Applies To: WatchGuard Full Encryption
This topic describes some of the most common errors that can occur during encryption of computers by Full Encryption:
To review encryption status errors:
- In WatchGuard Cloud, select Monitor > Endpoint Security.
- Select Status > Full Encryption.
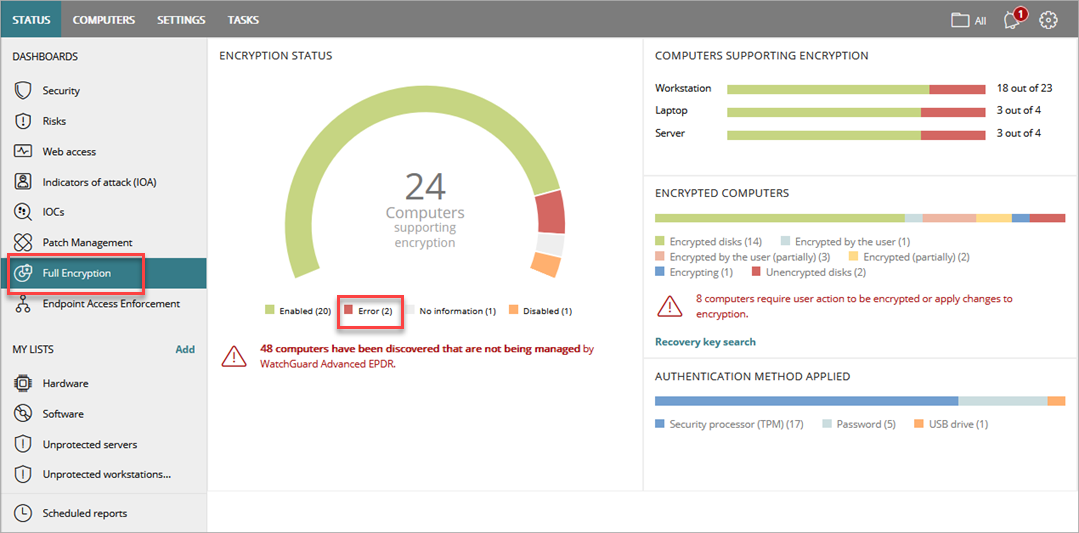
- On the dashboard, in the Encryption Status tile, select Error.
The Encryption Status list opens and shows all errors. Some error messages depend on the settings defined for Full Encryption. To review error details, select an error message in the table.
Encryption Errors Pending User Action
Encryption errors have various causes and can require different solutions. On Windows computers, the error code is received from BitLocker. If the error code you received is not in this help topic, you can search for it in the Microsoft documentation to find a problem description and solution.
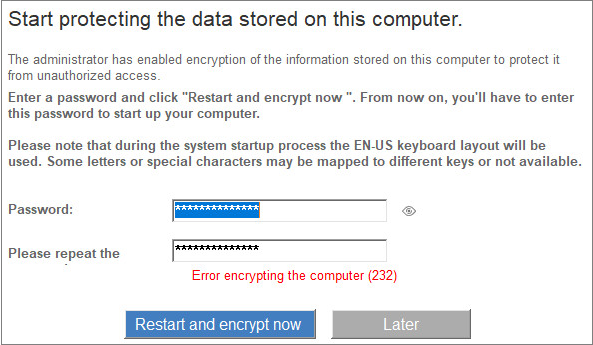
When a password or reboot is required, these error messages could appear.
| Error | Description and Solution |
|---|---|
|
Error 232 |
This error message occurs when Full Encryption tries to encrypt the Windows Server Core.
On the Windows Server Core, the bdehdcfg component is not available by default. This component is necessary for Full Encryption to encrypt this operating system. To avoid the error message, follow Microsoft instructions to download and install the component, and retry encryption. If the problem persists, collect data from the computer, and report the issue to WatchGuard Support. |
|
-2144862201 |
The TPM is disabled. |
|
-2144272329
|
The group policy setting that requires FIPS compliance prevents a local recovery password from being generated and written to the key backup file. Encryption continues. |
|
-2144272290
|
The group policy for encryption without TPM is not set. Enable the Require additional authentication at startup group policy, and select the Allow BitLocker without a compatible TPM check box. |
|
-2144272177 |
Go to Microsoft System Error Codes (0 - 499). |
|
-2144862201 |
TPM is disabled. |
| -2144272302 (0x80310052) | The path specified in the Boot Configuration Data (BCD) for a BitLocker Drive Encryption integrity-protected application is incorrect. Verify and correct your BCD settings and try again. |
| -214272312 | BitLocker Drive Encryption cannot be enabled on the operating system drive. Contact the computer manufacturer for BIOS upgrade instructions. |
Errors Encrypting the Computer
If the computer can only be encrypted with a USB drive for authentication, but the option to encrypt this type of computer is disabled in the encryption settings, you must assign the computer settings with encryption disabled.
If the computer does not support the authentication method selected in the settings. Do not ask for a password to access the computer. To apply this method, the computer must have a security processor (TPM). Edit the settings and verify that the problem is resolved.
You cannot use Full Encryption to encrypt computers from a remote desktop session. In a remote desktop session, you are not prompted to enter the encryption password. After you assign the encryption settings profile to the computer, you must log into the local console directly. You are then prompted to enter the encryption password.
| Error | Description/Solution |
|---|---|
| -2144862202 | The TPM is inactive. |
| -2144862188 | The TPM already has an owner. |
| -2144272293 | The group policy for the specified authentication method is not set. Enable the Require additional authentication at startup group policy. |
| -2144862208 | Go to Microsoft System Error Codes (0 - 499). |
| -2144845809 | A compatible TPM security device cannot be found on this computer. |
| -2144272203 |
This error message is caused by a Microsoft known issue that affects Microsoft Surface Pro. This Microsoft known issue requires you to manually set a BitLocker Group Policy Object (GPO). The policy setting enables users to enable authentication options that require user input from the pre-boot environment, even if the platform indicates a lack of pre-boot input capability. For more information, go to Enable the Local Group Policy. |
| -2147023890 (0x800703EE) |
The volume for a file has been externally altered so that the opened file is no longer valid. Operating system error which may happen when you try to encrypt a volume with Bitlocker, and the Registry.pol file is corrupted. The Registry.pol file is a component of Microsoft Group Policy Object Editor tool, which is responsible for storing Windows policies' data. If this file is corrupted, the system must regenerate it then you must update the Windows policies. A possible solution is to rename the file so that the system generates it again. For more information, go to Rename the Registry.pol File. |
| -2147024809 | Incorrect parameter. You should manually set a BitLocker Group Policy Object (GPO). |
| -2144272288 | The group policy does not allow the use of a PIN at startup. Select a different BitLocker startup option. |
Enable the Local Group Policy
Error -2144272203 requires you to manually set a BitLocker Group Policy Object (GPO). The policy setting will allow users to enable authentication options that require user input from the pre-boot environment, even if the platform indicates a lack of pre-boot input capability, which is the case with Surface Pro.
To enable the Local Group Policy for BitLocker:
- Press the Windows key + R.
- In the Run dialog box, type gpedit.msc.
- Click OK.
- In the Local Computer Policy section, navigate to Computer Configuration > Administrative Templates > Windows Component > BitLocker Drive Encryption > Operating System Drives.
- Select the Enable use of BitLocker authentication requiring pre-boot keyboard input on slates policy option to enable it.
Caution: When this option is enabled, devices must have an alternative means of pre-boot input, such as an attached USB keyboard.
- Reboot the computer.
If the problem persists, contact Technical Support.
Rename the Registry.pol File
Rename the Registry.pol file so that the system generates it again.
To rename the Registry.pol file:
- Go to C:\Windows\System32\GroupPolicy\Machine\Registry.pol and rename the file as Registry.pol_old.
The file could be hidden. - Open a CMD window with administrator permissions and push the Windows policies update with this command: gpupdate /force
- Restart the computer.
If the problem persists, contact Microsoft.