Deployment Overview
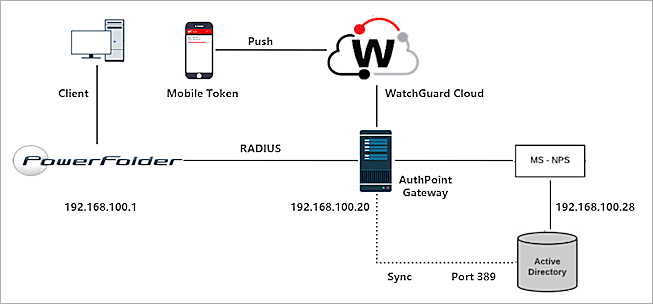
This document describes how to set up AuthPoint multi-factor authentication (MFA) with PowerFolder for Active Directory users.
PowerFolder must already be configured and deployed before you set up MFA with AuthPoint.
Integration Summary
The hardware and software used in this guide include:
- PowerFolder Server v14.11.100.20
- AuthPoint Gateway v5.3.1.184 or higher
- Windows Server 2016 with Microsoft Network Policy Server (NPS) and Active Directory Domain Services
PowerFolder Configuration for RADIUS Authentication
AuthPoint communicates with various cloud-based services and service providers with the RADIUS protocol. This diagram shows an overview of the configuration required for RADIUS authentication.
Before You Begin
Before you begin these procedures, make sure that:
- You have installed and configured Active Directory Domain Services
- You have installed Network Policy and Access Services, which includes Network Policy Server (NPS)
Configure Microsoft NPS Server
To enable users synced from Active Directory to successfully authenticate with MS-CHAPv2, you must configure Microsoft Network Policy Server (NPS). NPS is required to validate the user credentials from MS-CHAPv2 RADIUS requests against Active Directory.
You must register NPS in the Active Directory domain.
For instructions to configure Active Directory Domain Services, see the Microsoft documentation for Active Directory.
- On the Windows server, run Server Manager.
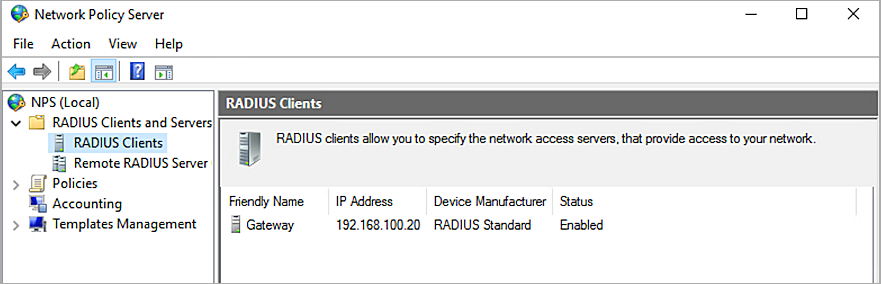
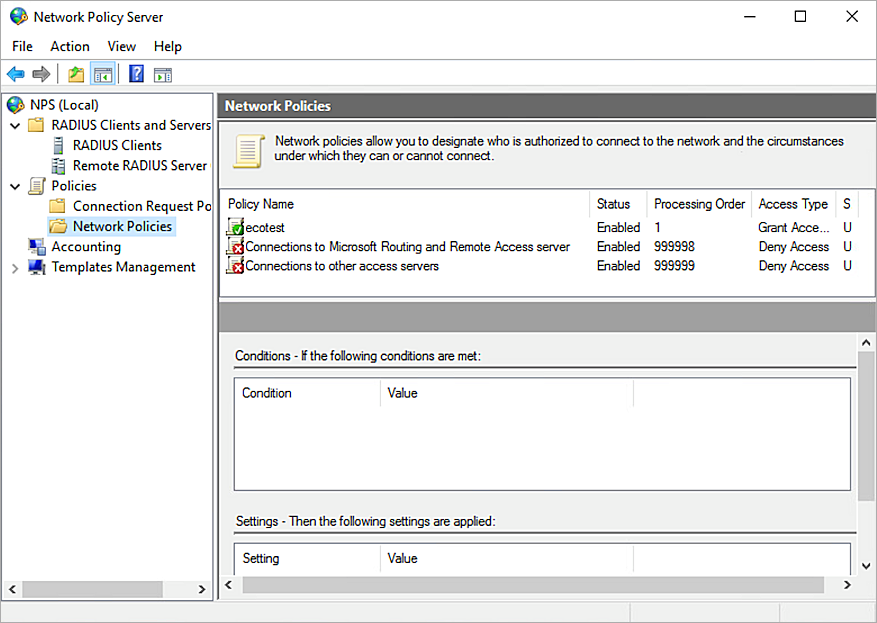
- Select Tools > Network Policy Server.
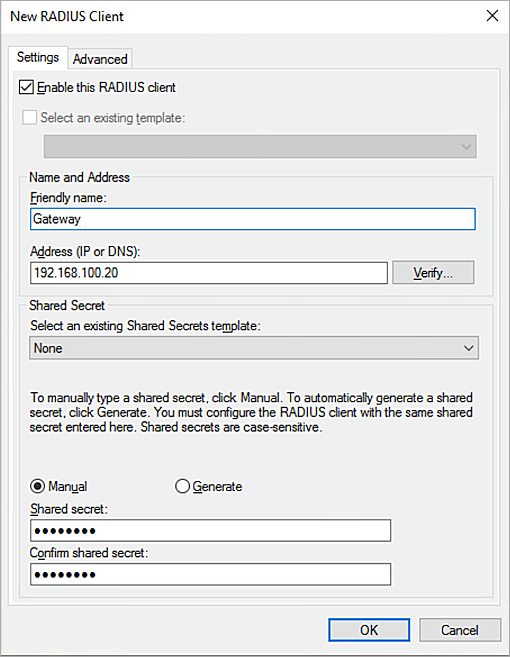
The Network Policy Server console appears. - Select RADIUS Clients and Servers > RADIUS Clients.
- Right-click RADIUS Clients and select New.
The New RADIUS Client window appears. - In the Friendly name text box, type a name.
- In the Address (IP or DNS) text box, type the IP address of the AuthPoint Gateway. In our example, the IP address of the AuthPoint Gateway is 192.168.100.20.
- In the Shared secret and Confirm shared secret text boxes, type a shared secret key. This key is used to communicate with the RADIUS server (AuthPoint Gateway).
You must use the same shared secret key when you configure your PowerFolder in the Configure PowerFolder section and your RADIUS client resource in the Add a RADIUS Client Resource in AuthPoint section.
- Click OK.
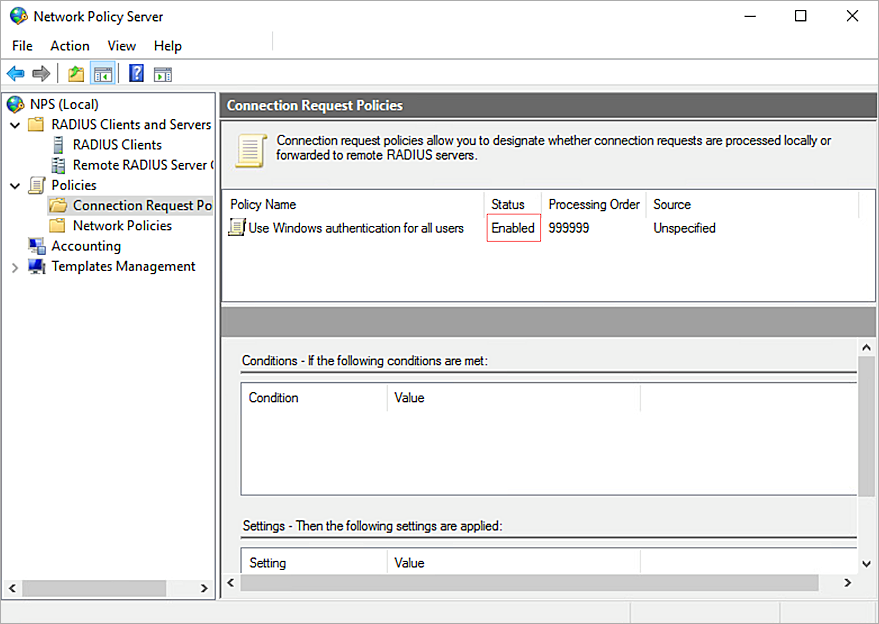
- Select Polices > Connection Request Policies. Make sure the default policy is enabled.
- Right-click Network Policies and select New.
The New Network Policy window appears. - In the Policy Name text box, type a name for this policy. In our example, we type ecotest.
- Click Next.
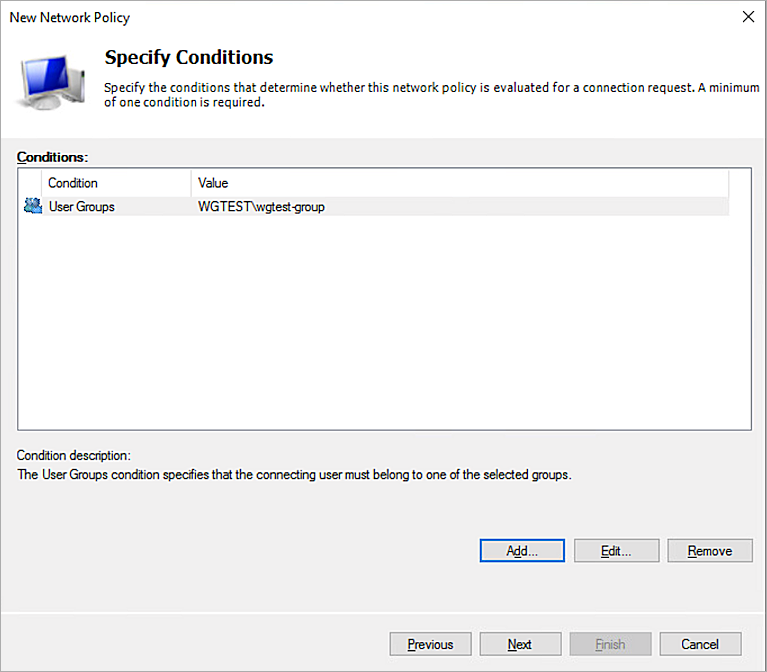
- In the Specify Conditions section, click Add.
- Select User Groups. Click Add > Add Groups.
- In the Enter the object name to select text box, type the group name. The name of this group must match the name of the Active Directory group your users belong to.
- Click OK.
- Click OK.
- Click Next.
- Click Next.
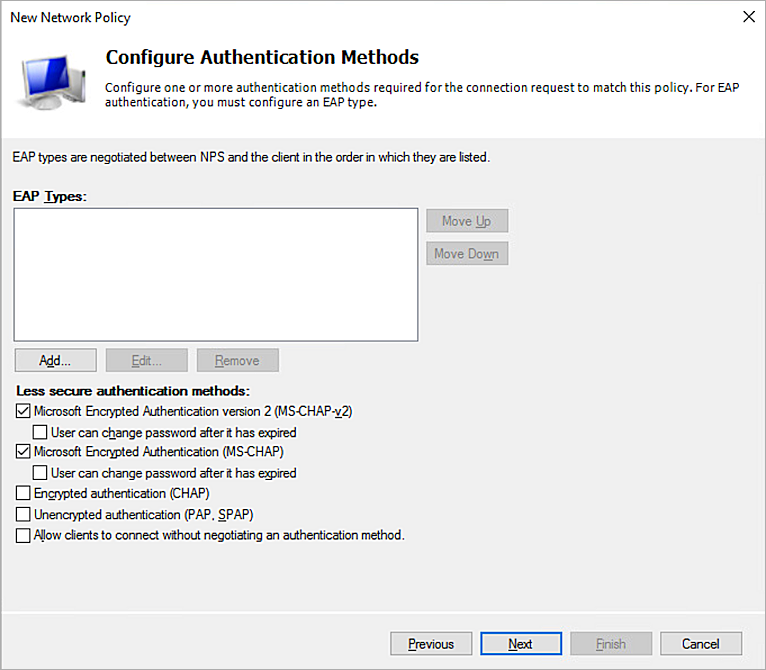
- In the Configure Authentication Methods section, clear the User can change password after it has expired check box.
- Click Next.
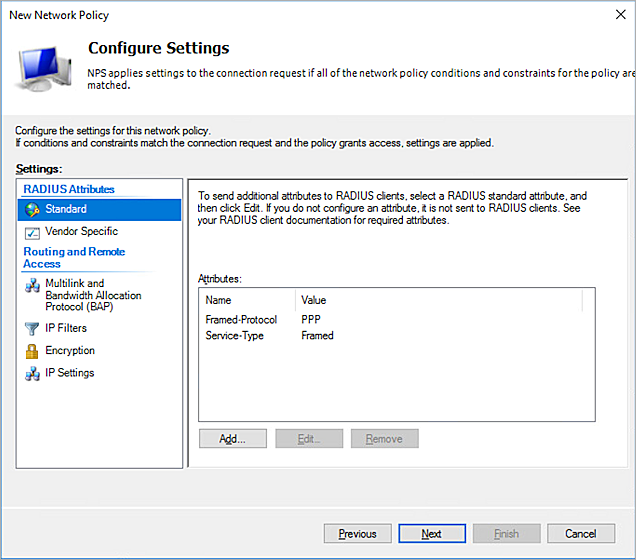
- Click Next.
- Click Next.
- Click Finish.
- Right-click NPS (Local) and select Register server in Active Directory.
- Click OK.
- Click OK.
Configure PowerFolder
- Log in to the PowerFolder Server web UI as an admin at http://<PowerFolder Server host name or IP address:8080>.
- Click Preferences.
- For Authentication, click Configure.
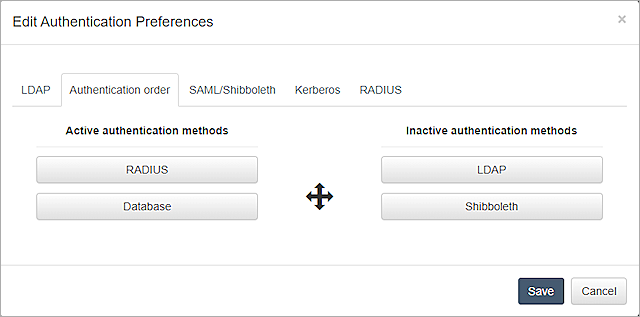
The Edit Authentication Preferences page appears. - Select the Authentication order tab.
- Move RADIUS and Database from the Inactive authentication methods section to the Active authentication methods section.
- Select the RADIUS tab.
- From the RADIUS drop-down list, select MSCHAPV2.
- In the Hostname text box, type the IP address and port of the AuthPoint Gateway. In our example, the IP address of the AuthPoint Gateway is 192.168.100.20 and the default port is 1812.
- In the Shared secret text box, type a shared secret key. This is the password that the RADIUS server (AuthPoint Gateway) and the RADIUS client (PowerFolder) will use to communicate.
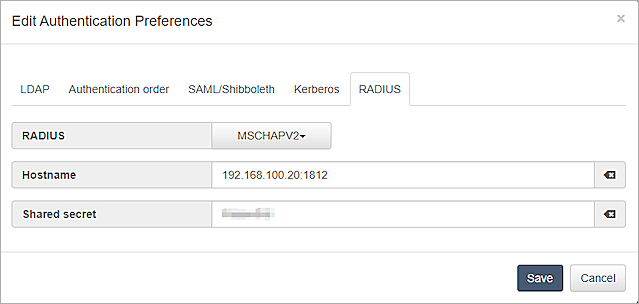
- Click Save.
Configure AuthPoint
Before AuthPoint can receive authentication requests from PowerFolder, you must:
- Specify PowerFolder as a RADIUS client resource in AuthPoint.
- Add a Zero Trust authentication policy for the PowerFolder RADIUS client resource or add the PowerFolder RADIUS client resource to an existing authentication policy.
- Bind the PowerFolder RADIUS client resource to the AuthPoint Gateway.
Add a RADIUS Client Resource in AuthPoint
From the AuthPoint management UI:
- From the navigation menu, select Resources.
Click Add Resource.
The Add Resource page opens.
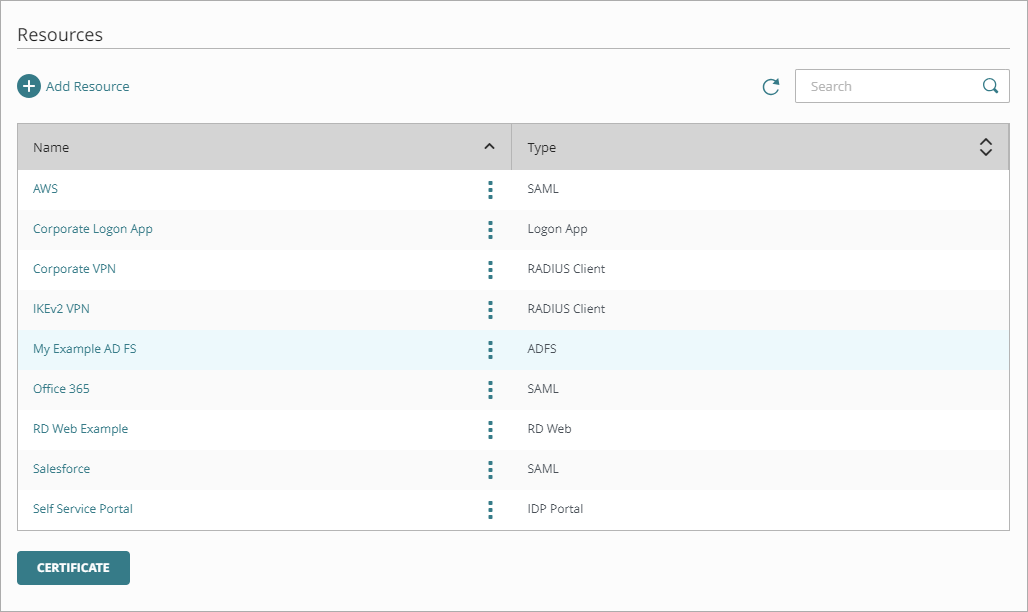
- From the Type drop-down list, select RADIUS Client.
Additional fields appear.
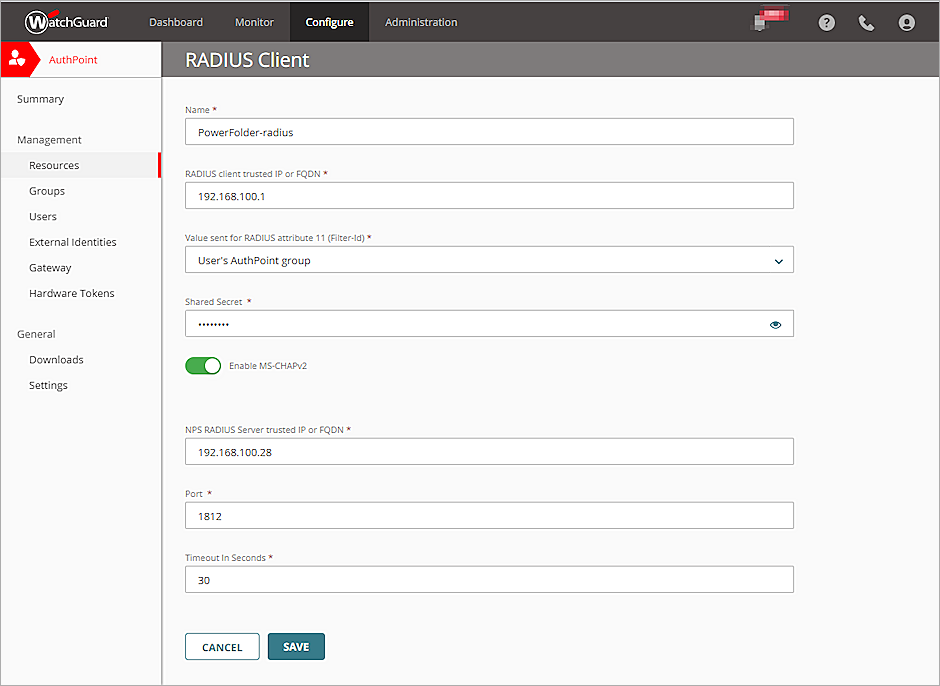
- In the Name text box, type a descriptive name for the resource.
- In the RADIUS client trusted IP or FQDN text box, type the IP address that your RADIUS client uses to send RADIUS packets to the AuthPoint Gateway.
- From the Value sent for RADIUS attribute 11 (Filter-Id) drop-down list, you can choose to send the user's AuthPoint group or the user's Active Directory groups.
- In the Shared Secret text box, type the shared secret key that you specified in the Configure Microsoft NPS Server and Configure PowerFolder section. This is the password that the RADIUS server (AuthPoint Gateway) and the RADIUS client (PowerFolder) will use to communicate.
- To configure the RADIUS client resource to accept MS-CHAPv2 authentication requests, click the Enable MS-CHAPv2 toggle.
Additional fields appear. - In the NPS RADIUS Server trusted IP or FQDN text box, type the IP address or fully qualified domain name (FQDN) of the NPS RADIUS server.
- In the Port text box, type 1812.
If NPS and the Gateway are installed on the same server, the port that the Gateway uses to communicate with NPS must be different than the port that the Gateway uses to communicate with the RADIUS client.
- In the Timeout In Seconds text box, type 30.
- Click Save.
Add a Group in AuthPoint
You must have at least one user group in AuthPoint to configure MFA. If you already have a group, you do not have to add another group.
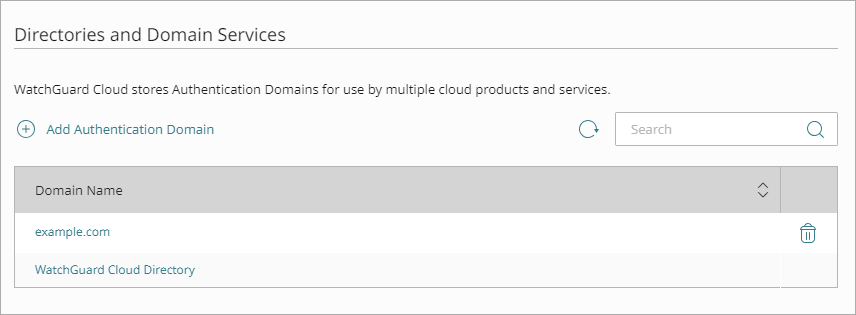
To add a WatchGuard Cloud-hosted group to the WatchGuard Cloud Directory:
- Go to Configure > Directories and Domain Services.
- Click the WatchGuard Cloud Directory domain name. If you have not yet added the WatchGuard Cloud Directory, click Add Authentication Domain and select the WatchGuard Cloud Directory.
The New Group page appears.
- In the Groups tab, click Add Group.
- In the Group Name text box, type a descriptive name for the group.
- (Optional) In the Description text box, type a description of the group.

- Click Save.
Your group is added to the WatchGuard Cloud Directory and to AuthPoint.
Add a Zero Trust Authentication Policy
Zero Trust policies specify which resources users can authenticate to and which authentication methods they can use.
You must have at least one Zero Trust authentication policy that includes the PowerFolder RADIUS client resource. If you already have Zero Trust authentication policies, you do not have to create a new authentication policy. You can add this resource to your existing authentication policies.
Users that do not have an authentication policy for a specific resource cannot authenticate to log in to that resource.
To configure a Zero Trust authentication policy:
- Go to Configure > Zero Trust. If you have a Service Provider account, you must select an account from Account Manager.
- Click Add Policy.
- Type a name for this policy.
- In the Target section, from the Content drop-down list, select which groups this policy applies to. You can make multiple selections to add multiple groups.
- In the Resources section, select the AuthPoint resources this policy applies to.
- In the Conditions section, select the conditions that apply to this policy. When you add a condition to an authentication policy, the policy applies only to user authentications that match the policy and the policy conditions. For example, if you add a time schedule to a policy, the policy only applies to user authentications that occur within that time schedule. Users who only have a policy that includes a time schedule do not get access to the resource when they authenticate outside of the allowed times (because they do not have a policy that applies, not because authentication is denied). For more information, go to About Zero Trust Conditions
For RADIUS authentication, policies that have a Network Location do not apply because AuthPoint does not have the IP address of the user.
- (Optional) To create a new condition, click Add New Condition. After you create a new condition, you must still add the condition to the policy.
- From the Type drop-down list, select the type of condition to add to the policy.
- From the Name drop-down list, select which condition of the chosen type to add to the policy.
- To add more conditions, repeat Step 6.
If you add conditions to a policy, we recommend that you create a second policy for the same groups and resources without the conditions. Assign a higher priority to the policy with the policy objects. For more information about priority, go to About Zero Trust Policy Precedence.
- In the Action section, select an option to specify whether to allow or deny authentications for the resources in this policy. In our example, we want to allow authentications.
- Allow — Allow user groups in this policy access to the resources associated with this policy.
- Deny — Deny authentications when users in the groups associated with this policy try to authenticate to the resources associated with this policy.
- If you allow access with this policy, select the Password and Push check boxes.
QR code authentication is not supported for RADIUS client resources. OTP authentication is not supported for RADIUS client resources with MS-CHAPv2 enabled.
- Click Save.
Your policy is created and added to the end of the policy list. - Review the order of your policies and adjust as necessary. For more information about priority, go to About Zero Trust Policy Precedence.
Bind the RADIUS Resource to a Gateway
To use RADIUS authentication with AuthPoint, you must have the AuthPoint Gateway installed on your corporate network and you must assign your RADIUS resources to the Gateway in the AuthPoint management UI. The Gateway functions as a RADIUS server.
If you have not already configured and installed the AuthPoint Gateway, see About Gateways.
To assign your RADIUS resources to the Gateway:
- From the navigation menu, select Gateway.
- Select the Name of the Gateway.
-
From the RADIUS section, in the Port text box, type the port number used to communicate with the Gateway. The default ports are 1812 and 1645.
If you already have a RADIUS server installed that uses port 1812 or 1645, you must use a different port for the AuthPoint Gateway.
- From the Select a RADIUS Resource drop-down list, select your RADIUS client resource.
- Click Save.
Sync Users to AuthPoint from Active Directory
You must create AuthPoint user accounts for your users. To sync users from Active Directory, you must add an LDAP external identity and create one or more queries.
In AuthPoint, LDAP external identities represent external user databases. They connect to user databases to get user account information and validate passwords. The queries you add to an external identity specify which users to sync from your Active Directory or LDAP database. They pull user information and create AuthPoint user accounts for the users that are found.
For detailed instructions to sync users from Active Directory, see Sync Users from Active Directory or LDAP.
Test the Integration
To test AuthPoint MFA with PowerFolder, you authenticate with a mobile token on your mobile device. For RADIUS resources with MS-CHAPv2 enabled, you authenticate with a push notification (you receive a push notification in the mobile app that you must approve to authenticate).
- Start the PowerFolder client.
- In the Username/Email text box, type the user name or email address associated with your AuthPoint user account. This should be a user that is synced from Active Directory or an LDAP database.
- In the Password text box, type your password.
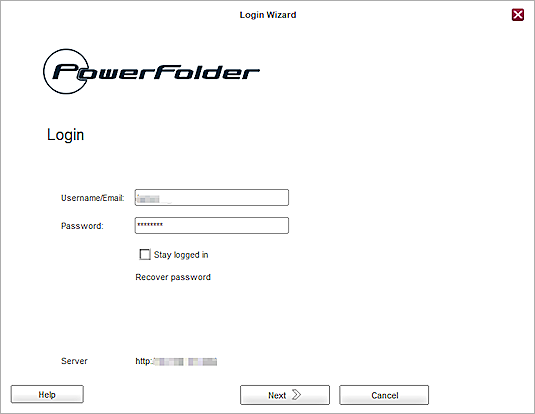
- Click Next.
- Approve the authentication request that is sent to your mobile device.
The first log in to PowerFolder will fail. PowerFolder then creates an account with the user name or email that you just used to log in.
- Log in to PowerFolder Server with the administrator account.
- Select Accounts.
- Find the account that PowerFolder just created and activate it.
- Repeat the Steps 1—5 to authenticate and log in to PowerFolder.