Applies To: Cloud-managed Fireboxes
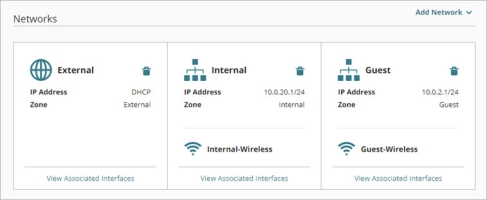
When you add a network to a cloud-managed Firebox, you select the network zone. You can see the zone for each configured network on the Networks configuration dashboard.
A Firebox supports three network zones:
External
An external network is any network external to the Firebox, such as the Internet. The Firebox configuration must have at least one external network so that the Firebox can connect to WatchGuard Cloud. When you add a cloud-managed Firebox, you configure settings for an external network.
An external network is a member of the built-in alias Any-External.
Internal
An internal network is a private network for internal users protected by the Firebox. By default, a cloud-managed Firebox has one internal network with multiple interfaces.
An internal network is a member of the built-in alias Any-Internal.
The default Outgoing firewall policy allows connections from internal networks to external networks.
Guest
A guest network is a private network for guest users. Add a guest network to enable outbound connections for guest users on your network.
When you add a guest network, the default Guest firewall policy allows connections from the guest network to external networks.
Both the Internal and Guest zones are private networks. Add a Guest network to allow guest users to connect to the Internet. Users on a Guest network cannot connect to resources on your other internal networks unless you explicitly add a policy to allow it.