Applies To: Locally-managed Fireboxes
By default, the Firebox inspects traffic that goes in and out of the same external interface and applies firewall policies to that traffic. The Firebox does not inspect traffic that goes in and out of internal interfaces by default.
You can enable or disable intra-interface inspection on physical and link aggregation interfaces. If you enable this setting, the Firebox applies firewall policies to intra-interface traffic for the specified interface. In Fireware v12.9 or higher, you can enable or disable the setting from Fireware Web UI or Policy Manager. In Fireware v12.8, you must use the CLI to enable or disable the setting, as described in the Fireware CLI section of this topic.
- Select Network > Interfaces.
- Select the interface you want to configure. Click Edit.
- Select the Advanced tab.
- Select the Apply firewall policies to intra-interface traffic on the current interface check box.
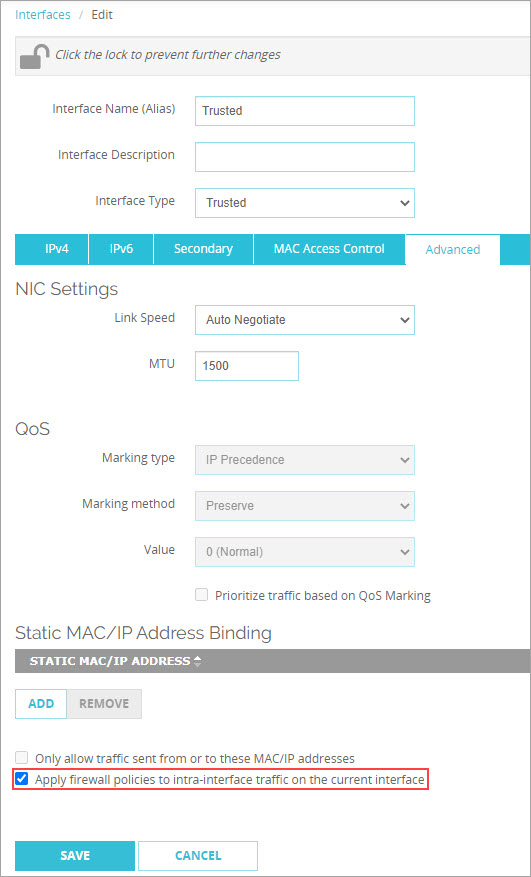
- Click Save.
- Select Network > Configuration.
The Network Configuration dialog box opens. - Select the interface you want to configure. Click Configure.
The Interface Settings dialog box opens. - Select the Advanced tab.
- Select the Apply firewall policies to intra-interface traffic on the current interface check box.
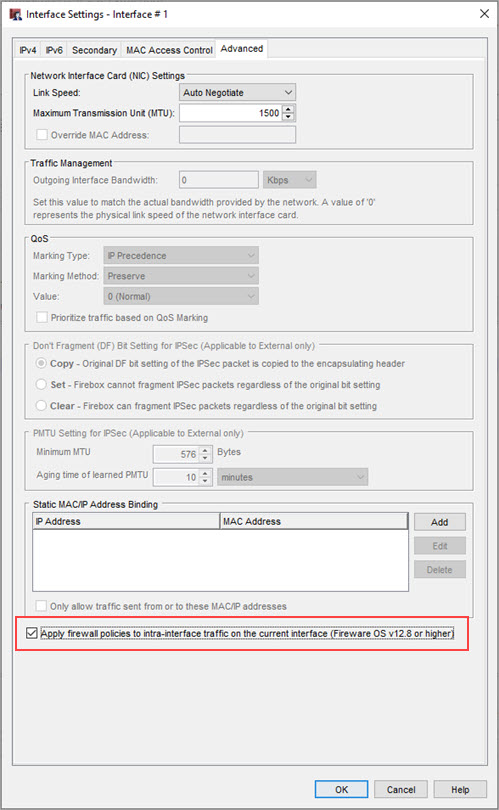
- Click OK.
In Fireware v12.8 or higher, from the Fireware CLI, you can specify the intra-if-inspection command to enable or disable intra-interface inspection on physical and link aggregation interfaces.
- In the Configuration Command Mode, enter the Interface Command Mode and specify an interface.
- To disable intra-interface traffic inspection for the interface, run this command:
no intra-if-inspection enable - To enable intra-interface traffic inspection for the interface, run this command:
intra-if-inspection enable - To verify the intra-interface traffic inspection status, run this command:
show interface
Examples
WG(config/if-fe01)#intra-if-inspection enable
WG(config/if-fe01)#no intra-if-inspection enable
WG(config/if-fe01)#show interface 0