. This action is selected automatically and you cannot change it.
ThreatSync Automation Policy Precedence
You rank ThreatSync policies in order of relative priority from top to bottom. If an incident matches the conditions configured in multiple policies, ThreatSync performs the action specified in the highest priority policy that applies.
Each recommended action in an incident is evaluated individually against a policy. If an incident does not have a recommended action that matches an action specified in the policy, that policy is skipped.
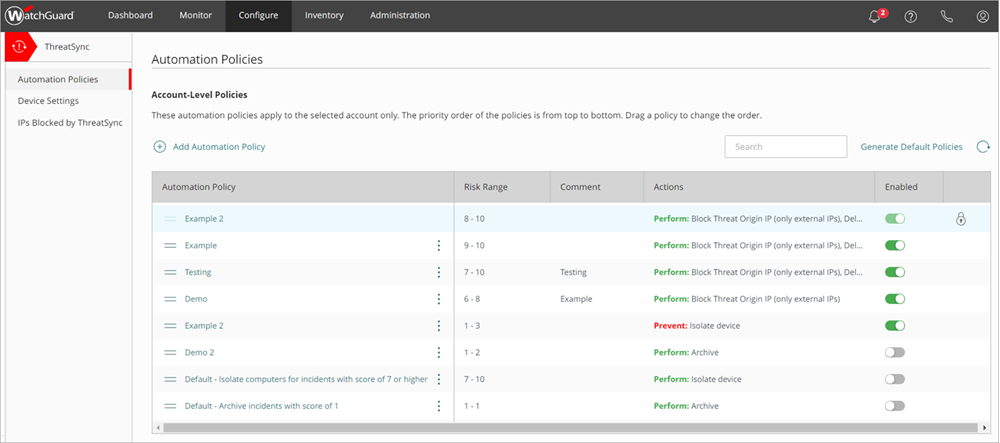
Automation policies assigned through a template appear at the top of the policies list in the Subscriber account. To change the order of your automation policies and templates, go to Manage ThreatSync Automation Policies (Subscribers).
Automation Policy Example
In this example, you have two automation policies with these conditions:
Automation Policy 1
- Rank — 1
- Policy Type — Remediation
- Risk Range — 8 to 10
- Device Type — Endpoint, Firebox
- Actions — Perform > Kill Malicious Process
Automation Policy 2
- Rank — 2
- Policy Type — Remediation
- Risk Range — 8 to 10
- Device Type — Endpoint, Firebox
- Actions — Perform > Isolate Device, Kill Malicious Process
An incident occurs with these details:
- Type — IOA
- Risk Level — 8
- Device Type — Endpoint
- Recommended Actions — Perform > Isolate Device, Kill Malicious Process, Delete File
In this example:
- Automation Policy 2 is the highest ranked policy that applies to the incident for the Isolate Device recommended action.
- Automation Policy 1 is the highest ranked policy that applies to the incident for the Kill Malicious Process recommended action.
- No automation policies apply to the incident for the Delete File recommended action.
Result:
- ThreatSync automatically isolates the device and kills the malicious process but does not try to delete the file.
ThreatSync Automation Policy Templates
You can create automation policies at the Subscriber account level. To add an automation policy for a Subscriber account, go to Manage ThreatSync Automation Policies (Subscribers).
In addition, Service Providers can create automation policy templates that include multiple automation policies, then assign the templates to the accounts or account groups they manage. This enables Service Providers to apply automation policies consistently across managed accounts, and save time when they set up ThreatSync for new accounts.
To set up automation policy templates for your managed accounts or account groups, go to Manage ThreatSync Automation Policy Templates (Service Providers).
Manage ThreatSync Automation Policies (Subscribers)
Manage ThreatSync Automation Policy Templates (Service Providers)
Configure Device Settings in ThreatSync