Applies To: Locally-managed Fireboxes
When you configure a mobile VPN, the Firebox automatically creates two types of policies:
Connect policy
The connect policy allows the VPN to establish. For Mobile VPN with SSL, the connect policy is named WatchGuard SSLVPN. We recommend that you do not change this policy.
Access policy
The access policy allows Mobile VPN with SSL groups and users to get access to resources on your network. For Mobile VPN with SSL, the access policy is named Allow SSLVPN-Users.
By default, the Allow SSLVPN-Users policy allows users to access all network resources. This occurs because the To list in the Allow SSLVPN-Users policy includes only the alias Any.
Only the SSLVPN-Users group appears in the From list of the SSLVPN-Users policy. The SSLVPN-Users group includes any users and groups that you add to the Mobile VPN with SSL configuration. Users and groups that you add to the Mobile VPN with SSL configuration do not appear in the From list of the Allow SSLVPN-Users policy. However, the policy still applies to those users and groups.
Authentication Groups and SSL Policies
It is important to understand that Firebox policies control which resources that mobile VPN users can access. VPNs are not considered to be part of the Trusted or Optional zones. When users connect to the VPN, they are not considered to be trusted users on the local network.
This means that Firebox policies with the Trusted or Optional aliases in the From list do not apply to traffic from mobile VPN users unless you add mobile VPN groups or users to those policies. Or, you can create new policies for traffic from mobile VPN groups and users.
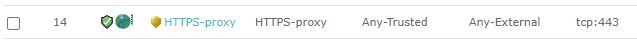
For example, this policy does not apply to traffic from Mobile VPN with SSL users because the From list includes only the alias Any-Trusted:
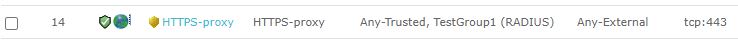
This policy does apply to traffic from Mobile VPN with SSL users because the From list includes a Mobile VPN with SSL user group:

This policy also applies to traffic from Mobile VPN with SSL users because the RADIUS user group TestGroup1 is specified in the Mobile VPN with SSL configuration:
Carefully consider which user groups you add to Firebox policies. For example, if you add RADIUS user groups to the authentication configuration on your Firebox, and you add the same groups to your Mobile VPN with SSL configuration, consider adding the RADIUS groups to Firebox policies rather than the default SSLVPN-Users group. The SSLVPN-Users group includes all groups and users that you add to the Mobile VPN with SSL configuration. If you add the SSLVPN-Users group to a Firebox policy, all mobile users have access to resources specified in that policy, which might not be your intention.
To learn more, go to the Secure Mobile VPN Access video tutorial (12 minutes).
Virtual IP address pools do not affect whether VPN users are considered as trusted users on the local network. For example, if you specify an IP address pool for Mobile VPN with SSL that overlaps with the IP address range of your local network, mobile VPN users are still not considered as trusted users on the local network.
Best Practices for SSL Policies
We recommend that you limit which network resources Mobile VPN with SSL users can access through the VPN. To do this, you can replace the Allow SSLVPN-Users policy.
To replace the Allow SSLVPN-Users policy:
- Determine the ports and protocols your users require. To determine this, assess your network with baseline tests and view logs.
- Add Mobile VPN with SSL groups and users to existing Firebox policies that specify those ports and protocols. For example, you can add Mobile VPN with SSL groups and users to policies for web traffic.
- If required, add new policies:
- When you select a policy type for the new policy, you can specify a protocol and port.
- In the From list of the policy, specify users or groups. You must specify groups or users included in the Mobile VPN with SSL configuration. For example, you can specify the default SSLVPN-Users group. Or, specify groups and users that you added to the Mobile VPN with SSL configuration.
- In the To list of the policy, remove the Any alias and add other destinations.
- Before you disable the Allow SSLVPN-Users policy, make sure your policies allow Mobile VPN with SSL users to access all required network resources.
- Disable the Allow SSLVPN-Users policy.