Applies To: Locally-managed Fireboxes
This topic explains how to configure BGP on your Firebox.
Before You Begin
Before you configure BGP, make sure you understand the following BGP requirements and options.
To participate in BGP with an ISP you must have a public autonomous system (AS) number. For internal BGP between private networks you must use a private AS number. For more information, go to About Border Gateway Protocol (BGP). You can configure BGP to do dynamic routing for both IPv4 and IPv6 networks.
If you enable BGP for a FireCluster, you must set the router-id in the BGP configuration to the IP address of the Firebox interface that connects to the router. This is to make sure that the routing protocol does not try to use the FireCluster management IP address as the router-id. Do not use the FireCluster management IP address or cluster IP address as the router-id. To set the router-id, use the command bgp router-id <ip-address> in your BGP configuration, where ip-address is the IP address of the Firebox interface that connects to the router.
If your Firebox has multi-WAN enabled, you can configure a loopback interface, and use the IP address of the loopback interface instead of the IP address of the physical interfaces in the dynamic routing configuration. For more information, see Configure a Loopback Interface.
Free Range Routing (Fireware v12.9 or Higher)
In Fireware v12.9 or higher, Fireware uses the Free Range Routing (FRR) routing engine, which replaces Quagga. If your configuration includes Quagga commands for dynamic routing, those commands work after you upgrade. Some FRR commands appear in a different section than in Quagga.
In Fireware v12.9 or higher:
- The network and redistribute BGP commands are under the address-family section. If your Firebox includes an existing BGP configuration, and you upgrade from Fireware v12.8.x or lower to Fireware v12.9 or higher, the configuration conversion automatically converts your existing Quagga commands. If you add new network and redistribute commands after you upgrade to Fireware v12.9, make sure to add those under the address-family section. For a code sample, go to Sample BGP Routing Configuration File (FRR).
- You can use a simplified implementation of bidirectional forwarding (BFD). You must configure a BGP policy for BFD traffic and enable BFD in the OSPF or BGP configuration on your Firebox. For information about how to implement BFD, go to Bidirectional Forwarding.
- The Firebox cannot learn or announce routes unless you add inbound or outbound BGP filtering policies for the eBGP session. If you prefer not to add BGP policies, you can enter the no bgp ebgp-requires-policy command, which removes the policy requirement. When you upgrade to Fireware v12.9, if you have an existing BGP configuration, the Firebox adds the no bgp ebgp-requires-policy command automatically. If you add a new BGP configuration after you upgrade to Fireware v12.9, you must manually enter the no bgp ebgp-requires-policy command to remove the policy requirement. If you do not enter this command, and you also do not configure BGP filtering policies, the Firebox cannot learn routes from the BGP peer or announce routes to the BGP peer.
- The bgp network import-check is enabled by default for new BGP configurations configured in Fireware v12.9 or higher. When this setting is enabled, routes created by the network command must be validated before those routes can be advertised to neighbors. If you add a new BGP configuration in Fireware v12.9 or higher, we recommend that you manually disable this setting so BGP peers can learn Firebox routes. To disable this setting, use the command no bgp network import-check. If your Firebox includes an existing BGP configuration, and you upgrade from Fireware v12.8.x or lower to Fireware v12.9 or higher, the configuration conversion automatically disables bgp network import-check.
- You can use rpki commands for Resource Public Key Infrastructure (RPKI) configuration mode. RPKI is a component of Route Origin Authorization (ROA). ROA verifies whether the origin autonomous system number (AS) of an IP prefix can legitimately announce that IP prefix. BGP routers connect to RPKI cache servers to receive validated prefix-to-origin AS mappings. For more information, see RPKI Configuration Example in the FRR documentation.
For a routing configuration file sample, go to Sample BGP Routing Configuration File (FRR).
For a list of commands, go to BGP Commands (FRR).
Quagga (Fireware v12.8.x or Lower)
Quagga is the routing daemon in Fireware v12.8.x or lower.
For a sample routing configuration file, go to Sample BGP Routing Configuration File (Quagga).
For a list of commands, go to BGP Commands (Quagga).
Configure BGP
- Select Network > Dynamic Routing.
The Dynamic Routing page appears. - Select the Enable Dynamic Routing check box.
- Select the BGP tab.

- Select the Enable check box.
- Copy and paste your routing daemon configuration file in the text box. To get started, you need only three commands in your BGP configuration file. These three commands start the BGP process, set up a peer relationship with the ISP, and create a route for a network to the Internet. For more information, go to About Sample Routing Configuration Files.
In Fireware v12.9 or higher, use the commands in this order:
- router BGP: BGP autonomous system number supplied by your ISP
- neighbor: <IP address of neighboring BGP router> remote-as <BGP autonomous number>
- network: Network IP address that you want to advertise a route to from the Internet. In Fireware v12.9 or higher, the network and redistribute commands are under the address-family section.
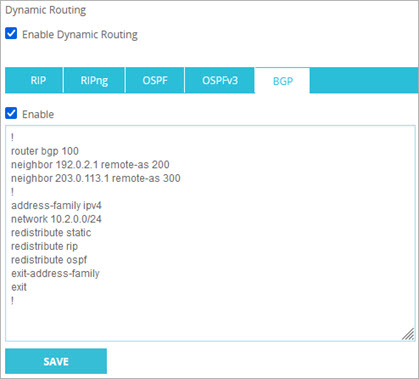
In Fireware v12.8.x or lower, use the commands in this order: router BGP, network, neighbor.
- Click Save.
If necessary, Fireware automatically adds the required dynamic routing policy or enables an existing BGP dynamic routing policy, if one exists.
- Select Network > Dynamic Routing.
The Dynamic Routing Setup dialog box appears. - Select the Enable Dynamic Routing check box.
- Select the BGP tab.
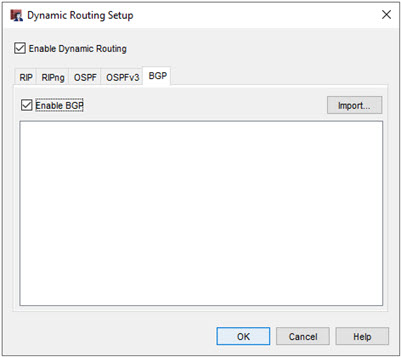
- Select the Enable BGP check box.
- Click Import to import a routing daemon configuration file.
Or, copy and paste your configuration file in the text box.
For more information, go to About Sample Routing Configuration Files.
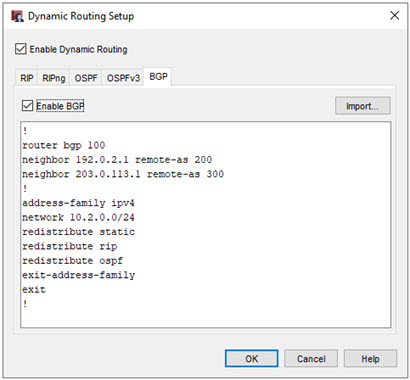
To get started, you need only three commands in your BGP configuration file. These three commands start the BGP process, set up a peer relationship with the ISP, and create a route for a network to the Internet. In Fireware v12.9 or higher, use the commands in this order:
- router BGP: BGP autonomous system number supplied by your ISP
- neighbor: <IP address of neighboring BGP router> remote-as <BGP autonomous number>
- network: Network IP address that you want to advertise a route to from the Internet. In Fireware v12.9 or higher, the network command is under the address-family section.
In Fireware v12.8.x or lower, use the commands in this order: router BGP, network, neighbor.
- Click OK.
If an enabled dynamic routing policy does not exist, Policy Manager asks if you want to add the required dynamic routing policy. - Click Yes to add the required dynamic routing policy.
Policy Manager adds the required dynamic routing policy, or enables an existing BGP dynamic routing policy, if one exists.
When you enable BGP, the Firebox automatically creates a dynamic routing policy called DR-BGP-Allow. By default, the DR-BGP-Allow policy allows traffic from the alias Any to the Firebox. As a best practice, we recommend that you edit this policy to add authentication and restrict the policy to listen on only the correct interfaces.
After you configure the Firebox and the BGP router, you can look at the routes table to verify that the Firebox has received route updates from the BGP router.
To see the dynamic routes, from Firebox System Manager select the Status Report tab.
To see the dynamic routes, from Fireware Web UI select System Status > Routes.