NAT Loopback and Static NAT (SNAT)
Applies To: Locally-managed Fireboxes
NAT loopback enables a user on the trusted or optional networks to connect to a public server with the public IP address or domain name of the server, if the server is on the same physical Firebox interface. To help you understand how to configure NAT loopback when you use static NAT (SNAT), we give this example:
Company ABC has an HTTP server on the Firebox trusted interface. The company uses static NAT to map the public IP address to the internal server. The company wants to allow users on the trusted network to use the public IP address or domain name to get access to this public server.
For this example, we assume:
- The trusted interface is configured with an IP address on the 10.0.1.0/24 network
- The HTTP server is physically connected to the trusted 10.0.1.0/24 network.
The Firebox always uses the IP address of the internal interface as the source IP address for loopback connections with Static NAT. This is true even if you select the Set Source IP Address option in the Static NAT action.
If you configure a NAT loopback policy, and the SNAT action includes more than one member, users on your internal network are always redirected to the first member of the SNAT action.
Add a Policy for NAT Loopback to the Server
In this example, to allow users on your trusted and optional networks to use the public IP address or domain name to connect to a public server that is on the trusted network, you must create an SNAT action and add it to an HTTP policy. The policy addresses could look like this:
From:
Any-Trusted
Any-Optional
To:
snat-NAT-Loopback (Static NAT)
203.0.113.5 --> 10.0.1.5
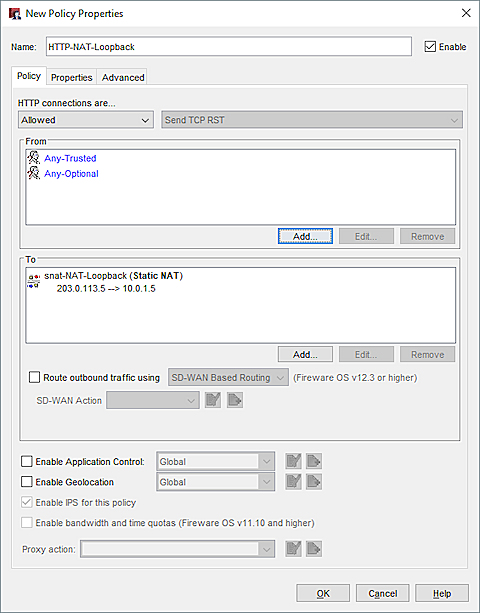
The SNAT action in the NAT loopback policy in Policy Manager
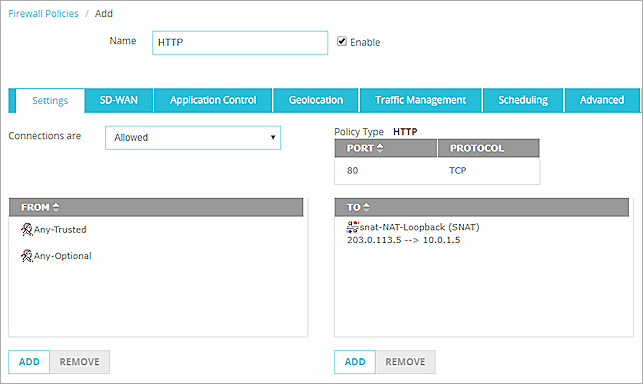
The To section of the policy contains an SNAT action that defines a static NAT route from the public IP address of the HTTP server to the real IP address of that server. In Fireware v12.2 or higher, you can specify an FQDN in the SNAT action.