Applies To: Locally-managed Fireboxes
Device feedback helps WatchGuard to troubleshoot and secure our services, assess the threat landscape, and comply with our legal obligations (such as export control rules). It is also used to improve our products and features. It can include information about how your Firebox is used and issues you encounter with your Firebox, but does not include any information about your company or any company data that is sent through the Firebox. Because of this, device feedback is technical in nature and mainly consists of non-identifiable information. All device feedback that the Firebox sends to WatchGuard is encrypted.
The Firebox sends three types of device feedback data to WatchGuard:
Basic Device Feedback
Your Firebox sends this basic device feedback data to WatchGuard each time the device reboots:
- Firebox serial number
- Firebox device model
- IP address
- Country
- Fireware version
- Fireware build number
- Firebox uptime since the last restart
- Hash of the device MAC address
- Whether advanced device feedback is enabled (Fireware v12.4 or higher)
- Trusted Platform Module (TPM) public key data (Fireware v12.11.3 or higher)
You cannot disable basic device feedback. If you clear the Send Advanced Device Feedback to WatchGuard check box, the Firebox continues to send basic device feedback data to WatchGuard.
Firebox Cloud devices do not send basic device feedback data to WatchGuard unless advanced device feedback is enabled.
Advanced Device Feedback (Optional)
When you create a new configuration file for your Firebox, your Firebox is configured to send advanced device feedback to WatchGuard.
If you do not want to send advanced device feedback to WatchGuard, you can disable it at any time. To disable advanced device feedback on your Firebox, clear the Send Advanced Device Feedback to WatchGuard check box.

When the Send Advanced Device Feedback to WatchGuard check box is enabled, the Firebox sends advanced feedback data to WatchGuard in a compressed file once every six days and each time the device reboots. To conserve space on the Firebox, the advanced feedback data is removed from the Firebox after it is sent to WatchGuard.
Advanced device feedback data includes the following information:
- Information listed in the Basic Device Feedback section
- Start and end time stamps for the feedback data sent to WatchGuard
- Count of policies
- Number of enabled interfaces
- Number of VLANs
- Configuration file size
- Maximum number of concurrent sessions
- Maximum number of proxy connections
- Maximum CPU usage
- Maximum memory usage
- Whether the Firebox is under Centralized Management and the management mode for the Firebox
- Number of Access Points (AP) configured on the Firebox
- Authentication options configured on the Firebox
- Whether the Firebox is a member of a FireCluster and in Active/Active or Active/Passive mode
- Whether VoIP security feature is enabled
- Whether Intrusion Prevention Service (IPS) is enabled
- Logging options configured on the Firebox
- Number of proxy actions with Subscription Services enabled in the configuration, and number of connections handled by the proxy actions
For each service, the details include whether the service is enabled and counts of the number of events for each service enabled on the Firebox.
- APT Blocker
- Data Loss Prevention (DLP)
- Default Threat Protection
- File Exceptions
- Gateway AntiVirus
- IntelligentAV
- Intrusion Prevention Service (IPS)
- Reputation Enabled Defense (RED)
- spamBlocker
- WebBlocker
- Whether the Gateway Wireless Controller is enabled
- Number of access point devices configured on the Firebox
- Number of SSIDs configured on the Firebox
- Whether the Wireless Hotspot is enabled
- Access point license status details (Fireware 12.5.1 and higher)
- Whether Access Portal is enabled
- Maximum number of users signed in
- Maximum number of RDP connections launched by users
- Maximum number of SSH connections launched by users
- Identity provider (IdP) metadata (when SAML authentication is enabled)
- Whether reverse proxy is enabled
- Whether Active Directory single sign-on is enabled
- Number of SSO agents
- SSO agent details (IP address, version, description, last connection time, and connection status)
- Whether AuthPoint is enabled (cloud-managed devices)
- Whether Mobile VPN with SSL is enabled and uses AuthPoint as an authentication domain
- Whether Mobile VPN with IKEv2 is enabled and uses AuthPoint as an authentication domain
- Whether Autotask is enabled
- Number of successful and unsuccessful attempts to save a backup image to the Firebox, a USB Drive, and a computer.
- Number of successful and unsuccessful attempts to restore a backup image from the Firebox, a USB Drive, and a computer.
- Whether the Firebox has ever been reset to factory-defaults.
- Whether Botnet Detection is enabled
- How many traffic source addresses have been tested
- How many traffic source addresses were from botnets and were dropped
- How many traffic destination addresses were tested
- How many traffic destination addresses that were sent to botnets were dropped
- Whether Connectwise is enabled
- How much data is written to the Firebox storage
- Whether DNS forwarding is enabled
- Number of DNS forwarding rules defined
- Whether DNSWatch is enabled
- Whether dynamic routing is enabled on a firewall for a specific dynamic routing protocol
- Whether dynamic routing is enabled for Routing Information Protocol (RIP)
- Whether dynamic routing is enabled for Routing Information Protocol Next Generation (RIPng)
- Whether dynamic routing is enabled for Open Shortest Path First (OSPF) protocol
- Whether dynamic routing is enabled for Border Gateway Protocol (BGP)
- Whether dynamic routing is enabled for Open Shortest Path First protocol version 3 (OSPFv3)
- Whether Endpoint Policy is enabled
- Number of connected endpoints
- Number of connected Android devices
- Number of connected iOS devices
- Number of connected devices that use VPN
- Whether TDR is enabled
- Whether network access enforcement is enabled
- Whether FQDN is used in the configuration
- Number of FQDNs configured
- Number of FQDNs that use specific domain names
- Number of wildcard domain names configured in the system
- Number of times FQDNs are used in the From or To field of a policy
- Number of FQDNs configured in the Blocked Sites list
- Number of FQDNs configured in the Blocked Sites Exceptions list
- Number of FQDNs configured in quota exceptions
- Number of policies that have FQDNs in the From or To fields
- Whether an FQDN is configured in at least one static NAT object that is used by a policy
- Number of policies configured with FQDN static NAT
- Number of FQDNs configured in static NAT objects that are used by policies
- Number of sanctioned DNS servers are in use
- Whether Geolocation is enabled
- Number of Geolocation actions configured
- Number of source and destination IP addresses checked against the Geolocation database
- Number of source and destination IP addresses detected from blocked countries
- Whether LDAP over SSL is enabled
- Whether the LDAP client certificate is used
- The number of management accounts and Firebox-DB accounts
The Firebox sends management details to WatchGuard in Fireware v2026.1 or higher, or Fireware v12.12 or higher.
- Number of logins through WatchGuard System Manager (WSM)
- Number of logins through Fireware Web UI
- Number of logins through the CLI
- Number of times a cloud-managed Firebox is removed from WatchGuard Cloud
- Number of times a cloud-managed Firebox is switched to Visibility Only mode
These counters reset after the Firebox sends weekly data to WatchGuard.
- Number of references to the Microsoft 365 alias
- Whether Mobile Security is enabled
- How many mobile devices are connected
- How many Android devices are connected
- How many iOS devices are connected
- How many mobile devices are connected through a VPN
- How many policies include a Mobile Security device group
- How many connections were denied by a policy with Mobile Security enabled
- Whether multicast routing is enabled
- Whether NetFlow is enabled
- NetFlow protocol version that is enabled
- How many interfaces have Active Scan enabled
- The schedule interval configured for Active Scan
- How many devices were found on your network
- How many devices were found by Active Scan
- How many devices were found by Mobile Security
- How many devices were found by Exchange Monitor
- How many devices were found by the FireClient service
- How many devices were found by HTTP detection
- How many devices were found by the iked process
- How many devices were found by the SSL VPN process
- Last active scan performance details (how many devices were found, how many active devices were found, how long the scan took to complete)
- Whether quotas are configured on the Firebox
- How many quota rules are configured
- How many quota actions are configured
- How many quota exceptions are configured
- Whether RADIUS SSO is configured
- Whether quota statistics are configured for RADIUS SSO
- Method used for global multi-WAN
- Number of WAN interfaces configured on the Firebox
- Number of SD-WAN actions configured on the Firebox
- Number of round-robin SD-WAN actions configured on the Firebox
- Number of failover SD-WAN actions configured on the Firebox
- Whether Spanning Tree Protocol is enabled
- Whether Tigerpaw is enabled
- Whether the TOR Exit Node Blocking service is enabled
- Total number of source IP addresses scanned
- Total number of source IP addresses blocked
- Whether Traffic Management and QoS marking is enabled
- Number of policies that use a Traffic Management action
- Number of policies with QoS marking enabled
- Number of Application Control actions that use a Traffic Management action
- Number of regular (policy-based) BOVPN gateways configured
- Number of regular (policy-based) BOVPN tunnel routes configured
- Number of regular (policy-based) BOVPN gateways with multi-wan VPN failover and failback enabled
- Number of regular (policy-based) BOVPN gateways that use certificate as the authentication method
- Number of regular (policy-based) BOVPN gateways that use IKEv1
- Number of regular (policy-based) BOVPN gateways that use IKEv2
- Number of BOVPN virtual interfaces (route-based BOVPN) configured
- Number of BOVPN virtual interfaces (route-based BOVPN) with multi-wan VPN failover and failback enabled
- Number of BOVPN virtual interfaces (route-based BOVPN) that use certificate as the authentication method
- Number of BOVPN virtual interfaces (route-based BOVPN) configured with an optional local IP address
- Number of BOVPN virtual interfaces (route-based BOVPN) configured with an optional peer IP address
- Number of BOVPN virtual interfaces (route-based BOVPN) configured with an optional netmask
- Number of BOVPN virtual interfaces (route-based BOVPN) configured that use IKEv1
- Number of BOVPN virtual interfaces (route-based BOVPN) configured that use IKEv2
- Number of BOVPN virtual interfaces (route-based BOVPN) configured with a remote endpoint type of Firebox (use the GRE driver)
- Number of BOVPN virtual interfaces (route-based BOVPN) configured with a remote endpoint type of cloud VPN (use the WGTVI driver)
- Number of BOVPN virtual interfaces (route-based BOVPN) configured that use the dynamic peer gateway IP
- Whether Mobile VPN with IPSec is enabled
- Whether Mobile VPN with IKEv2 is enabled
- Whether Mobile VPN with LT2P is enabled
- Maximum number of active BOVPN tunnels allowed by the Firebox license
- Current number of active BOVPN tunnels
- Maximum number of mobile VPN users allowed by the Firebox license for Mobile VPN with IPSec and Mobile VPN with IKEv2
- Current number of active or connected mobile VPN users for Mobile VPN with IPSec and Mobile VPN with IKEv2
- Whether BOVPN virtual interfaces (route-based BOVPN) and FireCluster are enabled
- Whether Mobile VPN with SSL is enabled
- Whether management tunnel over SSL is enabled
- Whether BOVPN over TLS is enabled and the Firebox is configured in Server mode
- Number of configured clients when the local Firebox is configured in Server mode
- Whether BOVPN over TLS is enabled and the Firebox is configured in Client mode
- Number of configured servers when the local Firebox is configured in Client mode
- Number of the configured servers that use the native OpenVPN configuration file (.ovpn)
- Whether WatchGuard Cloud is enabled
Threat Telemetry (Optional)
When you create a new configuration file for your Firebox or upgrade your Firebox to Fireware v12.11 or higher, by default, your Firebox is configured to send threat telemetry data to WatchGuard. The WatchGuard security team uses that threat telemetry data to research and investigate the threats the Firebox detects and analyze the current threat landscape. WatchGuard then uses the anonymous aggregated data to showcase threat detection trends in the WatchGuard quarterly Internet Security Report and on the WatchGuard Cybersecurity Hub page.
This feature is only available for Fireboxes that run Fireware v12.11 or higher.
If you do not want to send threat telemetry data to WatchGuard, you can disable this feature. To disable threat telemetry feedback on your Firebox, clear the Send Threat Telemetry to WatchGuard check box.
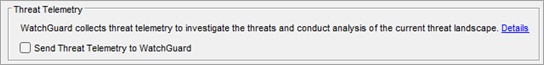
When the Send Threat Telemetry to WatchGuard check box is enabled, the Firebox sends threat telemetry data to WatchGuard in a compressed file daily and each time the device reboots. To conserve space on the Firebox, threat telemetry data is removed from the Firebox after it is sent to WatchGuard.
Threat telemetry data can include the following information for threats detected by the security services enabled on the Firebox:
- Incident time
- Security service that detected the incident
- Proxy policy that handled the traffic
- Source IP address
- Destination IP address
- Type of virus detected
- Threat level
- Signature ID
- MD5 value
The threat telemetry data sent to WatchGuard depends on the security service that detected the threat.