Use an HTTP Content Action for TLS/SSL Offloading
When content inspection is enabled, the Firebox can decrypt an HTTPS request, examine the content, then encrypt the request again with a new certificate. The HTTPS proxy inspects content for requests that match configured domain name rules with the Inspect action and for WebBlocker categories you select to inspect.
In some instances, you might not want to encrypt the content sent between the Firebox and the internal server. This is known as TLS/SSL offloading. This option reduces the CPU load on the Firebox, and removes the burden of TLS/SSL encryption and decryption from your internal web server.
With TLS/SSL offloading, connections between the Firebox and the internal web server are not encrypted. This might not meet compliance requirements for security of some types of data.
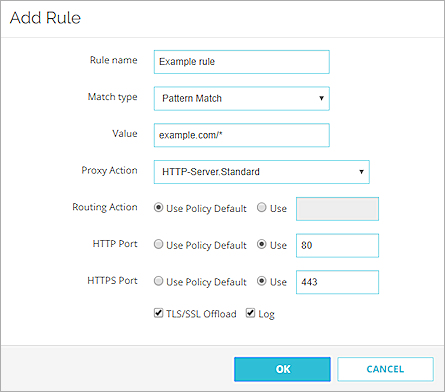
To enable TLS/SSL offloading, configure a content action that specifies the domain or path of the server, and enable the TLS/SSL Offload option.
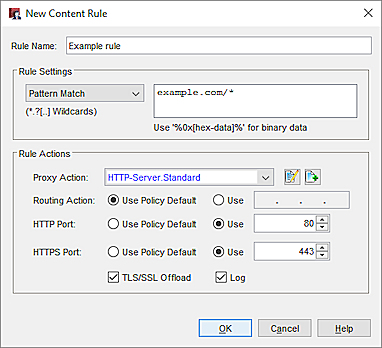
A content rule with TLS/SSL Offload enabled in Policy Manager
To use this action for inbound HTTPS requests, you must specify the content action in an HTTPS Proxy action. For information, go toHTTPS-Proxy: Domain Name Rules.
In a content action, you can enable TLS/SSL Offload in a content rule or in the action to take if no rule is matched. For information about how to configure content actions, go to Configure HTTP Content Actions.
When you enable the TLS/SSL Offload option in a content rule:
- HTTPS is used for traffic between external clients and the Firebox
- HTTP is used for traffic between the Firebox and the internal server
If you enable the TLS/SSL offload option, you might need to change configuration settings on your server application so that the server application uses HTTPS in links/redirects even if incoming requests use HTTP.
For example, Wordpress requires this setting:
$_SERVER[‘HTTPS’]=‘on’;
Some server applications recognize the Upgrade-Insecure-Requests header.
Upgrade-Insecure-Requests: 1
Configure HTTP Content Actions