HTTP Request: Request Methods
Applies To: Locally-managed Fireboxes
Most browser HTTP requests are in one of two categories: GET or POST operations. Browsers usually use GET operations to download objects such as a graphic, HTML data, or Flash data. More than one GET is usually sent by a client computer for each page, because web pages usually contain many different elements. The elements are put together to make a page that appears as one page to the end user.
Browsers usually use POST operations to send data to a website. Many web pages get information from the end user such as location, email address, and name. If you disable the POST command, the Firebox denies all POST operations to web servers on the external network. This feature can prevent your users from sending information to a website on the external network.
Web-based Distributed Authoring and Versioning (webDAV) is a set of HTTP extensions that allows users to edit and manage files on remote web servers. WebDAV is compatible with Outlook Web Access (OWA). If webDAV extensions are not enabled, the HTTP proxy supports these request methods: HEAD, GET, POST, OPTIONS, PUT, and DELETE. For HTTP-Server, the proxy supports these request methods by default: HEAD, GET, and POST. The proxy also includes these options (disabled by default): OPTIONS, PUT, and DELETE.
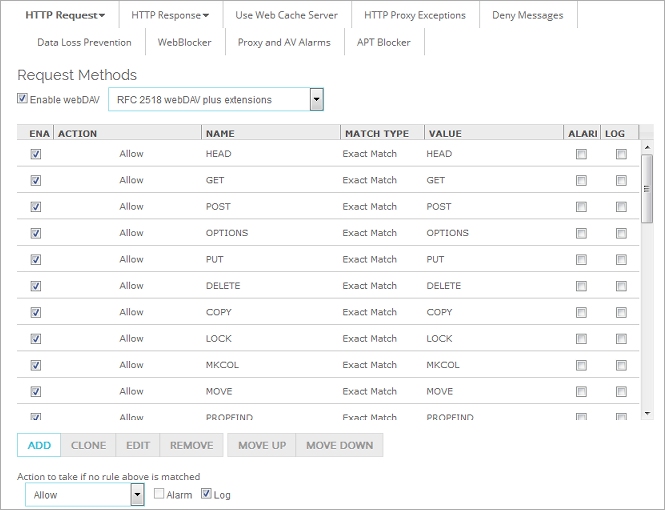
- In the HTTP Proxy Action configuration, select HTTP Request > Request Methods.
The Rules (simple view) list appears.
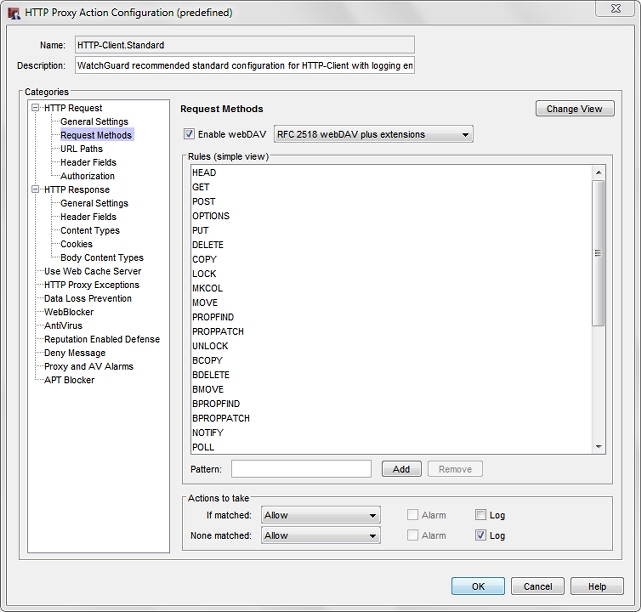
HTTP Proxy Action Request Methods configuration in Policy Manager
- To enable your users to use these extensions, select the Enable webDAV check box.
Many extensions to the base webDAV protocol are also available. If you enable webDAV, from the drop-down list, select whether you want to enable only the extensions described in RFC 2518 or if you want to include an additional set of extensions to maximize interoperability. - Configure the rule action.
For more information, go to Add, Change, or Delete Rules. - To change settings for another category in this proxy, see the topic for that category.
- Save the configuration.
If you modified a predefined proxy action, when you save the changes you are prompted to clone (copy) your settings to a new action.
For more information on predefined proxy actions, go to About Proxy Actions.