Applies To: Locally-managed Fireboxes
Server load balancing is not supported on Firebox T15 and NV5 models.
The server load balancing feature is designed to help you increase the scalability and performance of a high-traffic network with multiple servers. With server load balancing, you can enable the Firebox to control the number of sessions initiated to as many as 10 servers for each firewall policy you configure. The Firebox controls the load based on the number of sessions in use on each server. The Firebox does not measure or compare the bandwidth that is used by each server.
You configure server load balancing as an SNAT action. The Firebox can balance connections among your servers with two different algorithms.
When you configure server load balancing, it is important to know:
- You can configure server load balancing for any policy to which you can apply static NAT.
- If you apply server load balancing to a policy, you cannot set SD-WAN routing, policy-based routing, or other NAT rules in the same policy.
- If you use server load balancing in an active/passive FireCluster configuration, real-time synchronization does not occur between the cluster members when a failover event occurs. When the passive backup master becomes the active cluster master, it sends connections to all servers in the server load balancing list to see which servers are available. It then applies the server load balancing algorithm to all available servers.
- If you use server load balancing for connections to a group of RDP servers, you must configure the firewall on each RDP server to allow ICMP requests from the Firebox.
- You can configure a server load balancing SNAT action for traffic sent to an external or optional Firebox interface.
Server load balancing SNAT is limited to the source IP address.
Server Probes
To monitor the availability of servers configured in a server load balancing SNAT action, the Firebox sends probe packets to each server every 10 seconds. For a TCP policy, the probe is a SYN. For an RDP or UDP policy, the probe is an ICMP packet.
If the Firebox receives a response to the probe, the server that responded is considered active (up) and available to receive traffic. If a response is not received, the Firebox waits 10 seconds and sends another probe packet to that server. If the server does not respond to the second probe, or if it responds with a TCP reset, the device is considered inactive (down), which means the Firebox does not send load-balanced traffic to that server. If the server sends an ACK packet back to the Firebox, the Firebox immediately marks the server as active.
The Firebox continues to actively send probe packets to all load balanced servers regardless of whether the server status is active or inactive. When the Firebox receives traffic handled by a policy that is configured for server load balancing, the policy sends the traffic to one of the load balanced servers that is active.
Server Load Balancing Settings
Method
When you configure server load balancing, you must choose the algorithm method to use.
Round-robin
If you select this option, the Firebox distributes incoming sessions among the servers you specify in the policy in round-robin order. The first connection is sent to the first server specified in your policy. The next connection is sent to the next server in your policy, and so on.
Least Connection
If you select this option, the Firebox sends each new session to the server in the list that currently has the lowest number of open connections to the Firebox. The Firebox cannot tell how many connections the server has open on other interfaces.
Source IP Address
You can optionally configure a source IP address in a server load balancing action. If you do not configure a source IP address in the server load balancing action, the Firebox does not modify the sender, or source IP address, of traffic sent to these devices. While the traffic is sent directly from the Firebox , each device that is part of your server load balancing configuration sees the original source IP address of the network traffic.
When you add a server load balancing SNAT action, you can choose to specify a source IP address in the action. Then, when traffic that matches the parameters in your server load balancing SNAT action passes through the policies that manage the traffic on your Firebox, the source IP address is changed to the IP address that you specify. The same source IP address is used for all servers in the server load balancing action.
Sticky Connection
When you define the parameters for the SNAT action, sticky connections are always enabled. A sticky connection is a connection that continues to use the same server for a defined period of time. Stickiness makes sure that all packets between a source and destination IP address pair are sent to the same server for the time period you specify. By default, the Firebox uses the default sticky connection setting of 8 hours. You can change the setting to a different number of hours. When a new connection from the same client is received, the expiration time of the connection is extended.
In Fireware v12.11 and higher, you can change the timeout setting to hours, minutes, or seconds. When you disable sticky connections, the Firebox does not use a timeout value, and server load balancing occurs for new connections.
Server Weight
You can add any number of servers to a server load balancing action. When you configure the settings for a load balancing member, you can also add a weight to each server to make sure that your most powerful servers are given the heaviest load. The weight refers to the proportion of load that the Firebox sends to a server. By default, each server has a weight of 1. If you assign a weight of 2 to a server, you double the number of sessions the Firebox sends to that server, compared to a server with a weight of 1.
Port Address Translation
When you configure the settings for a load balancing member, you can enable port address translation (PAT). When you enable PAT, you can change the packet destination to specify a different internal host and a different port.
Add a Server Load Balancing SNAT Action
In Fireware Web UI, before you can configure a policy to use server load balancing, you must define the server load balancing details in an SNAT action.
- Select Firewall > SNAT.
The SNAT page appears. - Click Add.
The Add SNAT page appears.
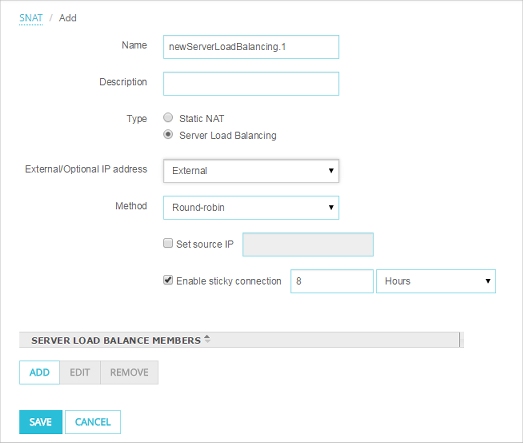
- In the Name text box, type a name for this SNAT action.
- (Optional) In the Description text box, type a description for this SNAT action.
- Select Server Load Balancing.
- From the External IP address drop-down list, select the external IP address or alias to use in this server load balancing action.
For example, you can have the Firebox apply server load balancing for this action to packets received on only one external IP address. Or, you can have the Firebox apply server load balancing for packets received on any external IP address if you select the Any-External alias.
- To specify the source IP address for this server load balancing action, select the Set source IP check box. In the adjacent text box, type the source IP address.
- From the Method drop-down list, select the algorithm to use for server load balancing: Round-robin or Least Connection.
- Click Add to add the IP address of an internal server to this action.
The Add Member dialog box appears.
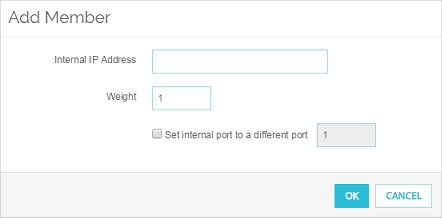
- In the Internal IP Address text box, type the IP address of the server to add.
- In the Weight text box, type or select the weight for this server for load balancing.
- To enable port address translation (PAT), select the Set internal port to a different port check box. In the adjacent text box, type or select the port number.
If you use a server load balancing SNAT action in a policy that allows traffic that does not have ports (traffic other than TCP or UDP), the internal port setting is not used for that traffic.
- Click OK.
The server appears in the Server Load Balance Members list .
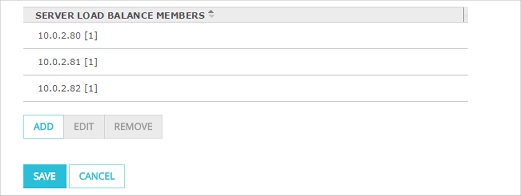
- To add another server to this action, click Add and repeat Steps 10–14.
- To set sticky connections for your internal servers, select the Enable sticky connection check box. In the Enable sticky connection text box and drop-down list, specify the time period for the sticky connection.
- Click Save.
In Policy Manager, you can create a server load balancing SNAT action and then add it to a policy, or you can create the server load balancing SNAT action from within the policy configuration.
- Select Setup > Actions > SNAT.
The SNAT dialog box appears. - Click Add.
The Add SNAT dialog box appears.

- In the SNAT Name text box, type a name for this SNAT action.
- (Optional) In the Description text box, type a description for this SNAT action.
- Select Server Load Balancing.
- Click Add.
The Add Server Load Balancing NAT dialog box appears.
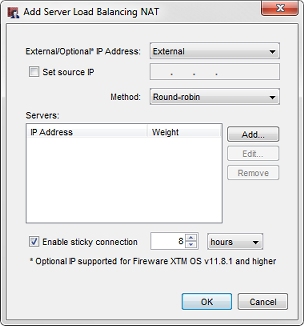
- From the External IP address drop-down list, select the external IP address or alias to use in this server load balancing action.
For example, you can have the Firebox apply server load balancing for this action to packets received on only one external IP address. Or, you can have the Firebox apply server load balancing for packets received on any external IP address if you select the Any-External alias.
- To specify the source IP address for this server load balancing action, select the Set source IP check box. In the adjacent text box, type the source IP address.
- From the Method drop-down list, select the algorithm to use for server load balancing: Round-robin or Least Connection.
- Click Add to add the IP address of an internal server to this action.
The Add Server dialog box appears.

- In the IP Address text box, type the IP address of the server to add.
- In the Weight text box, type or select the weight for this server for load balancing.
- To enable port address translation (PAT), select the Set internal port to a different port check box. In the adjacent text box, type or select the port number.
If you use a server load balancing SNAT action in a policy that allows traffic that does not have ports (traffic other than TCP or UDP), the internal port setting is not used for that traffic.
- Click OK.
The server appears in the Servers list.

- To add another server to this action, click Add and repeat Steps 10–14.
- To set sticky connections for your internal servers, select the Enable sticky connection check box. In the Enable sticky connection text box and drop-down list, specify the time period for the sticky connection.
- Click OK.
The servers are added to the SNAT Members list for this action.
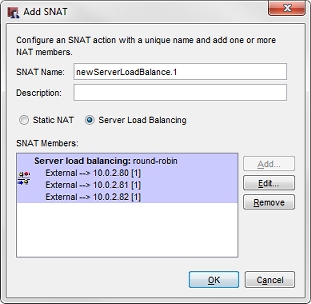
- Click OK.
The SNAT action is added. - Click OK.
Add a Server Load Balancing SNAT Action to a Policy
After you define a server load balancing SNAT action, you can use it in one or more policies.
- Select Firewall > Firewall Policies.
- Select a policy
Or, add a new policy. - From the Action drop-down list select,Edit Policy.
- In the To section, click Add.
The Add Member dialog box appears. - From the Member Type drop-down list, select Server Load Balancing.
The list of server load balancing actions appears.
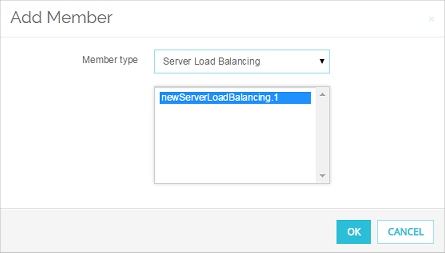
- Select a server load balancing action. Click OK.
The server load balancing action is added to the To section of the policy. - Click Save.
- Double-click a policy to edit it.
Or, add a new policy. - In the To section, click Add.
The Add Address dialog box appears. - Click Add SNAT.
The SNAT dialog box appears. This list shows all configured Static NAT and Server Load Balancing actions.
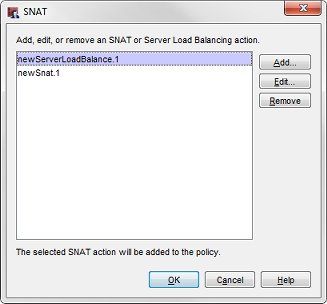
- Select a configured server load balancing action. Click OK.
Or, to define a new server load balancing action, click Add and follow the steps in the previous procedure.
The selected server load balancing action appears in the Add Address dialog box.
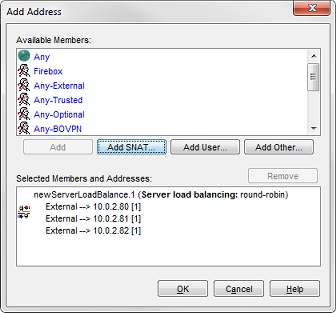
- Click OK to close the Add Address dialog box.
- Click OK to close the Policy Properties dialog box.
Edit or Remove a Server Load Balancing SNAT Action
- Select Firewall > SNAT.
The SNAT page appears. - Select an SNAT action.
- Click Edit.
The Edit SNAT page appears. - Modify the SNAT action.
When you edit an SNAT action, any changes you make apply to all policies that use that SNAT action. - Click Save.
- Select Setup > Actions > SNAT.
The SNAT dialog box appears. - Select an SNAT action.
- Click Edit.
The Edit SNAT page appears. - Modify the SNAT action.
When you edit an SNAT action, any changes you make apply to all policies that use that SNAT action. - Click OK.
In Policy Manager, you can also edit an SNAT action when you edit a policy.
- Double-click a policy to edit it.
The Edit Policy Properties dialog box appears, with the Policy tab selected. - In the To section, select the SNAT action you want to edit.
- Click Edit.
The Edit SNAT dialog box appears. - Modify the SNAT action.
When you edit an SNAT action in a policy, the changes apply to all policies that use that SNAT action. - Click OK.
You can remove any SNAT action that is not used by a policy.
- Select Firewall > SNAT.
The SNAT page appears - Select an SNAT action.
- Click Remove.
A confirmation dialog box appears. - Click OK to confirm that you want to remove the SNAT action.
- Select Setup > Actions > SNAT.
The SNAT dialog box appears. - Select an SNAT action.
- Click Remove.
A confirmation dialog box appears. - Click Yes to confirm that you want to remove the SNAT action.
- Click OK.