Duo Security Integration Overview
This document describes the steps to integrate WatchGuard Mobile VPN with SSL client software download access and Mobile VPN with SSL client authentication with the Duo Security® two-factor authentication solution. This integration only uses the Duo Security Authentication Proxy service on a domain controller and does not use an NPS server. For more details about how to integrate Duo Security RADIUS Authentication with an NPS server, go to the Duo Security Authentication Integration Guide.
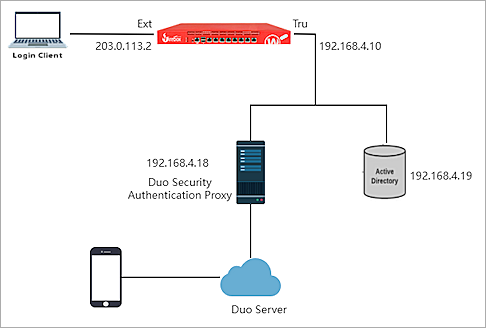
You must install a local Duo Proxy service on a device within your network. This Duo Proxy receives incoming RADIUS requests from your Firebox, contacts your existing local LDAP/AD to perform primary authentication, and contacts the Duo cloud service for secondary authentication.
This integration requires that each Active Directory (AD) user is defined in the Firebox VPN configuration. If you want to use AD groups for the authentication, go to:
Test Topology
This diagram shows the test topology for this integration.
Platform and Software
The hardware and software used in this guide include:
- Firebox with Fireware v12.8 or higher
- Duo Security Authentication Proxy 5.6.1 on Windows
- Windows Server 2016 with Active Directory Domain Services
- Duo Mobile Application 4.15.0.43.1 on iOS
Configuration
To complete this integration, you must have:
- Duo account
- Duo Security Authentication Proxy
- Active Directory
- WatchGuard Firebox
Use the Duo account to log in to the Duo Service to manage applications, enroll users, and get integration keys. The Duo Security Authentication Proxy acts as a bridge. It communicates with Active Directory, Duo Security service in the cloud, the WatchGuard Firebox, and the Duo mobile app. Active Directory is used for primary user authentication.
In our configuration, the Duo Security Authentication Proxy and Active Directory are on the same subnet.
To ensure reliable communication of services, avoid port overlap between the Firebox and the Duo Security Authentication Proxy.
Configure Firebox
You must configure RADIUS authentication settings and enable Mobile VPN with SSL on your Firebox.
Configure RADIUS Authentication
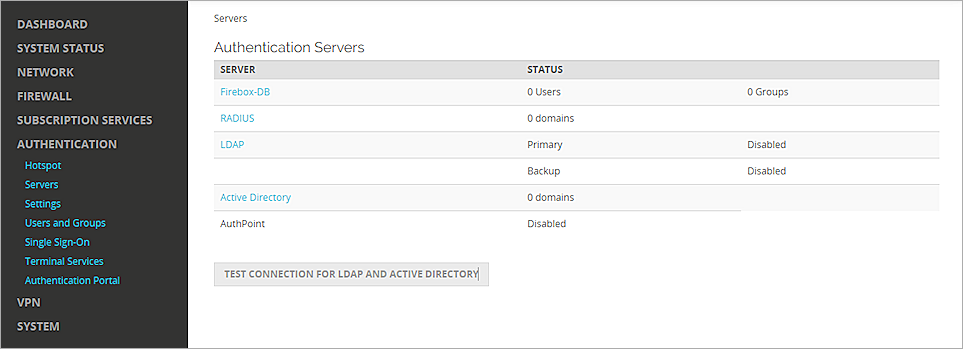
- Log in to Fireware Web UI (https://<your firebox IP address>:8080).
- Select Authentication > Servers.
The Authentication Servers page appears. - From the Authentication Servers list, select RADIUS.
The RADIUS page appears. - Click Add.
The Add page appears. - In the Domain Name text box, type the domain name for this RADIUS server. Users must specify this domain name on the user login page. You cannot change the domain name after you save the settings.
- In the Primary Server Settings section, select the Enable RADIUS Server check box.
- In the IP Address text box, type the IP address of the Duo Security Authentication Proxy.
- In the Port text box, leave the default port setting of 1812.
- In the Shared Secret and Confirm Secret text boxes, type a shared secret key. This key is used to communicate with the Duo Security Authentication Proxy Server.
- In the Timeout text box, type 60.
- Leave the default value for Group Attribute.
- Click Save.

Configure Mobile VPN with SSL
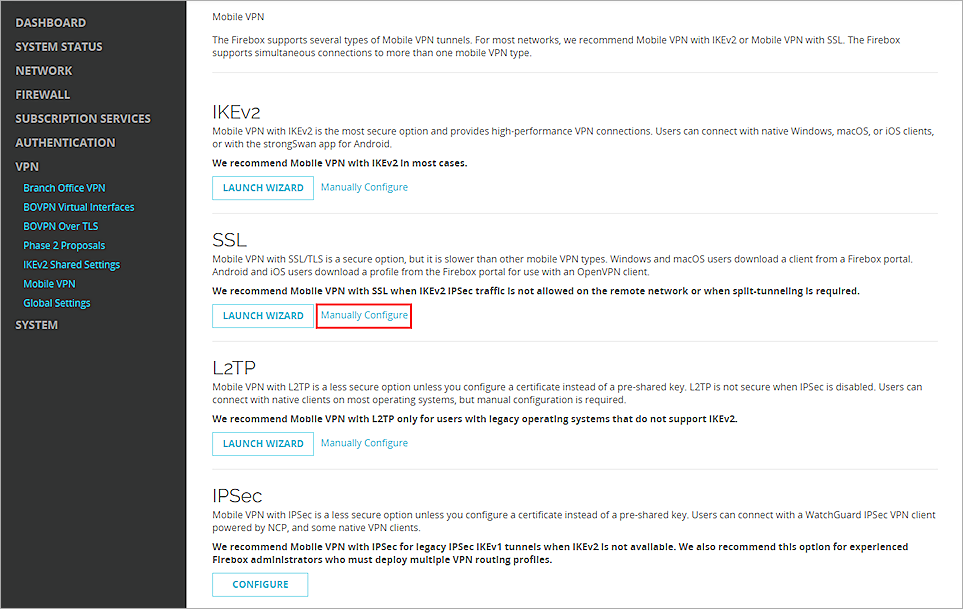
- Select VPN > Mobile VPN.
- In the SSL section, click Manually Configure.
- Select the Activate Mobile VPN with SSL check box.
- In the General section, for the Primary text box, type the public IP address (External IP address) or domain name of the Firebox. This is the IP address or domain name that Mobile VPN with SSL clients connect to by default.
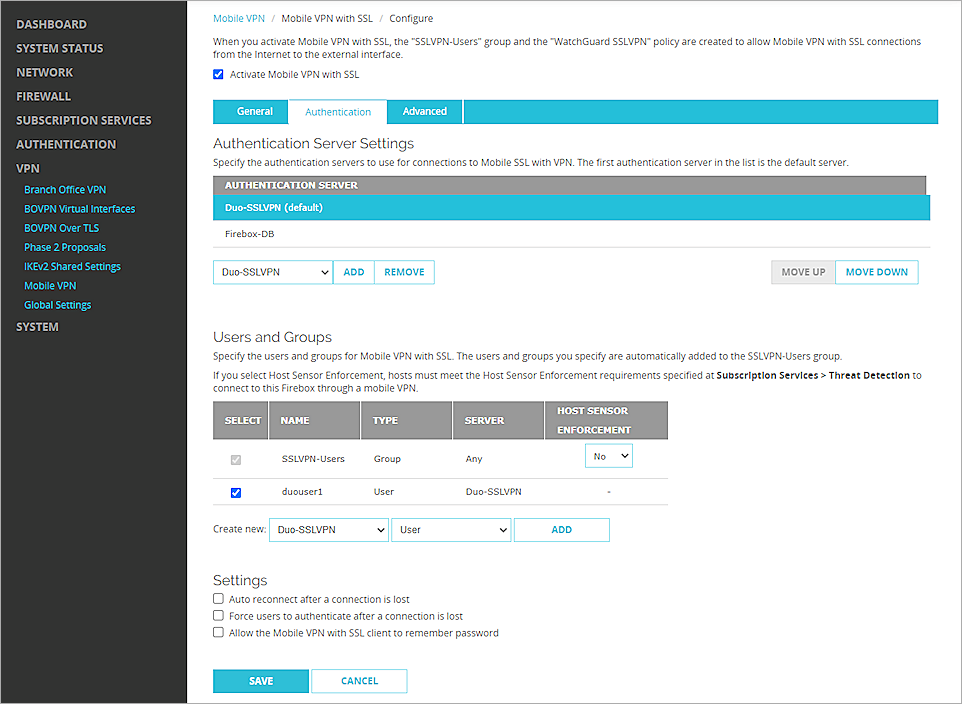
- Select the Authentication tab.
- From the Authentication Server drop-down list, select the authentication server you created. Click Add.
- In the Authentication Server list, select your authentication server and click Move Up to move it to first position on the list to make it the default authentication server.
Mobile VPN with SSL uses the default authentication server unless a user specifies an authentication server in the Username text box on the Mobile VPN with SSL client. - In the Users and Groups section, from the Create new drop-down list, select the authentication server you created.
- From the adjacent drop-down list, select User.
- Click Add.
The Add User or Group dialog box appears. - For Type, select User.
- In the Name text box, type the user name.
- From the Authentication Server drop-down list, select your authentication server.
- Click Save.
- Click Save.
Configure Duo
Set Up an Application
- Sign up for a Duo account.
- Log in to the Duo Admin Panel and select Applications.
- Select Protect an Application and find RADIUS in the application list.
- Select Protect to get the values of the Integration key, Secret key, and API hostname.
- Click Save.
Sync Users to Duo from Active Directory
Organizations with an existing on-premises Microsoft Active Directory domain can import users, phones, and groups into Duo with directory synchronization.
For detailed instructions about how to sync users from Active Directory, see Synchronizing Users from Active Directory.
Configure the Duo Security Authentication Proxy for Primary Authentication
The Duo Security Authentication Proxy validates the user password. In our integration, you must configure the Proxy to communicate with Active Directory.
To configure the Proxy, add an [ad_client] section at the beginning of the file that includes the properties described in this list. All properties are required.
|
Properties |
Description |
|---|---|
| host |
The hostname or IP address of your domain controller. |
|
service_account_username |
The user name of a domain account that has permission to bind to your directory and perform searches. |
| service_account_password |
The password corresponds to service_account_username. |
|
search_dn |
The LDAP distinguished name (DN) of an Active Directory container or organizational unit (OU) contains all of the users you want to permit to log in. |
For example:
[ad_client]
host=192.168.4.19
service_account_username=Administrator
service_account_password=Passw0rd
search_dn=DC=example,DC=com
Configure the Duo Security Authentication Proxy to Work with the Firebox
To configure the Duo Authentication Proxy to work with the Firebox, create a [radius_server_auto] section in the Proxy configuration file that includes the properties described in this list. All properties are required.
Save the configuration file when you are done.
|
Properties |
Description |
|---|---|
| ikey |
The Integration key, as referenced in the Setting Up an Application section of this document. |
| skey |
The Secret key, as referenced in the Setting up An Application section of this document. |
| api_host |
The API hostname, as referenced in the Setting up An Application section of this document. |
| radius_ip_1 |
The IP address of the Firebox that is connected to the Proxy. |
| radius_secret_1 |
A secret that is shared between the Proxy and the Firebox. |
|
client |
Set this value to ad_client so that the Proxy uses Active Directory for primary authentication. Make sure an [ad_client] section as described previously is configured. |
An example configuration file that uses Active Directory as the primary authenticator:
[ad_client]
host=192.168.4.19
service_account_username=Administrator
service_account_password=Passw0rd
search_dn=DC=example,DC=com
[radius_server_auto]
ikey=DI8XXZ4FIFR5ONXU5ZDM
skey=Vi3SSzp5T5YwUEX8RyzIOO1IwWxnH9kQfwnFzDDO
api_host=api-537a49ce.duosecurity.com
radius_ip_1=192.168.4.10
radius_secret_1=password
client=ad_client
port=1812
failmode=safe
pass_through_all=true
Start the Duo Authentication Proxy
On the Windows computer where the Duo Security Authentication Proxy is installed, open an Administrator command prompt and type this command:
net start DuoAuthProxy
Test the Integration
To test the integration of your Mobile VPN with SSL, authenticate with a mobile token on your mobile device. You can authenticate with a passcode or a push notification.
If you select passcode authentication, you must type the password followed by a comma and append the passcode from the Duo Mobile App.
In this example, we show the push authentication method (users receive a push notification in the mobile app that they must approve to authenticate).
- Open your Mobile VPN with SSL client.
- In the Server text box, type the external IP address of the Firebox.
- Type your user name and password.
- Click Connect.
- Approve the authentication request that is sent to your mobile device.
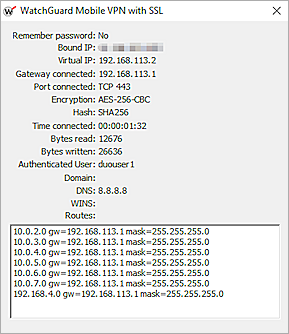
The VPN connects successfully.