Applies To: Cloud-managed Fireboxes
This document applies to Fireboxes you manage in WatchGuard Cloud. For information that applies to Fireboxes managed in Fireware Web UI or WatchGuard System Manager, go to: Run the VPN Diagnostic Report.
Overview
Run the VPN Diagnostic Report to view configuration and status information for a VPN gateway and the associated branch office VPN tunnels. When you run the report, the Firebox temporarily increases the log level for the selected gateway. The completed report shows the gateway and tunnel configuration, as well as information about the status of any active tunnels for the selected gateway.
The report contains information that can help you troubleshoot VPN connectivity and routing issues. To identify VPN issues, you can run this report while you send traffic through the tunnel. For some types of issues, the report includes information about how to resolve the issue.
Run a VPN Diagnostic Report
You can run the VPN diagnostic report from Fireware Web UI or from WatchGuard Cloud. For information about how to run this report from WatchGuard Cloud, go to Run a BOVPN Diagnostic Report for a Firebox or FireCluster.
To run a VPN Diagnostic Report from Fireware Web UI, you must connect to the Firebox and log in to Fireware Web UI.
To log in to the local Fireware Web UI for a cloud-managed Firebox:
- From a computer on a network connected to the cloud-managed Firebox, open a web browser.
- In the web browser, go to https://<firebox IP address>:8080.
The Fireware Web UI login page opens. - Log in with the user name admin and the admin user account password you set for this device in WatchGuard Cloud.
To run the VPN Diagnostic Report
- In Fireware Web UI, select Diagnostics.
- Select the VPN tab.
The VPN diagnostic report options appear.
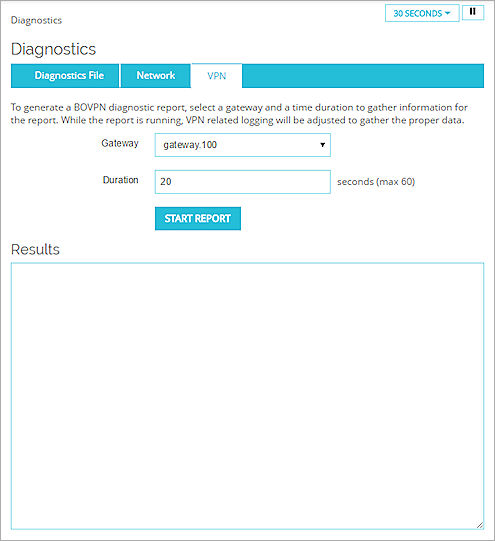
- From the Gateway drop-down list, select a VPN.
- In the Duration text box, type the number of seconds to run the VPN Diagnostic Report.
- Click Start Report.
The diagnostic task starts.
The Firebox collects log messages for the duration you specified. When the task completes, details of the gateway and tunnel configuration and information about the status of any active tunnels for the selected gateway appear in the Results section. The log level then returns to the previously set level.
VPN Diagnostic Report Details
The BOVPN Diagnostic Report includes these sections:
Conclusion
This is the complete report summary and can include information about actions you can take to resolve any issues identified by the report. For each tunnel route, the report shows whether the tunnel route was established, whether traffic was detected after the report started, and error messages related to the tunnel. Some error messages include information about what you can do to correct a problem with the BOVPN tunnel.
Gateway Summary
This is a summary of the gateway configuration and each configured gateway endpoint.
Tunnel Summary
This is a summary of the tunnel configuration for all tunnels that use the selected gateway. This includes both active and inactive tunnels.
Run-time Info (bvpn routes)
This section appears only when you run the diagnostic report for a branch office VPN virtual interface. It includes the static and dynamic routes that use the BOVPN virtual interface and the distance for each route. In Fireware v12.9 or higher, the Distance setting replaces the Metric setting.
Run-time Info (gateway IKE_SA)
The status of the IKE (Phase 1) security association for the gateway.
Run-time Info (tunnel IPSEC_SA)
The status of the IPSec tunnel (Phase 2) security association for active tunnels that use the gateway.
Run-time Info (tunnel IPSec_SP)
The status of the IPSec tunnel (Phase 2) security policy for active tunnels that use the gateway.
Address Pairs in Firewalld
The status of the address pairs for each tunnel. This section does not appear when you run the report for a branch office VPN virtual interface or for a BOVPN on a cloud-managed Firebox.
Policy checker result
The policies that manage inbound and outbound traffic for each tunnel route.
Related Logs
If tunnel negotiation occurs while the Diagnostic Report runs, the tunnel negotiation log messages appear in this section. If the remote device attempts to negotiate or rekey the tunnel while the report runs, the log messages that appear in this section include more informative details.