Deployment Overview
WatchGuard provides integration instructions to help our customers configure WatchGuard products to work with products created by other organizations. If you need more information or technical support about how to configure a third-party product, see the documentation and support resources for that product.
This integration guide describes how to configure an L2TP VPN connection between a Chromebook and a locally-managed Firebox.
Integration Summary
The hardware and software used to complete the steps outlined in this document include:
- Chromebook
- Google Chrome OS Version 79.0.3945.86
- WatchGuard Firebox
- Fireware v12.7 or higher
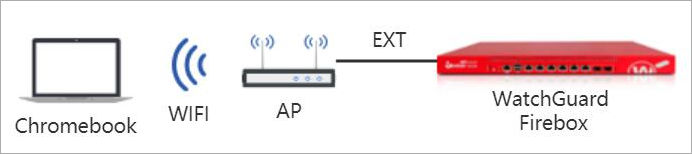
Test Topology
Configure Your Firebox for Chromebook
- Connect to the Firebox at https://<Firebox IP address>:8080.
- Log in with a user account that has administrator credentials.
- Select Authentication > Servers.
The Authentication Servers page appears. - Click Firebox-DB.
The Firebox Users and Groups page appears. - In the Firebox Groups section, click Add.
The Firebox Group dialog box appears. - In the Name text box, type a group name. In our example, we use the group name CB.
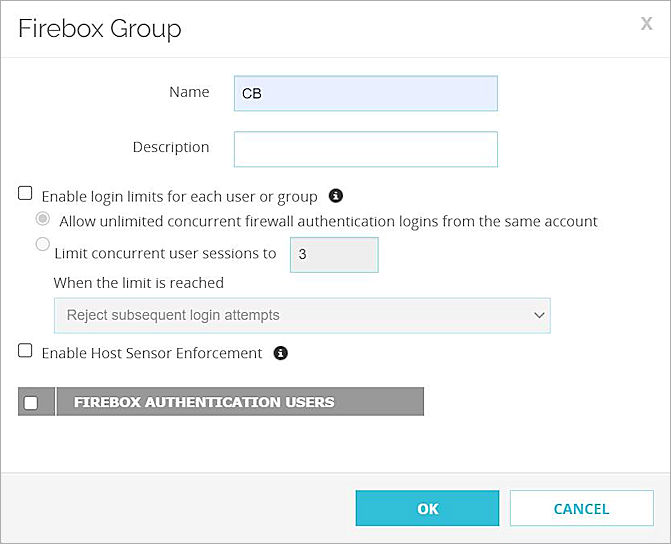
- Click OK.
- In the Firebox Users section, click Add.
The Firebox User dialog box appears. - In the Name text box, type a user name. In our example, we type the user name test.
- In the Passphrase and Confirm text boxes, type the password.
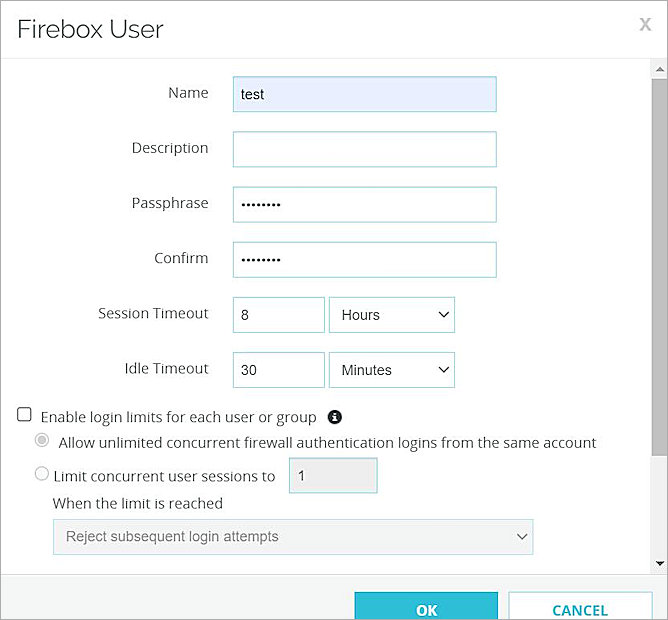
- At the bottom of the Firebox User dialog box, select the Firebox group you created. In our example, we select the group named CB.
- Keep other default settings.
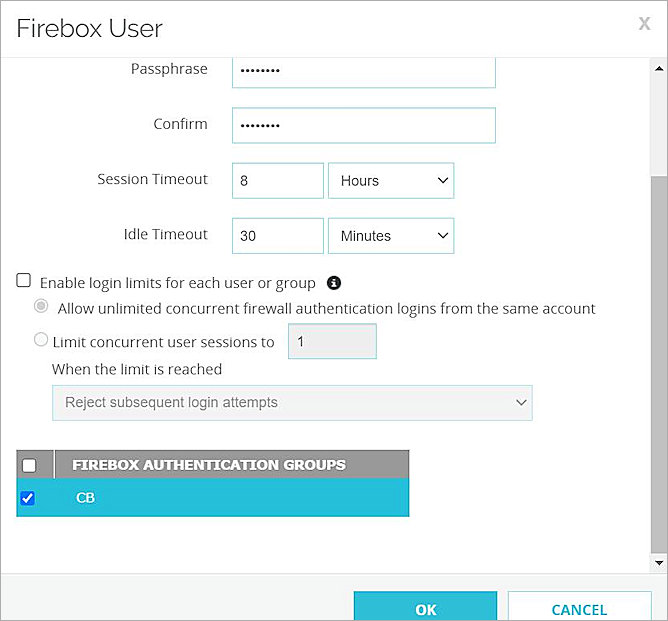
- Click OK.
- Click Save.
- Select VPN > Mobile VPN.
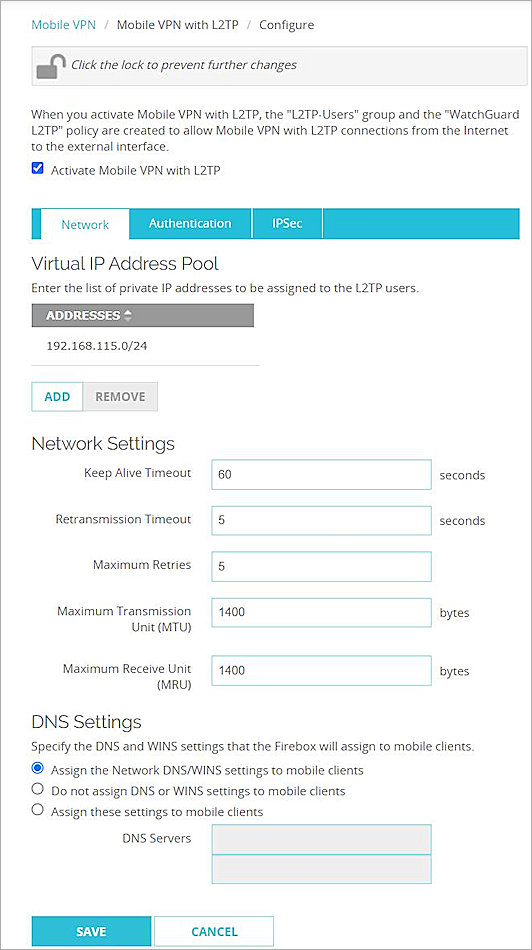
The Mobile VPN page appears. - In the L2TP section, click Manually Configure.
The Mobile VPN with L2TP configuration page appears. - Select Activate Mobile VPN with L2TP. Keep the default value for all settings.
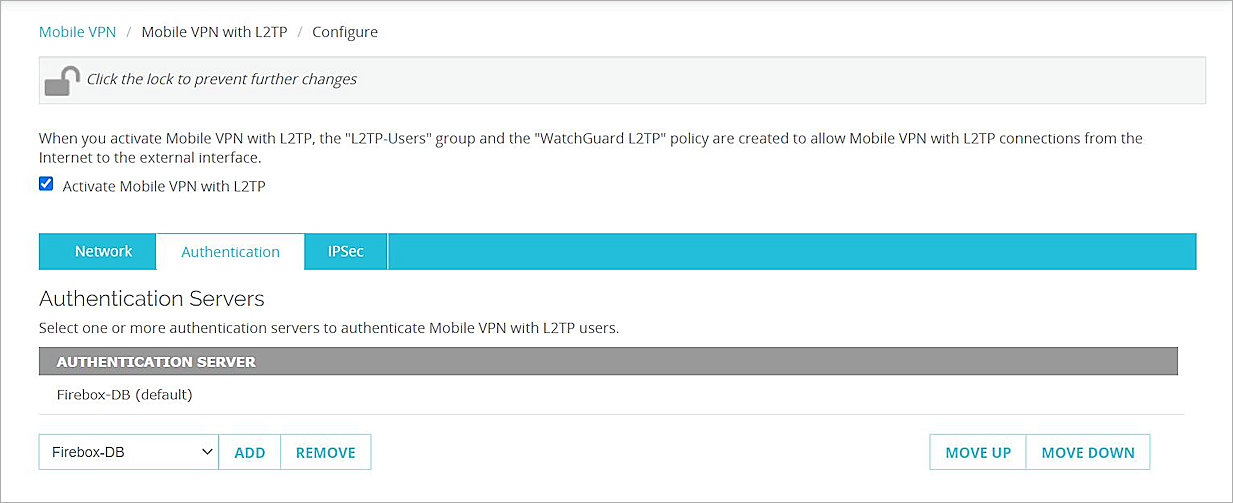
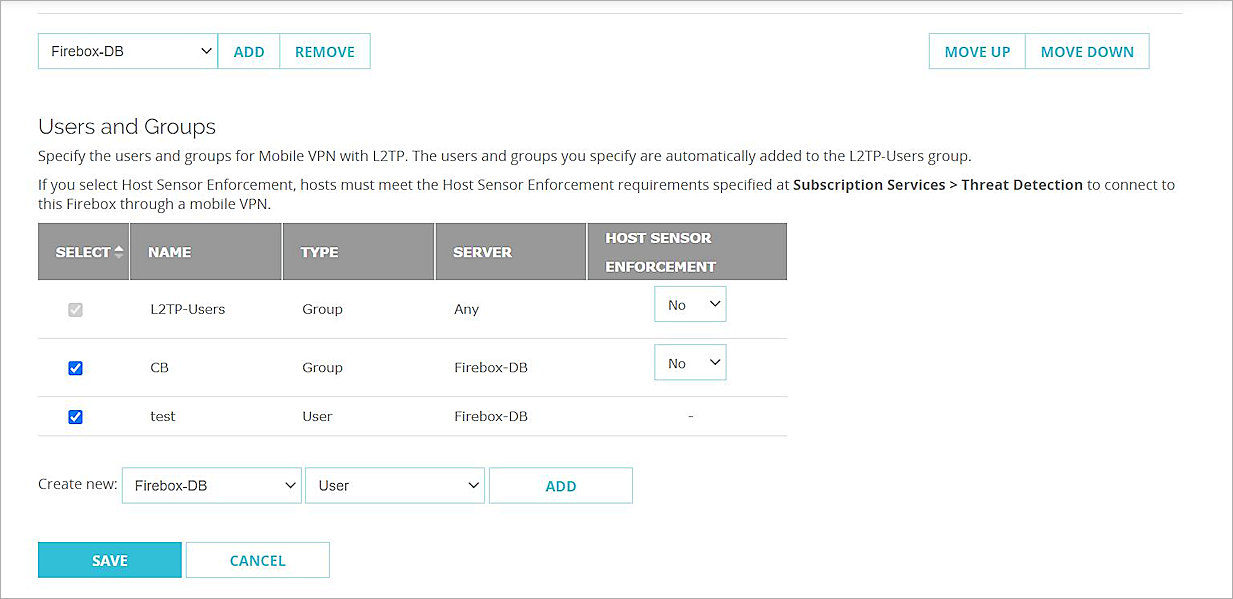
- Select the Authentication tab.
- In the Authentication Servers section, select Firebox-DB server.
- In the Users and Groups section, select the group you created. In our example, we select the group named CB.
- Select the user you created. In our example, we select the user named test.
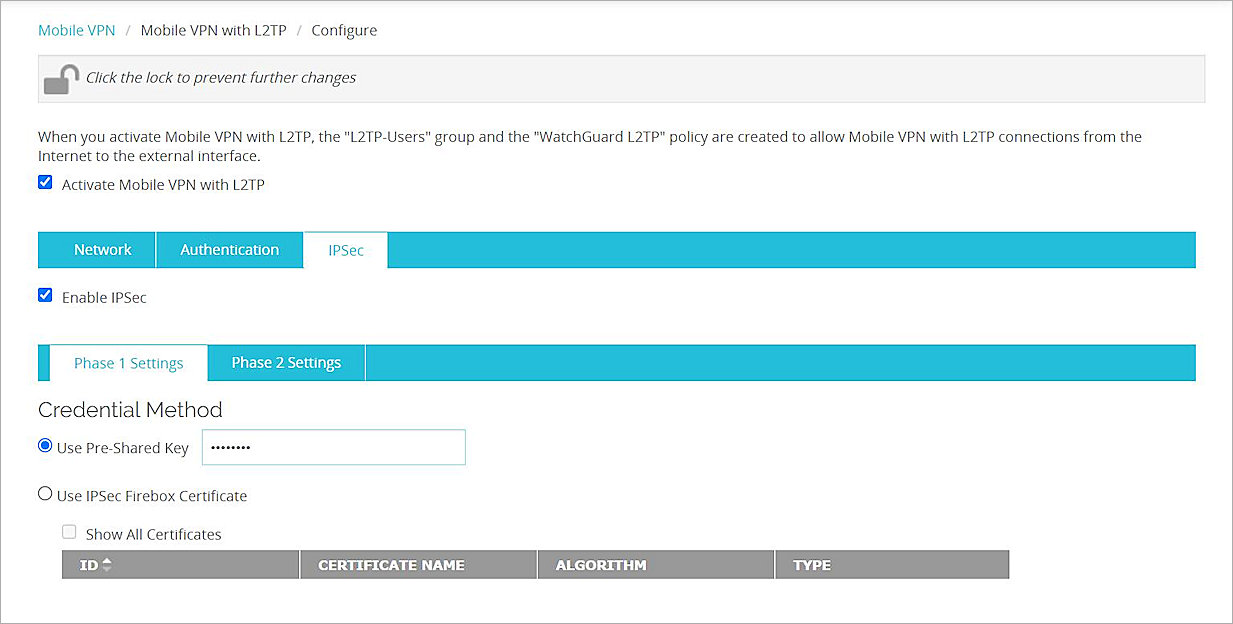
- Select the IPSec tab.
- Make sure Enable IPSec is selected.
- On the Phase 1 Settingstab, in the Credential Method section, select Use Pre-Shared Key.
- Type a pre-shared key.
- In the Transform Settings section, click Add.
The Transform Settings dialog box appears. - From the Authentication drop-down list, select SHA2-256.
- From the Encryption drop-down list, select AES (128-bit).
- From the Key Group drop-down list, select Diffie-Hellman Group 15. Keep the default value for all other settings.
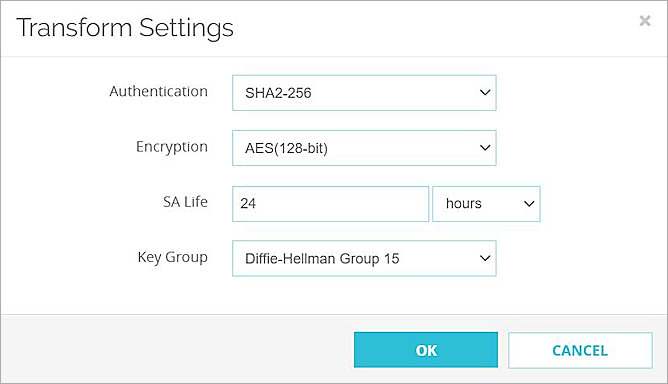
- Click OK.The transform you added appears in the transform list.
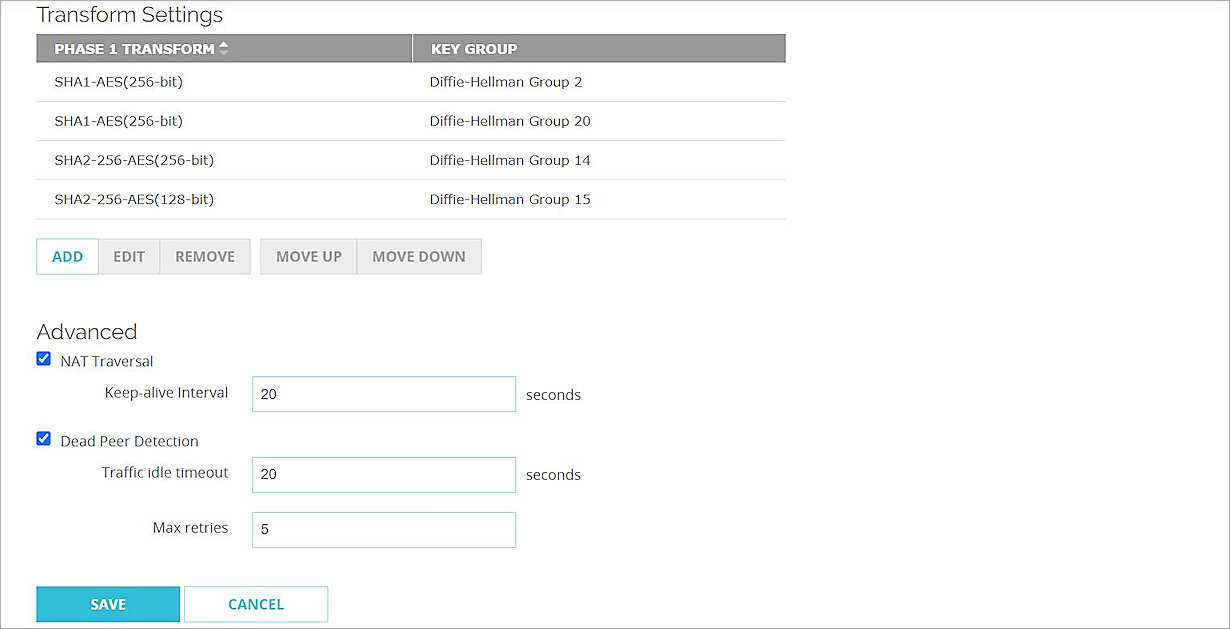
- Click Save. Keep the default value for all other settings.
- Click Save.
Configure Your Chromebook
In our example, we assume that your Chromebook is already connected to the Firebox through a Wi-Fi connection.
- At the bottom right of your desktop, select the time.
Configuration options appear.
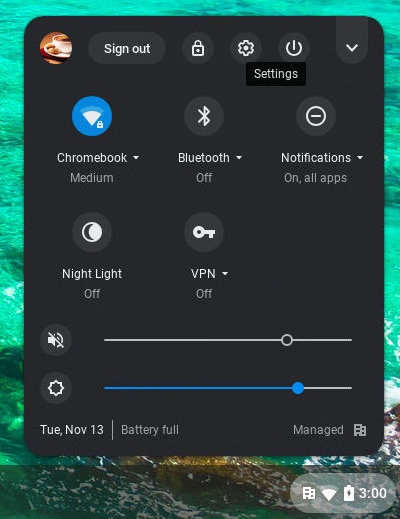
- Select Settings
 .
.
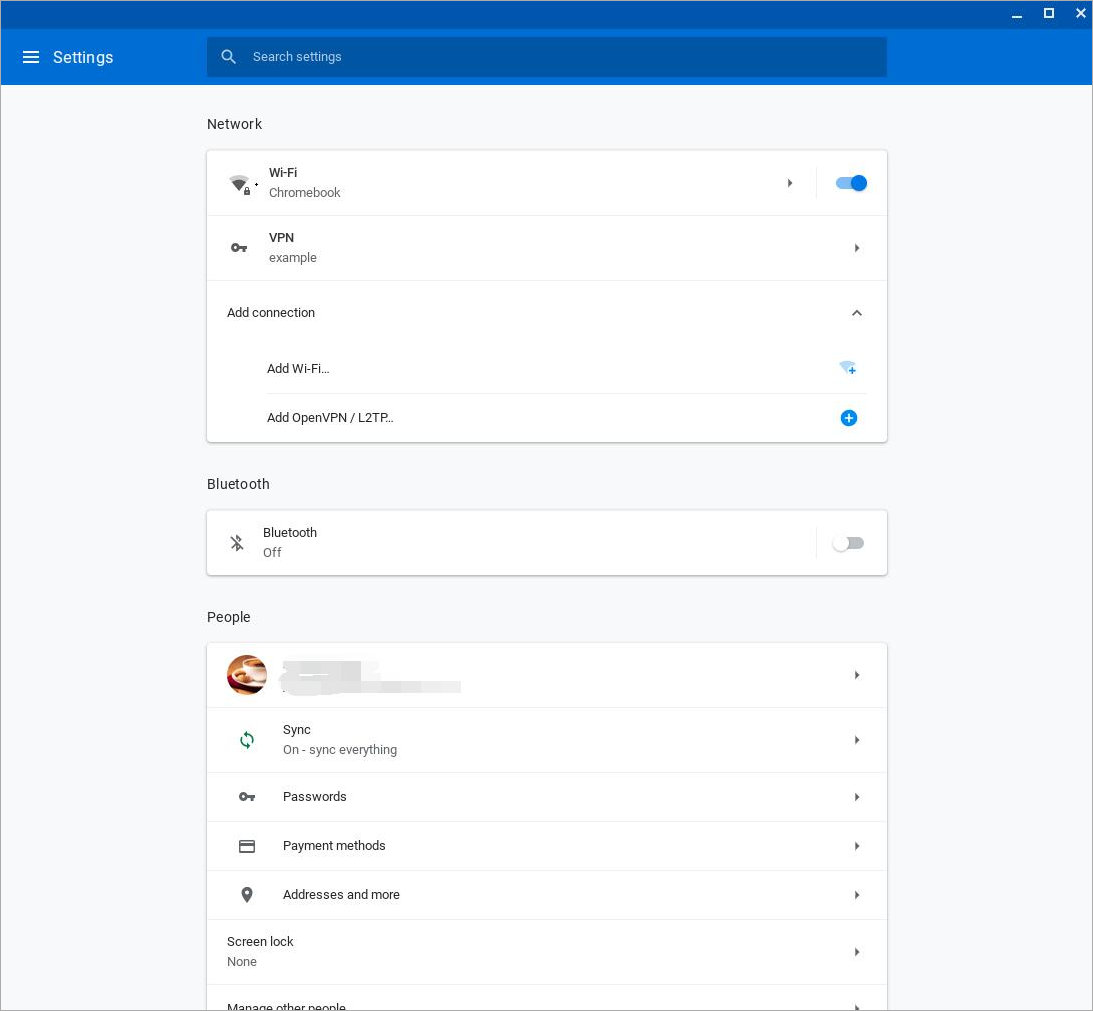
The Settings page appears.
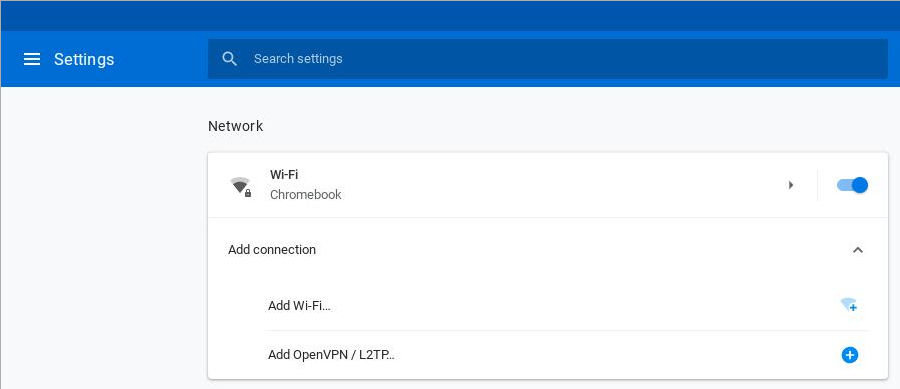
- In the Network section, expand the Add Connection section.
- Adjacent to Add OpenVPN / L2TP, click the add icon +.
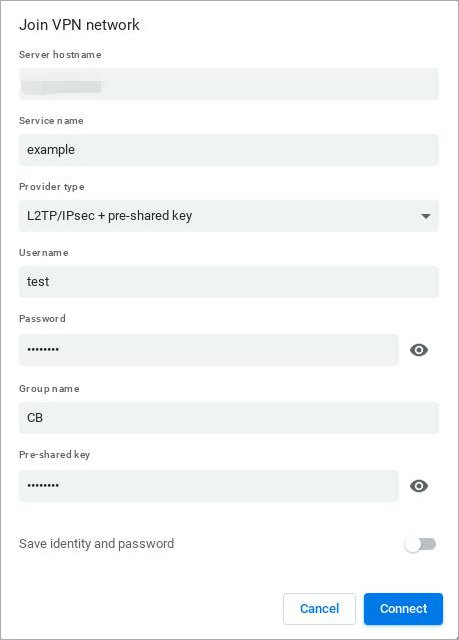
The Join VPN network page appears. - In the Server hostname text box, type the external IP address or host name of the Firebox.
- In the Service name text box, type a name for the VPN connection.
- From the Provider type drop-down list, select L2TP/IPsec + pre-shared key.
- In the Username text box, type the user name. This is the Firebox-DB user you added on the Firebox.
- In the Password text box, type the password associated with the specified user name.
- In the Group name text box, type the group name. This is the Firebox-DB group you added on the Firebox.
- In the Pre-shared key text box, type the pre-shared key. This is the pre-shared key you configured on the Firebox.
- Select the Save identity and password toggle.
- To save the configuration, click Connect.
The VPN connection is added to the Network list.
Test the Integration
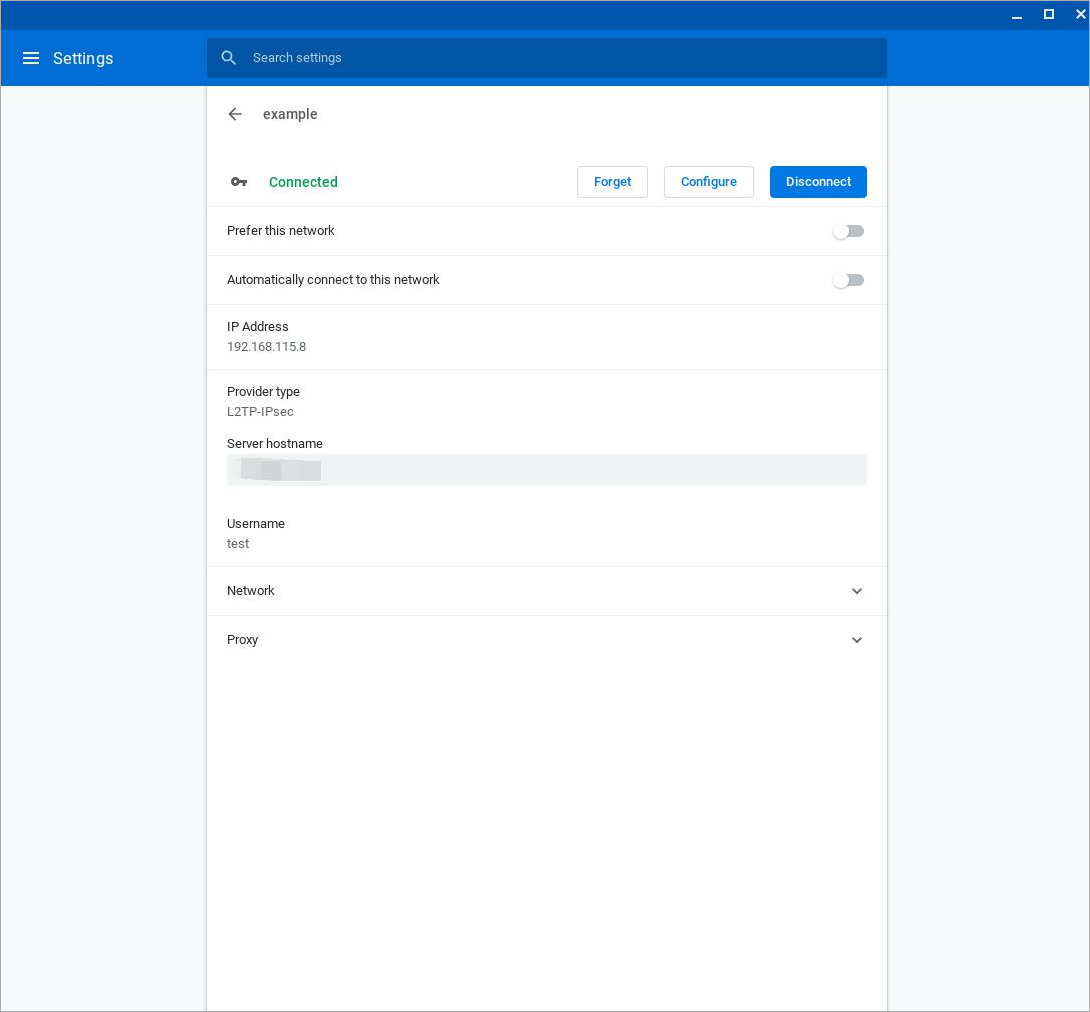
- In the Chromebook settings, from the Network list, select VPN.
- From the VPN list, select the arrow icon adjacent to the VPN connection you added.
- Click Connect. If the connection is successful, the status changes to Connected.