Access Point Auto-Classification
Applies To: Wi-Fi Cloud-managed Access Points (AP125, AP225W, AP325, AP327X, AP420)
It is important to know the authenticity of APs on your network because unauthorized or misconfigured APs can introduce severe security vulnerabilities.
APs are classified in these categories:
- Authorized — APs connected to your network that match your Authorized WiFi Policy.
- Misconfigured — Authorized APs with a configuration that does not match your Authorized WiFi Policy.
- Rogue — Unauthorized APs connected to your wired network that do not match your Authorized WiFi Policy.
- External — Neighborhood APs operating in the vicinity of your network, but not connected to your network.
- Uncategorized — New APs discovered by Wi-Fi Cloud that have not yet been classified. APs are then assigned a potential classification based on their network connectivity to the monitored network and their compliance with the Authorized WiFi Policy.
- All WatchGuard APs connected to your network that match your Authorized WiFi Policy are auto-classified as Authorized.
- All APs not managed by Wi-Fi Cloud (such as third-party APs) that are connected to your network and match your Authorized WiFi Policy are auto-classified as Potentially Authorized. You must manually classify these APs as Authorized.
- All APs not managed by Wi-Fi Cloud (such as third-party APs) that are connected to your network and do not match your Authorized WiFi Policy are auto-classified as Potentially Rogue.
- All APs not managed by Wi-Fi Cloud (such as third-party APs) that are not connected to your network are auto-classified as Potentially External.
Configure AP Auto-Classification
To configure AP auto-classification, in Discover, select Configure > WIPS > Access Point Auto-classification.
AP auto-classification is enabled by default. You can fine-tune the auto-classification behavior if you do not want External or Rogue APs to be automatically classified.
We recommend you use the default settings to automatically classify External and Rogue APs.
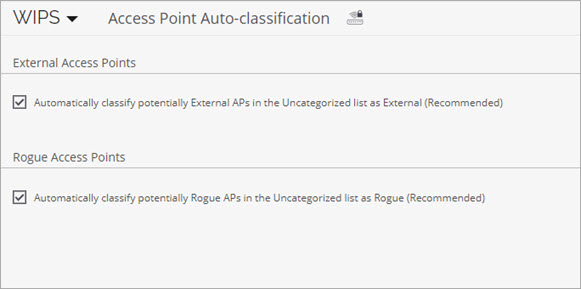
External Access Points
- Automatically classify potentially External APs in the Uncategorized list as External — The External AP might change classification if Wi-Fi Cloud detects that the AP is connected to the wired enterprise network at a later time.
Rogue Access Points
- Automatically classify potentially Rogue APs in the Uncategorized list as Rogue — When an AP is automatically classified as Rogue, the AP stays in that classification until an administrator manually reclassifies the AP. A Rogue AP will never be automatically changed to a different classification without administrator intervention.
Authorized AP List Locking
When you lock an AP device list, no more devices of that type can be subsequently authorized for the selected location.
This feature is intended for high-security environments where a specific list of Authorized APs can access the network. Any APs, even if they conform to your authorized WLAN policy as an Authorized AP, will not be allowed access until you add them manually to your network.
Because APs are not automatically moved to the Authorized folder, when you lock the list of Authorized APs, no wired APs will be tagged as Potentially Authorized at this location. These APs will become Potentially Rogue and might be automatically moved to the Rogue folder based on your AP Auto-Classification policy.
WARNING: Do not enable this feature until you are confident that you have identified and categorized all Authorized devices and want to make sure that any new device must be manually authorized before it can access your wireless network.
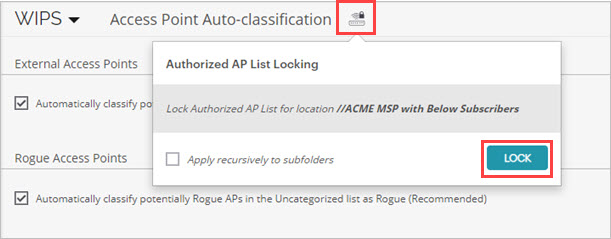
To lock the Authorized AP List:
- Select Configure > WIPS > Access Point Auto-classification.
- Click
 .
. - (Optional) To apply this action to all subfolders of your current location folder, select the Apply recursively to subfolders check box.
- Click Lock.