Applies To: Endpoint Security Elite, Endpoint Security 360, Endpoint Security Prime, WatchGuard EDR, WatchGuard EDR Core, Endpoint Security Basic
Some Linux distributions detect when a computer has Secure Boot enabled. With Secure Boot enabled, WatchGuard Endpoint Security software that is not correctly signed is automatically disabled.
Secure Boot is detected when the software is installed, or later, if the distribution did not initially support this feature but it was added in a later update. In either case, the management UI shows an error and the endpoint software does not run.
To solve the protection errors related to Secure Boot from the computer experiencing the problem, make sure your system meets these requirements and complete the steps to resolve the errors.
System Requirements
- DKMS: mokutil and openssl packages.
- Oracle Linux 7.x/8.x with kernel UEKR6: Repository ol7_optional_latest enabled, and openssl, keyutils, mokutil, pesign, kernel-uek-devel-$(uanme -r) packages.
Resolve the Protection Errors
- Check the state of Secure Boot:
$ mokutil --sb-state
Secure Boot enabled. - Verify that the driver is not loaded:
$ lsmod | grep prot - Import the protection keys:
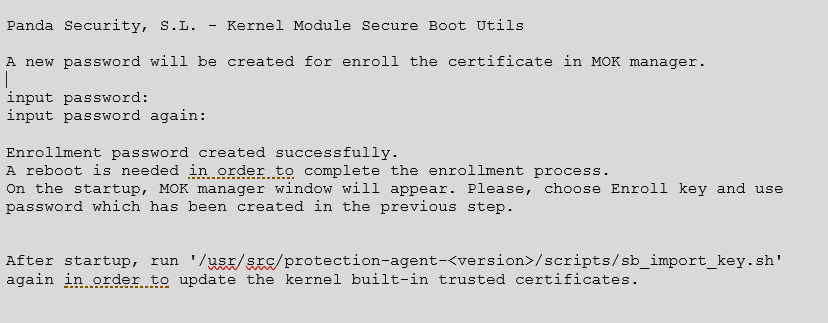
$ sudo /usr/src/protection-agent-<version>/scripts/sb_import_key.sh
A message appears to explain the implications of Secure Boot.
The protection and agent <version> have this format:
$ sudo /usr/src/protection-agent-03.01.00.0001-1.5.0_741_g8e14e52/scripts/sb_import_key.sh
The name varies according to the version and the driver. - Press C to register the certificate used to sign the modules.
- Enter an 8-character password:
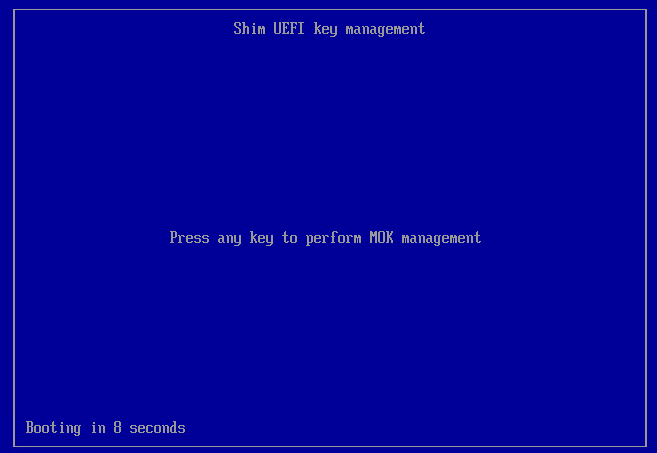
- Restart the computer and complete the registration process.
If it is a virtual machine, use the hypervisor. - To start the registration process, press any key.
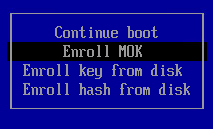
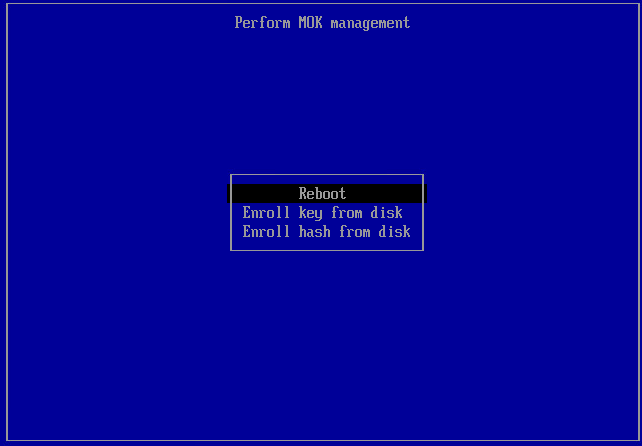
This screen appears for a limited time. If you do not press a key, you must restart the registration process. - Select Enroll MOK.
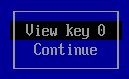
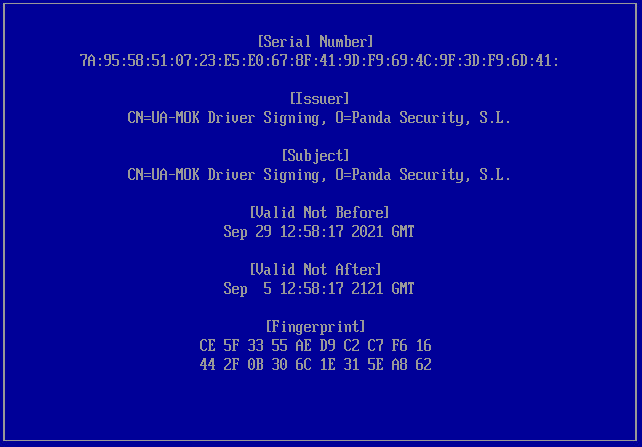
- To view the keys that are going to be registered, select View key.
- Confirm the keys belong to the WatchGuard Endpoint Security protection. Select Continue to continue the registration process.
- When prompted to Enroll the key, select Yes.
- Enter the password created previously.
- Select Reboot.
-
To confirm the driver is loaded, type $ lsmod | grep prot.
Oracle Linux 7.x/8.x with UEKR6 Kernel
When the distribution installed is Oracle Linux 7.x/8.x with UEKR6 kernel, after you complete the steps to register the certificate, complete these steps:
- Run this command:
sudo /usr/src/protection-agent-<version>/scripts/sb_import_key.sh
This adds the certificate used to sign the modules to the list of certificates trusted by the kernel. The modified kernel is signed and added to the list of kernels in GRUB. The module is loaded and started. -
Restart the computer.
The module is loaded and started. - To confirm that the certificate was added correctly, run this command:
sudo /usr/src/protection-agent-<version>/scripts/sb_import_key.shThe results should be:
- The signers common name is UA-MOK Driver Signing
- Image /boot/vmlinuz-kernel-version-panda-secure-boot already signed
- Kernel module successfully loaded