Applies To: Cloud-managed Fireboxes
Overview
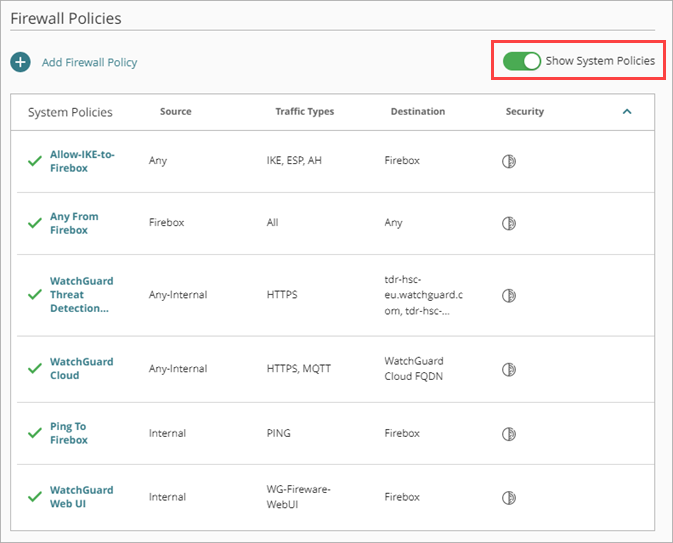
System policies are Firewall policies that allow or deny specific types of traffic required for Fireware features and WatchGuard services to operate. By default, the system policies are not shown on the Firewall Policies page. To show the system policies, at the top of the Firewall policies page, enable Show System Policies.
You cannot remove or reorder system policies, and you can only disable or edit specific system policies. For more information about which system policies you can disable, go to Disable System Policies.
Your operator role determines what you can see and do in WatchGuard Cloud. Your role must have the Devices permission to view or configure this feature. For more information, go to Manage WatchGuard Cloud Operators and Roles.
High Priority System Policies
High priority system policies appear above your other configured policies. These policies allow specific types of traffic regardless of other configured policies.
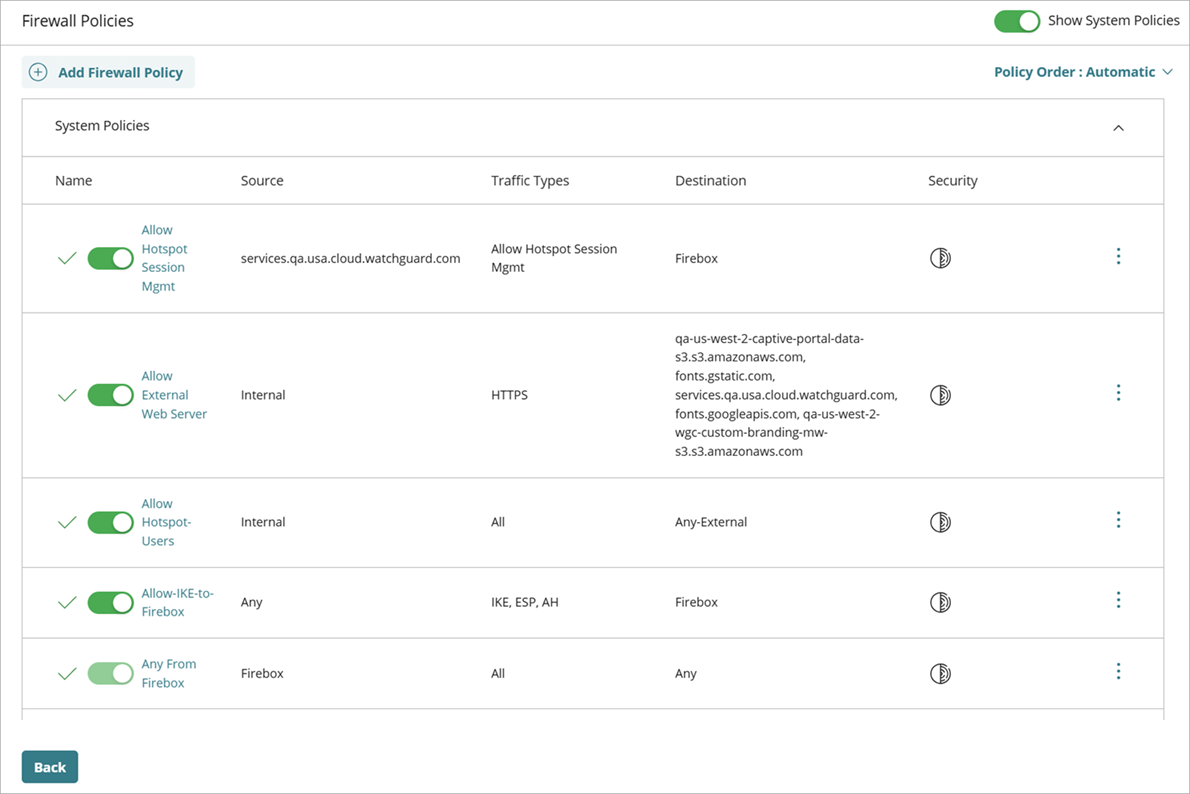
The high priority system policies are:
NTP Server
Allows NTP traffic from internal networks to the Firebox. This policy allows client devices on your private networks to contact the Firebox to synchronize the time. This policy is created automatically when you configure the Firebox as an NTP server.
WatchGuard SSLVPN
Allows SSL-VPN traffic from external networks to the Firebox. This policy allows Mobile VPN with SSL connections to the Firebox. This policy is created automatically when you configure Mobile VPN with SSL on the Firebox.
WatchGuard SNMP
Allows SNMP traffic from internal networks to the Firebox. This policy allows a Firebox to receive SNMP polls from an SNMP management station. This policy is created automatically when you enable SNMP on the Firebox.
Allow-IKE-to-Firebox
Allows IKE, ESP, and AH traffic from any source to the Firebox. This policy allows Mobile VPN with IKEv2 and BOVPN connections to the Firebox.
Any From Firebox
Allows all traffic from the Firebox itself to any destination.
WatchGuard Authentication Portal
Allows connections from internal networks to the Authentication Portal on the Firebox. This policy is created automatically when you enable the Authentication Portal in the Firebox Authentication settings.
WatchGuard Threat Detection and Response
Allows all traffic from internal networks to WatchGuard Threat Detection and Response servers.
WatchGuard Cloud
Allows all traffic from internal networks to WatchGuard Cloud.
Ping To Firebox
Allows ping traffic to the Firebox from internal networks that have the Ping Advanced option enabled.
WatchGuard Web UI
Allows connections to Fireware Web UI from internal networks that have the Web UI Access option enabled.
DR-RIP-Allow
Allows RIP multicasts to the reserved multicast address for RIP v2. This dynamic routing policy is created automatically when you enable RIP.
DR-RIPng-Allow
Allows RIPng multicasts to the reserved multicast address for RIPng, FF02::9. This dynamic routing policy is created automatically when you enable RIPng.
DR-OSPF-Allow
Allows OSPF multicasts to the reserved multicast addresses for OSPF. By default, the policy allows traffic from the alias Any to the Firebox. This dynamic routing policy is created automatically when you enable OSPF.
DR-OSPFv3-Allow
Allows OSPF multicasts to the reserved multicast addresses for OSPFv3, FF02::5 and FF02::6. This dynamic routing policy is created automatically when you enable OSPFv3.
DR-BGP-Allow
Allows traffic from the alias Any to the Firebox. This dynamic routing policy is created automatically when you enable BGP.
Allow External Web Server
Allows TCP connections from users on the guest network to the external web server IP address and the port you use for captive portal external guest authentication.
Allow Captive-Portal-Users
Allows connections from a captive portal to addresses external to the Firebox.
For internal networks, the Ping and Web UI Access options are enabled by default. For information about how to change these settings, go to Configure Advanced Network Settings.
Low Priority System Policies
Low priority system policies appear below your other configured policies.
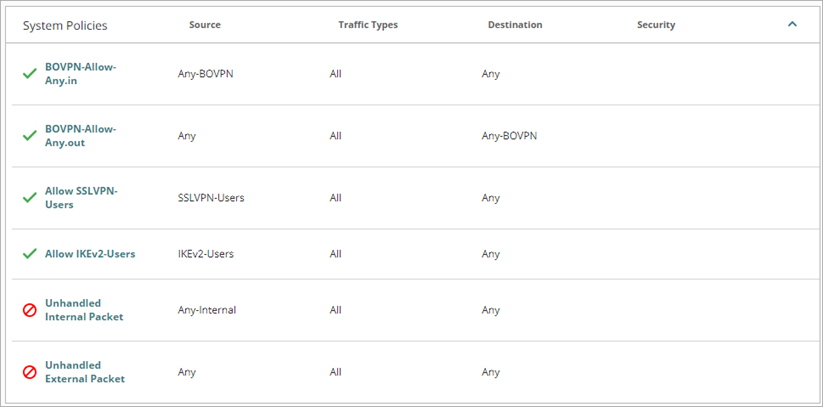
These policies are:
BOVPN-Allow-Any.in
Allows traffic from any BOVPN to any destination. This policy is created automatically when you configure a BOVPN on the Firebox.
BOVPN-Allow-Any.out
Allows traffic from any source to any BOVPN. This policy is created automatically when you configure a BOVPN on the Firebox.
Allow SSLVPN-Users
Allows traffic from users in the Mobile VPN with SSL configuration to all networks. This policy is created automatically when you configure Mobile VPN with SSL on the Firebox.
Allow IKEv2-Users
Allows traffic from users in the Mobile VPN with IKEv2 configuration to all networks. This policy is created automatically when you configure Mobile VPN with IKEv2 on the Firebox.
Unhandled Internal Packet
Denies traffic from any internal network to any destination.
Unhandled External Packet
Denies traffic from any source to any destination.
Allow DNS-Forwarding
Allows traffic DNS traffic from internal networks to the Firebox.
When these policies deny traffic through the Firebox, the policy names appear in Firebox log messages.
Disable System Policies
You can disable specific system policies if a default system policy is not restrictive enough for your needs. These are the system policies you can disable in WatchGuard Cloud:
- NTP Server
- WatchGuard SSLVPN
- WatchGuard Cloud
- WatchGuard Threat Detection and Response
- Allow-IKE-to-Firebox
- BOVPN-Allow-Any.in
- BOVPN-Allow-Any.out
- Allow SSLVPN-Users
- Allow IKEv2-Users
- Allow RADIUS SSO Service
- Allow RADIUS SSO Users
- Allow DNS-Forwarding
- DR-RIP-Allow
- DR-RIPng-Allow
- DR-OSPF-Allow
- DR-OSPFv3-Allow
- DR-BGP-Allow
- Allow External Web Server
- Allow Captive-Portal-Users
You can enable or disable a policy from the Firewall Policies page or when you edit a policy.
To disable a system policy from the Firewall Policies page in WatchGuard Cloud:
- Select Configure > Devices.
- Select a cloud-managed Firebox.
Status and settings for the selected Firebox appear. - Select Device Configuration.
The Device Configuration page opens. - In the Firewall widget, click Firewall Policies.
The Firewall Policies page opens. - Enable Show System Policies.
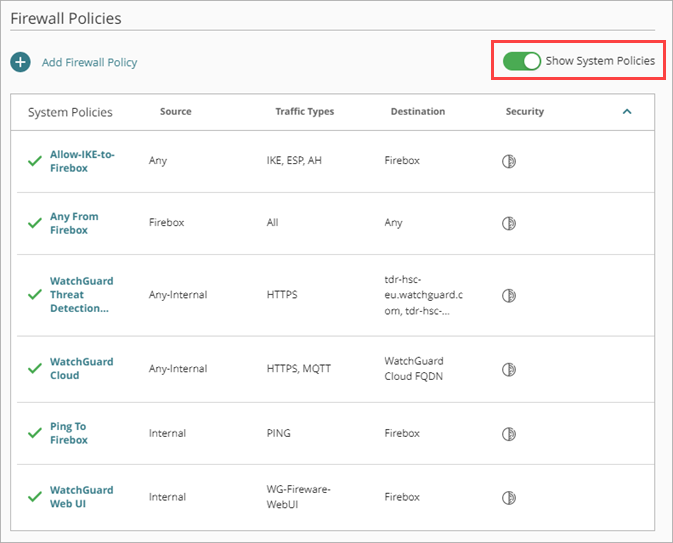
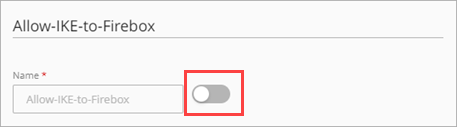
- To disable or enable a system policy in the list, click the toggle next to the policy name.
- If Manual Policy Order mode is enabled, click Save. If Automatic Policy Order mode is enabled, the change is saved automatically.
- For the change to take effect on the Firebox, you must deploy the configuration update to the Firebox. For more information, go to Manage Device Configuration Deployment.
To disable a system policy from the configuration page for an individual policy in WatchGuard Cloud:
- Select Configure > Devices.
- Select a cloud-managed Firebox.
Status and settings for the selected Firebox appear. - Select Device Configuration.
The Device Configuration page opens. - In the Firewall widget, click Firewall Policies.
The Firewall Policies page opens. - Enable Show System Policies.
- Click the system policy name you want to disable.
- Disable the toggle next to the policy name.
- Click Save.
The policy remains in the Firebox configuration but is disabled.
For configuration changes to take effect on a cloud-managed Firebox, you must deploy the configuration update to the Firebox. For more information, go to Manage Device Configuration Deployment for Fireboxes.