Configure the WatchGuard Endpoint Security Plug-in for N-able N-sight
After you use the onboarding application to install the plug-in, you must configure the plug-in for integration with N-able N-sight. To configure the plug-in you must:
For more information on what N-able N-sight monitors after you complete your configuration, go to Items Monitored by the Service .
Import WatchGuard Scripts
When you download the WatchGuard Endpoint Security plug-in for N-able N-sight, the downloaded folder includes WatchGuard scripts. The plug-in uses these scripts to perform actions in N-able N-sight.
Script Table
This script table includes the name, file name, description, type, and operating system for each WatchGuard script available to use in N-sight. Use the data in this table when you use the Script Manager in N-sight to Import Scripts to N-sight.
| Script Name | File Name | Description | Type | Operating System |
|---|---|---|---|---|
| WatchGuard – Agent installation in Windows | WatchGuard Endpoint Security – Install agent in Windows.PS1 | Installs the WatchGuard Endpoint Agent on Windows devices. | Task | Windows |
| WatchGuard - Agent installation in macOS | WG-Install-Mac.SH | Installs the WatchGuard Endpoint Agent on Mac devices. | Task | macOS |
| WatchGuard - Agent installation in Linux | WG-Install-Linux.SH | Installs the WatchGuard Endpoint Agent on Linux devices. | Task | Linux |
| WatchGuard – Scan Windows device | WatchGuard Endpoint Security - Scan Windows device.PS1 | Scans Windows devices. | Task | Windows |
| WatchGuard – Scan Mac device | WG-Scan-Mac.SH | Scans Mac devices. | Task | macOS |
| WatchGuard – Monitor in Windows | WatchGuard Endpoint Security - Monitor Windows device.PS1 | Monitors security threats on Windows devices. | Task/Script Check | Windows |
| WatchGuard – Monitor in Mac | WG-Monitor-Mac.SH | Monitors security threats on Mac devices. | Task/Script Check | macOS |
| WatchGuard – Monitor in Linux | WG-Monitor-Linux.SH | Monitors security threats on Linux devices. | Task/Script Check | Linux |
Import Scripts to N-sight
To import WatchGuard scripts, from N-sight:
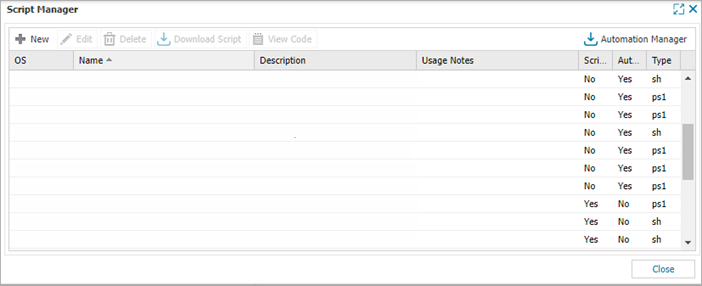
- Select Settings > Script Manager.
The Script Manager dialog box opens.
- Click New.
The Add User Defined Scripts dialog box opens.
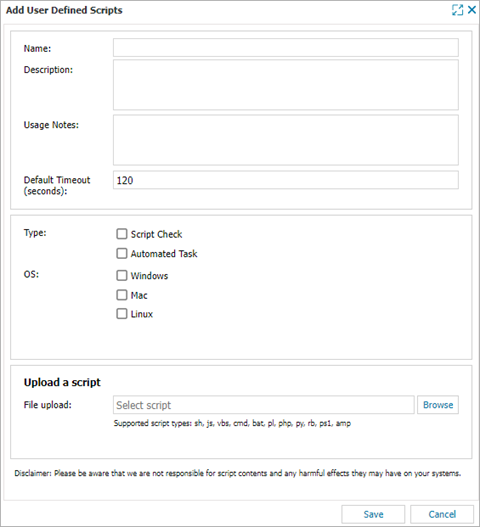
- In the Name text box, enter the script name for the script you want to add. For this example, type WatchGuard - Agent installation in Windows.
- In the Description text box, enter the description for the script you want to add. For this example, type This script installs WatchGuard Endpoint Agent on Windows devices.
- Select the Type. For this example, select Automated Task.
- Select the OS. For this example, select Windows.
- In the Upload a script section, click Browse and select the script from the NableInt folder. For this example, select WatchGuard Endpoint Security - Install agent in Windows.PS1.
- Click Save.
- Repeat this procedure for all Windows, macOS, and Linux scripts listed in the table.
Configure Monitoring
To monitor the security of endpoint devices in N-sight, such as threats detected and security status incidents, you must complete these steps:
Add a Monitoring Template
When you download the WatchGuard Endpoint Security plug-in for N-able N-sight, the downloaded folder includes the scripts to monitor Windows, macOS, and Linux devices.
| Script Name | Supported Devices |
|---|---|
| WatchGuard – Monitor in Windows | Windows workstations and servers |
| WatchGuard – Monitor in Mac | Mac workstations |
| WatchGuard – Monitor in Linux | Linux servers |
To add a monitoring template, from N-sight:
- Select Settings > Monitoring Templates > Manage Templates.

- Click Add and, from the drop-down list, select the type of workstation you want to use the template for. For this example, select Add Workstation Monitoring Template.
The Add Monitoring Template dialog box opens.
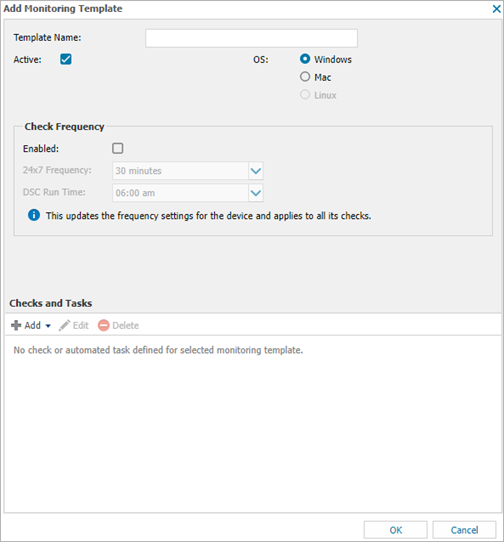
- In the Template Name text box, type the template name. For this example, enter WatchGuard Endpoint Security template.
- For the OS, select the operating system of the workstation you selected. For this example, select Windows.
- In the Check Frequency section, select the Enabled check box.
- Leave the default values for all other settings.
- In the Checks and Tasks section, select Add > Add 24x7 Check > Script Check.
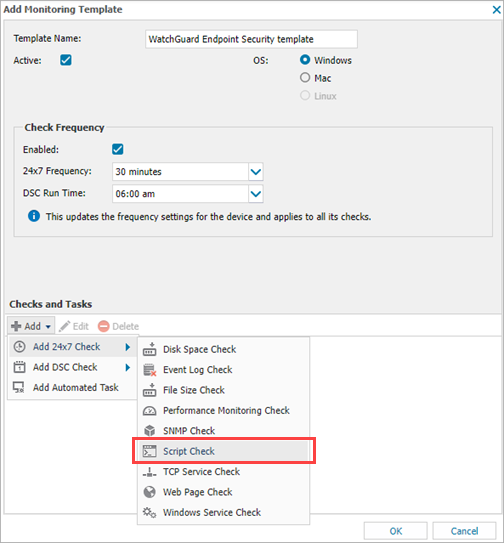
- In the Add Script Check dialog box, select the WatchGuard monitoring script that corresponds to the OS you selected in Step 2. For this example, select WatchGuard Endpoint Security - Monitor Windows device.
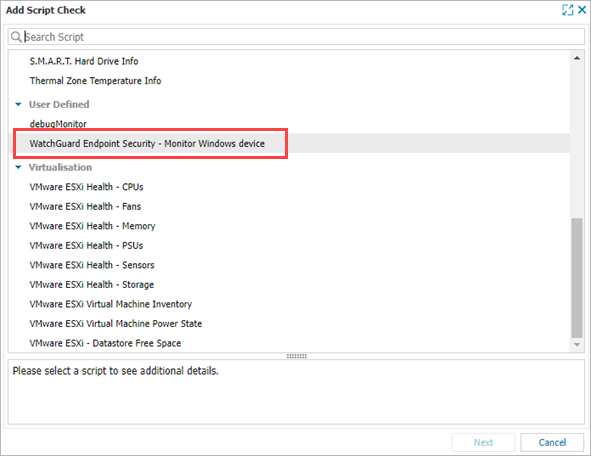
- Click Next.
The WatchGuard Endpoint Security - Monitor Windows Device dialog box opens.
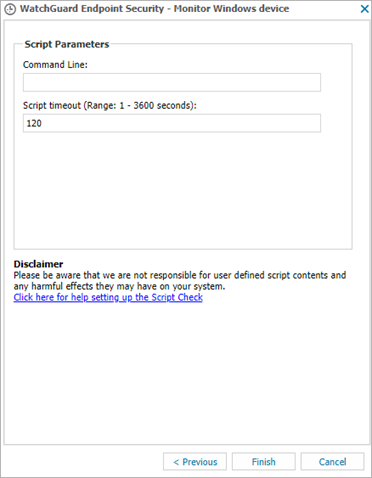
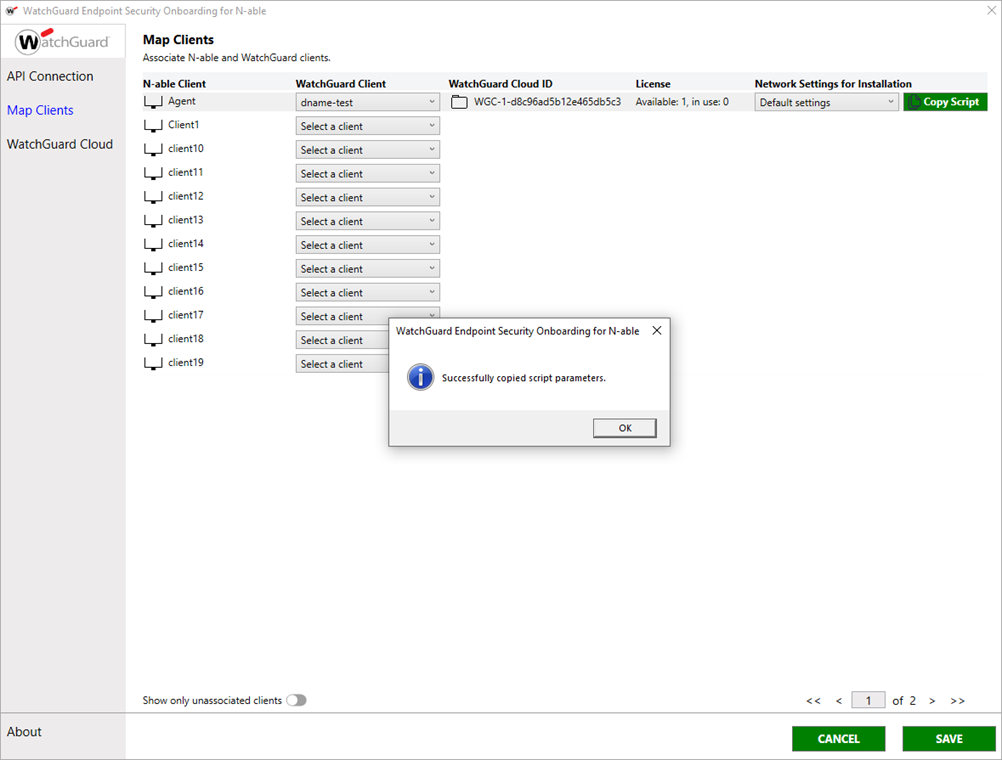
- In the WatchGuard Endpoint Security Onboarding for N-able application, select Map Clients.
- Select the client you want to create the template for from the list and click Copy Script.
- Click OK.
- Return to the WatchGuard Endpoint Security Monitor dialog box in N-sight.
- In the Command Line text box, paste the script parameters you copied from the onboarding application.
- Click Finish.
- Click OK.
- Repeat this procedure for all monitoring scripts.
Apply the Monitoring Template
After you create a monitoring template, you must apply it to a client.
To apply the monitoring service template, from N-sight:
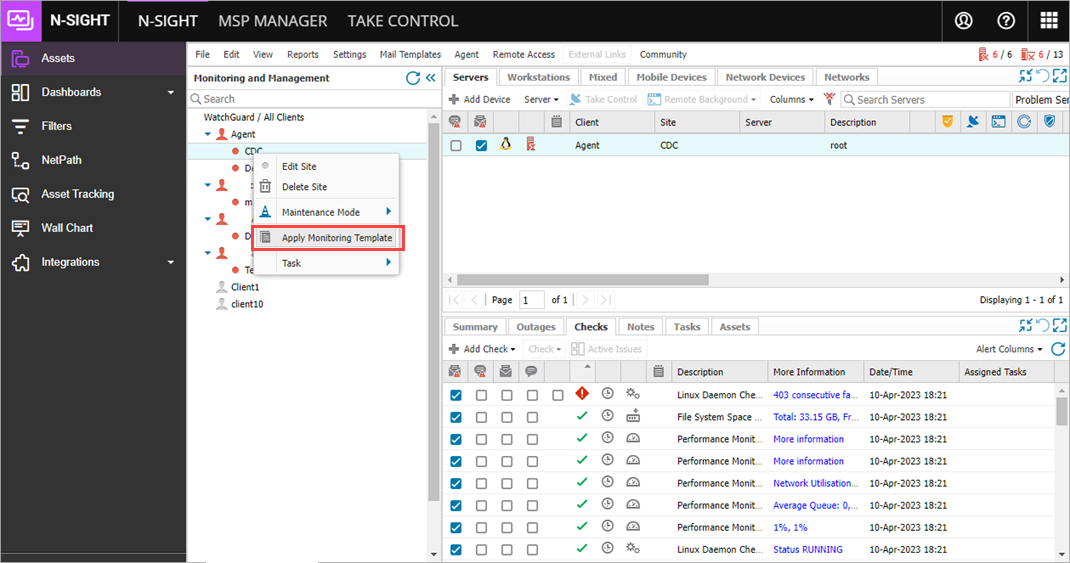
- In the Monitoring and Management section, right-click the client you want to apply the template to and select Apply Monitoring Template.
- In the Apply Monitoring Template dialog box, select the device type. For this example, select Workstations.
- From the Available Templates list, select the template you created, then click the right arrow button to move it to the Selected Templates list.
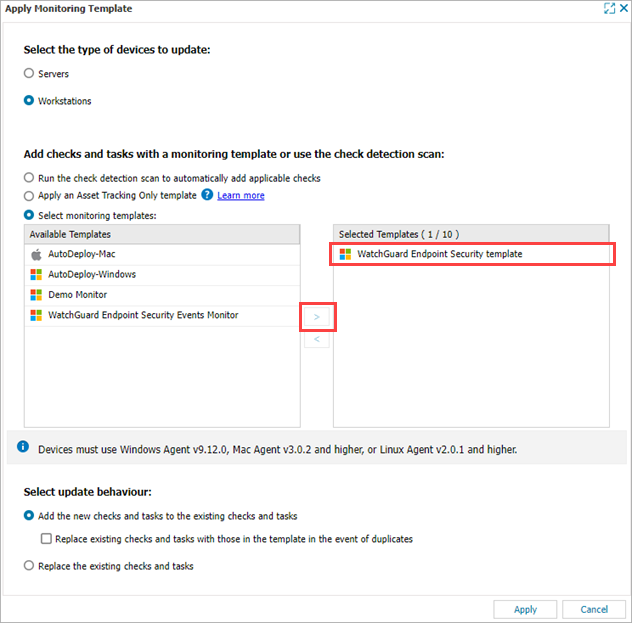
- Leave the default values for all other settings.
- Click Apply.
- Repeat this procedure for all monitoring templates.
Items Monitored by the Service
After you successfully configure N-able N-sight, you can use N-sight to monitor your devices for threats. This table shows items that the WatchGuard Endpoint Security service monitors and the messages for failed and normal results:
| Monitored Item | Failed Result | Normal Result |
|---|---|---|
|
Indicators of attack* |
One or more indicators of attack detected. | No indicators of attack detected. |
| PUP execution* | One or more PUP executions detected. | No PUP executions detected. |
| Malware execution* | One or more malware executions detected. | No malware executions detected. |
| Pending restart | There is a pending restart. | There is no pending restart. |
| WatchGuard Agent installation | WatchGuard Agent installation not successful. | WatchGuard Agent installation successful. |
| WatchGuard license validation | There is no valid WatchGuard license assigned. | A valid WatchGuard license is assigned. |
| Protection status | Protection status is not correct. | Protection status is correct. |
|
Threat detection** |
One or more threats detected. | No threats detected. |
* The WatchGuard Endpoint Security service monitors for indicators of attack, PUP executions, and malware executions in the previous seven days.
** Threat detection includes WatchGuard Endpoint Security monitoring for the previous seven days and includes:
- Malware detected
- Malware executed
- PUP detected
- PUP executed
- Programs blocked
- Exploit
- Virus
- Spyware
- Hacking tool
- Phishing
- Intrusion attempts blocked
- Malware URLs blocked
- Devices blocked
If WatchGuard Endpoint Security detects a threat, the Value column of the Status Details page in Service Monitoring shows details of the detections in JSON format that you can copy. For example:
{
"malwares": [
{
"eventDateTime": "2022-04-11T14:16:11.036",
"hostName": "WIN-LAPTOP-1",
"path": "C:\\Documents\\AAABC_d61266bfH.zip"
}
],
"puPs": [
{
"eventDateTime": "2022-04-11T11:01:12.52",
"hostName": "WIN-LAPTOP-1",
"itemName": "HackingTool/VulnerabilityScanner",
"path":"SYSTEMDRIVE|\\Users\\administrator\\Downloads\\vulnerabilityscanner.exe"
},
{
"eventDateTime": "2022-04-11T08:23:52",
"hostName": "WIN-LAPTOP-1",
"itemName": "Trj/WLT.C",
"path": "TEMP|\\62b2153392561255386e5f059c216110"
}
],
"ioAs":
[
{
"eventDateTime": "2022-04-07T00:33:05",
"hostName": "WIN-LAPTOP-1",
"ruleName": "Use of pipes to escalate privileges",
"ruleRisk": "Critical",
"action": "Undefined"
},
{
"eventDateTime": "2022-04-09T00:20:20.001",
"hostName": "WIN-LAPTOP-1",
"ruleName": "Credentials compromised after brute-force attack on RDP",
"ruleRisk": "Critical",
"action": "Attack Blocked"
},
{
"eventDateTime": "2022-04-09T00:20:20",
"hostName": "WIN-LAPTOP-1",
"ruleName": "In-memory execution of a remote script",
"ruleRisk": "Critical",
"action": "Undefined"
},
{
"eventDateTime": "2022-03-26T00:31:16.001",
"hostName": "WIN-LAPTOP-1",
"ruleName": "Credentials compromised after brute-force attack on RDP",
"ruleRisk": "Critical",
"action": "Attack Blocked"
},
{
"eventDateTime": "2022-04-11T00:33:38",
"hostName": "WIN-LAPTOP-1",
"ruleName": "Privilege escalation bypassing UAC",
"ruleRisk": "Critical", "action": "Undefined"
}
]
}
Install the WatchGuard Endpoint Security Plug-in for N-able N-sight