Applies To: Cloud-managed Fireboxes, Locally-managed Fireboxes
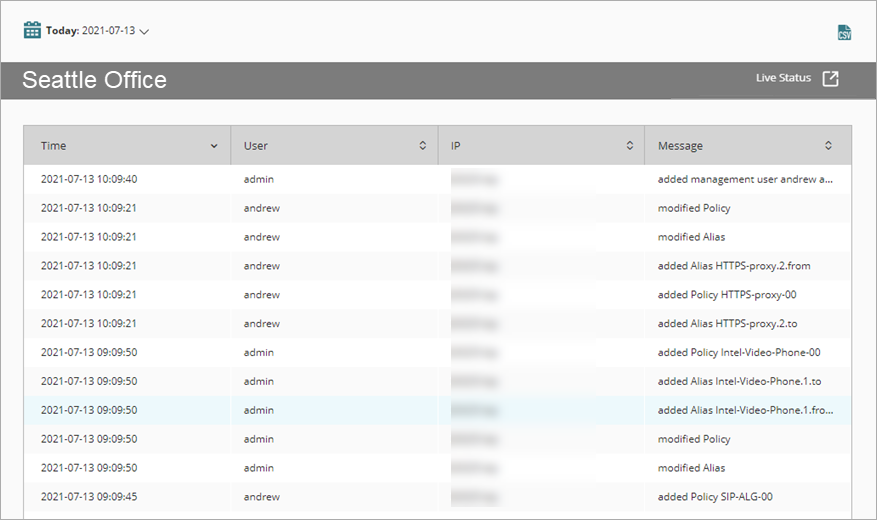
The Audit Trail report shows information about Firebox configuration changes.
This report is available when log messages with data for this report exist in the specified time frame. To make sure that your Firebox sends log messages required to generate this report, follow the steps to Enable Logging for this Report.
How to Use this Report
Use this report to see the history of Firebox configuration changes, and who made each change.
For this report to show who made each configuration change, each administrative user must log in with a unique Device Administrator account. For information about how to add Device Administrator accounts on the Firebox, see Manage Users and Roles on Your Locally-Managed Firebox.
View the Report
This report is available in WatchGuard Cloud and in Dimension.
- Log in to WatchGuard Cloud.
- Select Monitor > Devices.
- Select a folder or a specific device.
- To select the report date range, click
 .
.
- From the list of reports, select Device > Audit Trail.
The Audit Trail report opens.
- To see reports for your Fireboxes or FireClusters, select Home > Devices.
The Devices list opens.
To see reports for your groups of Fireboxes, select Home > Groups.
The Groups list opens. - Select the Name of a Firebox, cluster, or group.
The Tools > Executive Dashboard page opens. - Select the Reports tab.

- Select Device > Audit Trail.
The report opens.
The Audit Trail report includes a row for each configuration change:
| Column | Description |
|---|---|
| Time | Date and time the configuration change was saved to the Firebox |
| User | Name of the administrative user who saved the change |
| IP | IP address of the management computer that saved the change |
| Message | Brief description of what changed |
A single configuration change can trigger other related changes. For example, if an administrator adds or removes a policy, this report can show other related configuration changes to Aliases, Related Hosts, Multi-WAN, and other settings.
Enable Logging for this Report
To collect the data required for this report, in the Logging settings on the Firebox, select the Send log messages when the configuration for this Firebox is changed check box.
For more information about logging settings, see Define Where the Firebox Sends Log Messages.
Logging for cloud-managed Fireboxes is automatically enabled. For locally-managed Fireboxes, you must manually enable logging in Fireware Web UI or Policy Manager. For more information, see Set Logging and Notification Preferences.