Applies To: Locally-managed Fireboxes
This procedure describes how to enable Active Directory Single Sign-On. For information about how to enable RADIUS Single Sign-On, see Enable RADIUS Single Sign-On.
Before you can enable Active Directory SSO, you must:
- Configure your Active Directory server
- Install the WatchGuard Single Sign-On (SSO) Agent and Event Log Monitor
- Install the WatchGuard Active Directory SSO Client (Optional)
- Install the WatchGuard Active Directory SSO Exchange Monitor (Optional)
Enable and Configure SSO
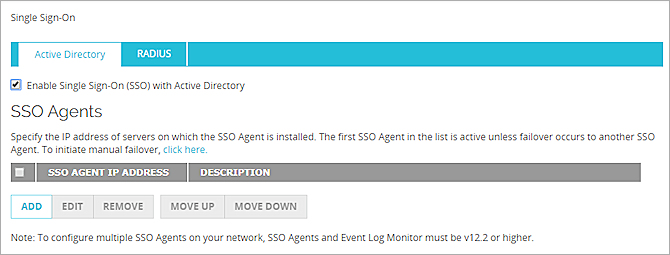
When you enable and configure the settings for SSO on your Firebox, you must specify the IP address of the SSO Agent.
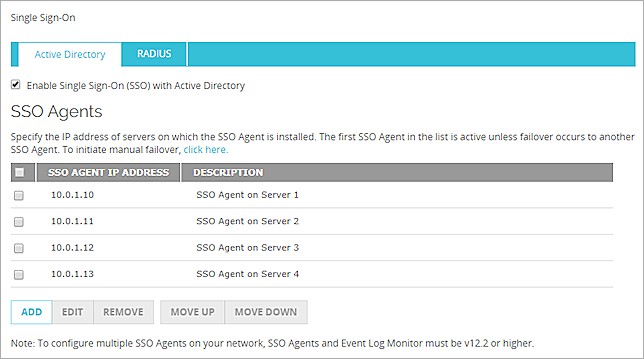
In Fireware v12.2 or higher, you can specify up to four SSO Agents. Only one SSO Agent is active at a time. If the active SSO Agent becomes unavailable, the Firebox automatically fails over to the next SSO Agent in your configuration. You can also manually fail over to an SSO Agent. For more information about SSO Agent failover, go to the Failover section in this topic.
You can also specify the IP addresses (or ranges) to exclude from SSO queries, and enable SSO through the branch office VPN tunnels on your Firebox.
When you enable SSO through your BOVPN tunnels, SSO connections through the tunnel to your domain workstations can increase the bandwidth consumption of the tunnel.
- Select Authentication > Single Sign-On.
The Single Sign-On page appears. - Select the Enable Single Sign-On (SSO) with Active Directory check box.
- Click Add.
The Add SSO Agent dialog box appears. - In the IP Address text box, type the IP address of the server on which the SSO Agent is installed.
- (Optional) In the Description text box, type a description of the SSO Agent.
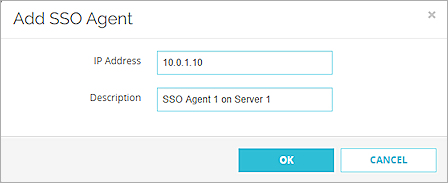
- Click OK.
- (Optional) To add additional SSO Agents, repeat Steps 3–6. A maximum of four SSO Agents can appear in the list.
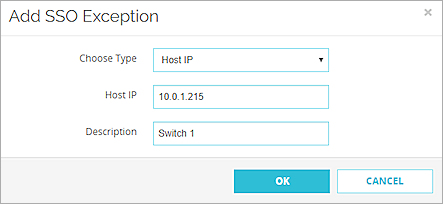
- (Optional) To add IP addresses or ranges to exclude from SSO queries, in the SSO Exceptions section, click Add. For more information about SSO exceptions, go to the Define SSO Exceptions section.
The Add SSO Exception dialog box appears. - From the Choose Type drop-down list, select Host IP, Network IP, or Host Range.
- Type the IP address, network address, or host range.
- In the Description text box, type a description of the host for which you want to create an exception from SSO.
- Click OK.
- In the Keep-Alive Interval text box, specify a value in seconds between 1 and 120.
- In the Keep-Alive Timeout text box, specify a value in seconds between 10 and 1200.
- (Optional) To enable users who connect to your network through a BOVPN tunnel to use SSO, select the Enable Single Sign-On (SSO) through BOVPN tunnels check box.
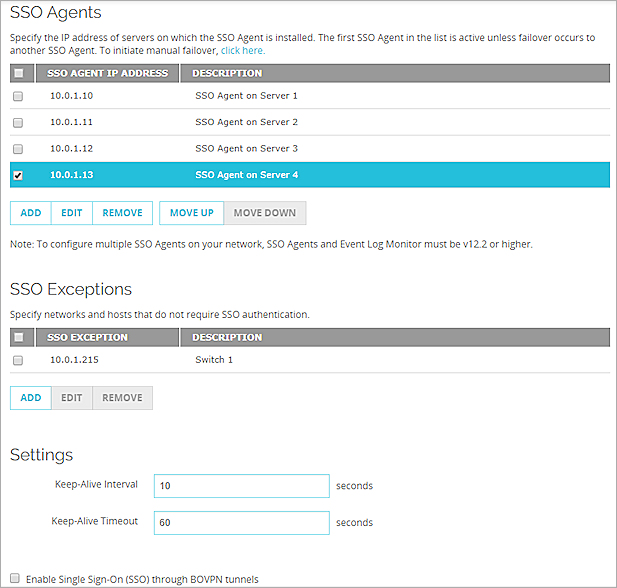
- Click Save.
- Select Setup > Authentication > Single Sign-On.
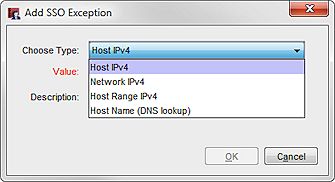
The Single Sign-On dialog box appears. - Select the Enable Single Sign-On (SSO) with Active Directory check box.
- Click Add.
The Add SSO Agent IP dialog box appears.
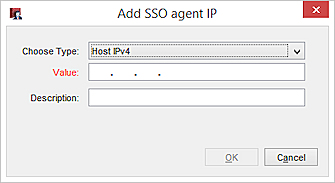
- From the Choose Type drop-down list, select Host IPv4.
- In the Value text box, type the IP address of the server on which the SSO Agent is installed.
- (Optional) In the Description text box, type a description of the SSO Agent.
- Click OK.
- (Optional) To add additional SSO Agents, repeat Steps 3–7. A maximum of four SSO Agents can appear in the list.
- (Optional) To add IP addresses or ranges to exclude from SSO queries, in the SSO Exceptions section, click Add. For more information about SSO exceptions, see the Define SSO Exceptions section.
The Add SSO Exception dialog box appears.- From the Choose Type drop-down list, select Host IPv4, Network IPv4, or Host Range, or Host Name (DNS Lookup).
- Type the IP address, network address, or host range, or host name.
- In the Description text box, type a description of the host for which you want to create an exception from SSO.
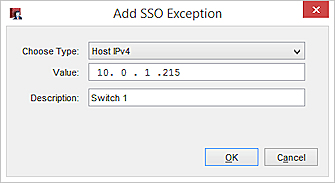
- Click OK.
- In the Keep-Alive Interval text box, specify a value in seconds between 1 and 120.
- In the Keep-Alive Timeout text box, specify a value in seconds between 10 and 1200.
- To enable users who connect to your network through a BOVPN tunnel to use SSO, select the Enable Single Sign-On (SSO) through BOVPN tunnels check box.
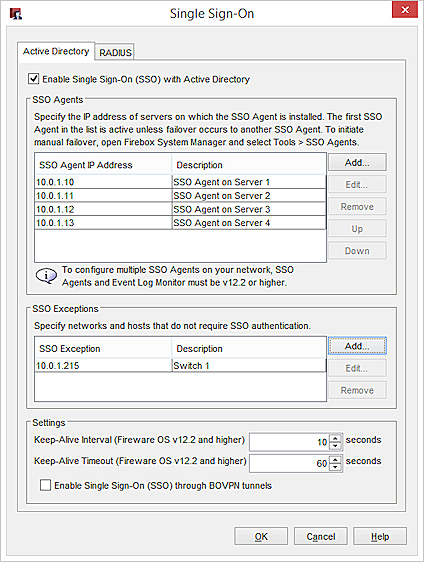
- Click Save.
Define SSO Exceptions
If your network includes devices with IP addresses that do not require authentication, such as network servers, switches and routers, print servers, or computers that are not part of the domain, if you have users on your internal network who must manually authenticate to the Authentication Portal, or if you have terminal servers for the Terminal Services Agent, we recommend that you add their IP addresses to the SSO Exceptions list.
Each time a connection attempt occurs from an IP address that is not in the SSO Exceptions list, the Firebox contacts the SSO Agent to try to associate the IP address with a user name. This takes about 10 seconds. You can use the SSO Exceptions list to prevent this delay for each connection, to reduce unnecessary network traffic, and enable users to authenticate and connect to your network without delay.
When you add an entry to the SSO Exceptions list, you can choose to add a host IP address, network IP address, subnet,
- Click Add.
The Add IP Addresses dialog box appears. - From the Choose Type drop-down list, select the type of entry to add to the SSO Exceptions list:
- Host IP
- Network IP
- Host Range
The text boxes that appear change based on the type you select.
- Type the IP address for the type you selected.
If you selected the type Host Range, in the From and To text boxes, type the start and end IP addresses for the range. - (Optional) In the Description text box, type a description to include with this exception in the SSO Exceptions list.
- Click OK.
The IP address or range appears in the SSO Exceptions list. - Click Save.
- Below the SSO Exceptions list, click Add.
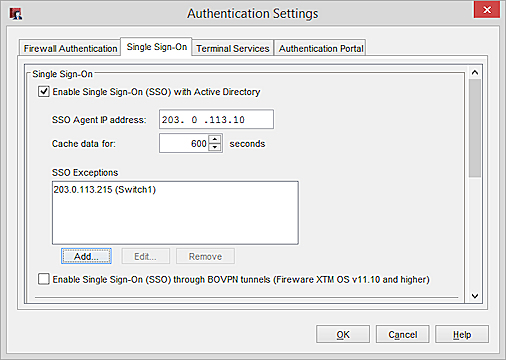
The Add SSO Exception dialog box appears.
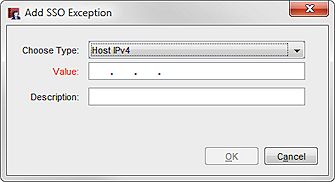
- From the Choose Type drop-down list, select the type of entry to add to the SSO Exceptions list:
- Host IPv4
- Network IPv4
- Host Range IPv4
- Host Name (DNS lookup)
- In the Value text box, type the IP address for the type you selected.
If you selected the type Host Range, in the Value text box, type the IP address at the start of the range.
In the To text box, type the IP address at the end of the range.
- (Optional) In the Description text box, type a description to include with this exception in the SSO Exceptions list.
The Comment text box does not appear for the Host Name type. - Click OK.
The IP address or range appears in the SSO Exceptions list.
You can also edit or remove entries from the SSO Exceptions list.
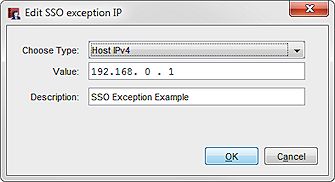
- From the SSO Exceptions list, select an entry.
- Click Edit.
The Edit SSO exception IP dialog box appears. - Change the settings for the SSO exception.
- Click OK.
The updated entry appears in the SSO Exceptions list.
- Click OK.
- From the SSO Exceptions list, select an entry.
- Click Remove.
The selected entry is removed from the SSO Exceptions list. - Click Save.
- From the SSO Exceptions list, select an entry.
- Click Remove.
The selected entry is removed from the SSO Exceptions list. - Click OK.
Failover
If you specify more than one SSO Agent, automatic failover occurs if the active SSO Agent becomes unavailable. Failover occurs sequentially. For example, if the first SSO Agent in the list becomes unavailable, failover occurs to the second SSO Agent in the list. If the last SSO Agent in the list is active and becomes unavailable, failover occurs to the first SSO Agent in the list.
Failback does not occur. For example, if the first SSO Agent in the list becomes unavailable, failover occurs to the second agent in the list. If the first SSO Agent becomes available again, the second SSO Agent remains the active agent. Failback does not occur back to the first SSO Agent.
You can also select to manually fail over to a different SSO Agent. The SSO Agent must be v12.2 or higher to support failover.
To manually fail over to a different SSO Agent, from Fireware Web UI:
- Select System Status > SSO Agents.
- Select an agent.
- Click Fail Over to SSO Agent.
To manually fail over to a different SSO Agent, from Firebox System Manager:
- Select Tools > SSO Agents.
- Select an agent.
- Click Fail Over to SSO Agent.
About Active Directory Single Sign-On (SSO)
How Active Directory SSO Works