Applies To: ThreatSync
ThreatSync is a WatchGuard Cloud service that provides eXtended Detection and Response (XDR) technology for WatchGuard network devices (Fireboxes, access points), WatchGuard Endpoint Security products, and AuthPoint products. This service:
- Provides a user interface primarily for Incident Responders
- Displays malicious detections as incidents
- Correlates events to create new malicious detections
- Enables responders to respond on-demand or configure automated responses to malicious detections and abnormal behaviors
ThreatSync+ NDR extends the existing ThreatSync functionality in WatchGuard Cloud and offers enhanced network detection and response, network device identification, and advanced reporting for Fireboxes, third-party firewalls, and LAN infrastructure. To learn more, go to About ThreatSync+ NDR.
ThreatSync+ SaaS enables you to monitor, detect, and report on activity from third-party SaaS and cloud environments, such as Microsoft 365. To learn more, go to About ThreatSync+ Cloud Integration — Microsoft 365.
ThreatSync Licensing
ThreatSync is a WatchGuard unified security feature included with these licenses:
- Firebox Total Security Suite (TSS)
- Access Point USP Wi-Fi Management
- Endpoint Security Elite
- Endpoint Security 360
- Endpoint Security Prime
- Endpoint Detection and Response (EDR)
- Endpoint Detection and Response Core (EDR Core)
- AuthPoint Multi-Factor Authentication
- AuthPoint Total Identity Security
WatchGuard EDR Core is included in the Firebox Total Security Suite. For more information, go to WatchGuard EDR Core Features.
The more WatchGuard products you have, the more visibility and expanded features you gain access to.
Key Concepts and Terms in ThreatSync
Correlation
ThreatSync gathers security event data from multiple security products to identify and group related events into single incidents. This data correlation provides Incident Responders with a contextualized view of a threat or attack, and enables them to respond to actionable incidents. ThreatSync correlates data from these WatchGuard security products:
- Fireboxes
- Access points
- WatchGuard Endpoint Security
- Advanced Endpoint Protection Detection and Response (Advanced EPDR)
- Endpoint Protection Detection and Response (EPDR)
- Endpoint Detection and Response (EDR)
- Endpoint Detection and Response Core (EDR Core)
- AuthPoint
- AuthPoint Multi-Factor Authentication
- AuthPoint Total Identity Security
ThreatSync uses these events for correlation:
- Advanced Persistent Threats (APTs) detected in the network and found on an endpoint or Firebox
- Malware detected in the network and found on an endpoint or Firebox
- Malicious network connection correlated to an endpoint process or Firebox
- Malicious access points (Rogue, Suspected Rogue, and Evil Twin) detected by Airspace Monitoring on access points managed by WatchGuard Cloud
- Credential Access events detected by AuthPoint
Incidents
The ThreatSync management UI presents correlated events as incidents for you to review and manage. An incident is activity that is confirmed to be malicious, and can be as simple as an indicator of compromise, or as complex as an indicator of attack that sequences behaviors to determine malicious intent. For more information, go to Incident Types and Triggers in ThreatSync.
Entities of Interest
In ThreatSync, entities of interest are the unique objects related to an incident. Entities of interest can include IP addresses, URLs, files, users, endpoints, and devices. On the Incident Details page, the Entities of Interest section provides a list of the unique objects related to the incident, and the available actions for each entity. This information provides context to Incident Responders when they review and respond to incidents. For more information, go to Entities of Interest for Incidents in ThreatSync.
Signals
The ThreatSync management UI presents the events and data that combine to form an incident as signals. You can review the signals associated with an incident on the Incident Details page. For more information, go to Signals for Incidents in ThreatSync.
Signal Sources
In ThreatSync, signal source refers to the original detection point that identified a security event and sent it to ThreatSync to create the incident. ThreatSync supports these signal sources: Fireboxes, endpoints, AuthPoint, access points, and ThreatSync+.
Risk Scores and Risk Levels
ThreatSync assigns risk scores and risk levels to incidents, endpoints, and users to help Incident Responders identify issues and prioritize responses in their networks. ThreatSync calculates risk scores on a scale of 1 to 10. The higher the score, the higher the risk.
- Incident Risk Score and Level — Incident risk score indicates the severity of an incident. ThreatSync automatically assigns each incident an incident risk score on a scale and corresponding level that appears on the Monitor > Summary and Monitor > Incidents pages. For more information, go to Incident Risk Scores and Risk Levels in ThreatSync.
- Endpoint Risk Score and Level — ThreatSync automatically assigns each endpoint a risk score and corresponding risk level that appears on the Monitor > Endpoints page. ThreatSync determines the risk score for an endpoint based on the incident risk scores associated with the endpoint in the past 30 days. For more information, go to Endpoint Risk Scores and Risk Levels in ThreatSync.
- User Risk Score and Level — ThreatSync automatically assigns each user a risk score and corresponding risk level that appears on the Monitor > Users page. ThreatSync determines the risk score for a user based on the risk scores for open incidents associated with that user. For more information, go to User Risk Scores and Risk Levels in ThreatSync.
Response Actions
In ThreatSync, there are two ways to respond to incidents:
- Manual Actions Performed by a User — As you monitor threats detected by ThreatSync and review incident details, you might decide to take a manual action to respond to the incident, or to reverse an action taken automatically by a WatchGuard product or service. For example, you might block an IP address, delete a malicious file, block an access point, or isolate a computer.
When you review an incident, you can manually perform actions from various locations in the ThreatSync management UI.
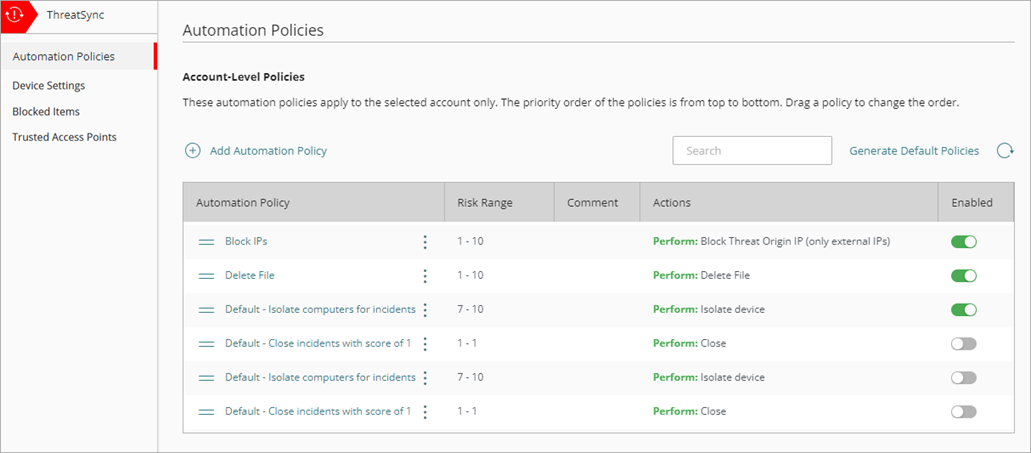
For more information, go to Perform Actions in ThreatSync. - Actions Performed Automatically by an Automation Policy — You can configure automation policies to automatically perform actions on incidents that meet the conditions you define. For example, you could create an automation policy to automatically delete files associated with a specific type of incident with a risk score of 9 or 10.
Automation policies enable Incident Responders to focus on the review of incidents that might require manual responses. Service Providers can use automation policy templates to assign multiple policies to the accounts or account groups they manage.
For more information, go to About ThreatSync Automation Policies.
ThreatSync Management UI
To configure and monitor ThreatSync, you use the ThreatSync management UI in WatchGuard Cloud. To connect to WatchGuard Cloud, go to cloud.watchguard.com and log in with your account credentials.
Configure ThreatSync
To configure ThreatSync, select Configure > ThreatSync.
Subscribers can use these pages to configure ThreatSync in WatchGuard Cloud:
- Automation Policies — On the Automation Policies page, you configure policies to automatically perform actions on specific incidents. For more information, go to About ThreatSync Automation Policies.
- Device Settings — On the Device Settings page, you can select which devices send incident data to ThreatSync. For more information, go to Configure Device Settings in ThreatSync
- Blocked Items — On the Items Blocked by ThreatSync page, from the Firebox tab, you can unblock IP addresses, and on the Access Point tab, you can unblock access point MAC addresses that were blocked by a ThreatSync action. For more information, go to Manage Items Blocked by ThreatSync.
- Trusted Access Points — On the Trusted Access Points page, you view the list of MAC addresses of access points trusted by ThreatSync. For more information, go to Configure Trusted Access Points in ThreatSync.
Service Providers can use these pages to configure ThreatSync in WatchGuard Cloud:
- Automation Policy Templates — On the Automation Policy Templates page, you can create ThreatSync automation policy templates that include multiple automation policies, and assign the template to the Subscriber accounts or account groups. For more information, go to Manage ThreatSync Automation Policy Templates (Service Providers).
- Managed Account Settings — On the Managed Account Settings page, you can select which of your managed accounts you want to view ThreatSync data for when you monitor threats in ThreatSync. You can also enable newly added managed accounts to automatically show ThreatSync data. For more information, go to Configure Managed Account Settings in ThreatSync (Service Providers).
Monitor ThreatSync
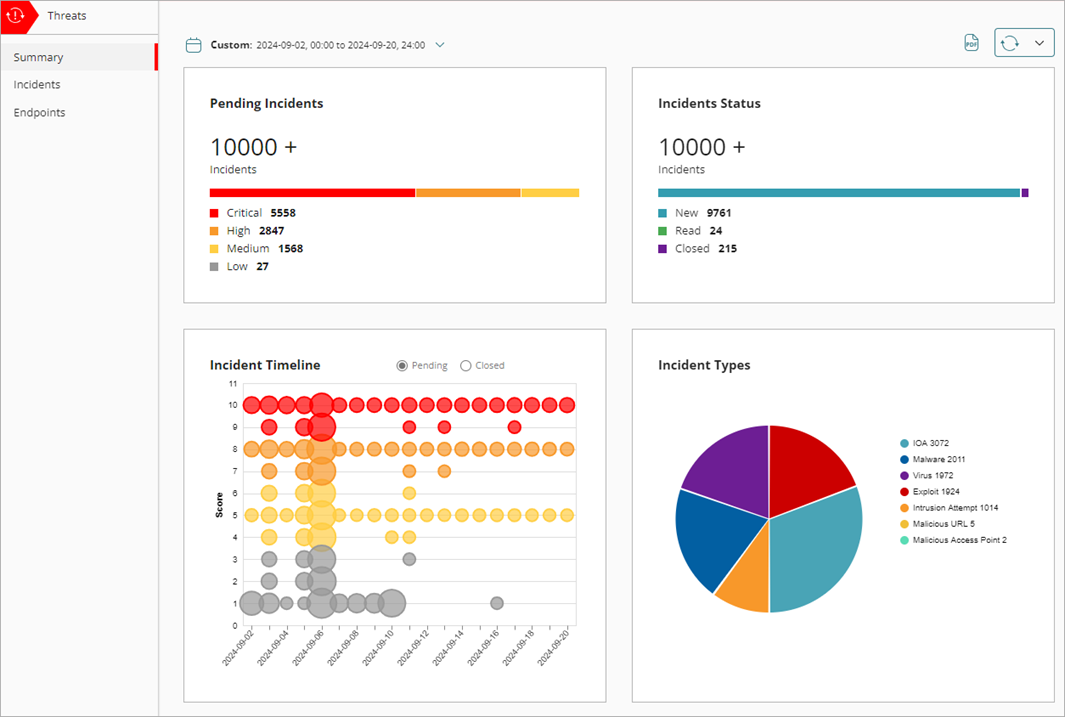
To monitor ThreatSync, select Monitor > Threats. The Summary page opens by default for both Service Providers and Subscribers.
Use these pages to monitor ThreatSync in WatchGuard Cloud:
- Summary — The Summary page provides a snapshot of incident activity for your account. For more information, go to ThreatSync Incident Summary.
- Incidents — The Incidents page shows a list of incidents for a specified time period and enables you to perform actions to remediate incidents. For more information, go to Monitor Incidents in ThreatSync.
- Endpoints — The Endpoints page provides an endpoint-based view of incident activity for a specified time period and enables you to perform actions to remediate incidents on an endpoint. For more information, go to Monitor Endpoints in ThreatSync.
- Users — The Users page provides a user-based view of incident activity for a specified time period and enables you to perform actions to remediate incidents for the user. For more information, go to Monitor Users in ThreatSync.