To configure your Firebox to automatically connect hotspot users to an external web server for authentication, you can enable an External Guest Authentication hotspot on the Firebox. Before you enable an External Guest Authentication hotspot on the Firebox, you must configure the web server for external guest authentication.
When a user connects to the External Guest Authentication hotspot, the Firebox sends the user to the external web server, which asks the user to provide authentication credentials or other information. Based on the information the user provides, the external web server sends an access decision to the Firebox. The Firebox then either allows or denies the user access to the hotspot.
External Guest Authentication is not related to other types of user authentication supported by your Firebox.
This feature is described in terms of authentication, but it does not require the external web server to authenticate users. You can create an authentication page on your web server to ask hotspot users for any information that you want to use as criteria for access to your hotspot.
Before You Begin
Before you configure the external web server and enable external guest authentication on the Firebox, you must select the shared secret, authentication URL, and authentication failure URL to use. These settings affect the configuration of the external web server and the hotspot configuration on the Firebox.
Shared Secret
The external web server uses the shared secret to calculate a checksum it includes with the access decision it sends to the Firebox. The Firebox uses the shared secret to verify the checksum it receives. The shared secret must be between 1 and 32 characters.
Authentication URL
This is the URL on the external web server of the web page where a hotspot user authenticates. In the hotspot configuration on the Firebox, the Authentication URL must begin with https:// or http://. You can specify the IP address or domain name of the web server.
Authentication Failure URL
This is the URL on the external web server of the web page the hotspot user sees if external guest authentication is not successful. In the hotspot configuration on the Firebox, the Authentication Failure URL must begin with https:// or http://. You can specify the IP address or domain name of the web server.
Configuration
Because configuration of the web server requires web programming, we recommend that you configure the web server first. A link to a code example is included in the setup instructions for the web server. After you set up the web server, configure the Firebox hotspot for External Guest Authentication.
For details about the configuration requirements and procedures, see:
- Configure a Web Server for Hotspot External Guest Authentication
- Configure an External Guest Authentication Hotspot
After you have configured your web server and hotspot, you can test external guest authentication on your hotspot and review the log messages to identify any errors.
For an example of the script on the external web server, see the WatchGuard Knowledge Base.
External Guest Authentication Example
Communication between the Firebox and the external authentication server occurs through the hotspot client browser. The Firebox and authentication server use the parameters specified in the URLs to allow the communication. This example provides some example URLs that show at a high level how external authentication operates. For more details and a description of all the parameters in each URL, go to Configure a Web Server for Hotspot External Guest Authentication.
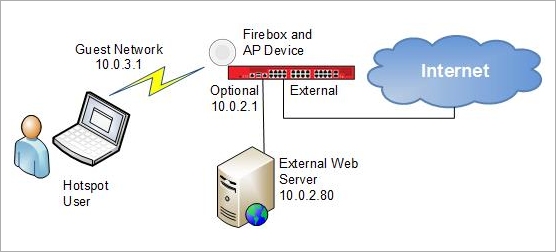
The URLs in this example are based on these configuration settings:
- Firebox:
- Guest Network IP address — 10.0.3.1
- Optional interface IP address — 10.0.2.1
- External Web Server:
- IP address — 10.0.2.80
- Authentication URL — http://10.0.2.80:8080/auth.html
- Authentication Failure URL — http://10.0.2.80:8080/failure.html
- Hotspot User:
- MAC address — 9C:4E:36:30:2D:26
- The hotspot user initially tries to connect to http://www.google.com.
Step 1 — Hotspot User Authenticates
When a user first tries to get access to a website, the Firebox receives an HTTP request from the hotspot user. The Firebox verifies the MAC address to see if this user already has a current hotspot session. If there is already a hotspot session for this MAC address, the Firebox allows or denies the traffic based on the firewall policy configuration. If this is a new MAC address, to send the access request URL to the external web server, the Firebox sends a redirect to the hotspot client browser.
Example access request URL:
http://10.0.2.80:8080/auth.html?xtm=http://10.0.3.1:4106/wgcgi.cgi&action=hotspot_auth
&ts=1344238620&sn=70AB02716F745&mac=9C:4E:36:30:2D:26&redirect=http://www.google.com/
The authentication page on the external web server appears in the browser. The hotspot user provides the information required to authenticate.
Step 2 — External Web Server Sends the Access Decision
After the external web server authenticates the hotspot user, it sends the access decision URL to the Firebox through the hotspot client browser.
Example access decision URL:
http://10.0.3.1:4106/wgcgi.cgi?action=hotspot_auth&ts=1344238620&success=1
&sig=a05d352951986e5fbf939920b260a6be3a9fffd3&redirect=http://www.google.com/
In this URL:
- Success=1 indicates that the access decision from the web server was to allow access to this URL.
- The URL specified in the redirect section of the access decision URL is the URL the hotspot user originally requested.
- The external web server could optionally replace this with a different URL.
Step 3 — Firebox Allows or Denies Access
The Firebox reads the access decision (success=1 or success=0) and verifies the checksum. If success=1 and the checksum verification is successful, the Firebox creates a hotspot session for the client and redirects the client to the URL specified in the access decision URL. If success=0 or any authentication error is detected, the Firebox redirects the client to the authentication failure URL.
In this example, authentication is successful, so the originally requested site, http://www.google.com, appears in the browser.
If authentication fails or if access was denied, the authentication failure URL appears in the browser.
Example failure URL:
http://10.0.2.80:8080/failure.html?error=510&sn=70A70272B454E&mac=9C:4E:36:30:2D:26