Applies To: Locally-managed Fireboxes
References to DNSWatch in this topic relate to the legacy DNSWatch UI. To learn about DNSWatch in WatchGuard Cloud, go to About DNSWatch in WatchGuard Cloud in WatchGuard Cloud Help.
When you enable DNSWatch on a Firebox, two separate actions occur. The two actions are:
Firebox registration
The Firebox contacts the DNSWatch servers and registers itself to the DNSWatch account where the Firebox was originally registered. After the Firebox is registered, it receives the IP addresses of two DNSWatch DNS servers and a Blackhole Server.
DNS forwarding
The Firebox forwards all outbound DNS queries to the DNSWatch DNS servers unless another DNS setting configured on the Firebox has precedence. For information about precedence of DNS settings, go to DNSWatch DNS Settings Precedence on a Firebox.
For all interfaces with DNSWatch Usage Enforcement enabled, the Firebox intercepts all DNS requests on port 53 and forwards them to a DNSWatch DNS Server, even if the DNS request was addressed to another DNS server. For more information about the options, go to Enable DNSWatch on Your Firebox.
Troubleshoot Registration and Status Errors
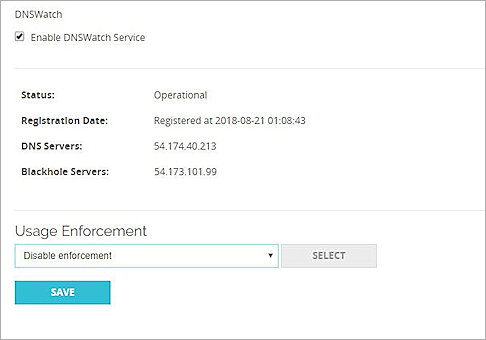
If the Firebox is registered and there are no DNSWatch errors, the DNSWatch page in Fireware Web UI shows:
Registration Date: Registered at <date and time>
Status: Operational
If registration fails, or if any other error affects the DNSWatch service, the Status line includes an error message that can be useful for troubleshooting. An error also appears for the Firebox on the Protected Fireboxes page in your DNSWatch account.
After the Firebox is registered to your DNSWatch account, the Firebox sends a request to https://dnswatch.watchguard.com/whatismyip/ to determine the public IP address for the Firebox external interface. The Firebox sends this IP address to DNSWatch. The public IP address for each Firebox external interface appears on the Protected Fireboxes page in your DNSWatch account. If DNSWatch cannot update interface information, a red cross appears in the Update Status column. For more information, go to View Fireboxes Protected by DNSWatch.
If the Firebox is behind a NAT device, the public IP address the Firebox reports to DNSWatch is not the same as the external interface IP address on the Firebox itself.
The external IP address is used to associate DNS requests from clients on your network to your DNSWatch account. DNSWatch also uses the external public interface to determine which regional DNS servers to assign to the Firebox, based on the region.
After the Firebox is registered and DNSWatch has received the public IP address, the Firebox receives the IP addresses for DNSWatch Servers and the Blackhole Server. These addresses appear in the DNSWatch page in Fireware Web UI.
If any errors occur for any of these steps, you can use the error messages described in the next section to troubleshoot the problem.
DNSWatch Error Messages and Log Messages
If the DNSWatch feature on your Firebox does not function as expected, errors appear in the Status section of the DNSWatch page in Fireware Web UI and in the Firebox log messages. To view log messages related to DNSWatch, open Traffic Monitor and filter on diagnostic logs. To find Firebox log messages related to DNSWatch, search the log file for dnswatchd.
These log messages contain information to help you troubleshoot issues with DNSWatch.
This message indicates that the Firebox failed to register with the DNSWatch service. The message includes the dnswatch domain (dnswatch.watchguard.com).
The message also includes the specific cause of the failure. For example:
error registering with the DNSWatch service at dnswatch.watchguard.com": we do not have a record for this license
This log message indicates a problem with the license for DNSWatch for the Firebox in your WatchGuard account. If you see this log message, contact WatchGuard Customer Care with your Firebox serial number and WatchGuard account ID so they can resolve the licensing issue in your account.
This error indicates that the Firebox could not retrieve the public IP address to send to DNSWatch. The error message contains other information to help you troubleshoot the problem.
To resolve this error, look at the specific error in the message for information about how to troubleshoot the problem.
This message indicates that the Firebox failed to get the DNS server addresses from the DNSWatch service. The Firebox tries to get the IP addresses of DNSWatch DNS servers after the Firebox is registered, so this error message indicates that the Firebox was successfully registered with the DNSWatch service.
The message also includes the specific cause of the failure. For example:
failed to obtain DNS-server addresses: cidr '203.0.113.10/32' overlaps with one already in use by another client: retrying in 60 seconds
The error in this example indicates that the Firebox is successfully registered, but the Firebox could not get a DNS server address because the public IP address of the Firebox is already associated with a Firebox registered to a different DNSWatch account.
The same public IP address cannot be associated with Fireboxes activated for two different accounts in the WatchGuard account.
If you enable DNSWatch on Fireboxes activated in two different WatchGuard accounts, and those Fireboxes use the same public IP address, DNSWatch associates the public IP address with the first Firebox that successfully registered with DNSWatch. Any other Firebox with the same public IP address that is registered to a different DNSWatch account gets this error and does not receive the IP address of DNSWatch DNS servers. To resolve this error, make sure no other Fireboxes that use the same public IP address are activated to a different account in the WatchGuard account.
This error indicates that DNSWatch is enabled, but the Firebox feature key does not include DNSWatch. This error appears only in log messages. This error could occur if you enable DNSWatch, and then update the feature key with a key that does not enable the DNSWatch feature. To resolve this error, make sure the Firebox has the latest feature key, and that the feature key includes DNSWatch.
The DNSWatch feature in the feature key has expired. To resolve this error, renew the Total Security Service subscription or DNSWatch trial subscription and update the feature key on the Firebox.
The dnswatch process could not locate the feature key on the Firebox. The error contains more details about the specific cause of the failure. To resolve this error, make sure the Firebox has the latest feature key.
The Firebox generates this log message if DNSWatch expires and the Firebox does not have a DNS server in its configuration. To make sure your Firebox does not continue to use the DNSWatch servers, you must specify a DNS server in the network DNS/WINS settings.
Troubleshoot DNSWatch Protection On a Client
To test your protection, use test.strongarm.io. If you are protected, the phishing education page appears. If you are not protected, a page with information about the issue appears.
To troubleshoot DNSWatch protection from a client on a protected network, you must know:
- The IP address of your Firebox internal (trusted, optional, or custom) interface
- The IP address of a publicly available DNS server. For example, 8.8.8.8.
- The DNSWatch test domain: test.strongarm.io
- A safe domain: (for example) www.google.com
- The URL of a Firebox subscription service excluded from DNSWatch: rp.cloud.threatseeker.com
- The domain of the DNSWatch Blackhole: blackhole.dnswatch.watchguard.com
To verify that your network is protected by DNSWatch and that DNS resolution works correctly, complete these tests from a computer protected by your Firebox:
- From a computer protected by your Firebox, open a command prompt window.
- Run this command:
nslookup test.strongarm.io <FIREBOX TRUSTED INTERFACE> - Look at the results. If the Firebox used the DNSWatch DNS server to resolve the domain, the result looks like this:
$ nslookup test.strongarm.io 10.0.1.1 Server: 10.0.1.1 Address: #53 Non-authoritative answer:test.strongarm.io canonical name = blackhole.dnswatch.watchguard.com. Name: blackhole.dnswatch.watchguard.com Address: 54.173.101.99
If the result does not include the IP address of the DNSWatch Blackhole Server, the Firebox did not forward the DNS request to DNSWatch. Do not continue to troubleshoot until you confirm that your Firebox forwards traffic to DNSWatch.
- From a computer protected by your Firebox, open a command prompt window.
- Run this command:
nslookup test.strongarm.io 8.8.8.8 - Look at the results. If the Firebox used the DNSWatch DNS server to resolve the domain, the result looks like this:
$ nslookup test.strongarm.io 8.8.8.8
Server: 8.8.8.8
Address: 8.8.8.8#53
Non-authoritative answer:
test.strongarm.io canonical name = blackhole.dnswatch.watchguard.com.
Name: blackhole.dnswatch.watchguard.com
Address: 54.173.101.99
If Test 1 worked, but you do not receive the IP address of the DNSWatch Blackhole Server with this test, Usage Enforcement is not enabled on this network. If you want to enforce DNSWatch use on your network, you must enable DNSWatch for this interface before you continue. For more information, go to Enable DNSWatch on Your Firebox.
- From a computer protected by your Firebox, open a command prompt window.
- Run the nslookup for a legitimate domain. For example:
nslookup www.salesforce.com - Look at the results, which look like this:
$ nslookup www.salesforce.com
Server: 10.0.0.1
Address: 10.0.0.1#53
Non-authoritative answer:
www.salesforce.com canonical name = www.gslb.salesforce.com.
Name: www.gslb.salesforce.com
Address: 96.43.144.26
Name: www.gslb.salesforce.com
Address: 96.43.145.26
- Compare this result to the same test on a system not protected by your Firebox. If the results match, then DNSWatch correctly resolved the DNS requests.
- From a computer protected by your Firebox, open a command prompt window.
- Run the nslookup command for one of the WatchGuard domains that is excluded from DNSWatch.
nslookup rp.cloud.threatseeker.com - Look at the results, which look like this:
$ nslookup rp.cloud.threatseeker.com 10.0.0.1
Server: 10.0.0.1
Address: 10.0.0.1#53
Non-authoritative answer:
Name: rp.cloud.threatseeker.com
Address: 208.87.234.140
- Compare this result to the same test on a system not protected by your Firebox. If the results match, then DNSWatch correctly resolved the DNS request.
If these tests all produce the expected results, your network is protected by DNSWatch.
By default, the domain test.strongarm.io is on the blocklist in your DNSWatch account. You can browse to test.strongarm.io to view the deny message that clients on your network see when DNSWatch denies a DNS request.
For information about how to customize the block page, go to Customize DNSWatch Block Pages.