Applies To: Cloud-managed Fireboxes, Locally-managed Fireboxes
The Advanced Malware (APT) report shows a summary of the malware and malicious activity on your network that was detected by APT Blocker.
This report is available when log messages with data for this report exist in the specified time frame. To make sure that your Firebox sends log messages required to generate this report, follow the steps to Enable Logging for this Report.
How to Use this Report
This report can show you the top instances of malware downloaded by users on your network. Here are some ways to use this report:
- Select the Recipient/Destination and Sender/Source pivots to identify the sender and recipient of malicious files and the connection source and destination.
- Select the Protocols and MIME Type pivots to identify the protocols and file types used to introduce malicious files to your network.
- Select the Activity Trend pivot to see malware activity over time.
- Select the Content Name pivot to see the names of files identified as malicious by APT Blocker and to troubleshoot files that cause false positives. If you identify files that cause false positives, add them to the File Exceptions list.
View the Report
This report is available in WatchGuard Cloud and in Dimension.
- Log in to WatchGuard Cloud.
- Select Monitor > Devices.
- Select a folder or a specific device.
- To select the report date range, click
 .
.
- From the list of reports, select Services > Advanced Malware (APT).
The Advanced Malware (APT) report opens.
- To see reports for your Fireboxes or FireClusters, select Home > Devices.
The Devices list opens.
To see reports for your groups of Fireboxes, select Home > Groups.
The Groups list opens. - Select the Name of a Firebox, cluster, or group.
The Tools > Executive Dashboard page opens. - Select the Reports tab.

- Select Services > Advanced Malware (APT).
The Advanced Malware (APT) report opens.
Pivots
You can use pivots to change the view of the data on the report.
To switch to a different view, select a pivot from the drop-down list above the report.
This report includes these pivots:
Activity Trend
Summary report of the trend of malware detected by APT Blocker over time.
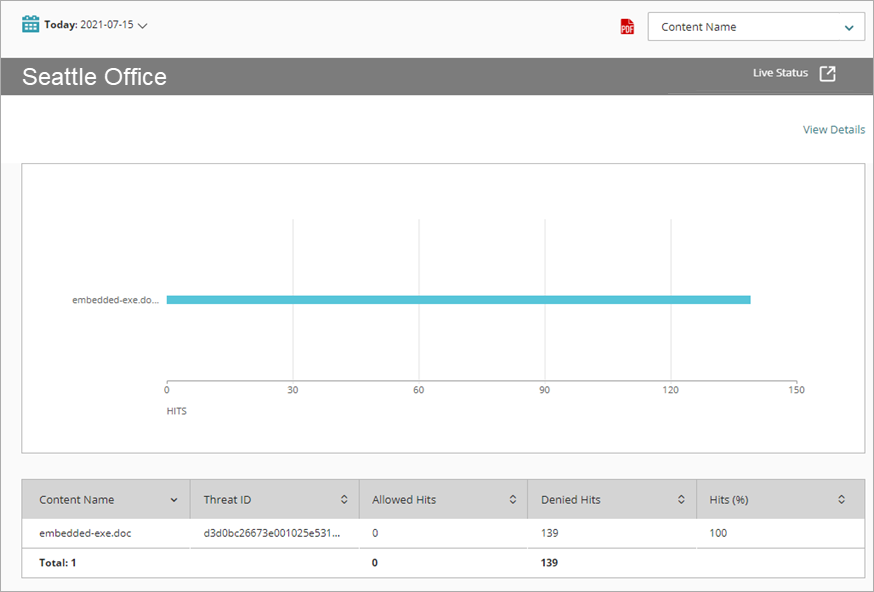
Content Name
Summary of the malware detected by APT Blocker, organized by content name. Includes allowed and denied hits.
MIME Type
Summary of the MIME types used for malicious activity detected on your network by APT Blocker.
Protocol
Summary of the protocols used for malicious activity detected on your network by APT Blocker.
Recipient/Destination
Summary of the recipient names and destination addresses for malicious activity on your network.
Sender/Source
Summary of the sender names and source addresses for malicious activity on your network.
Threat ID
Summary of the malware detected by APT Blocker, organized by the Threat ID.
Threat Level
Summary of the threat levels assigned to malicious activity on your network.
Advanced Malware (APT) Report Detail View
To view a detailed report of all malicious activity detected by APT Blocker, click View Details at the top of the report.
The Advanced Malware (APT) Detail report includes a row for each instance of malicious activity detected by APT Blocker:
| Column | Description |
|---|---|
| Disposition | Action taken by the Firebox for this traffic, such as Stripped or Allowed |
| Time | Date and time that the event occurred |
| Threat Level | Severity of the threat (High, Medium, or Low) |
| Threat ID | Identification number assigned to the threat |
| Content Name | Name of the file or content that included the threat |
| Source | IP address of the traffic source |
| Destination | IP address of the traffic destination |
| Policy | Name of the Firebox policy that examined the traffic |
| Protocol | Protocol used to send the traffic |
| Host | Host name used to send the traffic |
| Sender | For SMTP, POP3, or IMAP protocols, the email address that sent the email |
| Recipient | For SMTP, POP3, or IMAP protocols, the email address the email was sent to |
| Hits | Number of attempts |
| More Information | To see more detailed information (includes MD5 and Threat Level information), click Threat Details. |
Enable Logging for this Report
Logging for cloud-managed Fireboxes is automatically enabled. For locally-managed Fireboxes, you must manually enable logging in Fireware Web UI or Policy Manager. For more information, see Set Logging and Notification Preferences.
To collect the data required for this report for locally-managed Fireboxes, in Fireware Web UI or Policy Manager:
- In the General Settings for all proxy actions that have APT Blocker enabled, select Enable logging for reports.
- In all APT Blocker Actions, select the Log check boxes for threat levels you want to appear on the report. For more information, see Configure APT Blocker.