Applies To: AuthPoint Multi-Factor Authentication, AuthPoint Total Identity Security
Network location policy objects enable you to specify a list of IP addresses. You can then configure authentication policies that only apply when users authenticate from the IP addresses in the specified network location. You might do this if you want to allow users to log in without MFA when they are in the office.
When you add a network location to an authentication policy, the policy only applies to user authentications that come from that network location. Users who only have a policy that includes a network location cannot get access to the resource when they authenticate outside of that network location (because they do not have a policy that applies, not because authentication is denied).
When you configure a policy that includes a network location, we recommend that you create a second policy without the network location for the same groups and resources. The second policy applies to the users when they are not in the network location. Make sure the policy with the network location has a higher priority than the policy without the network location. For more information, see About Policy Precedence.
Network locations require that the end-user has an Internet connection.
For RADIUS authentication and basic authentication (ECP), policies that include a network location do not apply because AuthPoint cannot determine the IP address of the end user or the origin IP address.
Network Locations for RDP
For Remote Desktop Protocol (RDP) connections, AuthPoint uses the IP address that connects to port 3389 or port 443 to determine if the authentication originates from a network location.
If you configure RDP to use a port other than 3389 or 443, AuthPoint cannot identify the IP address of the end-user. In this scenario, policies with a network location do not apply to the authentication.
If you have a firewall, the network location receives the trusted IP address of the firewall, not the IP address of the end-user.
To allow users on your network to use RDP to connect to a server on the network without MFA, you can create a network location that includes the private IP addresses of the internal users, but not the internal IP address of the firewall. Add this network location to a policy that only requires password authentication. With this configuration:
- Internal users can connect to the server without MFA.
- External connections that come through the firewall require MFA.
Create Network Locations to Bypass MFA
To configure a "safe" location that does not require MFA when users authenticate, you must configure a network location and add it to an authentication policy that only requires password authentication. This allows users to log in with only their passwords (no MFA) when they authenticate from the specified network location to the resources in the authentication policy.
This section provides examples to help you configure network locations for different use cases for local or external networks. In these examples, we use these definitions:
- Local Network — Computers inside the company network are considered local.
- External Networks — Computers outside the company network are considered external.
- VPN Connections — Computers that are connected to a company VPN are considered part of the local network.
- Public IP Address — Public IP address used to connect to the Internet.
- Local IP Address — IP address used inside the local network.
- User IP Address — IP address of the user's computer, on an external network.
- Terminal Connections — Connection where a user logs in to the computer directly.
- Remote Connections— Connection where a user logs in to a computer with an RDP connection.
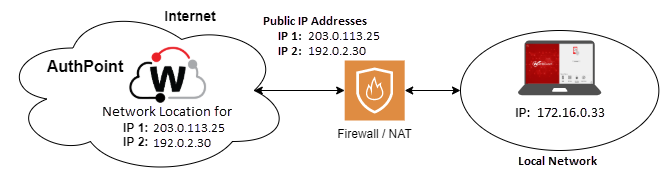
In this example, we want to create a network location to allow users on the local network to log in with only their passwords to computers with the agent for Windows or macOS (Logon app) installed. For this example, the user logs in to the computer directly (no RDP connection).
The network location must include the public IP address of the Firewall or NAT device. In the example shown, you would create a network location with the public IP addresses 203.0.113.25 and 192.0.2.30.
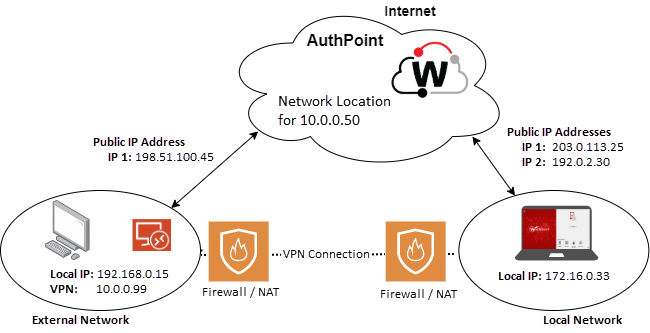
In this example, when a user is connected to a VPN, we want their computer to be considered a local computer on the internal network. While connected to the VPN, the user can authenticate and log in with only their password to the resources associated with the authentication policy.
For VPN requests, AuthPoint uses the internal package IP address to validate the network location in the authentication policy. In the example shown, you would create a network location with the IP address 10.0.0.50.
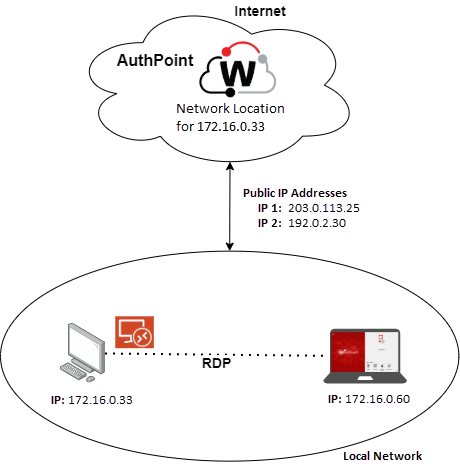
This example applies to organizations that only use virtual machines that are deployed on local servers. In this example, we want to allow users that are on a local network to connect to virtual machines that have the agent for Windows (Logon app) installed and log in with only their passwords.
Because AuthPoint uses the internal IP address to validate the network location for RDP requests, we must configure the network location to use the local network IP address or IP range. In the example shown, you would create a network location with the IP address of the computer: 172.16.0.33.
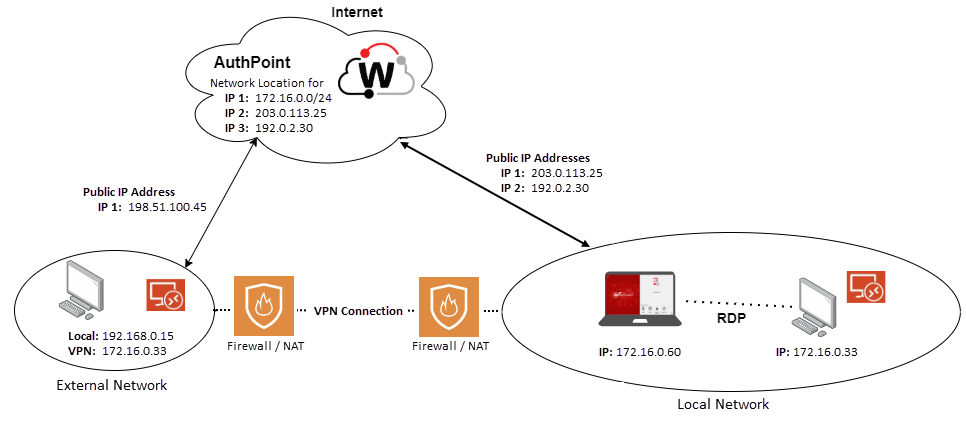
In this example, we want to allow all local users (terminal and remote) to log in with only their passwords. To do this, we configure a network location with the public IP addresses of our organization and the IP range of the local network.
In the network location:
- The public IP addresses 203.0.113.25 and 192.0.2.30 apply to authentications from terminal connections.
- The IP range 172.16.0.0/24 applies to authentications from local computers and external computers that are connected to the VPN.
For RD Gateway, there are two ways that users can connect to the internal computers:
- An RDP RemoteApp configured in an RD Session or a Virtualization Host collection in Remote Desktop Service (RDS)
- Device redirection to connect with RDP
How users use RD Gateway determines whether you must add the public IP addresses of the network or the private IP address of the RD Gateway server when you configure a network location.
For RemoteApps, the RD Gateway server initiates the RDP connection, and this is handled as an RDP connection from the local network (as in example 3). You must add the private IP address of the RD Gateway to your network location.
Device redirection creates an HTTPS tunnel to the RD Gateway and the RDP connection goes through the tunnel. This causes the Logon app to match against the range of public IP addresses assigned to devices on the network, like a local (terminal) logon. For this use case, you must add the public IP address of the network to your network location.
Configure a Network Location
To configure a network location policy object, in the AuthPoint management UI:
- From the AuthPoint navigation menu, select Policy Objects.
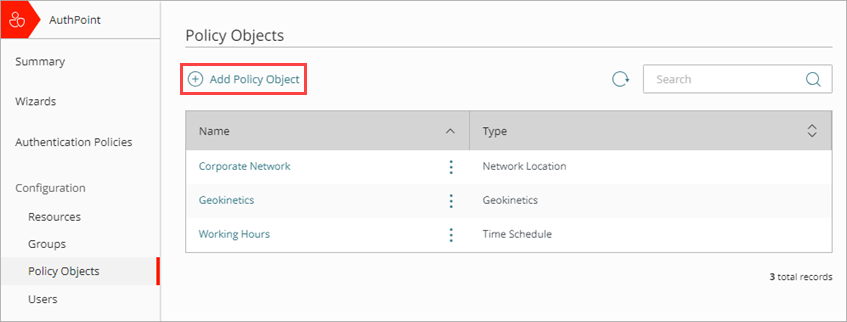
- Click Add Policy Object.
The Add Policy Object page appears.
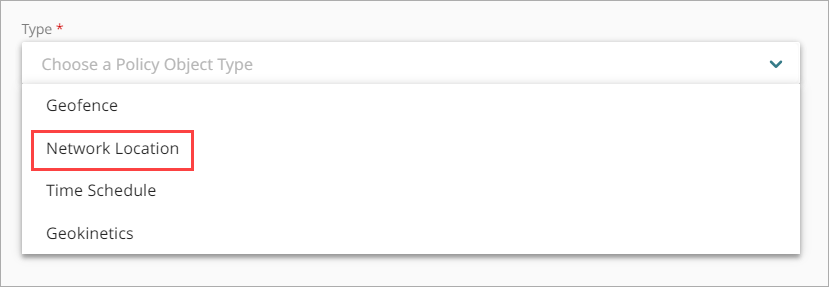
- From the Type drop-down list, select Network Location.
Additional fields appear. - In the Name text box, type a name to identify this network location policy object. This helps you identify the network location when you add it to authentication policies.
- In the IP Mask text box, type a public IP address or netmask that defines the range of public IP addresses for this network location and press Enter or Return. You can specify multiple IP addresses and ranges for one network location.
AuthPoint only supports IPv4 addresses for network locations.
You cannot add the IP addresses 0.0.0.0 or 255.255.255.255 to a network location.
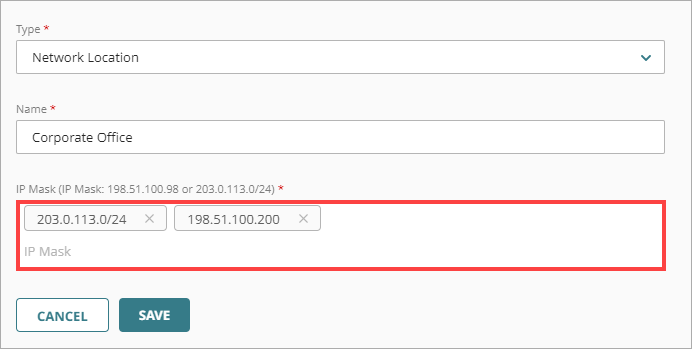
- Click Save.
- Add this network location to the authentication policies that you want it to apply to. For more information, see Add Authentication Policies
We recommend that you create a second policy for the same groups and resources without the network location to apply to users when they are not in the network location. Make sure the policy with the network location has a higher priority than the policy without the network location. For more information, see About Policy Precedence.