Applies To: Locally-managed Fireboxes
The objective of this configuration example is to show how an organization could block the use of specific applications on their network, without changing their existing firewall configuration or any of their existing network addresses. In this example, we block access to all online games, and block access to Facebook.
This configuration example is provided as a guide. Additional configuration settings could be necessary, or more appropriate, for your network environment.
Solution Overview
An organization can add a Firebox behind any firewall on their existing network to monitor and control which applications their users can use. To do this, they configure their Firebox in bridge mode, so it can transparently monitor and control content in and out of their network without any change to their existing firewall configuration or network addressing.
After the Firebox is added to the network, NAT and network routing are still managed by the existing gateways and routers. The Firebox simply examines the content as it passes through, and then applies policies to that traffic.
In bridge mode, the Firebox does not route network traffic. The Firebox examines the traffic and then passes it on to the destination, without any changes to the packet header or routing information. When the packet arrives at a gateway from the Firebox, it appears to have been sent from the original device.
The traffic that passes through the Firebox is managed by the policies you add to the device configuration file. When Application Control is enabled in the policies, traffic is inspected to identify applications and block the traffic for the applications that you specify.
Requirements
- A Firebox appropriate for your network size
Firebox capabilities vary by model. You must select a Firebox that has the capacity to manage the traffic for your network. For information about Fireboxes, go to https://www.watchguard.com/wgrd-products/. - A security subscription to Application Control
The Firebox must have an active Application Control security subscription.
Configuration
In this example, we present an existing firewall that protects a private network. Because routing is managed by the existing network devices, the network behind the firewall can either be a single network or multiple subnets behind a router. The Firebox can apply Application Control rules to the traffic between the network users and the existing firewall, regardless of your network configuration.
In this example, our existing network uses these IP addresses:
| Example network configuration | IP address |
|---|---|
| Existing firewall | 192.168.100.1 |
| Private network immediately behind the existing firewall | 192.168.100.0/24 |
To configure the Firebox, you only need to know the existing firewall IP address and an available IP address on the internal network that you can assign to the Firebox for management. As long as the Firebox is located between the network users and the firewall, the rest of the existing network topology does not affect the Firebox configuration.
To illustrate this point, we provide two different existing network topologies: Flat Internal Network and Routed Internal Network.
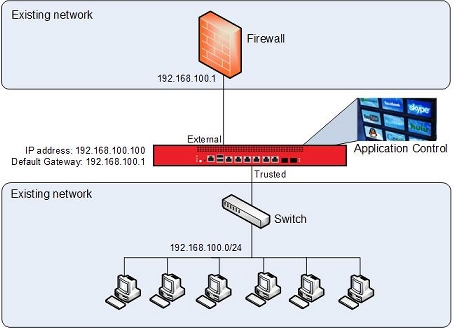
Topology 1 — Flat Internal Network
This diagram shows where to install your Firebox on a network with a single subnet, so that you can use Application Control.
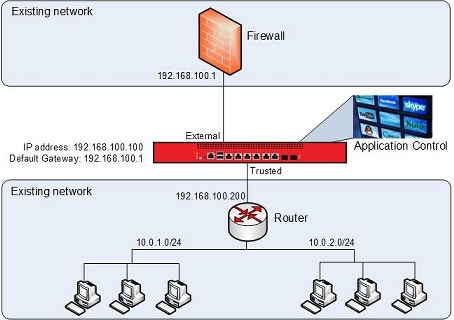
Topology 2 — Routed Internal Network
This diagram shows where to install your Firebox on a network with a router and multiple subnets, so that you can use Application Control.
How It Works
The network is configured in Bridge Mode. To connect to the device to manage it, you use the IP address of the Firebox. That address must be on the same subnet as the firewall. In this image, the Firebox IP address is set to 192.168.100.100/24.
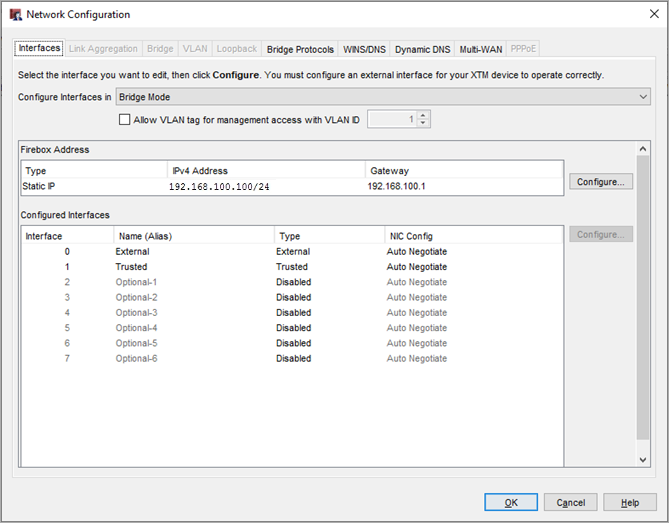
The existing firewall is the default gateway for the network that is immediately behind the firewall, so the gateway IP address in the Firebox configuration is set to the firewall IP address, 192.168.100.1.
Policies
Create two policies which allow all traffic to flow through the device, for example:
- Any-inbound — Allows all traffic from the firewall to the users on the network.
- Any-outbound — Allows all traffic from the users on the private network to the firewall.
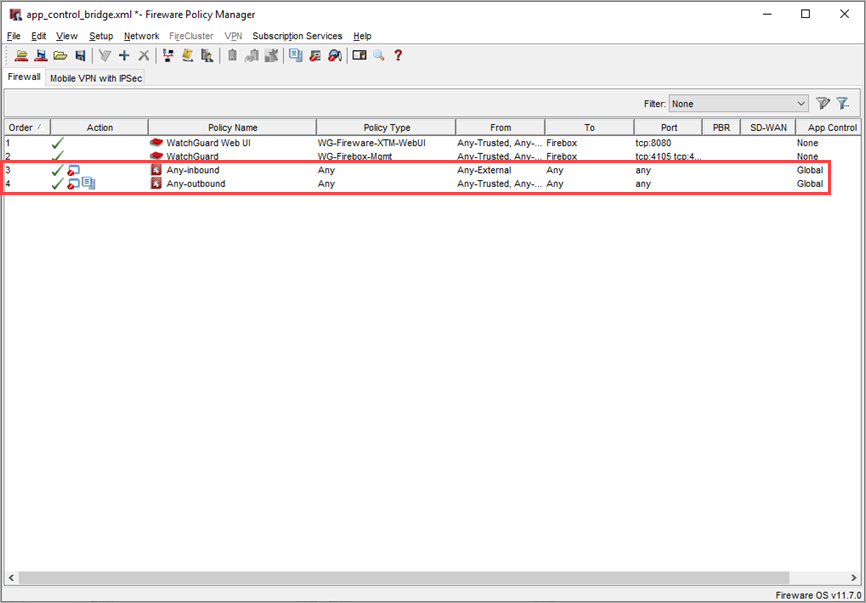
Policies of the type Any apply to any type of traffic. You can open these policies to examine the policy configuration details.
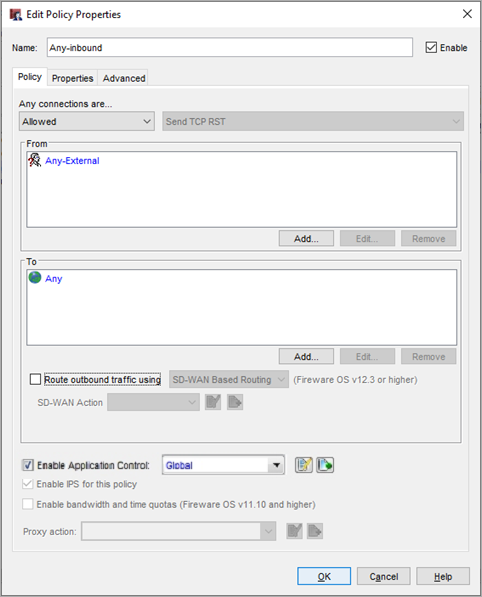
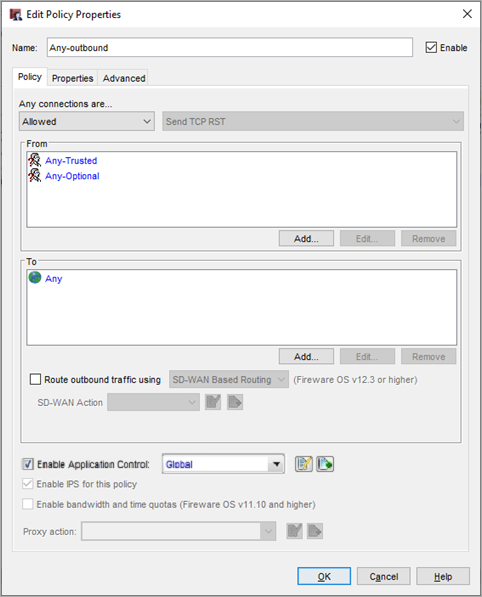
Each policy has the Global Application Control action enabled.
Application Control Settings
Configure the Global Application Control action to block:
- All Facebook applications
- All applications in the Games category
Enable the Global Application Control action for the Any-inbound and Any-outbound policies that allow the traffic.
To see the Global Application Control action, in Fireware Policy Manager:
- Select Subscription Services > Application Control.
The Application Control Actions dialog box opens. - From the Actions list, select the Global Application Control action and click Edit.
The Application Control Action (predefined) dialog box opens. - Select Show Only Configured Applications.
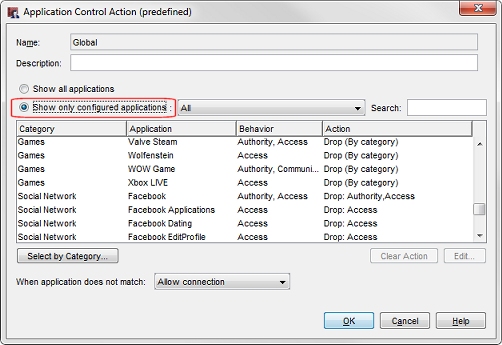
In this image, all games applications are blocked based on the application category, as indicated by the selected action: Drop (By Category). The Facebook applications, however, are blocked individually, as indicated by the specified drop actions.
- To see which application categories are blocked, click Select by Category.
For this example, you can see the action for the Games category is set to Drop.
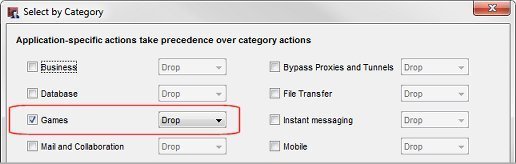
The Games category blocks all online games, not just Facebook games. This is what we want for this configuration example.
Monitor Blocked Applications
When Application Control drops traffic that matches a configured Application Control action, that event appears in a traffic log message. If you connect to the Firebox with Firebox System Manager, you can select the Traffic Monitor tab to see the log messages that indicate which applications have been blocked. By default, policies are configured to create a log message only when traffic is not allowed by the policy, so only messages about applications that are blocked appear in Traffic Monitor.
To see log messages for all applications that are detected, even if that traffic is not blocked, you can configure the policy to generate a log message for all allowed packets. In the example, the Any-Outbound policy is configured to send a log message for all allowed packets.
To see this configuration setting:
- Double-click the Any-Outbound policy.
The Edit Policy Properties dialog box opens for the Any-outbound policy. - Select the Properties tab.
- Click Logging.
The Logging and Notification dialog box opens.

WatchGuard System Manager also includes other reporting and monitoring tools that you can use to review Application Control log messages and create reports. For more information about logging and reporting, go to Set Logging and Notification Settings in Fireware Help.
Conclusion
In this configuration example, we explored how to add an Firebox to an existing network to block selected applications with Application Control. The addition of the Firebox to this network required no change to the existing firewall configuration, and no change to the configuration of any other devices on this network. The Firebox simply inspects the traffic and blocks the applications configured in the Application Control action.
After the Firebox is added to the network, it is easy to enable other security services that can increase the security of your network and your control over the content on the network. For example, you could enable WebBlocker, which allows you to block web content based on content categories, or Intrusion Prevention Service, which provides real-time protection from threats such as spyware, cross-site scripting, and buffer overflows.
For more information about the available WatchGuard security subscriptions, go to https://www.watchguard.com/wgrd-products/security-services.
This configuration example blocks access to all Facebook applications, but you can also choose to selectively block some Facebook applications and allow others. For example, you can allow Facebook applications as needed by your Marketing department, but at the same time block access to Facebook games.