Optimize and Troubleshoot Gateway AntiVirus
Optimize Gateway AntiVirus
If web pages load slowly, you can limit content types and reduce the file scan size to optimize Gateway AntiVirus performance.
Scan Objects Based on Content Types
The setup wizards and the Gateway AntiVirus Activation wizard configure HTTP proxy policies to use a proxy action that scans allowed traffic for viruses. To optimize performance, we recommend that you configure the proxy action to use content types to determine whether to scan an object.
The content type in the HTTP header tells the browser whether to render or download an object. Threats are typically downloaded, so you can skip AV scans for some common content types that are not downloaded, such as:
- text/plain
- text/html
- text/xml
- text/css
- image/jpeg
- image/jpg
- application/json
- application/ocsp-response
To scan objects based on content types, in Policy Manager, configure the HTTP proxy action as follows:
- In the URL Paths ruleset, from the None matched action drop-down list, select Allow.
- In the Content Types ruleset:
- In advanced view, add rules for safer content types and set the rule action to Allow. For more information, go to Add, Change, or Delete Rules.
- Click the Up and Down buttons to move the rules for safer content types to the top of the list. For more information, go to Change the Order of Rules.
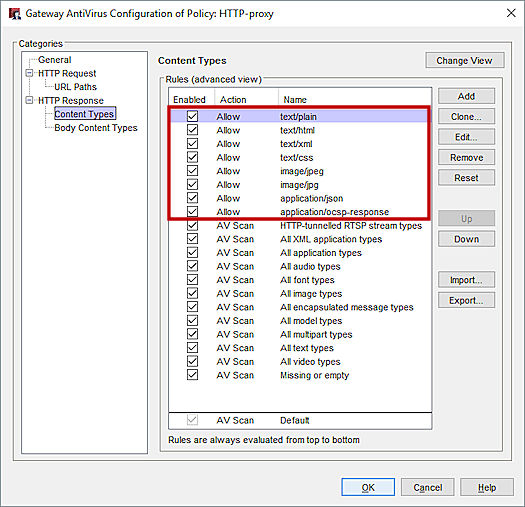
- Keep the Default rule action set to AV Scan so that content types you do not choose to allow are scanned.
- In the Body Content Types ruleset, from the None matched action drop-down list, select Allow. This does not mean that all other file types are allowed without an AV scan. The HTTP proxy can still decide to scan files based on the Content Types ruleset.
Use the Default Gateway AntiVirus Scan Limit
Most malware is delivered in files smaller than 1 MB. Because larger files are less likely to spread in a viral way, we recommend that you do not increase the default scan limit setting for your device.
If you increase the scan limit, Gateway AntiVirus scans larger files which can result in fewer concurrent connections through your Firebox.
For more information, go to About Gateway AntiVirus Scan Limits
Update the Firebox to the Latest OS Version
We recommend that you use the latest available OS version for your Firebox device. It is especially important for Gateway AntiVirus scanning performance to ensure that your device uses the current scan engine, and the correct signature set for your device. For more details on the signature sets for Firebox devices, go to Gateway AntiVirus signature set sizes.
As of 2020, Fireboxes that run Fireware v12.1.1 or lower will not get Gateway AntiVirus updates.
Enable RED
We recommend you enable Reputation Enabled Defense (RED) to reduce the resources used by Gateway AntiVirus. When you use RED, your Firebox device skips AV scans for sites with a very good reputation, and refuses access to sites with a very poor reputation.
For more information, go to About Reputation Enabled Defense.
Policy Configuration
Enable Gateway AntiVirus in any proxy action that handles traffic to or from an untrusted network and has an option to scan for viruses.
For the When a scan error occurs option, select Quarantine or Lock to avoid loss of data to scan errors. When you unlock a file, make sure that you scan the unlocked file with a local or online virus scanner.
Global Configuration
Gateway AntiVirus can scan inside compressed attachments. Gateway AntiVirus file decompression is always enabled in Fireware v12.0 and higher, and there are no configurable settings. The number of levels to scan depends on the amount of RAM the Firebox has. Firebox models with less then 2 GB RAM scan 8 levels of compressed files. Firebox models with 2 GB or more RAM scan up to 16 levels of compressed files.
For Fireware v11.12.4 and lower, you can configure Gateway AntiVirus Decompression Settings in Policy Manager. We recommend that you use the default Levels to scan of 3. If you select a higher value, this may impact performance for the proxy policy. If Gateway AntiVirus detects that the archive depth is greater than the value set in this field, it will generate a scan error for the content.
Compressed attachments that cannot be scanned include encrypted files or files that use a type of compression that is not supported such as password-protected zip files.
Troubleshoot Gateway AntiVirus
If a client on your network becomes infected with a virus, it is important to identify the reason this occurred:
- Gateway AntiVirus does not have a signature to detect this virus
- The infected file was not scanned with Gateway AntiVirus
- The Firebox device did not download the most recent signature set
Test Gateway AntiVirus
You can use the EICAR test tool to confirm that Gateway AntiVirus is enabled for the correct policy and that it can detect viruses. To obtain this tool, go to Eicar.org. For information about how to us this, go to Use the EICAR Test File to test Gateway AntiVirus in the WatchGuard Knowledge Base.
Virus Signatures
Gateway AntiVirus uses a signature set to detect infected files. If a virus is not detected, or if a virus is detected in a file that you think does not have a virus, you can report the false negative or false positive and submit the file for analysis.
In some cases, a virus which exists in the database might not be in the signature set used by your Firebox. Some Firebox models use a smaller set which focus on the more common viruses, and may not detect every virus. To learn more, see the article Gateway AntiVirus signature set sizes in the WatchGuard Knowledge Base.
Review Log Messages for Gateway AntiVirus Scans
If your Firebox device is configured to send log data to a Dimension system or WatchGuard Log Server, you can search your log data for the filename to identify whether your Firebox scanned the file, and see the scan results.
By default, your proxy policies log all events where a virus is found or if an error occurs with the scan. To ensure that a proxy policy logs all proxy events, including files with no infection found, select the Enable logging for reports check box in the proxy action.
For more information on how to search log messages in Dimension, go to Search Device Log Messages (Dimension).
Example Log Messages
In this log message, the HTTP Proxy scanned a file named eicar.com and detected a virus.
Deny 2-Internal-traffic 4-External-traffic tcp 10.0.1.8 192.168.53.92 57525 80 msg="ProxyDrop: HTTP Virus found" proxy_act="HTTP-Client.1" virus="EICAR_Test" host="192.168.53.92" path="/viruses/eicar.com" (HTTP-proxy-00)
Allow 1-Trusted 0-External tcp 10.0.1.2 8.25.35.115 51859 80 msg="ProxyAllow: HTTP AV scanning error" proxy_act="HTTP-Client.3" error="avg scanner is not created" host="api.yontoo.com" path="/LoadJS.ashx" (HTTP-proxy-00)
For more details on subscription services in Firebox System Manager, go to Subscription Services Statistics (Subscription Services).
This log message indicates a scan failure. This can occur with .zip or other compressed files that have too many levels of compression, or files that are encrypted, or otherwise cannot be opened.
Allow 1-Trusted 0-External tcp 10.0.1.2 100.100.100.11 39589 25 msg="ProxyLock: SMTP Cannot perform Gateway AV scan" proxy_act="SMTP-Outgoing.1" sender="[email protected]" recipients="wg@localhost" error="scan request failed" filename="message.scr" (SMTP-proxy-00)
If Gateway AntiVirus cannot scan a password protected file within a compressed archive file, the scan error in the log message includes the name of the file within the archive. For example, if Gateway AntiVirus could not scan a password-protected file called protected.xlsx in an archive called archive.zip, the scan error in the log message includes the names of both files.
error="Object (protected.xlsx) Encrypted" host="example.net: path-"/archive.zip"
The log message includes the name of the file within the archive in Fireware v12.2 and higher.
Review Email Headers for Gateway AntiVirus
If a user received a virus by email, you can confirm if the file was scanned, and what the result was. Look for a header similar to X-WatchGuard-AntiVirus: scanned 'file.pdf'. clean action=allow to indicate whether a virus was detected.
For instructions on how to preserve the message headers, go to When I submit messages to technical support for analysis, how do I preserve the original message header? in the WatchGuard Knowledge Base.