About Modular Interfaces
Some Firebox models support user-installable interface modules. In each modular interface slot on the Firebox, you can install an interface module that adds network interfaces to the Firebox.
The available interface modules are:
- WatchGuard Firebox M 8 port 1Gb Copper Module
- WatchGuard Firebox M 8 Port SFP Fiber Module
- WatchGuard Firebox M 4 Port 10 Gb SFP+ Fiber Module
- WatchGuard Firebox T 1 Port 10 GB SFP+ Fiber Module
- WatchGuard Firebox T80/T85 LTE Interface module
This interface module is available only for the Firebox M4600, M4800, M5600, and M5800:
- WatchGuard Firebox M 2 Port 40 GB QSFP+ Fiber Module
These interface modules are available only for the Firebox M290, M390, M590, and M690:
- WatchGuard Firebox M 4 Port 1Gb Copper Module
- WatchGuard Firebox M 4 port SFP Fiber Module
- WatchGuard Firebox M 2 Port 10 Gb SFP+ Fiber Module
- WatchGuard Firebox M 4 Port Multispeed (1/2.5/5G) Copper Module with PoE
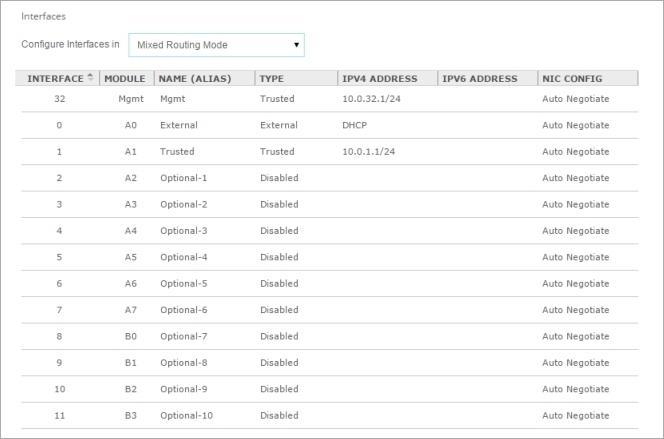
In the interface configuration for Firebox models that support modular interface, the Module column lists the port numbers for each modular interface. The letter indicates the Firebox slot where the interface module is installed. The number indicates the port number as it is labeled on the interface module. For example module A6 refers to port 6 on the interface module installed in slot A.
The image below shows the default interface configuration for a Firebox M5600, with two interface modules installed.
Interface Modules
Each Firebox model has a different number of built-in interfaces and supports additional interface modules. You must install an interface module before you can configure the interfaces. If you use Policy Manager, after you install or remove an interface module, you must connect to the Firebox and launch a new Policy Manager instance to retrieve the Firebox configuration file that shows the installed network interfaces.
These Firebox models have eight built-in interfaces, and one interface module slot. On the interface module, ports are labeled with port numbers from 0-7 or 0-3.
| Modular Interface Port Numbers | Interface Numbers in Firebox Configuration |
|---|---|
| A0–A7 (8 port) A0–A3 (4 port) |
8–15 8–11 |
If an interface module is not installed, those interface numbers do not appear in the configuration.
These Firebox models have eight built-in interfaces, and one interface module slot.
The Firebox M590 and M690 have 2 additional interfaces for SFP+, and the M690 has 2 addition interfaces for 10GbE.
For each interface module, ports are numbered from 0-3 or 0-1. The interface numbers that appear in the Firebox configuration depend on the number of ports on the interface module. In the management software, the interfaces numbers start after the number of interfaces built into the base model.
| Number of Ports | Modular Interface Port Numbers | Interface Numbers in Management Software (M290 and M390) | Interface Numbers in Management Software (M590) | Interface Numbers in Management Software (M690) |
|---|---|---|---|---|
| 4 | 0-3 | 8-11 | 10-13 | 12-15 |
| 2 | 0-1 | 8-9 | 10-11 | 12-13 |
If an interface module is not installed, those interface numbers do not appear in the configuration.
The Firebox M4600 and M4800 have eight built-in interfaces, and two interface module slots, A and B. You can install an interface module in each slot. For each interface module, ports are labeled with port numbers from 0–7 or 0–3.
| Firebox Slot | Modular Interface Port Numbers | Interface Numbers in Firebox Configuration |
|---|---|---|
| A | A0–A7 (8 port) A0–A3 (4 port) A0-A1 (2 port) |
8–15 8–11 8-9 |
| B | B0–B7 (8 port) B0–B3 (4 port) B0-B1 (2 port) |
16–23 16–19 16-17 |
If any slot is empty, those interface numbers do not appear in the configuration, and the interface numbers for other installed modular interfaces do not change.
The Firebox M5600 and M5800 have one built-in interface, and four interface module slots, A, B, C, and D. Two interface modules come preinstalled in slots A and B. For each interface module, ports are labeled with port numbers from 0–7 or 0–3.
| Firebox Slot | Modular Interface Port Numbers | Interface Numbers in Firebox Configuration |
|---|---|---|
| A |
A0–A7 (8 port) A0–A3 (4 port) A0-A1 (2 port) |
0–7 (preinstalled) 0–3 0-1 |
| B | B0–B7 (8 port) B0–B3 (4 port) B0-B1 (2 port) |
8–15 8–11 (preinstalled) 8-9 |
| C | C0–C7 (8 port) C0–C3 (4 port) C0-C1 (2 port) |
16–23 16–19 16-17 |
| D |
D0–D7 (8 port) D0–D3 (4 port) D0-D1 (2 port) |
24–31 24–27 24-25 |
If any slot is empty, those interface numbers do not appear in the configuration, and the interface numbers for other installed modular interfaces do not change.
The Firebox T80 and T85 have eight built-in interfaces, and one interface module slot. You can install an interface module to add one interface.
| Firebox T80/T85 Slot | Modular Interface Port Number | Interface Number in Firebox Configuration |
|---|---|---|
| A | A0 | 8 |
If the slot is empty, the interface number does not appear in the configuration.
The Firebox automatically detects installed interface modules when you power it on.
Before you remove an interface module, you must disable the interfaces in the Firebox configuration. If an enabled interface is not installed, you cannot connect to the Firebox to modify the configuration.
Interface modules are not hot-swappable. To avoid damage to the system, disconnect power to the Firebox before you install or remove interface modules. For complete information about interface modules and how to safely install them, see the Hardware Guide for your Firebox.
Some transceivers for the modules are hot-pluggable, which means you can add them to an active system. You cannot hot plug SFP or SFP+ transceivers on 8 x 1Gb SFP fiber modules on Firebox M4600 and M5600 models.
For information about how to install or remove interface modules for members of a FireCluster, go to About FireCluster with Modular Interfaces.
About the Management Interface
The Firebox M5600, M4800, and M5800 have a built-in management interface.
- For M5600 and M5800, the management interface is interface 32.
- For M4800, the management interface is interface 24.
The management interface is always listed first in the configuration. By default, this interface is configured as a Trusted interface with the alias Mgmt. You connect to this interface to run the Web Setup Wizard or Quick Setup Wizard to configure a Firebox that uses factory-default settings.
The management interface is for initial setup, but is not a dedicated management interface. You can configure and use it just as you would use any other interface. We recommend that you keep the management interface configured as a Trusted interface, so that you can always use it connect to your Firebox for management, even if the modular interfaces are not installed.
About Factory-Default Settings the Firebox M4800, M5600 and M5800
The default network and configuration properties for a Firebox M5600 and M5800 are:
Management Interface
The default IP address for Eth32 is 10.0.32.1/24.
The default IP address and port for Fireware Web UI on Eth32 is https://10.0.32.1:8080.
Interface 32 is configured to give IP addresses to computers on the trusted network through DHCP. By default, these IP addresses can be from 10.0.32.2 to 10.0.32.254.
The default IP address for Eth24 is 10.0.24.1/24.
The default IP address and port for Fireware Web UI on Eth24 is https://10.0.24.1:8080.
Interface 24 is configured to give IP addresses to computers on the trusted network through DHCP. By default, these IP addresses can be from 10.0.24.2 to 10.0.24.254.
External network
Interface 0 (Eth0) is configured as an external interface.
The external interface is configured to get an IP address with DHCP.
You must have an interface module installed in slot A before you power on a new Firebox M5600 or M5800 or reset it to factory-default settings.
About FireCluster with Modular Interfaces
If you configure two Fireboxes with modular interfaces as a FireCluster, you must install the same interface modules in the same slots on both cluster members. There are also other interface connection requirements for a FireCluster with these models. For more information, go to About FireCluster with Modular Interfaces.