AP Deployment with a Single SSID
For basic AP installation, you can deploy WatchGuard APs with a single SSID. In this simple deployment scenario, you do not have to configure VLANs or complex network settings. This example is recommended for small office deployments where the requirement is to add secure, wireless access to an existing LAN.
If your environment is large enough to require more than one AP for wider wireless coverage, you can assign the same SSID to multiple APs. When you assign the same SSID to more than one AP, the range of that SSID is extended, which enables mobile users to roam from one AP coverage area to another. For more information, go to AP Deployment with Simple Roaming.
For wireless networks with a large number of WatchGuard APs to deploy that will be assigned the same SSIDs and do not require unique configurations, you can use the Automatic Deployment feature. For more information, go to About AP Automatic Deployment.
With this deployment scenario, there are two primary methods you can use to physically connect your WatchGuard AP to the network:
- Connect the AP directly to your Firebox on a Trusted or Optional network interface.
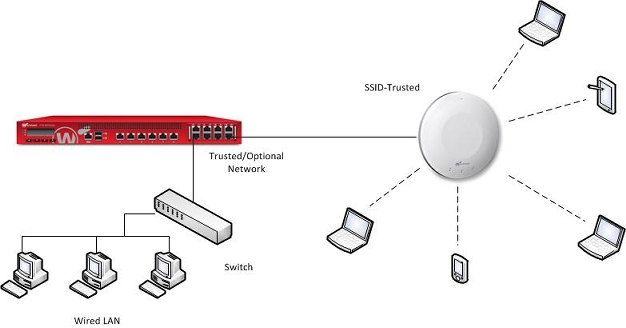
- Connect the AP to a switch that is on a Trusted or Optional network.

AP Deployment and Firebox Policies
Note these policy requirements, which depend on how you connect the APs and other resources to your network.
- If you connect the AP directly to a Firebox interface, the wireless users do not automatically have access to trusted resources that connect to other trusted interfaces on the Firebox. You must configure policies to allow that traffic because the wireless users are on a separate trusted network. The default firewall policies only allow outbound traffic from trusted networks, but do not allow traffic between devices on different trusted networks.
- If you connect the AP to a switch on the trusted network, the wireless users can access other network resources on the network connected to the same interface. You do not need to create additional policies to allow access because the traffic does not go through the Firebox, but you do need to create policies for traffic to resources that connect to any other trusted interface.
Configure a Firebox Interface and Enable DHCP
To connect the AP directly to a Firebox interface, configure that interface as a Trusted or Optional interface. Enable the DHCP server or DHCP relay on that interface so that the Firebox can automatically assign an IP address to the AP and to wireless clients.
- Select Network > Interfaces.
- Select a network interface and click Edit.
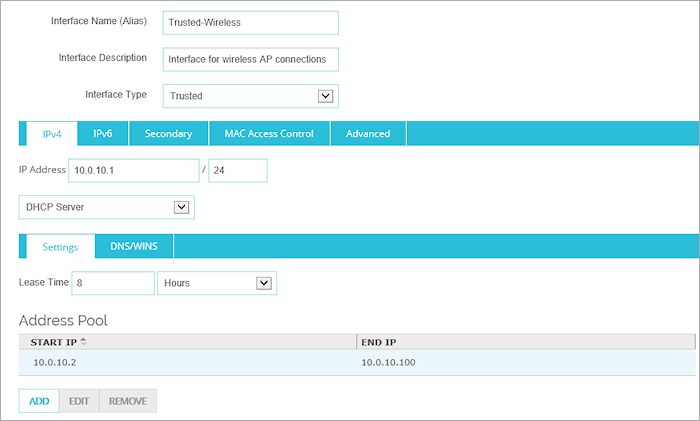
- In the Interface Name (Alias) text box, type a name for this network.
For this example, type Trusted-Wireless. - (Optional) In the Interface Description text box, type a description of the interface.
- From the Interface Type drop-down list, select Trusted.
- In the IP Address text box, type the IP address for this interface in slash notation.
For this example, type 10.0.10.0/24. - Select DHCP Server.
- In the Address Pool section, click Add.
- In the Starting IP and Ending IP text boxes, type the IP addresses for the DHCP range.
For this example, type 10.0.10.2 and 10.0.10.100. - Click Save to save the interface settings.
- Select Network > Configuration.
The Network Configuration dialog box appears. - Select a network interface and click Configure.
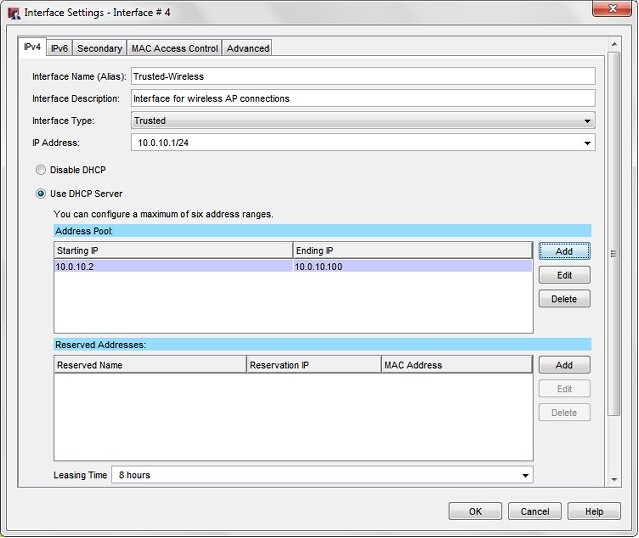
- In the Interface Name (Alias) text box, type a name for this network.
For this example, type Trusted-Wireless. - (Optional) In the Interface Description text box, type a description of the interface.
- From the Interface Type drop-down list, select Trusted.
- In the IP Address text box, type the IP address for this interface in slash notation.
For this example, type 10.0.10.0/24. - Select Use DHCP Server.
- In the Address Pool section, click Add.
The Add Address Range dialog box appears. - In the Starting IP and Ending IP text boxes, type the IP addresses for the DHCP range.
For this example, type 10.0.10.2 and 10.0.10.100. - Click OK to save the DHCP configuration.
The IP address range appears in the Address Pool list. - Click OK to save the interface settings.
- Save the configuration file to your Firebox.
Add an SSID to the Gateway Wireless Controller
- Select Network > Gateway Wireless Controller.
- Select the Enable the Gateway Wireless Controller check box.
- On the SSIDs tab, click Add.
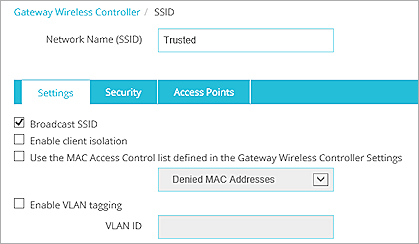
- In the Network Name (SSID) text box, type a name for this SSID.
For this example, type Trusted. - In the Access Points tab, select the APs that will use this SSID.
If the APs have not been paired to the Firebox yet, you can assign this SSID to each AP after you add it to the Gateway Wireless Controller. - Select the Security tab.
- Configure your wireless encryption security settings for this SSID.
- Save the SSID configuration.
- Click Save to save the Gateway Wireless Controller configuration.
- Select Network > Gateway Wireless Controller.
The Gateway Wireless Controller configuration page appears, with the SSIDs tab selected. - Select the Enable the Gateway Wireless Controller check box.
This enables the Firebox to discover unpaired APs on your trusted or optional network.
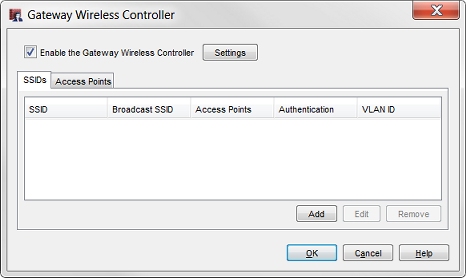
- On the SSIDs tab, click Add.
The Add SSID dialog box appears, with the Settings tab selected. - In the Network Name (SSID) text box, type a name for this SSID.
For this example, type Trusted.
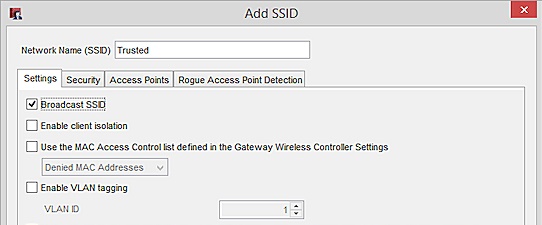
- Make sure the Enable VLAN tagging check box is cleared.
This is required because you do not want to configure VLANs for this simple deployment scenario. - In the Access Points tab, move the APs that you want to use this SSID from the Available list to the Member list.
- Select the Security tab.
- Configure your wireless encryption security settings for this SSID.
- Click OK to save your SSID settings.
- Save the configuration file to your Firebox.
After you have configured the SSIDs, you can pair the AP with the Firebox, and assign these SSIDs to the radios on the AP.