Applies To: Locally-managed Fireboxes
RADIUS (Remote Authentication Dial-In User Service) authenticates the local and remote users on a company network. RADIUS is a client/server system that keeps the authentication information for users, remote access servers, VPN gateways, and other resources in one central database.
In Fireware v12.5 or higher:
- SecurID is part of the RADIUS configuration.
- You can configure more than one primary RADIUS server.
- You must manually specify a domain name for new RADIUS servers.
- To authenticate, users must type the domain name you specified in the RADIUS configuration. Mobile VPN and Access Portal users must type the domain name to authenticate to a server other than the primary server.
If your configuration includes a RADIUS server, and you upgrade from Fireware v12.4.1 or lower to Fireware v12.5 or higher, the Firebox automatically uses RADIUS as the domain name. To authenticate, users must select RADIUS as the server and type RADIUS as the domain name. If a user types a domain name other than RADIUS, authentication fails. This applies to authentication through the Web UI, WatchGuard System Manager v12.5 or higher (to a Firebox with any Fireware version), Mobile VPN clients, and the Access Portal.
For information about the RADIUS protocol, go to How RADIUS Server Authentication Works.
To configure SecurID authentication, go to Configure SecurID Authentication.
Authentication Key
The authentication messages to and from the RADIUS server use an authentication key. This authentication key, or shared secret, must be the same on the RADIUS client and server. Without this key, there is no communication between the client and server.
RADIUS Authentication Methods
The Firebox uses only these authentication protocols for user authentication with a RADIUS server:
- Web authentication, Mobile VPN with SSL authentication, and Mobile VPN with IPSec authentication — PAP (Password Authentication Protocol)
- Mobile VPN with L2TP authentication — MSCHAPv2 (Microsoft Challenge-Handshake Authentication Protocol version 2)
- Mobile VPN with IKEv2 authentication — EAP-MSCHAPv2
- Authentication with WPA Enterprise and WPA2 Enterprise authentication methods — EAP (Extensible Authentication Protocol)
RADIUS and Multi-Factor Authentication
You can use RADIUS server authentication with multi-factor authentication (MFA).
If the Firebox does not receive a response to an MFA challenge, the Firebox marks the RADIUS server as dead for the Dead Time duration. The Firebox does not send authentication requests for other users to the RADIUS server during this time. To avoid this issue, we recommend that you change the default Dead Time value in the Firebox RADIUS settings:
- If you configure only a primary RADIUS server, specify a Dead Time of 0 minutes.
- If you also configure a backup RADIUS server, specify a Dead Time of 10 minutes.
If a user does not respond to an MFA challenge, the authentication request times out and AuthPoint sends a response to the Firebox.
Before You Begin
Before you configure your Firebox to use a RADIUS authentication server, you must have this information for each RADIUS server:
- Primary RADIUS server — IP address and RADIUS port
- Secondary RADIUS server (optional) — IP address and RADIUS port
- Shared secret — Case-sensitive password that is the same on the Firebox and the RADIUS server
- Authentication methods — Set your RADIUS server to allow the authentication method your device uses: PAP, MSCHAPv2, WPA Enterprise, WPA2 Enterprise, or WPA/WPA2 Enterprise
Use RADIUS Server Authentication with Your Firebox
To use RADIUS server authentication with your Firebox, you must:
- Add the IP address of the Firebox to the RADIUS server to configure the Firebox as a RADIUS client.
- Enable and specify the RADIUS server in the Firebox configuration.
- In the Firebox RADIUS configuration, specify the server IP address and shared secret.
- Add RADIUS users or groups in the Firebox configuration.
- Add RADIUS user names or group names to Firebox policies.
Configure RADIUS
- Select Authentication > Servers.
The Authentication Servers page appears.
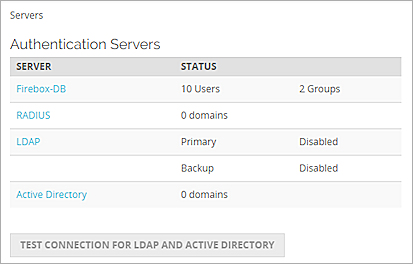
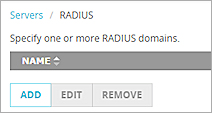
- From the Server list, click RADIUS.
The RADIUS page appears. - Click Add.
The Add page appears.
- In the Domain Name text box, type the domain name or server name for this RADIUS server. Users must specify this domain name on the user login page. You cannot change the domain name after you save the settings.
- In the IP Address text box, type the IP address of the RADIUS server.
Fireware v12.4 or higher supports IPv4 and IPv6 addresses. Fireware v12.3.x or lower supports only IPv4 addresses. - In the Port text box, type the port number RADIUS uses for authentication. The default port number is 1812. Older RADIUS servers might use port 1645.
- In the Shared Secret text box, type the shared secret used by the Firebox and the RADIUS server. The shared secret is case-sensitive, and it must be the same on the Firebox and the RADIUS server. The shared secret cannot include only space characters.
Fireware v12.7.1 or higher supports 256-character shared secrets. Fireware v12.4 or higher supports 64-character shared secrets. Fireware v12.3.x or lower supports 36-character shared secrets. - In the Confirm Secret text box, type the shared secret again.
- In the Timeout text box, type a value in seconds. The timeout value is the amount of time the device waits for a response from the authentication server before it tries to connect again. The default value is 10 seconds.
- In the Retries text box, type the number of times the device tries to connect to the authentication server before it reports a failed connection for one authentication attempt. The default value is 3.
If you use AuthPoint MFA with a Firebox, we recommend that you configure the total timeout settings for RADIUS authentication on the Firebox to be greater than the default AuthPoint timeout of 60 seconds. With the default settings, if a user does not approve the AuthPoint push notification that is sent to them within 30 seconds, the Firebox will fail over to another server, even though the current server is not down.
- In the Dead Time text box, type the amount of time after which an inactive server is marked as active again.
The default value is 10 minutes. In Fireware v12.5.3 or lower, the default value is 3 minutes. - From the Dead Time drop-down list, select Minutes or Hours to set the duration.
After an authentication server has not responded for a period of time, it is marked as inactive. Additional authentication attempts will not try this server until it is marked as active again.If the Firebox does not receive a response to an MFA challenge, the Firebox marks the RADIUS server as dead for the Dead Time duration. The Firebox does not send authentication requests for other users to the RADIUS server during this time. To avoid this issue, specify a Dead Time of 0 minutes if you configure only a primary RADIUS server. If you also configure a backup RADIUS server, specify a Dead Time of 10 minutes.
- In the Group Attribute text box, type an attribute value. The default group attribute is FilterID, which is RADIUS attribute 11.
The group attribute value is used to set the attribute that carries the User Group information. You must configure the RADIUS server to include the Filter ID string with the user authentication message it sends to the device. For example, engineerGroup or financeGroup. This information is then used for access control. The device matches the FilterID string to the group name configured in the device policies.

- To require the message-authenticator attribute, select the Require the Message-Authenticator Attribute check box. This attribute validates the integrity of RADIUS packets, and protects against vulnerabilities such as Blast RADIUS . If this attribute is required by an external client, such as NPS, you must configure your RADIUS server on the Firebox to require this attribute or authentication will fail.
- To add a backup RADIUS server, in the Backup Server Settings section, select Enable Backup RADIUS Server.
- Repeat Steps 4–14 to configure the backup server. Make sure the shared secret is the same on the primary and backup RADIUS server.
For more information about Backup Authentication Servers, go to Use a Backup Authentication Server. - If the RADIUS domain uses SecurID, select SecurID.
- Click
 .
.
Or, select Setup > Authentication > Authentication Servers.
The Authentication Servers dialog box appears. - Select the RADIUS tab.
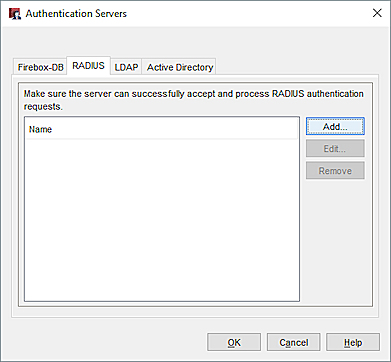
- Click Add.
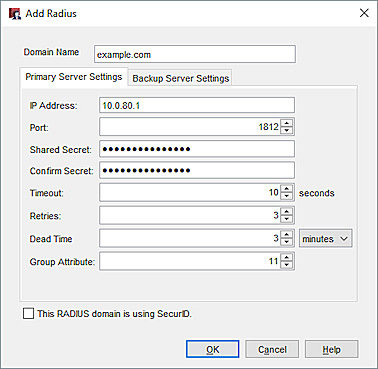
The Add RADIUS dialog box appears. - In the Domain Name text box, type the domain name or server name for the RADIUS server. Users must specify this domain name on the user login page. You cannot change the domain name after you save the settings.
- In the IP Address text box, type the IP address of the RADIUS server.
Fireware v12.4 or higher supports IPv4 and IPv6 addresses. Fireware v12.3.x or lower supports only IPv4 addresses. - In the Port text box, make sure that the port number RADIUS uses for authentication appears.
The default port number is 1812. Older RADIUS servers might use port 1645. - In the Shared Secret text box, type the shared secret between the device and the RADIUS server. The shared secret is case-sensitive, and it must be the same on the device and the RADIUS server. The shared secret cannot include only space characters.
Fireware v12.7.1 or higher supports 256-character shared secrets. Fireware v12.4 or higher supports 64-character shared secrets. Fireware v12.3.x or lower supports 36-character shared secrets. - In the Confirm Secret text box, type the shared secret again.
- Type or select the Timeout value. The timeout value is the amount of time the device waits for a response from the authentication server before it tries to connect again. The default value is 10 seconds.
- In the Retries text box, type or select the number of times the device tries to connect to the authentication server before it reports a failed connection for one authentication attempt. The default value is 3.
If you use AuthPoint MFA with a Firebox, we recommend that you configure the total timeout settings for RADIUS authentication on the Firebox to be greater than the default AuthPoint timeout of 60 seconds. With the default settings, if a user does not approve the AuthPoint push notification that is sent to them within 30 seconds, the Firebox will fail over to another server, even though the current server is not down.
- In the Dead Time text box, type or select the amount of time after which an inactive server is marked as active again.
The default value is 10 minutes. In Fireware v12.5.3 or lower, the default value is 3 minutes. - From the Dead Time drop-down list, select Minutes or Hours to set the duration.
After an authentication server has not responded for a period of time, it is marked as inactive. Additional authentication attempts will not try this server until it is marked as active again.If a user does not respond to a multi-factor challenge, the Firebox marks the RADIUS server as dead for the Dead Time duration. The Firebox does not send authentication requests for other users to the RADIUS server during this time. To avoid this issue, specify a Dead Time of 0 minutes if you configure only a primary RADIUS server. If you also configure a backup RADIUS server, specify a Dead Time of 10 minutes.
- In the Group Attribute text box, type or select an attribute value. The default group attribute is FilterID, which is RADIUS attribute 11.
The group attribute value is used to set the attribute that carries the User Group information. You must configure the RADIUS server to include the Filter ID string with the user authentication message it sends to the device. For example, engineerGroup or financeGroup. This information is then used for access control. The device matches the FilterID string to the group name configured in the device policies. - To require the message-authenticator attribute, select the Require the Message-Authenticator Attribute check box. This attribute validates the integrity of RADIUS packets, and protects against vulnerabilities such as Blast RADIUS . If this attribute is required by an external client, such as NPS, you must configure your RADIUS server on the Firebox to require this attribute or authentication will fail.
- To add a backup RADIUS server, on the Backup Server Settings tab, select Enable a backup RADIUS server.
- Repeat Steps 5–14 to configure the backup server. Make sure the shared secret is the same on the primary and backup RADIUS server.
For more information about Backup Authentication Servers, go to Use a Backup Authentication Server.
- Click OK.
- Save the Configuration File.
About Third-Party Authentication Servers
Use Users and Groups in Policies
Enterprise Wireless Authentication with RADIUS
RADIUS Authentication with Active Directory For Mobile VPN Users
Configure Windows Server 2016 or 2012 R2 to authenticate mobile VPN users with RADIUS and Active Directory in the WatchGuard Knowledge Base