You can configure your Firebox to forward DNS queries from computers on your network to a DNS server. For example, you can use DNS forwarding to send DNS queries from a branch office to a remote DNS server at headquarters.
You can enable DNS forwarding from Fireware Web UI, Policy Manager, and the CLI. You can also add conditional DNS forwarding rules. These rules allow you to send DNS queries to different DNS servers based on the domain name in the query.
Conditional DNS forwarding can result in faster response times to DNS queries. If you have resources in the cloud, your users can connect to those resources faster, because:
- Some cloud service providers use geolocation to select which datacenter you connect to. When you connect to a DNS server close to your location, your cloud provider can connect you to their closest datacenter.
- The Firebox caches the results from DNS queries.
This topic explains:
In Fireware v11.12.1 or lower, you can only enable DNS forwarding from the command line, and conditional DNS forwarding is not supported. If you enabled DNS forwarding before you upgrade to Fireware v11.12.2, DNS forwarding remains enabled, but the functionality changes, as described in this topic. For instructions to enable DNS forwarding in Fireware v11.12.1 or lower, go to How to enable DNS forwarding in the WatchGuard Knowledge Base.
DNS Servers on Your Firebox
These DNS servers might be configured on your Firebox:
- Network DNS server — Default DNS server for all interfaces and local processes on the Firebox
- Interface DNS server — DNS server for the interfaces that you specify
- Conditional DNS server — DNS server for the domain names and interfaces that you specify in a DNS forwarding rule
- DNS server obtained from your ISP — When your Firebox is configured as a DHCP client or PPPoE client
- DNSWatch server — DNS server when DNSWatch is enabled, in some cases
Each DNS server has a different purpose and is configured in a different location in the Firebox settings.
Some DNS servers take precedence over others. When you enable a DNS Forwarding rule, be aware that:
- Conditional DNS servers take precedence over the Network DNS server and DNSWatch servers.
- The Interface DNS server takes precedence over the Conditional DNS server.
For more information about DNS server precedence, go to About DNS on the Firebox.
DNS Forwarding
You can enable DNS forwarding, and conditional DNS forwarding, in these network modes:
- Mixed routing mode
- Drop-in mode
- Bridge mode
When you enable DNS forwarding:
- Select one or more Trusted, Optional, or Custom interfaces to participate in DNS forwarding.
- The local processes on the Firebox use the Firebox as the DNS server.
- The Firebox caches the results of DNS queries (up to 10,000 entries).
- If you do not add conditional DNS forwarding rules, DNS queries sent to the local IP address of the Firebox are forwarded to the network DNS server that you specified. The Firebox caches the results of these queries.
- If you configure the Firebox to be a DHCP server, the DHCP clients on your network automatically use the IP address of the interface as the DNS server, unless you specify a DNS server in the DHCP server settings.
- DNS traffic sent from interfaces configured for DNS forwarding to the Firebox is allowed. The DNS policy and DNS proxy policy only apply to pass-through DNS traffic.
- If you configure a Firebox interface to be a DHCP server, and the interface is configured for DNS forwarding:
- If you do not specify a DNS server in the DHCP settings, the DHCP server automatically gives the IP address of the Firebox interface as the DNS server. DNS forwarding occurs.
- If you specify a DNS server other than the IP address of the Firebox interface in the DHCP settings, the DHCP server automatically gives the IP address of the DNS server you specified. DNS forwarding does not occur.
The Firebox can process up to 10,000 DNS requests at the same time.
If you enable logging for DNS forwarding, the Firebox generates a log message when DNS forwarding occurs.
If you have a BOVPN virtual interface connection between sites, and you configure DNS forwarding, you must add a virtual interface IP address in the BOVPN virtual interface settings so that DNS forwarding works across the VPN. The virtual interface IP address is required because the DNS server must route traffic back to that IP address. For more information about virtual interface IP addresses, go to Configure BOVPN Virtual Interface IP Addresses.
In Fireware v12.4 or higher, you can enable DNSWatch in Bridge Mode. For the Firebox to resolve host names on local domains, you must create DNS forwarding rules for local domains that specify the local DNS servers.
DNS Forwarding Policy
In Fireware v12.9 or higher, when you enable DNS Forwarding, a policy named Allow DNS-Forwarding appears in the policy list. You can apply this policy to DNS traffic when DNS forwarding is enabled. For example, you might want to exclude IoT devices from DNS forwarding.
The policy allows DNS traffic (TCP and UDP traffic on port 53) to the Firebox from interfaces that you specify in the DNS Forwarding configuration.
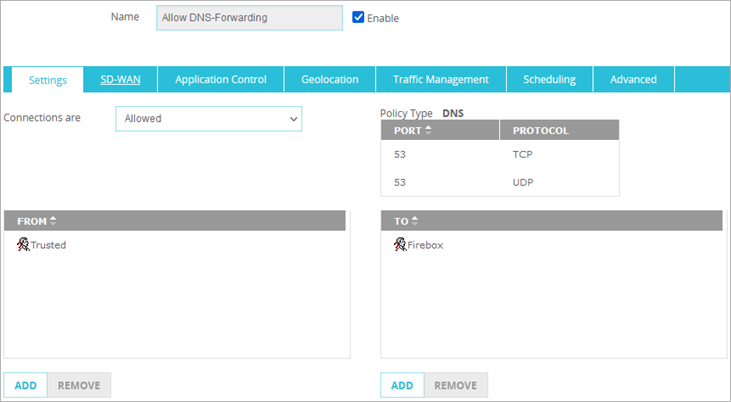
If you edit the policy to add interfaces to the From list, those interfaces do not appear in the DNS Forwarding configuration.
Log messages for this policy are generated by the Allow DNS-Forwarding policy.
If you disable DNS Forwarding, or enable DNS Forwarding and do not select any interfaces, the policy does not appear in the policy list.
Conditional DNS Forwarding
You can add conditional DNS forwarding rules. When you add a forwarding rule, the Firebox uses cached information to respond to a DNS query, or it forwards the query to a DNS server specified in the rule.
For example, on a branch office Firebox that has a VPN connection to headquarters, you can configure DNS settings to:
- Forward DNS queries for the internal domain example.com through the VPN to the DNS server at headquarters.
- Forward all other DNS queries to a public DNS server that is physically closer to the branch office.
Configuration
When you enable conditional DNS forwarding on your Firebox, you can add DNS forwarding rules. For each DNS forwarding rule, you specify these settings:
Domain Name
Add one or more domain names. There is no limit to the number of domain names that you can specify. More specific domain names take precedence. The order of domain names does not matter.
DNS Server
Specify a DNS server. Queries for the domain name you added are sent to the DNS server you specify. You can add up to four DNS servers for each domain name. The Firebox contacts the first DNS server in the list, and contacts the other DNS servers as needed.
Disable the DNS Cache
If you enable the DNS Forwarding or DNSWatch features, a DNS resolver (127.0.0.1) is automatically activated on the Firebox. In Fireware v12.6.4 or higher, you can disable the DNS cache. For information about how to disable the cache, go to About DNS on the Firebox.
Example
In this example, a branch office has a Firebox configured as a DHCP server. An interface DNS server is not specified in the DHCP server settings. The internal DNS server is on the network at the headquarters office. On the Firebox at the branch office, a conditional DNS forwarding rule sends queries for example.com to the DNS server at headquarters. All other DNS queries are sent to the network DNS server specified on the Firebox.
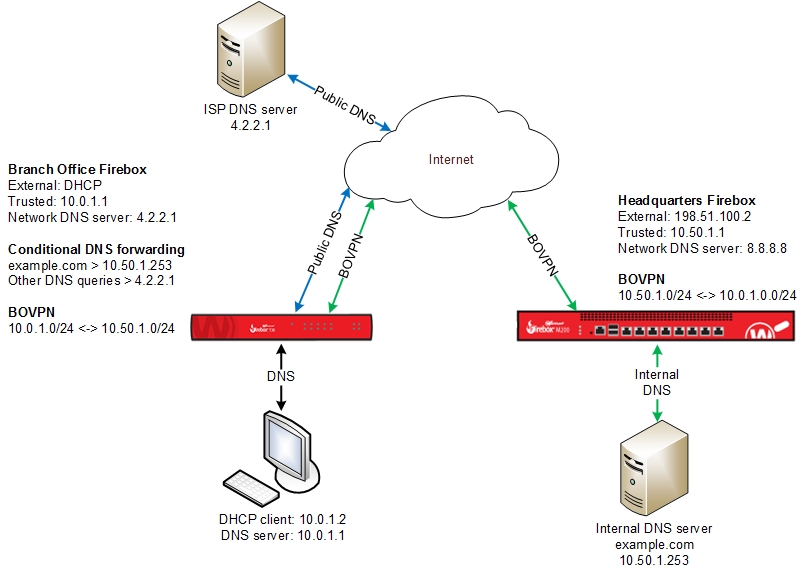
How it works:
- At the branch office, a DHCP client on the network sends a DNS query for the domain name example.com.
- The Firebox receives the query and examines its DNS cache.
- If the cache does not contain an entry for example.com, the Firebox examines its DNS Forwarding list.
- If example.com is included in the DNS Forwarding list, the Firebox forwards the query to the DNS server specified for that domain name.
In our example, the query is forwarded to the remote DNS server at headquarters, 10.50.1.253. - If example.com is not included in the DNS Forwarding list, the Firebox forwards the DNS query to the network DNS server, which is 4.2.2.1 in our example.
These images show the Network DNS and DNS forwarding settings for our example:
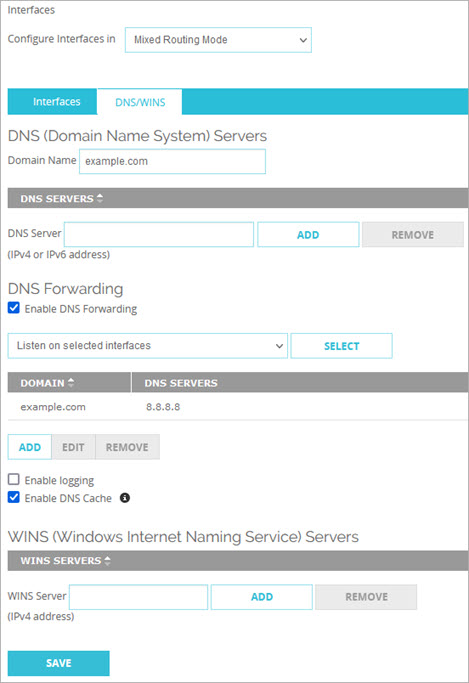
DNS forwarding settings in Fireware Web UI
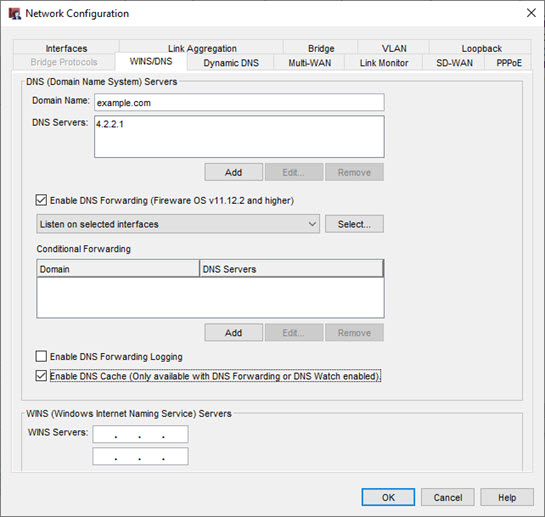
DNS forwarding settings in Policy Manager
Configure Network DNS and WINS Servers