Define Advanced Phase 1 Settings
Applies To: Locally-managed Fireboxes
You can define the advanced Phase 1 settings for your Mobile VPN user profile.
- Select VPN > Mobile VPN.
- In the IPSec section, click Configure.
- Select an IPSec configuration and click Edit.
- Select the IPSec Tunnel tab.
- In the Phase 1 Settings section, click Advanced.
The Phase1 Advanced Settings appear.
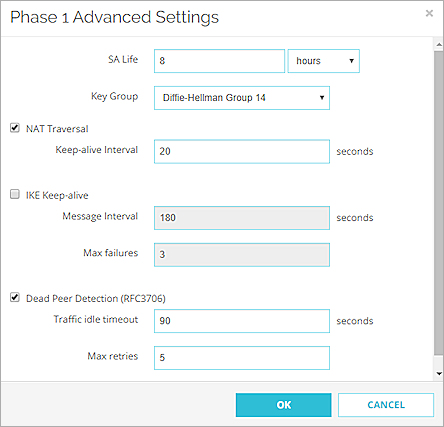
- Configure the settings for the group as described in the Phase 1 Options section.
We recommend you select the default settings if the IPSec VPN client on your device is compatible with these settings. If you configure the native IPSec VPN client on iOS, macOS, or Android, go to Use the macOS or iOS Native IPSec VPN Client and Use Mobile VPN with IPSec with an Android Device for recommended settings. - Click OK.
- Click Save.
- Select VPN > Mobile VPN > IPSec.
- Select an IPSec configuration and click Edit.
- Select the IPSec Tunnel tab.
- Click Advanced.
The Phase1 Advanced Settings dialog box appears.
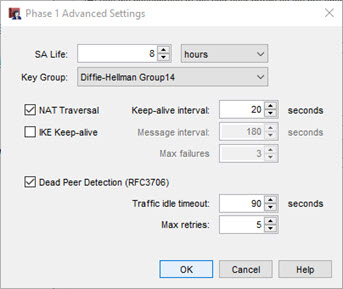
- Configure the settings for the group as described in the Phase 1 Options section.
We recommend you select the default settings if the IPSec VPN client on your device is compatible with these settings. If you configure the native IPSec VPN client on iOS, macOS, or Android, go to Use the macOS or iOS Native IPSec VPN Client and Use Mobile VPN with IPSec with an Android Device for recommended settings. - Click OK.
Phase 1 Options
SA Life
Select a SA (security association) lifetime duration and select Hour or Minute in the drop-down list. When the SA expires, a new Phase 1 negotiation starts. A shorter SA life is more secure but the SA negotiation can cause existing connections to fail.
Key Group
In Fireware v12.10 and higher, Fireware supports Diffie-Hellman Group 21.
Select a Diffie-Hellman group supported by the IPSec VPN client you use.
- The WatchGuard IPSec Mobile VPN client supports groups 1, 2, 5,14,15,19, 20 and 21.
- The native IPSec VPN client on macOS and iOS devices supports groups 2 and 14 for connections to a Firebox.
- The native Android IPSec VPN client uses group 2 by default.
Diffie-Hellman groups determine the strength of the master key used in the key exchange process. Higher group numbers are more secure, but require additional time to compute the key.
NAT Traversal
Select this check box to build a Mobile VPN tunnel between the Firebox and a VPN client that is behind a NAT device. NAT Traversal, or UDP Encapsulation, allows traffic to route to the correct destinations. NAT Traversal is enabled by default. Do not disable it unless you do not want to build tunnels between the Firebox and VPN clients behind a NAT device.
IKE Keep-alive
Select this check box only if this group connects to an older Firebox that does not support Dead Peer Detection. All Fireboxes with Fireware v9.x or lower, Edge v8.x or lower, and all versions of WFS do not support Dead Peer Detection. For these devices, select this check box to enable the Firebox to send messages to its IKE peer to keep the VPN tunnel open. Do not select both IKE Keep-alive and Dead Peer Detection.
Message interval
Select the number of seconds for the IKE keep-alive message interval.
Max failures
Set the maximum number of times the Firebox waits for a response to the IKE keep-alive messages before it terminates the VPN connection and starts a new Phase 1 negotiation.
Dead Peer Detection
Select this check box to enable Dead Peer Detection (DPD). Both endpoints must support DPD. All Fireboxes with Fireware v10.x or higher support DPD. Do not select both IKE Keep-alive and Dead Peer Detection.
DPD is based on RFC 3706 and uses IPSec traffic patterns to determine whether a connection is available before a packet is sent. When you select DPD, a message is sent to the peer when no traffic has been received from the peer within the selected time period. If DPD determines a peer is unavailable, additional connection attempts are not made.
Traffic idle timeout
Set the number of seconds the Firebox waits before it checks to see if the other device is active.
Max retries
Set the maximum number of times the Firebox tries to connect before it determines the peer is unavailable, terminates the VPN connection, and starts a new Phase 1 negotiation.