This integration guide describes how to configure a Branch Office VPN (BOVPN) tunnel between a WatchGuard Firebox and a Sophos XG firewall.
WatchGuard provides integration instructions to help our customers configure WatchGuard products to work with products created by other organizations. If you need more information or technical support about how to configure a third-party product, go to the documentation and support resources for that product.
Contents
Integration Summary
The hardware and software used in this guide include:
- WatchGuard Firebox
- Fireware v12.10
- Sophos XG Firewall SFVUNL
- SFOS 19.5.3 MR-3-Build652
Topology
This diagram shows the topology for a BOVPN connection between a Firebox and a Sophos XG Firewall.

Configure the Firebox
To configure a BOVPN connection on a Firebox:
- Log in to Fireware Web UI.
- Select VPN > Branch Office VPN.
The Branch Office VPN configuration page opens. - In the Gateways section, click Add.
The add Branch Office VPN settings page opens.
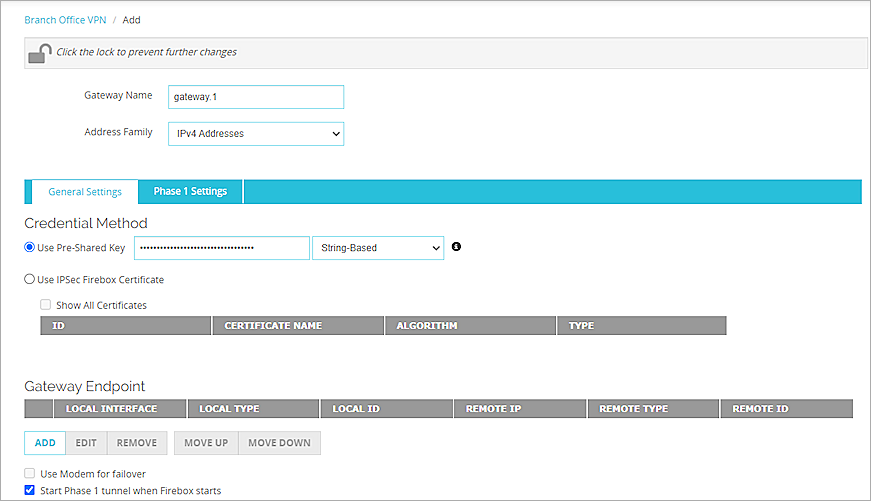
- In the Gateway Name text box, type a name to identify this Branch Office VPN gateway.
- From the Address Family drop-down list, select IPv4 Addresses.
- From the Credential Method section, select Use Pre-Shared Key.
- In the adjacent text box, type the pre-shared key.
- From the Gateway Endpoint section, click Add.
The Gateway Endpoint Settings (IPv4) dialog box opens.
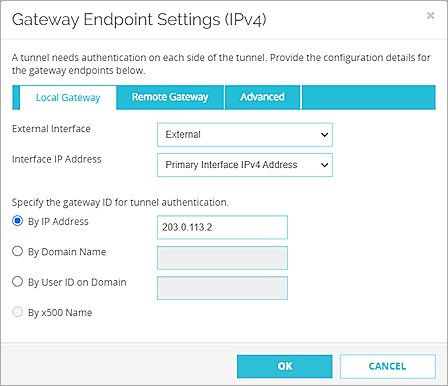
- From the External Interface drop-down list, select External.
- From the Interface IP Address drop-down list, select Primary Interface IPv4 Address.
- To specify the local gateway ID for tunnel authentication, select By IP Address.
- In the adjacent text box, type the primary IP address of the External Firebox interface.
- Select the Remote Gateway tab.

- To specify the remote gateway IP address for the tunnel, select Static IP Address.
- In the adjacent text box, type the IP address of your Sophos XG firewall WAN connection.
- To specify the remote gateway ID for tunnel authentication, select By IP Address.
- In the adjacent text box, type the IP address of your Sophos XG firewall WAN connection.
- Click OK.
- In the Gateway Endpoint section, select the Start Phase 1 Tunnel when Firebox Starts check box.
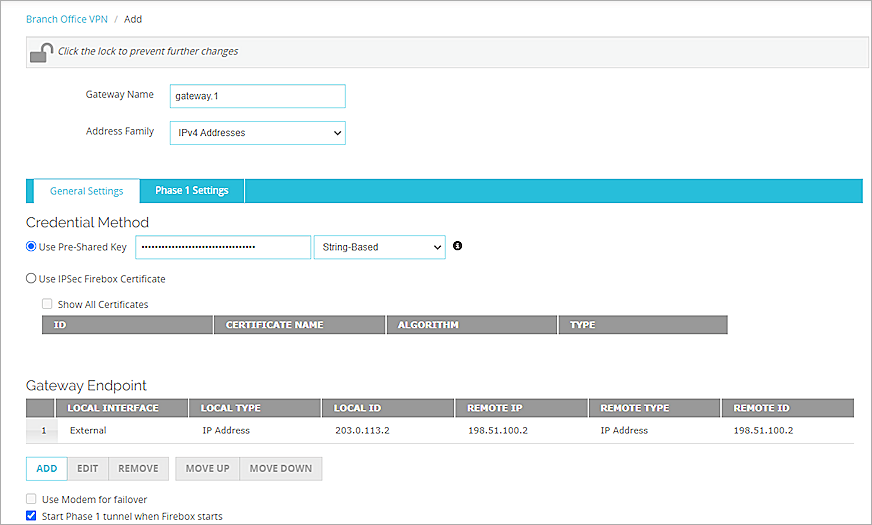
- Select the Phase 1 Settings tab.
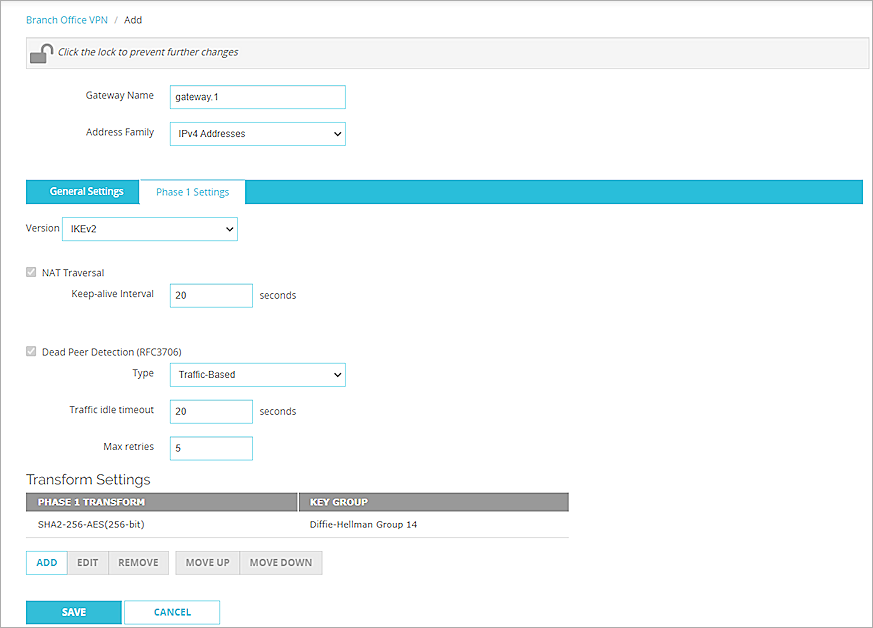
- From the Version drop-down list, select IKEv2.
- Keep the default values for all other Phase 1 settings.
- Click Save.
The Branch Office VPN page opens.
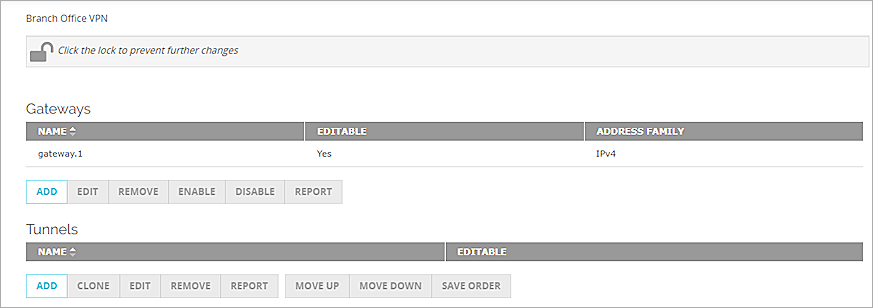
- From the Tunnels section, click Add.
The Tunnel settings page opens.
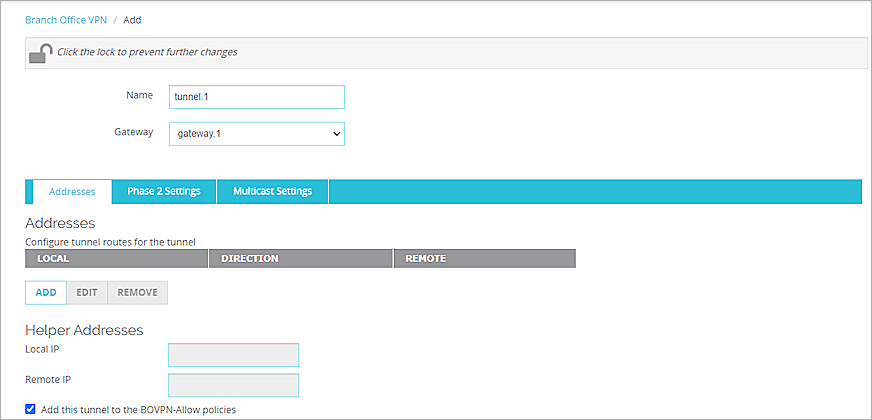
- From the Gateway drop-down list, select the gateway. In our example, we use Gateway.1.
- From the Addresses section, click Add.
The Tunnel Route Settings page opens.
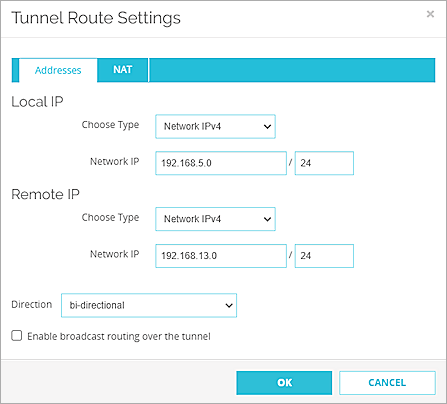
- From the Local IP section, from the Choose Type drop-down list, select Network IPv4.
- In the Network IP text box, type the local IP segment. This is the local network protected by the Firebox.
- From the Remote IP section, from the Choose Type drop-down list, select Network IPv4.
- In the Network IP text box, type the remote IP segment. This is the local network protected by the Sophos XG Firewall.
- From the Direction drop-down list, select bi-directional.
- Click OK.
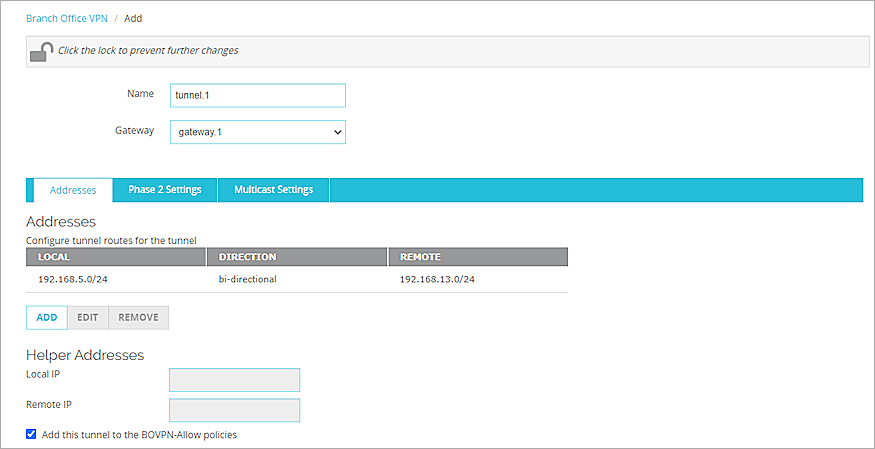
- From the Phase 2 Settings tab, keep the default values for all options.
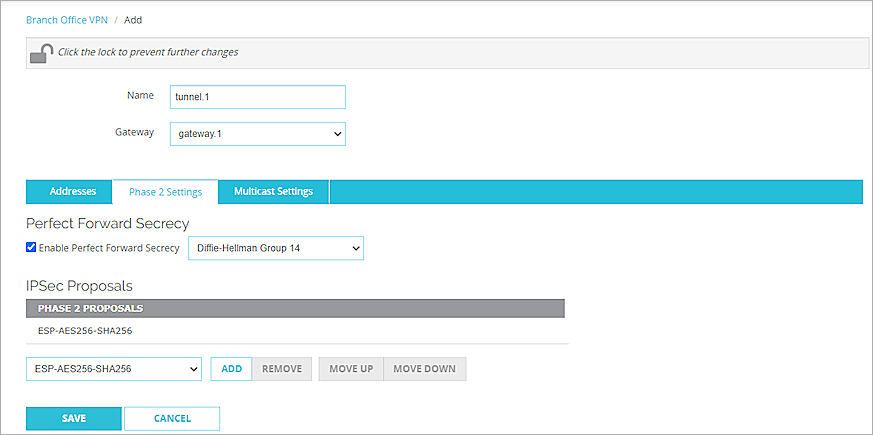
- Click Save.
Configure the Sophos XG Firewall
From the Sophos XG Firewall Web UI, configure the Sophos XG firewall.
To configure the Sophos XG Firewall, complete these steps:
Configure Basic Settings
To configure the Sophos XG Firewall, configure these basic settings:
- Log in to the Sophos XG Firewall Web UI at https://<IP address of the Sophos firewall>. The default URL is https://172.16.16.16:4444.
- Configure the interfaces. For information about how to configure interfaces, go to the Sophos XG Firewall documentation. Our example uses192.168.13.3 for the IPv4 address of PortA.
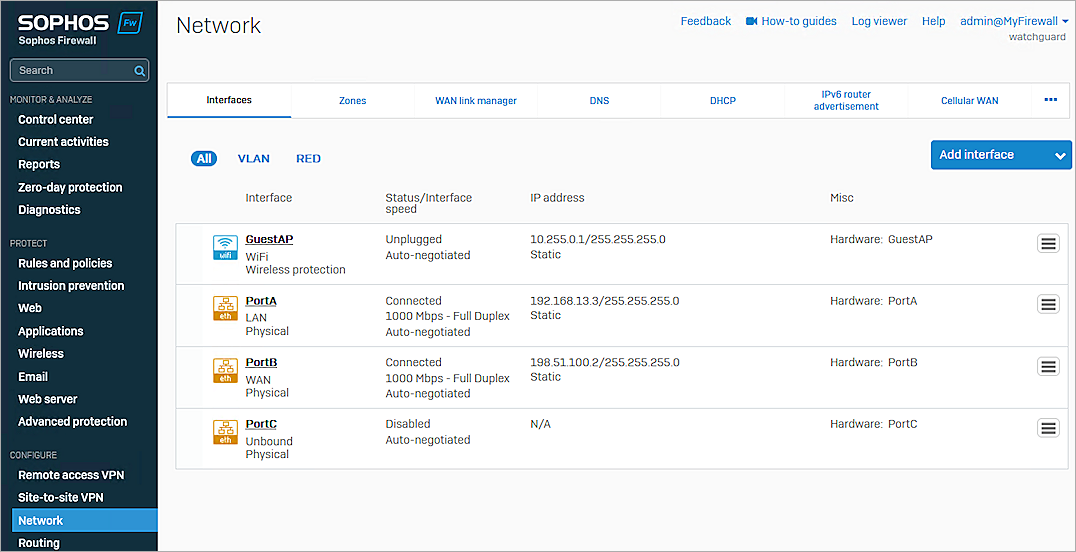
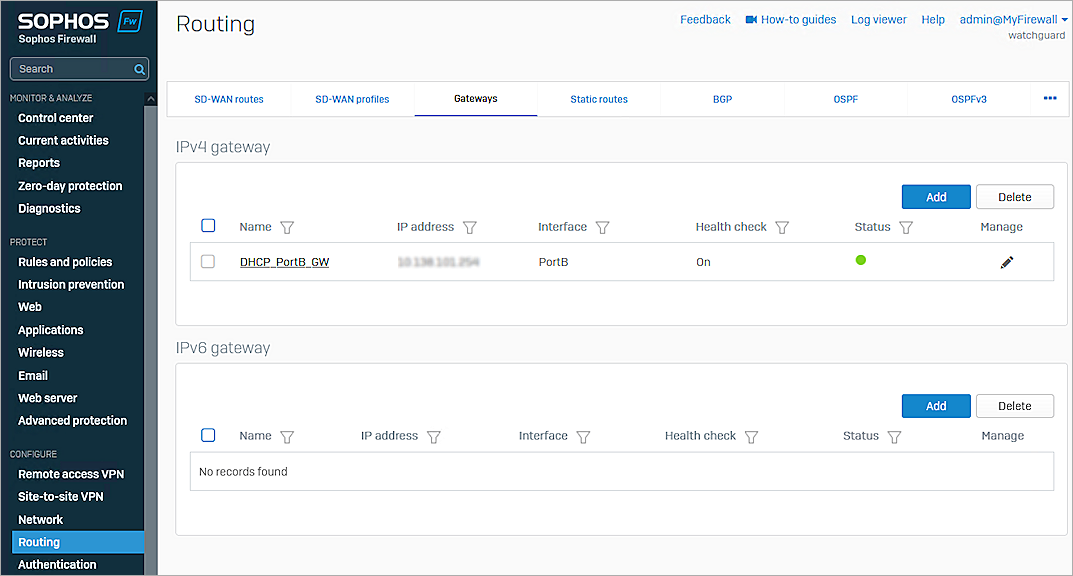
- Select Configure > Routing > Gateways.
- Verify the gateway status is green.
Add IPSec Profiles
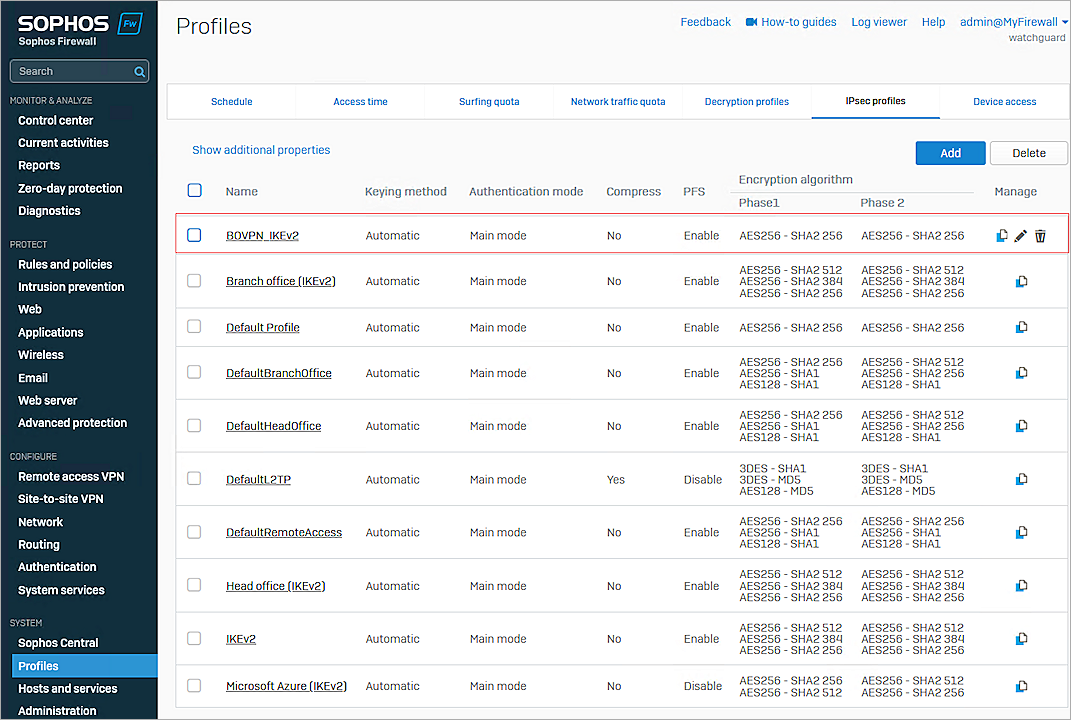
To add IPSec profiles, from the Sophos XG Firewall Web UI:
- Select System > Profiles.
- Select the IPsec Profiles tab.
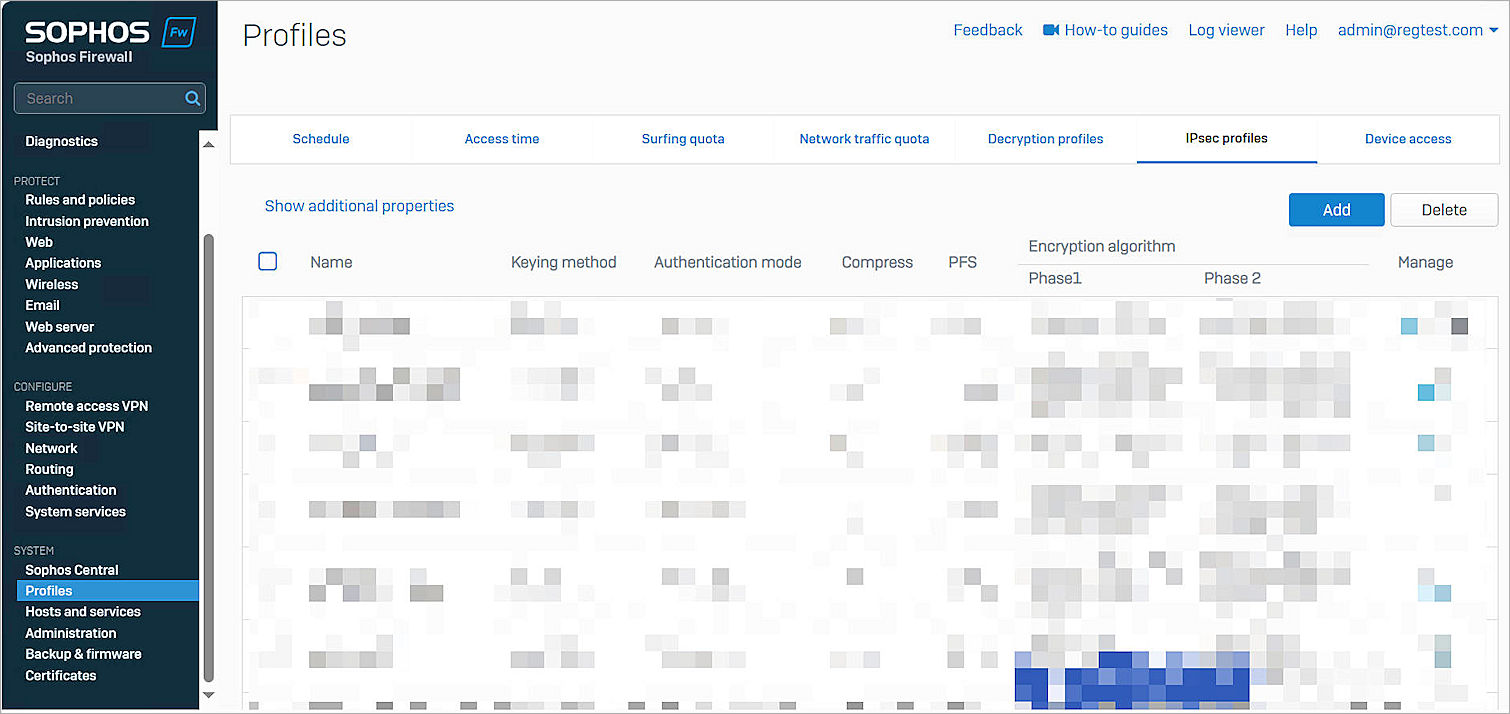
- Click Add.
The IPSec Profiles page opens.

- In the Name text box, type the object name. In our example, we use BOVPN_IKEv2.
- For Key Exchange, select IKEv2.
- Select the Re-Key Connection check box.
- From the Phase 1 section, from the DH Group (Key Group) drop-down list, select 14 (DH2048).
- Delete the other default DH groups.
- From the Phase 2 section, from the PFS group (DH group) drop-down list, select 14 (DH2048).
- Keep the default values for all other settings.
- Click Save.
IPSec VPN Connection Settings
To configure the IPSec VPN connection settings, from the Sophos XG Firewall Web UI:
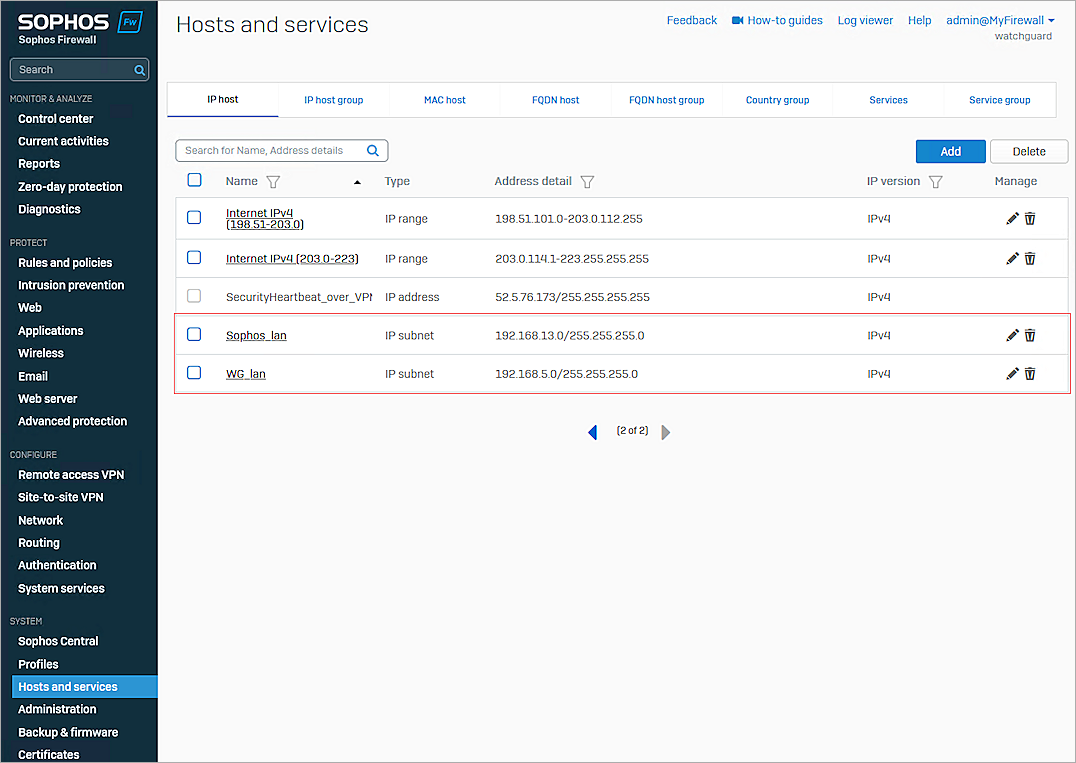
- Select System > Hosts and Services.
- Select the IP Host tab.
- Click Add.
The Add IP Host page opens.
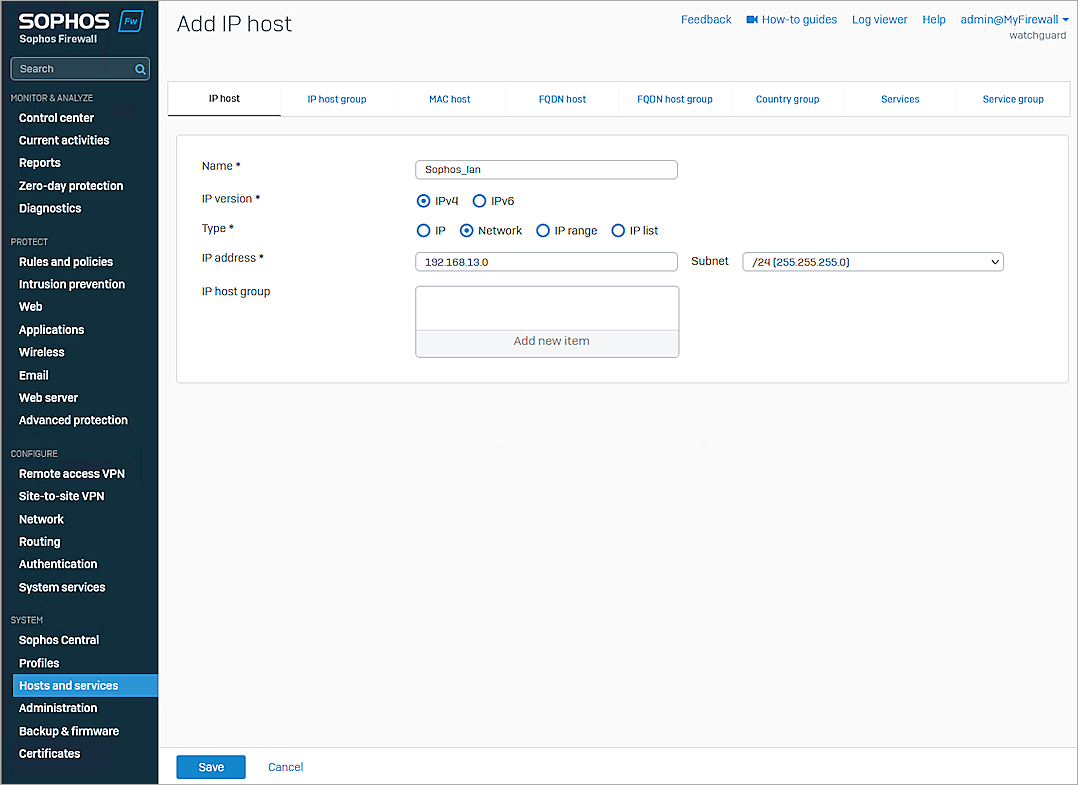
- In the Name text box, type the object name. In our example, we use Sophos_lan.
- For Type, select Network.
- In the IP Address text box, type the IP segment.
- Keep the default values for all other settings.
- Click Save.
- Repeat steps 1–8 to create another IP segment.
- Select Configure > Site-to-site VPN.
- Select the IPsec tab.
- From the IPsec Connections section, click Add.
The Site-to-Site VPN'IPsec settings page opens.
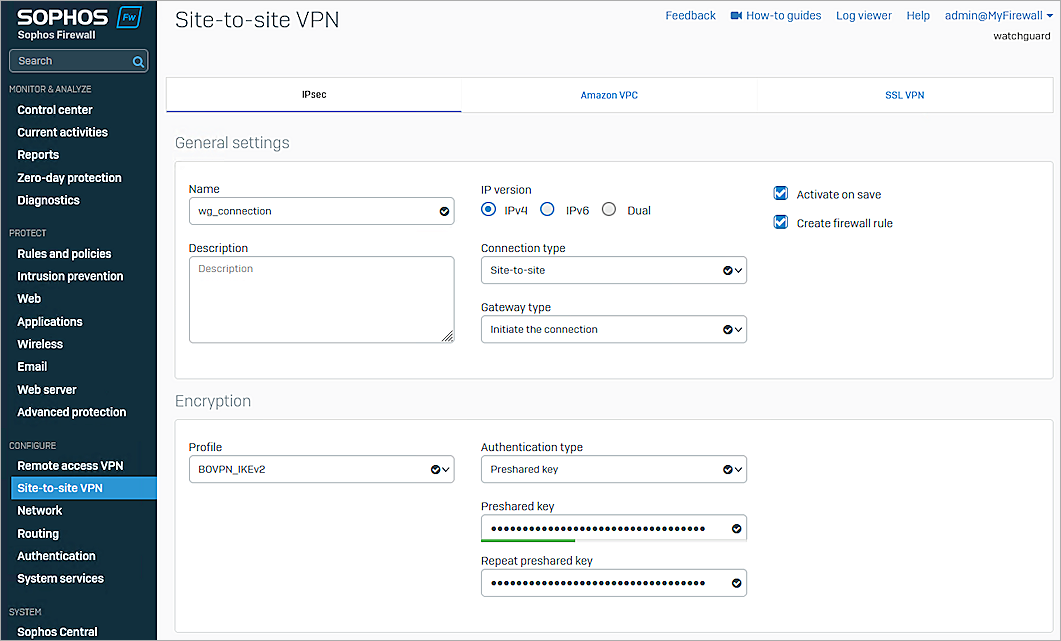
- From the General Settings section, in the Name text box, type an object name. In our example, we use wg_connection.
- From the Gateway type drop-down list, select Initiate the Connection.
- Select the Activate On Save check box.
- Keep the default values for all other General Settings.
- From the Encryption section, from the Profile drop-down list, select BOVPN_IKEv2. You create this profile in the Add IPsec Profiles section of this document.
- From the Authentication Type drop-down list, select Preshared Key.
- In the Preshared Key text box, type the pre-shared key.
- In the Repeat Preshared Key text box, type the pre-shared key again.
- From the Gateway Settings section, from the Listening Interface drop-down list, select PortB - 198.51.100.2.
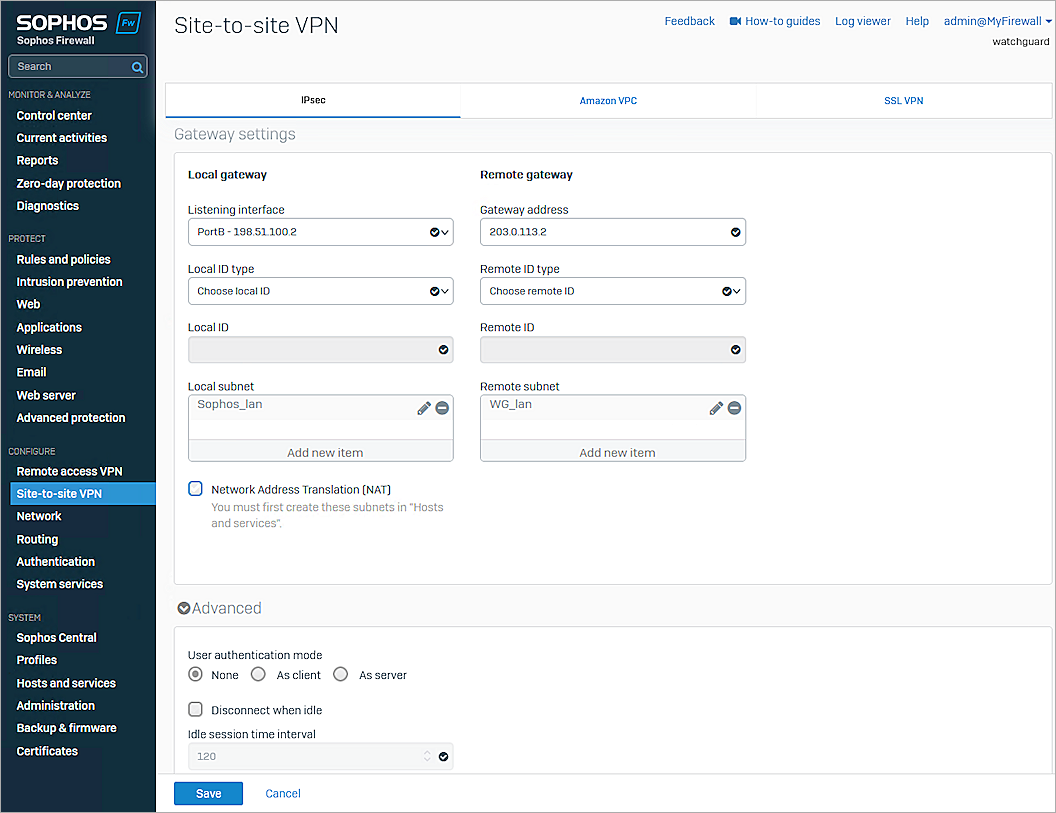
- From the Local Subnet drop-down list, select Sophos_lan.
- In the Gateway Address text box, type the WAN IP address of Firebox.
- From the Remote Subnet drop-down list, select WG_lan.
- Keep the default values for all other settings.
- Click Save.
- Click OK.
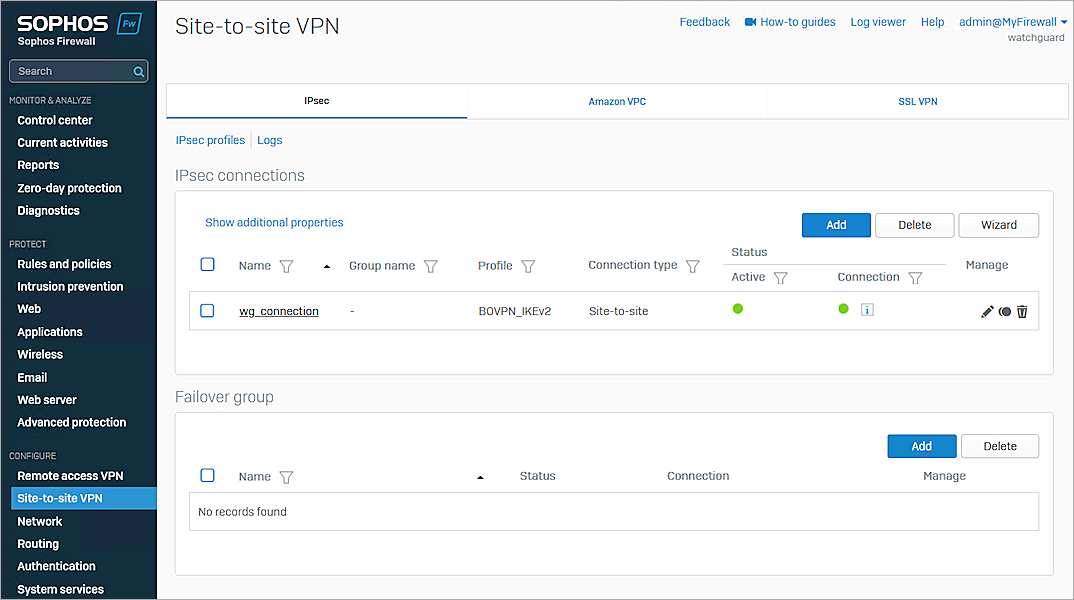
Test the Integration
To test the integration, from Fireware Web UI:
- Select System Status > VPN Statistics.
- Select the Branch Office VPN tab, then verify the VPN is established.
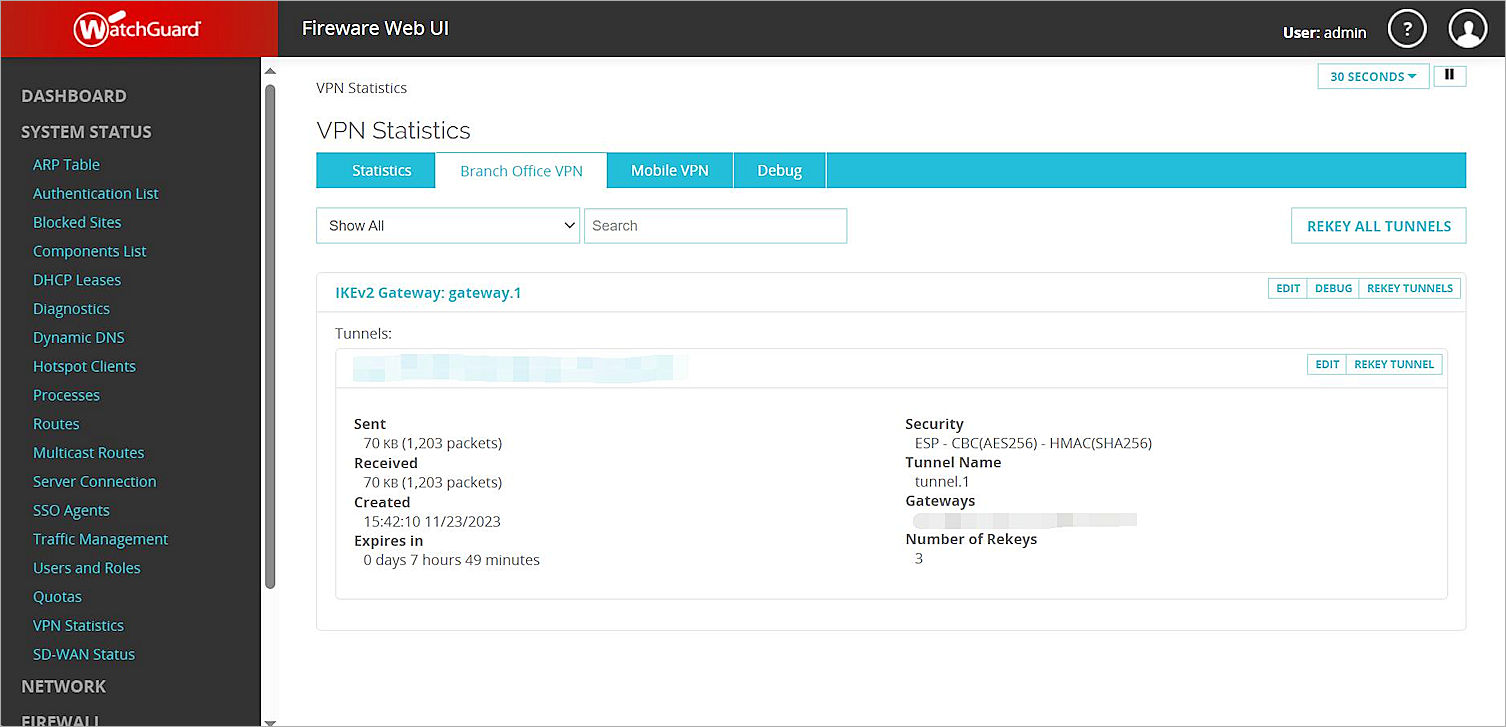
- Verify that Host1 (behind the Firebox) and Host2 (behind the Sophos XG Firewall) can ping each other.