Use Certificates with Outbound HTTPS Proxy Content Inspection
Many websites use both the HTTP and HTTPS protocols to send information to users. While your Firebox can easily examine HTTP traffic, HTTPS traffic is encrypted. To examine HTTPS traffic requested by a user on your network, you must configure your Firebox to decrypt the information and then re-encrypt it with a different private key.
For more detailed information about content inspection for the HTTPS-proxy, see HTTPS-Proxy: Content Inspection.
For a demonstration of the use of certificates for outbound HTTPS content inspection, go to Outbound Content Inspection video tutorial.
HTTPS Proxy Authority Certificate Options
When your Firebox scans an HTTPS connection with content inspection, the HTTPS-proxy intercepts the HTTPS request and initiates its own connection to the destination HTTPS server on behalf of the client. After the Firebox receives a reply and a copy of the remote server certificate from the destination HTTPS server, the Firebox presents an altered version of the certificate from the remote server (signed with the Proxy Authority CA certificate) to the originating client. The Common Name (CN), Subject Alternative Name (SAN), and other values remain the same for identity validation. The Proxy Authority re-signing certificate can be either an imported CA certificate or the default self-signed Firebox certificate.
Local CA Certificate (Recommended Option)
If your organization already has a Public Key Infrastructure (PKI) set up with a local CA, you can import a certificate that is signed by the internal CA to your Firebox. We recommended this option. When the client devices already trust your local PKI root CA certificate, you will not have to deploy another certificate to each client device.
We recommend that you use a certificate signed by your own internal CA.
For example, if your organization uses Microsoft Active Directory Certificate Services, you can:
- Create a Certificate Signing Request (CSR) from Firebox System Manager. Make sure you select Proxy Authority (re-signing CA certificate for outbound SSL/TLS content inspection) as the certificate function. For instructions, see Create a Certificate CSR .
- Have the certificate signed by your Microsoft CA server. For instructions, see Sign a Certificate with Microsoft CA.
- Use the Certificate Import Wizard to import the re-signing CA and root CA certificates to your Firebox. For instructions, see Manage Device Certificates (Web UI) or Manage Device Certificates (WSM).
- Distribute the re-signing certificate to all your non-domain computer users manually, or through the Certificate Portal. Clients that are joined to the domain already have a copy of the root CA certificate and trust the re-signing CA certificate. For instructions, see Import a Certificate on a Client Device or Certificate Portal.
You must create a CA certificate that can re-sign other certificates. If you create a CSR with Firebox System Manager and have it signed by a third-party CA, you cannot use it as a CA certificate.
For a demonstration of the Active Directory certificate service for HTTPS content inspection, see the Create an Active Directory Certificate for Content Inspection video tutorial.
Default Firebox Proxy Authority Certificate
You can use the default self-signed Proxy Authority CA certificate on the Firebox with the HTTPS-Proxy content inspection features. Your device re-encrypts the content it has decrypted with the built-in private key for this self-signed certificate.
When you use this default certificate, users without a copy of the certificate see a warning in their web browser when they connect to a secure website with HTTPS. To avoid these warnings, you can export the Proxy Authority certificate from the Firebox and import the certificate on your client devices, or you can use the Firebox Certificate Portal to distribute the certificate.
For information on how to export the default Proxy Authority CA certificate from your device, see Export a Certificate from Your Firebox.
For information on how to import this certificate on your client devices, see Import a Certificate on a Client Device.
To download and install the root CA certificate that signed the Proxy Authority certificate from the Certificate Portal on the Firebox, go to http://<Firebox IP address>:4126/certportal. For more information, see Certificate Portal.
Examine Content from External HTTPS Servers
Before you enable this feature, we recommend that you provide the certificate used to re-sign HTTPS traffic to all clients on your network. You can provide a link to the Certificate Portal in an email with instructions, or use network management software to install the certificates automatically. We recommend that you test the HTTPS-proxy content inspection with a small number of users to make sure it operates correctly before you apply content inspection to all HTTPS traffic on a large network.
For more detailed information on how to import certificates to clients, see Import a Certificate on a Client Device and Certificate Portal.
If you have other outbound traffic that uses the HTTPS port, such as SSL VPN traffic, we recommend that you evaluate the content inspection feature carefully. To make sure that other traffic sources operate correctly, we recommend that you add domain name rules with the Allow action to bypass inspection for those domains or IP addresses. For more information, see HTTPS-Proxy: Domain Name Rules.
In Fireware v12.1 or lower, you must enable content inspection in the HTTPS-proxy before you can select the Inspect action. For more information, see HTTPS-Proxy: Content Inspection.
- Click
 .
.
Or, select Edit > Add Policy.
The Add Policy dialog box opens. - Select HTTPS-proxy. Click Add Policy.
The New Policy Properties dialog box opens, with the Policy tab selected. - Next to the Proxy action drop-down list, click
 .
.
The HTTPS Proxy Action Configuration dialog box opens, with the Content Inspection category selected. - Configure domain name rules with the Inspect action and select the HTTP proxy action to use for inspection.
For more information, see HTTPS-Proxy: Domain Name Rules. - Click OK.
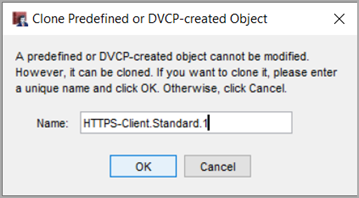
The Clone Predefined or DVCP-created Object dialog box opens. - In the Name text box, type a name for the proxy action.
For example, type HTTPS-Client-Inspect. - Click OK.
- To close the New Policy Properties dialog box, click OK.
- Select Firewall > Firewall Policies.
The Firewall Policies page opens. - Click Add Policy.
The Add Firewall Policy page opens. - Select the Proxies policy type.
- From the Proxies drop-down lists, select HTTPS-proxy and the HTTPS-Client.Standard proxy action.
- Click Add Policy.
The Add page opens for the HTTPS-proxy. - Select the Proxy Action tab.
- From the Proxy Action drop-down list, select Clone the current proxy action.
- In the Name text box, type a name for this proxy action.
For example, type HTTPS-Client-Inspect. - Configure domain name rules with the Inspect action and select the HTTP proxy action to use for inspection.
For more information, see HTTPS-Proxy: Domain Name Rules. - Click Save.
When you select the Inspect action in the HTTPS proxy action, you select an HTTP proxy action to apply to the decrypted traffic. You can select the Inspect action in domain name rules and you can enable inspection of allowed WebBlocker categories in the HTTPS proxy action.
For more information about domain name rules in the HTTPS-proxy, go to HTTPS-Proxy: Domain Name Rules.
For more information about WebBlocker configuration in the HTTPS-proxy, go to HTTPS-Proxy: WebBlocker.
Protect a Private HTTPS Server
Troubleshoot Problems with HTTPS Content Inspection