Applies To: Locally-managed Fireboxes
A branch office virtual private network (BOVPN) tunnel is a secure way for networks, or for a host and a network, to exchange data across the Internet. This document tells you how to use Policy Manager to define a manual BOVPN tunnel between two Fireboxes.
For the same example as configured in Fireware Web UI, go to Set up a VPN Between Two Fireware Devices (Web UI).
- About Manual IPSec Branch Office VPNs
- Configure Manual BOVPN Gateways
- Configure Manual BOVPN Tunnels
Determine IP Address and Tunnel Settings
Before you create a manual BOVPN tunnel, we recommend that you determine which IP addresses and settings to use. This topic includes a checklist that can help you plan.
In this example, both endpoints have static external IP addresses. For information on BOVPN tunnels to devices with a dynamic external IP address, go to Define Gateway Endpoints for a BOVPN Gateway.
Make sure that you configure the VPN endpoints correctly and that the Phase 1 and Phase 2 settings are the same on both Fireboxes. The VPN tunnel does not build if the settings do not match.
If a setting does not appear in this list, keep the default value for that setting.
BOVPN Tunnel Settings
Site A Firebox
Public IP address: ______________________________
Private IP address: _____________________________
Site B Firebox
Public IP address: ______________________________
Private IP address: _____________________________
Phase1 Settings
Both Fireboxes must use exactly the same values.
For a BOVPN tunnel between two Fireboxes, we recommend that you select Dead Peer Detection (RFC3706), not IKE Keep-Alive. Do not select both. You should always select Dead Peer Detection if both endpoint devices support it.
Credential method: Select Use Pre-Shared Key.
Pre-shared key: ______________________________
(Fireware v12.5.4 or higher) Pre-shared key type (string-based or hex-based): ________________
IKE Version: IKEv1 ____ IKEv2 ____
Mode (choose one): Main ____ Aggressive ____
NAT Traversal: Yes ____ No ____
NAT Traversal Keep-alive interval: ________________
IKE Keep-alive: Yes ____ No ____
IKE Keep-alive Message interval: ________________
IKE Keep-alive Max failures: ________________
Dead Peer Detection (RFC3706): Yes ____ No ____
Dead Peer Detection Traffic idle timeout: ________________
Dead Peer Detection Max retries: ________________
Authentication algorithm (choose one): MD5___SHA1____
SHA2-256____SHA2-384____SHA2-512____
We recommend SHA-1 or SHA-2
Encryption algorithm (choose one): DES____ 3DES____ AES-128____ AES-192____ AES-256____
AES-GCM-128____AES-GCM-192____AES-GCM-256
We recommend an AES variant. AES-GCM is supported in Fireware v12.2 or higher. AES-GCM is supported for IKEv2 only.
SA Life ________________
Select Hours as the unit for SA life.
Diffie-Hellman Group (choose one): 1____ 2____ 5____14____15____19____20____
Phase 2 Settings
Both Fireboxes must use exactly the same values.
Perfect Forward Secrecy (Diffie-Hellman Group): Disable____ Group1____ Group2____ Group5____ Group14____ Group15____ Group19____ Group20____
Authentication algorithm (choose one): MD5___SHA1____ SHA2-256____SHA2-384____SHA2-512_____ (We recommend SHA-1 or SHA-2)
Encryption algorithm (choose one): DES____ 3DES____AES-128____ AES-192____ AES-256____
AES-GCM-128____AES-GCM-192____AES-GCM-256
We recommend an AES variant. AES-GCM is supported in Fireware v12.2 or higher. AES-GCM is supported for ESP only.
Force Key Expiration Time (Default) (Hours): ________________
Force Key Expiration Traffic (kilobytes or MB): ________________
Example Tunnel Settings
This section has the same fields as the previous section, and includes example settings. These settings correspond to the settings that appear in the images in this example.
Site A Firebox
Public IP address: 203.0.113.2
Private network IP address: 10.0.1.0/24
Site B Firebox
Public IP address: 198.51.100.2
Private network IP address: 10.50.1.0/24
Phase 1 Settings
Both sides must use exactly the same values.
Credential method: Select Use Pre-Shared Key.
Pre-shared key: [Specify a strong key]
Pre-shared key type: String-based
Version: IKEv1
Mode: Main
NAT Traversal: Enable
NAT Traversal Keep-alive interval: 20 seconds
IKE Keep-alive: Disable
IKE Keep-alive Message interval: none
IKE Keep-alive Max failures: none
Dead Peer Detection (RFC3706): Enable
Dead Peer Detection Traffic idle timeout: 20 seconds
Dead Peer Detection Max retries: 5
Authentication algorithm: SHA256
Encryption algorithm: AES (256-bit)
SA Life: 24 hours
Diffie-Hellman Group: 14
Phase 2 Settings
Both sides must use exactly the same values.
Perfect Forward Secrecy (Diffie-Hellman Group): 14
Type: ESP
Authentication algorithm: SHA256
Encryption algorithm: AES (256-bit)
Configure Site A
You now use Policy Manager to configure the gateway on the Site A Firebox. A gateway is a connection point for one or more tunnels. To configure a gateway, you must specify:
- Credential method (either pre-shared keys or an IPSec Firebox certificate)
- Location of local and remote gateway endpoints, either by IP address or domain information
- Settings for Phase 1 of the Internet Key Exchange (IKE) negotiation
Add a VPN Gateway
- Select VPN > Branch Office Gateways.
The Gateways dialog box appears. - Click Add.
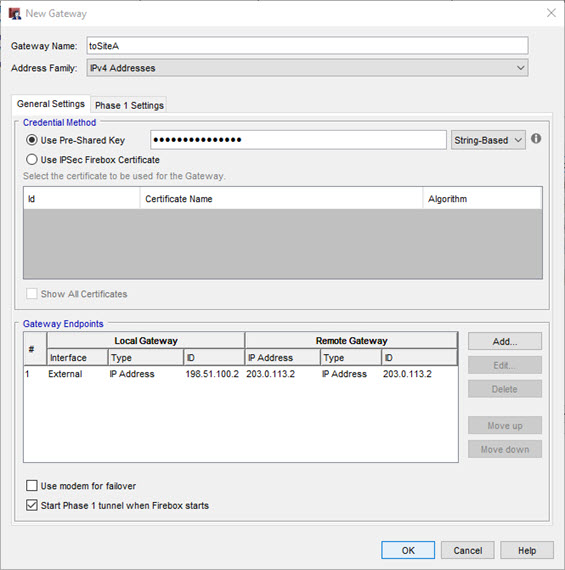
The New Gateway dialog box appears.
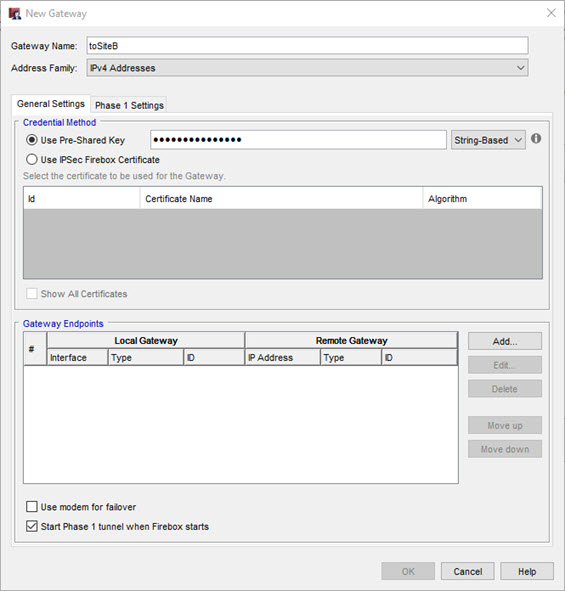
- In the Gateway Name text box, type a name to identify this gateway in Policy Manager.
- In the Credential Method area, select Use Pre-Shared Key.
- (Fireware v12.5.4 or higher) Select String-Based or Hex-Based. The default setting is String-Based. For information about hex-based keys, go to Hex-Based Pre-Shared Keys.
- Type the shared key.
The shared key must use only standard ASCII characters. - In the Gateway Endpoints section, click Add.
The New Gateway Endpoints Settings dialog box appears.
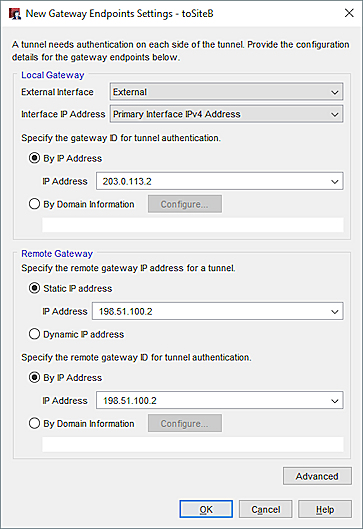
- From the External Interface drop-down list, select the interface that has the external (public) IP of the Site A Firebox.
- (Fireware v12.2 or higher) To specify an IP address, in the Interface IP Address drop-down list, select Primary Interface IP Address or select a secondary IP address that is already configured on the selected external interface. Tip!
- Select By IP Address and type the primary IP address of the Firebox interface.
In Fireware v12.4 or higher, you must specify an IP address type that matches the Address Family setting you configured earlier. For example, if you specified IPv6 Addresses, you must specify an IPv6 address in the By IP Address text box. - In the Remote Gateway section, select Static IP Address.
- In the adjacent text box, type the external (public) IP address of the Site B Firebox.
- Select By IP Address.
- In the adjacent text box, type the external (public) IP address of the Site B Firebox.
- Click OK.

For information about the Use modem for failover setting, go to Configure VPN Modem Failover.
For information about the Start Phase 1 tunnel when Firebox startssetting, go to Disable Automatic Tunnel Startup.
Configure the Phase 1 Settings
Phase 1 of establishing an IPSec connection is where the two peers make a secure, authenticated channel they can use to communicate. This is known as the ISAKMP Security Association (SA).
- Select the Phase 1 Settings tab.
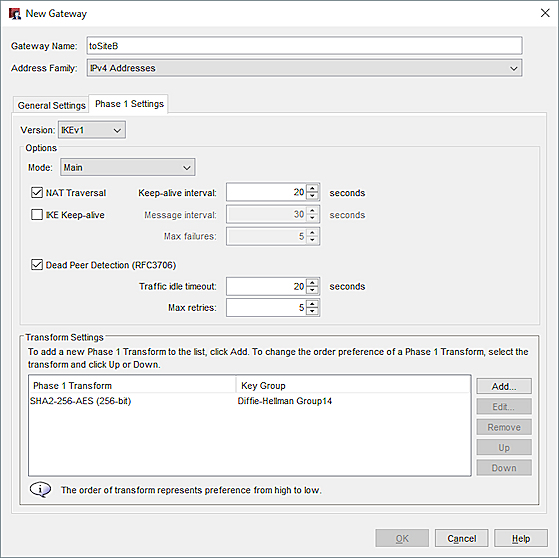
- From the Mode drop-down list, select Main.
The example uses Main Mode because both endpoints have static IP addresses. If one endpoint has a dynamic IP address, you must use Aggressive mode. - Select NAT Traversal, which we recommended for a BOVPN tunnel between two Fireboxes.
NAT Traversal, or UDP Encapsulation, allows traffic to get to the correct destinations when a device does not have a public IP address. - Dead Peer Detection (RFC3706), which we recommended for a BOVPN tunnel between two Fireboxes.
When you enable dead peer detection, the Firebox connects to a peer only if no traffic is received from the peer for a specified length of time and a packet is waiting to be sent to the peer. This method is more scalable than IKE keep-alive messages. - In the Transform Settings area, select the default transform and click Edit.
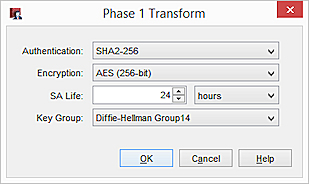
- From the Authentication and Encryption drop-down lists, select your preferred algorithm. In our example, we use SHA256 and AES (256-bit).
- In the SA Life text box, type 24 and select Hours.
The security association (SA) is valid for the amount of time that you specify in this setting. If the two VPN gateways do not complete Phase 2 negotiations before the Phase 1 SA expires, then they must complete Phase 1 negotiations again. - From the Key Group drop-down list, select a Diffie-Hellman group. In our example, we select Diffie-Hellman Group 14.
Diffie-Hellman (DH) groups determine the strength of the key used in the key exchange process. - Click OK. Leave all other Phase 1 settings with their default values.
- Click OK.
The gateway you added appears in the Gateways list.
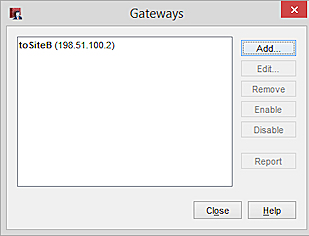
- Click Close to close the Gateways dialog box.
For more information about IPSec VPN negotiations, go to About IPSec VPN Negotiations.
For more information about Diffie-Hellman groups, go to About Diffie-Hellman Groups.
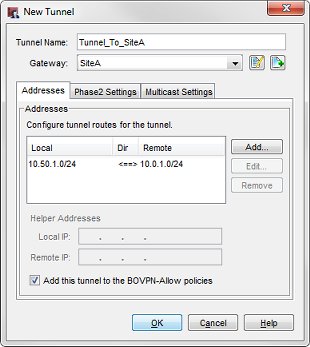
Add a VPN Tunnel
After you define gateways, you can make tunnels between them. The process for making a tunnel includes:
- Specify routes (local and remote endpoints for the tunnel)
- Configure Phase 2 of the Internet Key Exchange (IKE) negotiation
From Policy Manager:
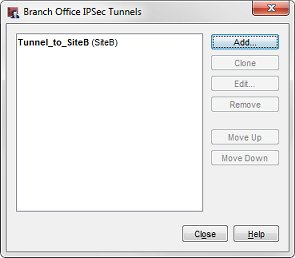
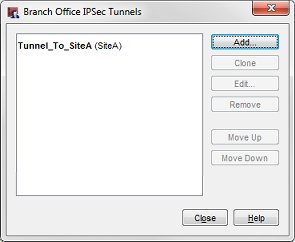
- Select VPN > Branch Office Tunnels.
The Branch Office IPSec Tunnels dialog box appears. - Click Add.
The New Tunnel dialog box appears.
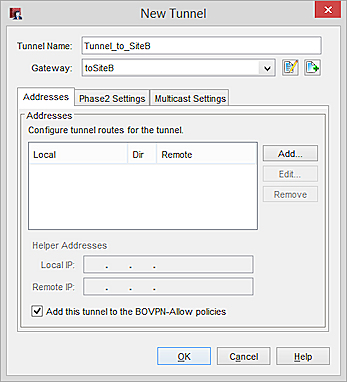
- In the Tunnel Name text box, type a name for the tunnel.
- From the Gateway drop-down list, select the gateway you just created.
- Select the Add this tunnel to the BOVPN-Allow policies check box at the bottom of the dialog box if you want to add the tunnel to the BOVPN-Allow.in and BOVPN-Allow.out policies. These policies allow all traffic that matches the tunnel routes. If you want to restrict traffic through the tunnel, clear this check box and use the BOVPN Policy Wizard to create policies for types of traffic that you want to allow through the tunnel. For more information, go to Define Custom Tunnel Policies.
- In the Addresses area, click Add.
The Tunnel Route Settings dialog box appears.
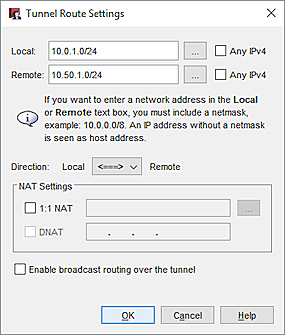
- In the Local and Remote sections, configure one of these options to specify which devices behind the local Firebox can communicate through the tunnel.
- (Fireware v12.3.1 or lower) Type an IPv4 address in the text box.
- (Fireware v12.4 or higher) Type an IPv4 or IPv6 address in the text box.
The IP address you specify must be of the same address family (IPv4 or IPv6) as the gateway. - Click the button adjacent to the Local drop-down list to specify a host IP address, network address, range of host IP addresses, or a host name.
For IPv6, if you select Host Name, your local computer must be able to resolve the host name to an IPv6 address. - (Fireware v12.4 or higher) Select the Any IPv4 or Any IPv6 box to specify a zero route (0.0.0.0/0 or ::/0).
- From the Direction drop-down list, click the tunnel direction. The tunnel direction determines which endpoint of the VPN tunnel can start a VPN connection through the tunnel.
- Click OK.
The tunnel route appears in the Addresses tab of the New Tunnel dialog.
Configure the Phase 2 Settings
Phase 2 settings include settings for a security association (SA), which defines how data packets are secured when they are passed between two endpoints. The SA keeps all information necessary for the Firebox to know what it should do with the traffic between the endpoints.
- From the New Tunnel dialog box, select the Phase 2 Settings tab.

- Select the PFS check box to enable Perfect Forward Secrecy (PFS).
PFS makes keys more secure because new keys are not made from previous keys. If a key is compromised, new session keys are still secure. When you specify PFS during Phase 2, a Diffie-Hellman exchange occurs each time a new SA is negotiated. - Select a Diffie-Hellman Group from the drop-down list. In our example, we select Diffie-Helman Group 14.
- The Firebox contains one default proposal, which appears in the IPSec Proposals list. This proposal specifies the ESP data protection method, AES 256-bit encryption, and SHA256 authentication. For this example, we use the default proposal. You can either:
- Use the default proposal.
- Remove the default proposal. Then select a different proposal in the drop-down list and click Add.
- Add an additional proposal, as described in Add a Phase 2 Proposal.
- Click OK to return to the Branch Office IPSec Tunnel dialog box.
The tunnel you added appears on the Branch Office IPSec Tunnels list.
- Click Close and save the changes to the Firebox.
The Firebox at Site A is now configured.
Configure Site B
You now use Policy Manager to configure the gateway at Site B that has an Firebox with Fireware 11.x or higher.
Add a VPN Gateway
- Select VPN > Branch Office Gateways.
The Gateways dialog box appears. - Click Add.
The New Gateway dialog box appears. - In the Gateway Name text box, type a name to identify this gateway in Policy Manager.
- Click the General Settings tab.
- In the Credential Method area, select Use Pre-Shared Key.
- (Fireware v12.5.4 or higher) Select String-Based or Hex-Based. The default setting is String-Based. For information about hex-based keys, go to Hex-Based Pre-Shared Keys.
- Type the shared key.
This shared key must use only standard ASCII characters. - In the Gateway Endpoints section, click Add.
The New Gateway Endpoints Settings dialog box appears.
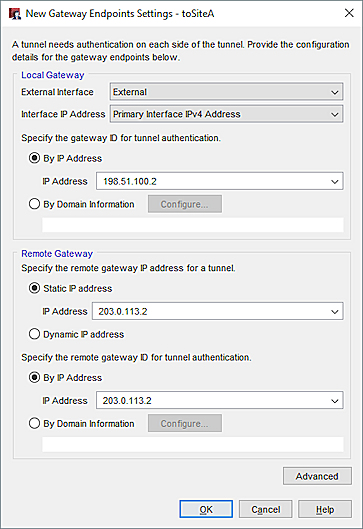
- In the External Interfacedrop-down list, select the interface that has the external (public) IP of the Site B Firebox.
- (Fireware v12.2 or higher) To specify an IP address, in the Interface IP Address drop-down list, select Primary Interface IP Address or select a secondary IP address that is already configured on the selected external interface. Tip!
- Select By IP Address and type the primary IP address of the Firebox interface.
In Fireware v12.4 or higher, you must specify an IP address type that matches the Address Family setting you configured earlier. For example, if you specified IPv6 Addresses, you must specify an IPv6 address in the By IP Address text box. - In the Remote Gateway section, select Static IP Address.
- In the adjacent text box, type the external (public) IP address of the Site A Firebox.
- Select By IP Address.
- n the adjacent text box, type the external (public) IP address of the Site A Firebox.
- Click OK.
The gateway pair you defined appears in the list of gateway endpoints.
Configure the Phase 1 Settings
Phase 1 of establishing an IPSec connection is where the two peers make a secure, authenticated channel they can use to communicate. This is known as the ISAKMP Security Association (SA).
- Select the Phase 1 Settings tab.
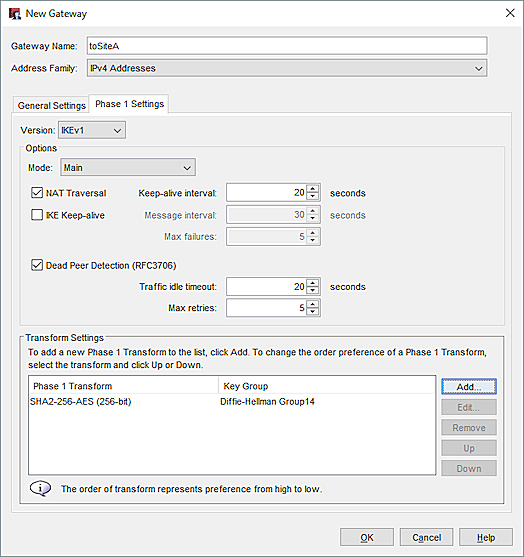
- From the Mode drop-down list, select Main.
The example uses Main Mode because both endpoints have static IP addresses. If one endpoint has a dynamic IP address, you must use Aggressive mode. - Select NAT Traversal and Dead Peer Detection (RFC3706).
- In the Transform Settings section, select the default transform and click Edit.
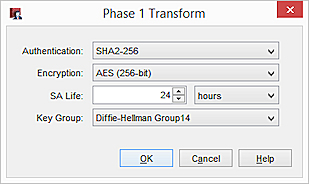
- From the Authentication and Encryption drop-down lists, select SHA2-256 and AES (256-bit).
- In the SA Life text box, type 24. In the drop-down list, select Hours.
- In the Key Group drop-down list, select a Diffie-Helman Group. In our example, we select Diffie-Hellman Group 14.
- Click OK. Keep the default values for all other Phase 1 settings.
- Click Close to close the Gateways dialog box.
The gateway you added appears on the Branch Office VPN page in the Gateways list.
Add a VPN Tunnel
After you define gateways, you can make tunnels between them. When you make a tunnel you must specify:
- Routes (local and remote endpoints for the tunnel)
- Settings for Phase 2 of the Internet Key Exchange (IKE) negotiation
To add a VPN tunnel:
- Select VPN > Branch Office Tunnels.
The Branch Office IPSec Tunnels dialog box appears. - Click Add.
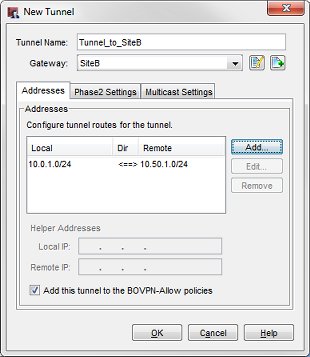
The New Tunnel dialog box appears. - In the Tunnel Name text box, type a name for the tunnel.
- From the Gateway drop-down list, select the gateway you created.
- To add the tunnel to the BOVPN-Allow.in and BOVPN-Allow.out policies, select the Add this tunnel to the BOVPN-Allow policies check box. These policies allow all traffic that matches the tunnel routes. If you want to restrict traffic through the tunnel, clear this check box and use the BOVPN Policy Wizard to create policies for types of traffic that you want to allow through the tunnel.
- In the Addresses area, click Add.
The Tunnel Route Settings dialog box appears.
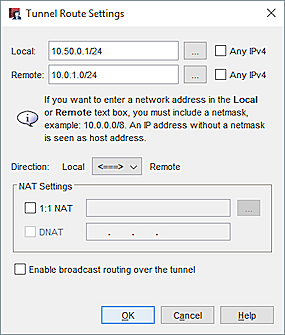
- In the Local and Remote sections, configure one of these options to specify which devices behind the local Firebox can communicate through the tunnel.
- (Fireware v12.3.1 or lower) Type an IPv4 address in the text box.
- (Fireware v12.4 or higher) Type an IPv4 or IPv6 address in the text box.
The IP address you specify must be of the same address family (IPv4 or IPv6) as the gateway. - Click the button adjacent to the Local drop-down list to specify a host IP address, network address, range of host IP addresses, or a host name.
For IPv6, if you select Host Name, your local computer must be able to resolve the host name to an IPv6 address. - (Fireware v12.4 or higher) Select the Any IPv4 or Any IPv6 box to specify a zero route (0.0.0.0/0 or ::/0).
- Click OK.
The tunnel route appears in the Addresses tab of the New Tunnel dialog.
Configure the Phase 2 Settings
Phase 2 settings include settings for a security association (SA), which defines how data packets are secured when they are passed between two endpoints. The SA keeps all information necessary for the Firebox to know what it should do with the traffic between the endpoints.
- From the New Tunnel dialog box, click the Phase 2 Settings tab.
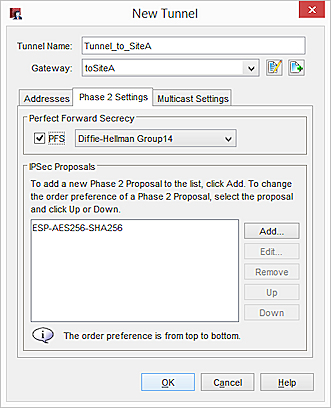
- Select the PFS check box to enable Perfect Forward Secrecy (PFS).
- If you enable PFS, in the Enable Perfect Forward Secrecy drop-down list, select a Diffie-Hellman group. In our example, we select Diffie-Hellman Group 14.
- The Firebox contains one default proposal, which appears in the IPSec Proposals list. This proposal specifies the ESP data protection method, AES 256-bit encryption, and SHA256 authentication. For this example, we use the default proposal. You can either:
- Use the default proposal.
- Remove the default proposal. Then select a different proposal in the drop-down list and click Add.
- Add an additional proposal, as described in Add a Phase 2 Proposal.
- Click OK to return to the Branch Office IPSec Tunnel dialog box.
The tunnel you added appears on the Branch Office IPSec Tunnels list.
- Click Close and save the changes to your Firebox.
The Firebox at Site B is now configured.
After both ends of the tunnel are configured, the tunnel opens and traffic passes through the tunnel. If the tunnel does not work, examine the log files on both Fireboxes for the time period you tried to start the tunnel. Log messages appear in the log file to indicate where the failure is located in the configuration and which settings might be part of the problem. You can also review the log messages in real-time with Firebox System Manager.