
Related Topics
HTTPS-Proxy: Domain Name Rules
In an HTTPS proxy action, you can add domain name rules that specify an action to take when the server domain in the HTTPS SSL negotiation matches a specified pattern. The server domain can be included in the SNI (Server Name Indication) extension for TLS, or in the server certificate as the CN (Common Name).
You also must specify the action to take when an HTTPS request does not match a domain name rule. You can configure domain name rules to allow, inspect, deny, drop, or block HTTPS requests to a site. In an HTTPS server proxy action you can also configure a domain name rule to route inbound HTTPS requests to a specific IP address and port.
Domain Name Rule Patterns
To match the specified pattern in your domain name rules against the name in HTTPS requests to the server, you can use the SNI, the certificate common name, or the IP address of the server.
The SNI is the most accurate option. A certificate CN is often shared between several services from the same site. For example, many Google services such as YouTube and Google Maps share the same certificate CN. If you block HTTPS requests to YouTube based on the certificate CN, requests are also blocked to Google Maps and other services with the same CN. The certificate CN is used if the SNI is not available.
When you create your domain name rules, make sure to review the HTTPS entries in the traffic log messages for the correct SNI/CN information.
Domain Name Rule Actions
For each domain name rule you select the action the proxy takes for HTTPS requests where the SNI, CN, or IP address matches a specified pattern. You must also configure the action to take when no domain name rule is matched. For each rule you can select one of these actions:
- Allow — Allows the HTTPS request.
- Inspect — Uses the specified HTTP proxy action or content action to inspect content. Content inspection must be enabled in the proxy action to select the Inspect action. For information about content inspection settings, see HTTPS-Proxy: Content Inspection. For information about content actions, see About Content Actions.
- Deny — Denies the specific request but keeps the connection if possible. Sends a response to the client.
- Drop — Denies the request, drops the connection, and sends a response to the client.
- Block — Denies the request, drops the connection, blocks the site, and sends a response to the client. All traffic from this site's IP address is denied for the amount of time you specify in the Blocked Sites configuration. For more information about blocked sites, see About Blocked Sites.
For an HTTPS server proxy action when you select the Allow or Inspect action in a domain name rule, you can configure a routing action and port to send the request to a different destination than what is specified in the policy To list. This enables the Firebox to route incoming HTTPS requests to the same public IP address to different internal IP addresses or ports based on the pattern in the HTTPS header.
If you select the Inspect action with a content action, you can configure rules in the content action to route the request to a server based on the content of the decrypted HTTP request. You can also enable TLS/SSL offloading. For more information, see Configure HTTP Content Actions.
Domain Names Rule Examples
The pattern in a domain name rule can match a top level domain. In a domain name rule you specify only a domain name, not a path.
To deny traffic from any site in the example.com domain, add a domain name rule with the pattern *.example.com and set the If matched action to Deny.
To block a connection to the example.com domain, add a domain name rule with the pattern *.example.com and set the If matched action to Block. In this case, the server IP address associated with example.com is blocked for the default time duration of your Blocked Sites configuration. For more information on blocked sites, see About Blocked Sites.
To allow a connection without content inspection for any site in the example.com domain, add a domain name rule with the pattern *.example.com and set the If matched action to Allow. When you specify a domain in a domain name rule, do not include any characters after the domain name. For example, *.example.com/ is not a valid domain name.
To perform content inspection for any site in the example.com domain, add a Domain Names rule with the pattern *.example.com and set the action to Inspect. When you select the Inspect action, you must select an HTTP proxy or HTTP content action to use for inspection.
You must enable content inspection and configure Domain Names rules with the Inspect action, or use the Inspect action with a WebBlocker category for content inspection to occur.
For an example of how to configure domain name rules in an HTTPS-Server proxy action with and without content inspection see:
- Example: HTTPS Proxy Action with Domain Name Rules
- Example: HTTPS Proxy Action with an HTTP Content Action
Add Domain Name Rules
Before you can configure a domain name rule with the Inspect action, you must enable Content Inspection in the proxy action. For more information, see HTTPS-Proxy: Content Inspection.
- In the HTTPS proxy action configuration, select Content Inspection.
The Content Inspection Summary and Domain Names settings appear.
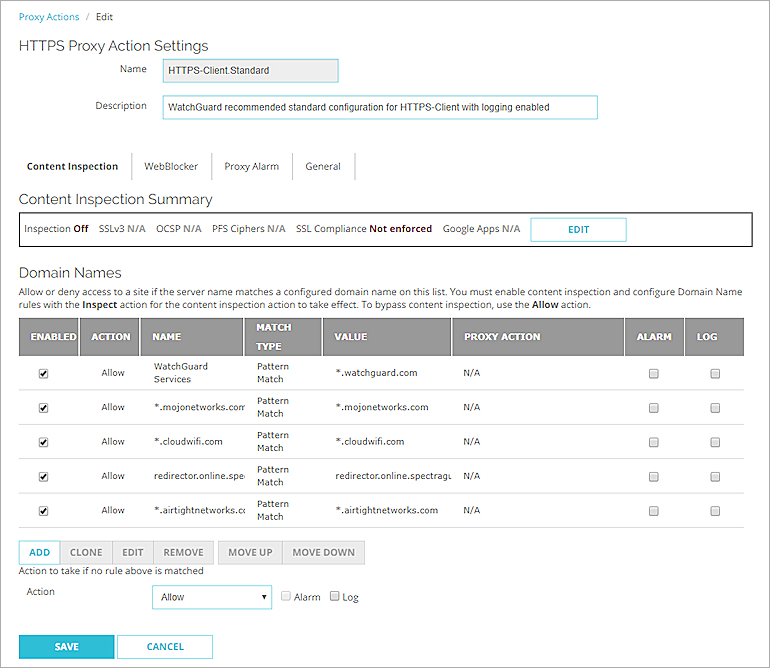
- Below the Domain Names list, click Add.
The New Domain Name Rule dialog box appears.
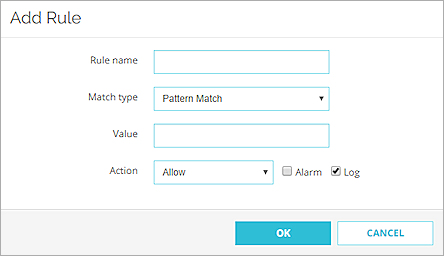
- In the Rule Name text box type a name to identify this rule.
- From the Match Type drop-down list, select one of these options to match with HTTPS requests:
- Exact Match — Specify an exact domain name.
- Pattern Match — Specify a pattern to match a domain name.
- IPv4 Address — Specify an IP address.
- Regular Expression — Specify a pattern as a regular expression.
- In the Value text box, type the text to match for this rule. If you selected Pattern Match as the rule setting, use an asterisk (*), a period (.), or a question mark (?) as wildcard characters.
- From the Action drop-down list, select the action the proxy takes for this rule.
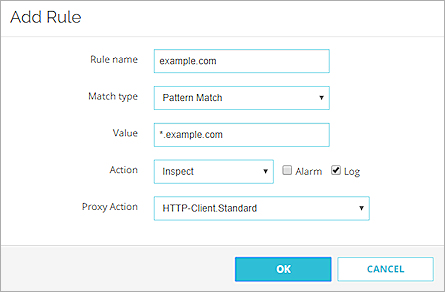
- If you select the Inspect action, select the proxy or content action to use for inspection. The HTTPS proxy uses the selected action to inspect the decrypted HTTPS request.
- In an HTTP client proxy action, from the Proxy Action drop-down list, select an HTTP proxy action to use for inspection.
- In an HTTP server proxy action, from the Proxy Action or Content Action drop-down list, select an HTTP proxy action or a content action to use for inspection and routing. For more information about content actions, see About Content Actions.
- To create a message for this event in the traffic log, select the Log check box.
- To create an alarm for this event, select the Alarm check box. An alarm tells users when a proxy rule applies to network traffic.
- If applicable, configure the Routing Action and Port, as described in the next section.
- Click OK.
The domain name rule is added to the Domain Names list.
- In the HTTPS proxy action configuration, select Content Inspection.
The Content Inspection Summary and Domain Names settings appear.
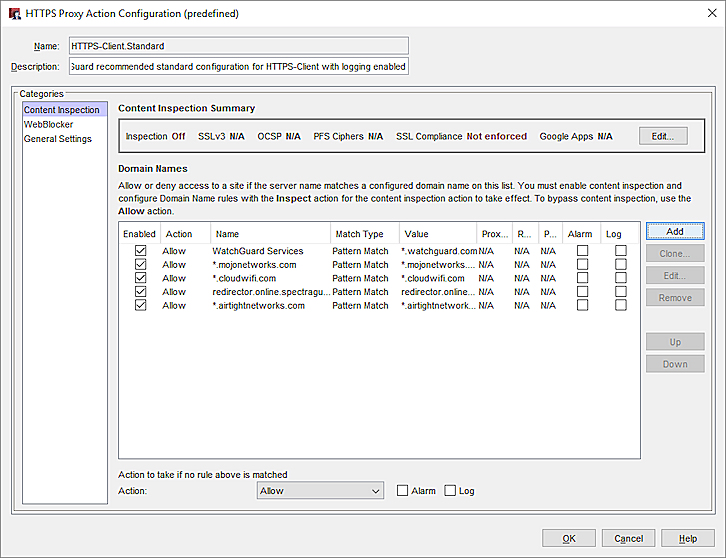
- In the Domain Names section, click Add.
The New Domain Name Rule dialog box appears.
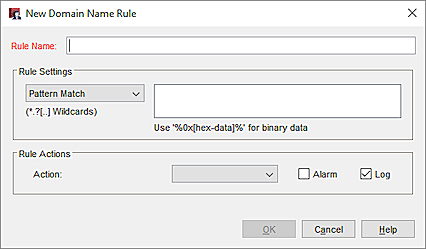
- In the Rule Name text box type a name to identify this rule.
- In the Rule Settings section, select one of these options to match with HTTPS requests:
- Exact Match — Specify an exact domain name.
- Pattern Match — Specify a pattern to match a domain name.
- IPv4 Address — Specify an IP address.
- Regular Expression — Specify a pattern as a regular expression.
- In the adjacent text box, type the text to match for this rule. If you selected Pattern Match as the rule setting, use an asterisk (*), a period (.), or a question mark (?) as wildcard characters.
- From the Action drop-down list, select the action the proxy takes for this rule.
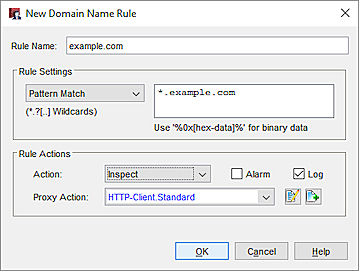
- If you select the Inspect action, select the proxy or content action to use for inspection. The HTTPS proxy uses the selected action to inspect the decrypted HTTPS request.
- In an HTTP client proxy action, from the Proxy Action drop-down list, select an HTTP proxy action to use for inspection.
- In an HTTP server proxy action, from the Proxy Action or Content Action drop-down list, select an HTTP proxy action or a content action to use for inspection and routing. For more information about content actions, see About Content Actions.
- To create a message for this event in the traffic log, select the Log check box.
- To create an alarm for this event, select the Alarm check box. An alarm tells users when a proxy rule applies to network traffic.
- If applicable, configure the Routing Action and Port, as described in the next section.
- Click OK.
The domain name rule is added to the Domain Names list.
- In the Action to take if no rule above is matched settings, from the Action drop-down list, select the action.
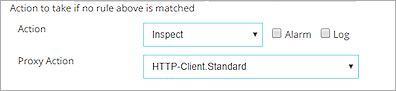
Action to take if no rule above is matched for an HTTPS client proxy action in Fireware Web UI
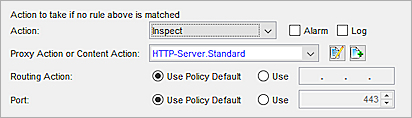
Action to take if no rule above is matched for an HTTPS server proxy action in Policy Manager
- If you select the Inspect action, select the proxy or content action to use for inspection. The HTTPS proxy uses the selected action to inspect the decrypted HTTPS request.
- In an HTTP client proxy action, from the Proxy Action drop-down list, select an HTTP proxy action to use for inspection.
- In an HTTP server proxy action, from the Proxy Action or Content Action drop-down list, select an HTTP proxy action or a content action to use for inspection and routing. For more information about content actions, see About Content Actions.
- To create a message for this event in the traffic log, select the Log check box.
- To create an alarm for this event, select the Alarm check box. An alarm tells users when a proxy rule applies to network traffic.
- If applicable, configure the Routing Action and Port, as described in the next section.
Routing Actions and Content Actions
In an HTTPS server proxy action you can use a routing action or content action to redirect inbound HTTPS requests to a specific server or port based on the domain or IP address of the request.
To use a routing action to redirect inbound HTTPS requests:
- In an HTTPS server proxy action, add or edit a domain name rule.
- In the domain name rule, select the Allow or Inspect action.
The Routing Action and Port settings appear.
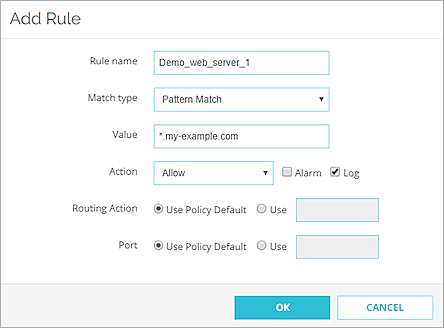
A domain name rule with routing action settings for an HTTPS server proxy action in Fireware Web UI
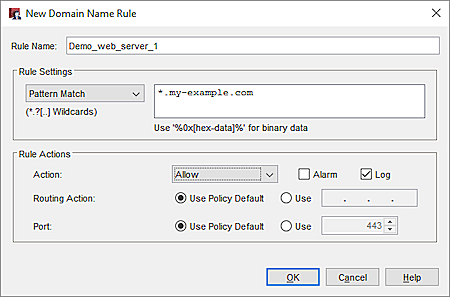
A domain name rule with routing action settings for an HTTPS server proxy action in Policy Manager
- To specify a destination IP address, in the Routing Action settings, select Use. In the adjacent text box, specify the IP address of the internal server.
- To specify a destination port, in the Port settings, select Use. In the adjacent text box specify the port number.
If content inspection is enabled, you can use a content action to implement host header redirect. With a content action, you can configure routing actions for each internal server and you can enable TLS/SSL Offload as part of a rule action. For more information, see Use an HTTP Content Action for TLS/SSL Offloading.
- In the domain name rule select the Inspect action.
- From the Proxy Action or Content Action drop-down list, select or add a content action.
- In the content action, add content action rules with routing actions for each internal server. For more information, see About Content Actions.
Domain Names and WebBlocker
For an HTTPS client proxy action you can select a WebBlocker configuration to allow, deny, or inspect website content based on the WebBlocker category.
The WebBlocker configuration you specify in the HTTPS proxy action is used only when the HTTP request does not match a domain rule, and the action to take if no rule is matched is Allow.
If the action in a domain name rule is set to Inspect, the WebBlocker action configured in the HTTP proxy action is used.
For more information about WebBlocker, see HTTPS-Proxy: WebBlocker.
Domain Names and Content Inspection Exceptions
Domain name rules take higher precedence than any match in the Predefined Content Inspection Exceptions list.
If a domain name rule is matched, the action from that rule will always be applied.
For more information about the predefined content exceptions list, see HTTPS-Proxy: Content Inspection.
Domain Names Rules Order
Domain names rules are processed in the rule order listed if multiple rules match for a domain. To change the order of precedence, select a rule, then use the Move Up or Move Down buttons.