The objective of this configuration example is to show how an organization can deploy the same wireless networks for internal employees and guests at the headquarters location and remote branch office locations using WatchGuard Access Points (AP). To do this, we use a Gateway Wireless Controller on a WatchGuard Firebox at each branch office with the same configuration as the Firebox at your headquarters.
This is useful for small deployments with few branch offices, but in this example, the company wants to use one Gateway Wireless Controller on the Firebox from the headquarters location to discover and manage all AP devices at headquarters and remote branch office locations through branch office VPNs (BOVPN).
This configuration example is intended for use with AP devices managed locally on a Gateway Wireless Controller on a Firebox. WatchGuard also provides a Wi-Fi Cloud management solution that allows you to manage your enterprise wireless networks in all company locations with cloud-based management. For more information, go to WatchGuard Wi-Fi Cloud.
This configuration example is provided as a basic guide. Your actual network environment may require additional configuration.
Solution Overview
You can use a Gateway Wireless Controller on a Firebox at the headquarters location to manage AP devices installed locally and also at remote branch office locations over a branch office VPN.
All AP devices must be paired to the Gateway Wireless Controller from your headquarters location and then assigned appropriate static IP addresses for installation at the remote branch offices. When the remote AP devices are installed at the branch offices, the Gateway Wireless Controller at the headquarters location will be able to communicate with and manage the AP devices through the branch office VPN.
Requirements
This configuration example has these requirements:
- Perform a wireless survey to optimize channel use and provide sufficient wireless coverage at the remote branch office.
- Make sure that the Firebox that hosts the Gateway Wireless Controller is properly sized to manage the amount of AP devices for the headquarters location and all branch offices.
- This configuration example is for a WatchGuard Firebox running Fireware v11.12 or higher. Remote branch offices may use third-party firewalls as BOVPN end points. Firewalls must allow TCP port 443 and UDP 2829 over the VPN for AP device management.
- WatchGuard Fireboxes must have a valid Live Security subscription.
Configuration Files
For this example, we created four configuration files:
- Firebox M200 with Single SSID over a BOVPN
- Firebox T50-W with Single SSID over a BOVPN
- Firebox M200 with Two SSIDs over a BOVPN
- Firebox T50-W with Two SSIDs over a BOVPN
Configuration for a Single SSID and Two SSIDs
In this example, the company has a head office with a Firebox M200 and a remote branch office with a Firebox T50W linked together with a branch office VPN.
The first example uses a single SSID for guest users broadcast from the headquarters location and the remote branch office location. The second example uses two SSIDs, one for internal users, and one for guest users, broadcast from the headquarters location and remote branch office location.
The Gateway Wireless Controller on the Firebox M200 manages a single AP device on the wireless network at the headquarters location. All AP devices to be installed at the remote branch office are paired to the Gateway Wireless Controller and then assigned a static IP address so that they can be discovered when installed at the remote location.
When you change the IP address of the AP after pairing, this might result in the AP being considered as untrusted by Gateway Wireless Controller if the Trust Store is enabled. We recommend you temporarily disable the Trust Store feature during the deployment of the remote APs with static IP addresses.
How It Works
The Wi-Fi LAN zone across remote offices use: 10.x.y.0 where x is linked to the site, and y to the wireless zone.
Single SSID
- Headquarters trusted LAN: 10.220.1.0/24
- Headquarters Wi-Fi zone: 10.220.6.0/24
- Branch Office trusted LAN: 10.50.1.0/24
- Branch Office Wi-Fi zone: 10.50.6.0/24
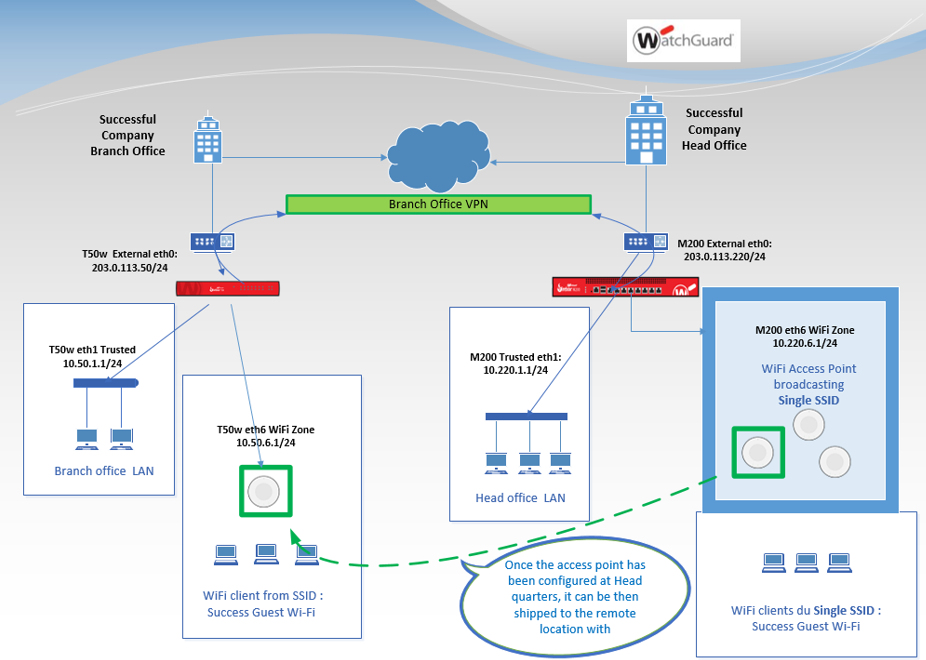
Single SSID across BOVPN set up with two locations, controlled by headquarters office
Two SSIDs
- Headquarters trusted LAN: 10.220.1.0
- Headquarters Guest Wi-Fi network: 10.220.50.0
- Headquarters Internal Wi-Fi network: 10.220.55.0
- Branch Office trusted LAN : 10.50.1.0
- Branch Office Guest Wi-Fi network: 10.50.50.0
- Branch Office Internal Wi-Fi network: 10.50.55.0
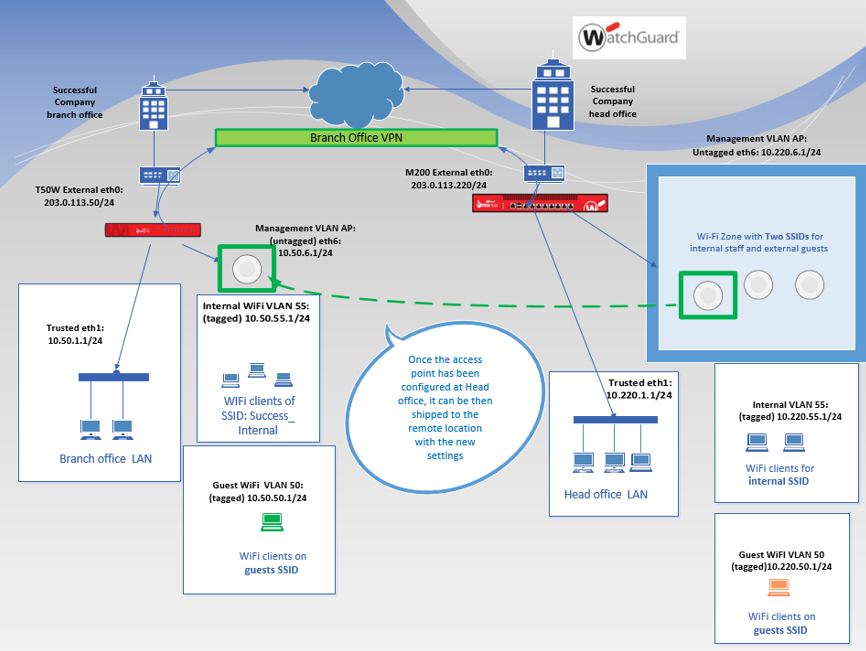
Two SSIDs across BOVPN set up with two locations, controlled by headquarters office
All AP devices to be installed at the remote branch office are first paired to the Gateway Wireless Controller at your headquarters location. WatchGuard APs must be connected to a Trusted or Optional network on the Firebox that has DHCP enabled. For instructions on how to pair an AP to the Gateway Wireless Controller, go to WatchGuard AP Discovery and Pairing.
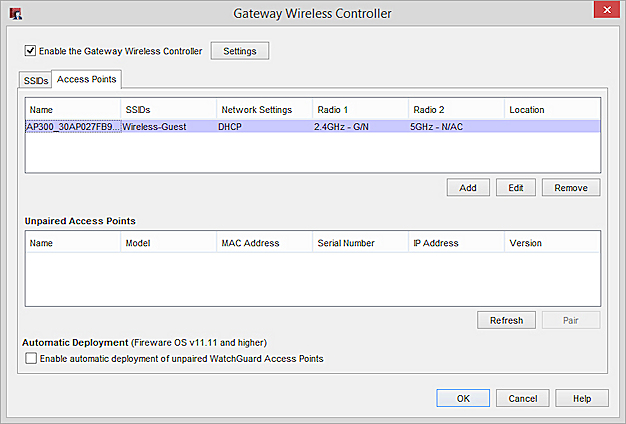
Paired Access Point on the Gateway Wireless Controller
After you discover and pair a WatchGuard AP with a Gateway Wireless Controller, you can then assign a static IP address instead of the default DHCP address to enable easier management of AP devices through the VPN. The static IP address must be configured in the same network defined at the remote branch office location.
In this example, we edit the paired AP device settings and change the name of the AP to reflect the new location, and change the network settings for the AP to use a static IP address for the remote wireless network.
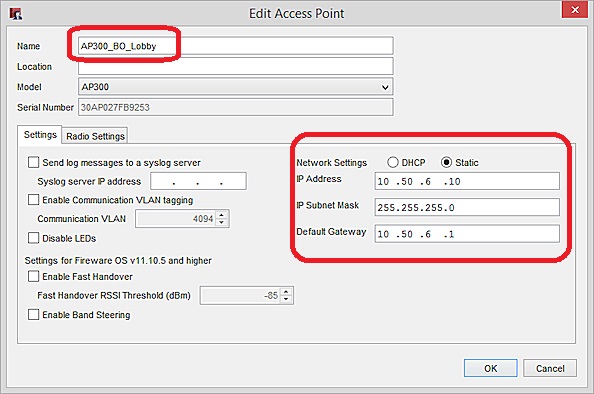
When you save the configuration, you will lose connectivity to the AP device because the IP address assigned is for the remote branch office network.
You can now deliver the APs to their respective branch office locations for installation in their new network. When the APs are connected at the remote branch office network, you will be able to manage them from the Gateway Wireless Controller at the headquarters location.
If you use the Gateway Wireless Controller Trust Store feature, you can re-enable the Trust Store after the APs are successfully deployed to the remote locations.
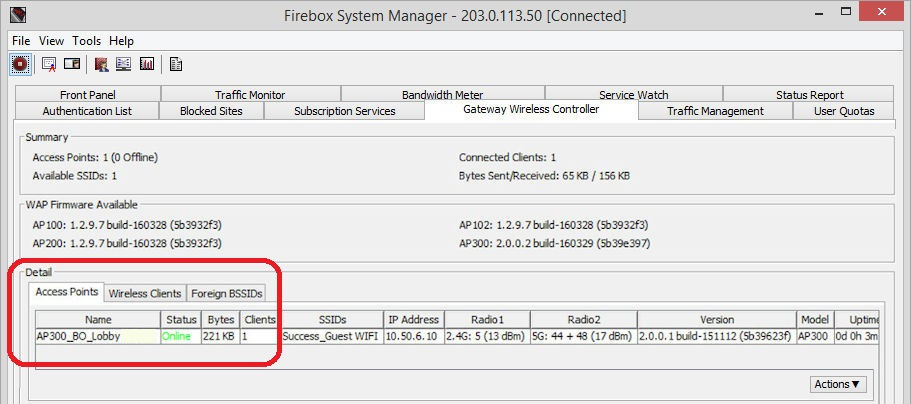
If the AP has connectivity, it will appear as Online in the Gateway Wireless Controller on the Firebox at the headquarters location.
Conclusion
You can repeat these procedures for multiple APs that will be delivered to remote branch offices. You must deploy and pair the AP devices at the headquarters location, then assign static IP addresses for their intended destination networks.