Applies To: Cloud-managed Fireboxes, Locally-managed Fireboxes
The Search Engine report displays details of web searches made from host computers with these search engines:
- bing.com
- google.com
- google.co.uk
- google.ie
- google.ca
This report is available when log messages with data for this report exist in the specified time frame. To make sure that your Firebox sends log messages required to generate this report, follow the steps to Enable Logging for this Report.
How to Use this Report
This report can help you to identify any searches performed by your users for inappropriate or unsafe content. For example, you could review the search query data and identify users who search for terms related to violence or drug use.
View the Report
This report is available in WatchGuard Cloud only and only for Fireboxes with the Total Security Suite or the Basic Security Suite with a Data Retention License.
- Log in to WatchGuard Cloud.
- Select Monitor > Devices.
- Select a folder or a specific device.
- To select the report date range, click
 .
.
- From the list of reports, select Detail > Search Engine.
The Search Engine report opens.
Pivots
You can use pivots to change the view of the data on the report.
To switch to a different view, select a pivot from the drop-down list above the report.
This report includes these pivots:
Users
Shows search data organized by the authenticated user who made the search.
Hosts
Shows search data organized by the host computer the search originated from.
Search Engine Report Detail View
The Search Engine report is only available as a Detail report.
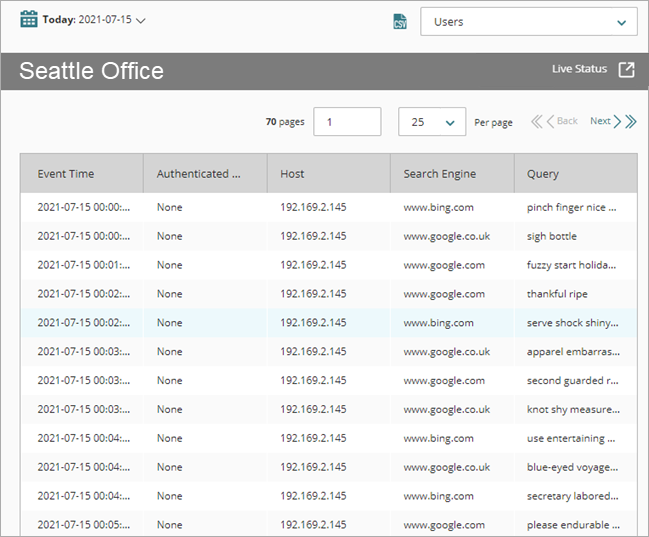
The Search Engine Detail report includes a row for each search made with the supported search engines and includes this detail:
| Column | Description |
|---|---|
| Event Time | Date and time of the search |
| Authenticated User | Name of the user who performed the search If authentication is not enabled on the device, None shows in this column. |
| Host | IP address of the host computer the search originated from |
| Search Engine | URL of the search engine |
| Query | Search text |
Enable Logging for this Report
Logging for cloud-managed Fireboxes is automatically enabled. For locally-managed Fireboxes, you must manually enable logging in Fireware Web UI or Policy Manager. For more information, go to Set Logging and Notification Preferences.
To collect the data required for this report for locally-managed Fireboxes, in Fireware Web UI or Policy Manager:
- In the HTTPS-proxy action that the HTTPS-proxy uses, enable content inspection for the search engines you want to include on the report. Make sure that the certificate the Firebox uses to re-encrypt content is installed on all host computers. For more information, go to HTTPS-Proxy: Content Inspection.
- In the General Settings of the HTTP-proxy action used to inspect content, select the Enable Logging for Reports check box.