Applies To: WatchGuard CloudDR
Compliance with regulations and standards is crucial for businesses of all sizes for many reasons, including:
- Security and Risk Management — Compliance frameworks often outline best practices for data security, access controls, and incident response. Compliance helps mitigate security risks and protect sensitive information.
- Customer Trust — Demonstration of compliance with relevant regulations builds trust with customers who know their data is being handled responsibly. This can be a significant competitive advantage.
- Legal and Regulatory Avoidance — Non-compliance can lead to fines or legal repercussions and potentially damage your reputation.
On the Compliance page in WatchGuard CloudDR, you can manage your compliance with major frameworks, view detailed compliance checks, and monitor and automate compliance.
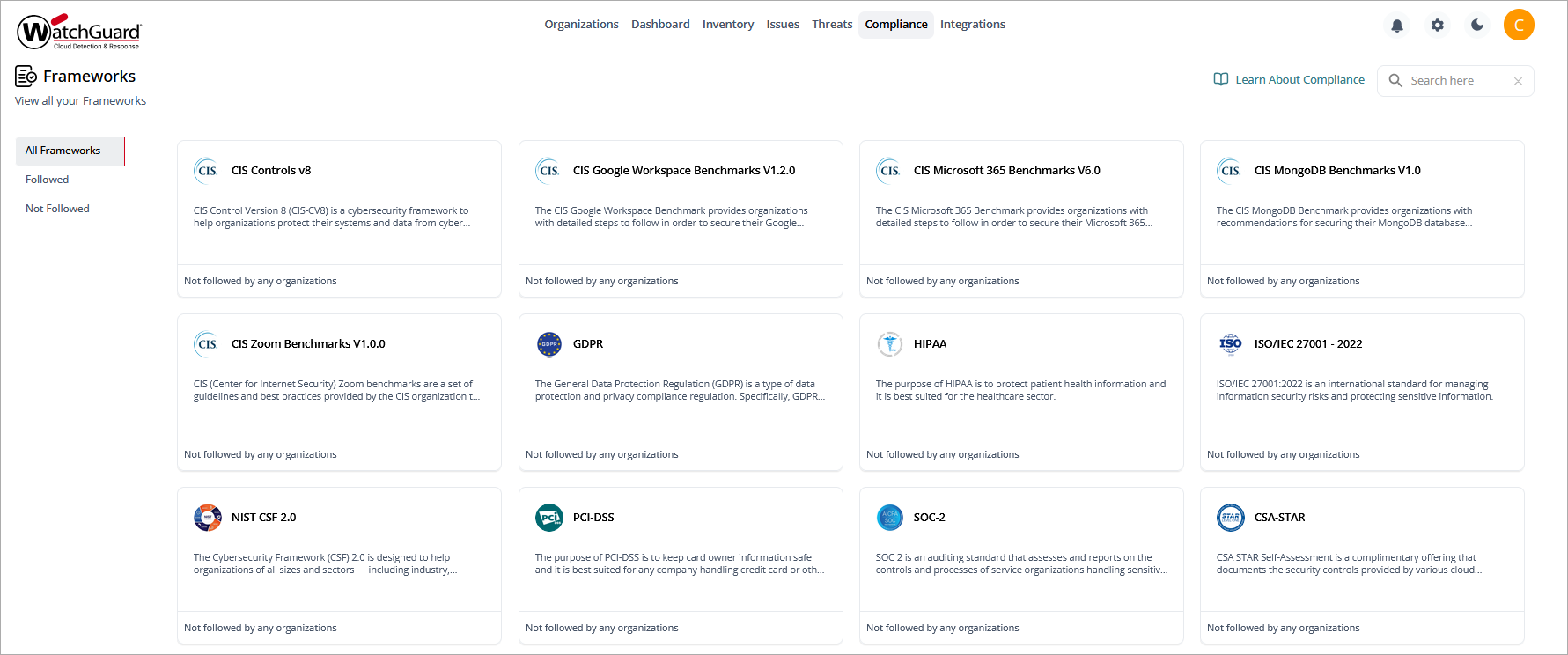
Overview > Compliance page, Service Provider view
Frameworks Supported by CloudDR
CloudDR supports these major compliance frameworks:
- CIS Controls (Center for Internet Security)
- SOC 2 (Service Organization Controls)
- HIPAA (Health Insurance Portability and Accountability Act)
- GDPR (General Data Protection Regulation)
- ISO 27001:2022 (International Organization for Standardization)
- NIST SP 800 - 53
- CSA STAR (Cloud Security Alliance Security Trust Assurance and Risk)
- PCI DSS (Payment Card Industry Data Security Standard)
- NIST CSF (National Institute of Standards and Technology Cybersecurity Framework)
CIS Controls (Center for Internet Security)
Overseeing Organization
Center for Internet Security (CIS) — Non-profit organization
Focus/Applicability
CIS controls are a recommended set of best practices for cybersecurity across various IT assets like servers, endpoints, and cloud environments. They are not official regulations but are widely adopted by organizations of all sizes.
Principles
CIS controls are based on a defense-in-depth approach, and prioritize critical security controls to mitigate the most common cyberthreats.
SOC 2 (Service Organization Controls)
Overseeing Organization
American Institute of Certified Public Accountants (AICPA)
Focus/Applicability
SOC 2 is an auditing standard for service providers that store or process customer data. It focuses on internal controls related to security, availability, integrity, confidentiality, and privacy.
Principles
SOC 2 reports come in three trust service principles (TSPs): Security, Availability, and Confidentiality (or Privacy). Organizations can select which principles to be audited for, based on their specific services and customer requirements.
HIPAA (Health Insurance Portability and Accountability Act)
Overseeing Organization
United States Department of Health and Human Services (HHS)
Focus/Applicability
HIPAA applies to healthcare providers, health plans, and healthcare clearinghouses that handle the protected health information (PHI) of individuals.
Principles
HIPAA focuses on protecting the privacy, security, and integrity of PHI. It outlines requirements for administrative, physical, and technical safeguards to achieve these goals.
GDPR (General Data Protection Regulation)
Overseeing Organization
European Union (EU)
Focus/Applicability
GDPR is a regulation that governs the processing of personal data of individuals who reside in the European Economic Area (EEA). It applies to any organization that processes this data, regardless of the location of the organization.
Principles
GDPR emphasizes individual control over personal data. It outlines principles such as transparency, accountability, and data subject rights (access, rectification, erasure, restriction of processing).
ISO 27001:2022 (International Organization for Standardization)
Overseeing Organization
International Organization for Standardization (ISO)
Focus/Applicability
ISO 27001 is an information security management system (ISMS) standard that any organization can apply, regardless of size or industry. It provides a framework for the implementation and maintenance of a comprehensive information security program.
Principles
ISO 27001 follows a risk-based approach, and requires organizations to identify information assets, assess security risks, implement controls, and continuously improve their ISMS.
NIST SP 800 - 53
Overseeing Organization
National Institute of Standards and Technology (NIST) — United States Department of Commerce.
Focus/Applicability
NIST SP 800-53 provides a catalog of security and privacy controls designed to protect information systems and organizations. It is applicable to US federal agencies, contractors, and organizations that handle government data, but it is also widely used in the private sector as a best-practice framework.
Principles
NIST SP 800-53 emphasizes a risk-based approach to cybersecurity, and organizes controls into families (such as, Access Control, Risk Assessment, Incident Response). Key principles include implementing multiple layers of security (defense-in-depth), continuous monitoring of risks and compliance, and tailoring controls to specific organizational needs (flexibility).
CSA STAR (Cloud Security Alliance Security Trust Assurance and Risk)
Overseeing Organization
Cloud Security Alliance (CSA)
Focus/Applicability
CSA STAR is a certification and assurance program designed to address cloud security. It applies to cloud service providers (CSPs) and their customers, and offers transparency and assurance of security practices in cloud environments.
Principles
CSA STAR emphasizes transparency by requiring CSPs to provide clear details about their security controls. It incorporates a three-level assurance model (self-assessment, third-party audit, and continuous monitoring), and aligns with frameworks like ISO 27001 and the Cloud Controls Matrix (CCM). Additionally, it supports organizations in the evaluation and management of cloud-related risks (risk management).
PCI DSS (Payment Card Industry Data Security Standard)
Overseeing Organization
Payment Card Industry Security Standards Council (PCI SSC)
Focus/Applicability
PCI DSS is a global standard that applies to all entities that store, process, or transmit credit card information. It is designed to protect payment card data and prevent fraud.
Principles
PCI DSS focuses on the protection of cardholder data through measures like encryption, masking, and tokenization (data protection). It emphasizes restricting access to sensitive data to authorized personnel (access control) and regularly monitoring and testing networks to detect vulnerabilities (monitoring and testing). Organizations must comply with stringent controls to make sure that they handle payment data safely (compliance enforcement).
NIST CSF (National Institute of Standards and Technology Cybersecurity Framework)
Overseeing Organization
National Institute of Standards and Technology (NIST), part of the United States Department of Commerce
Focus/Applicability
NIST CSF applies to organizations across all sectors, primarily in the United States, but is widely adopted globally. It is designed for organizations of all sizes to improve cybersecurity risk management.
Principles
NIST CSF focuses on the management and reduction of cybersecurity risk through a structured approach. It provides a risk-based framework that consists of six core functions:
- Govern – Establish and monitor cybersecurity risk management strategy, policies, and oversight.
- Identify – Understand assets, systems, data, and risks.
- Protect – Implement safeguards to limit or contain the impact of potential events.
- Detect – Develop activities to identify the occurrence of a cybersecurity event.
- Respond – Take action related to a detected cybersecurity incident.
- Recover – Restore capabilities and services impaired because of a cybersecurity event.
View and Manage Compliance in CloudDR
On the Compliance > Landscape page for a single organization, you can view available compliance frameworks and enable and disable frameworks for an organization.
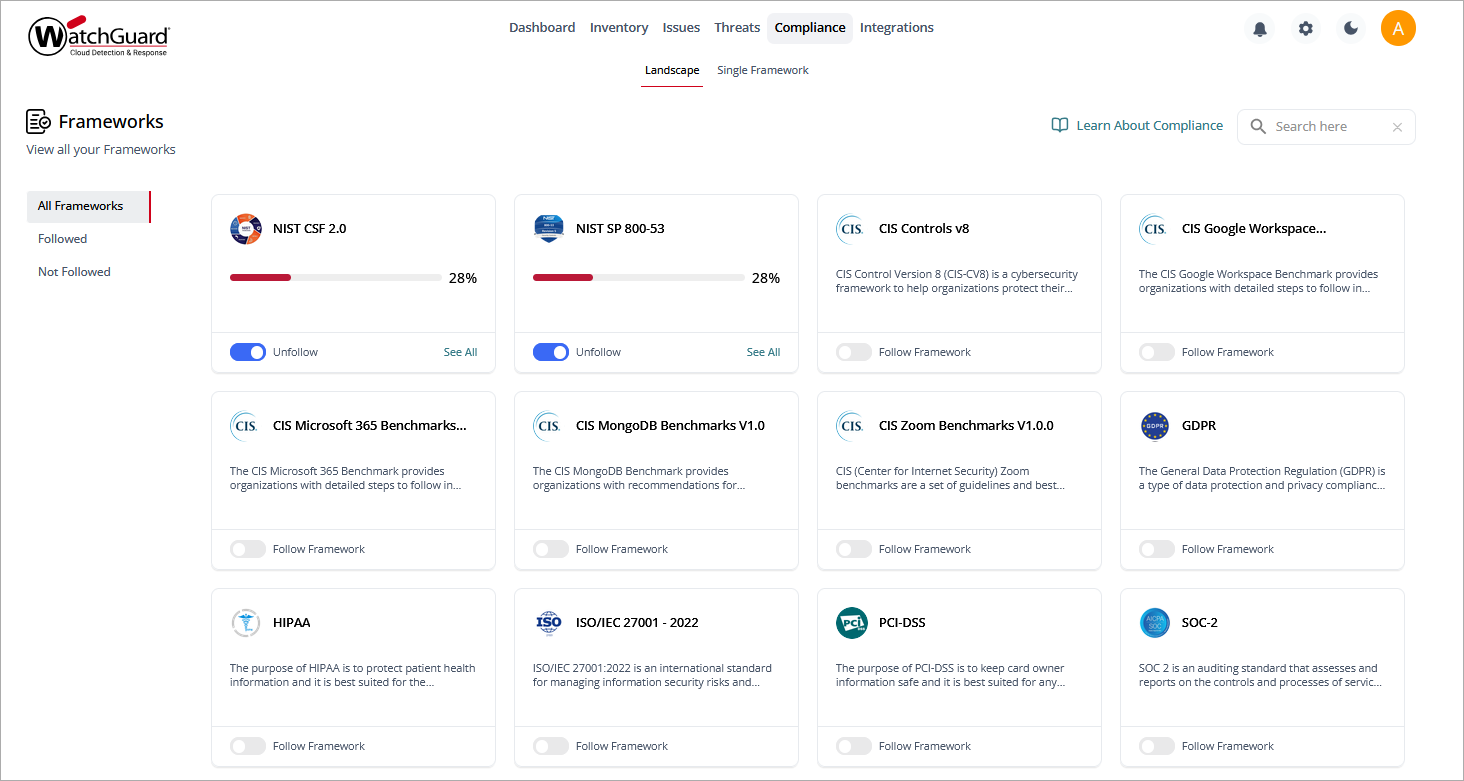
Each compliance framework has its own widget:
- To follow a compliance framework, enable Follow Framework in the relevant widget. It can take up to three minutes to calculate compliance statistics for an organization.
- To view details of a specific followed compliance framework, click See All on a widget. On the compliance details page, you can see statistics and the overall security posture score for each organization that follows that compliance framework.
Compliance Framework Details
The Compliance > Single Framework page shows detailed information about compliance checks and compliance posture for your organization.
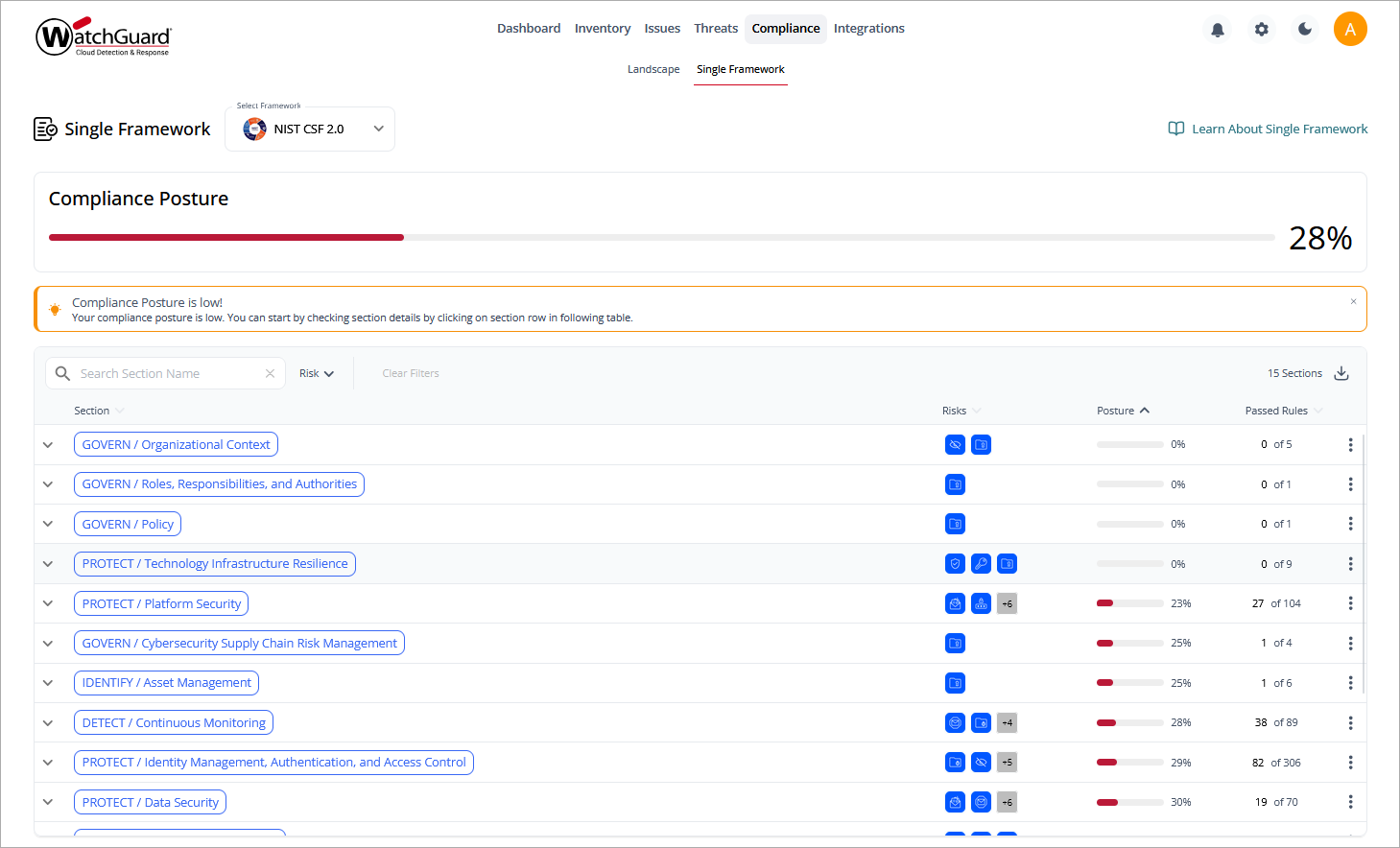
The page includes these sections:
Select Framework
Use this drop-down list to select the compliance framework you want to see details for. If you arrived at this screen after you clicked See All on a compliance framework widget, the relevant framework is automatically selected.
Compliance Posture
This section shows this information for the selected compliance framework:
- Your overall compliance posture score for the selected framework, shown as a progress bar and as a percentage.
- The total numbers of compliance checks run and compliance checks passed.
Section Information
The table shows details of all the compliance sections in the selected framework.
- To download section information, click
 and select Download as CSV or Download as PDF.
and select Download as CSV or Download as PDF. - To view controls in a section, click
 next to the section name.
next to the section name. - To view more details of a specific section or control, click
 in the relevant table row, then select View Section Details or View Control Details.
in the relevant table row, then select View Section Details or View Control Details.